SG-3100 LAN port with Unify AP and multiple VLANs
-
Has anyone had success configuring one of the SG-3100 LAN ports (1-4) with a directly connected Unify AP-AC-Pro and multiple VLANs/SSIDs? I followed the Netgate doc on how to enable the LAN port and it's working fine (LAN port 1, PVID 4081) but I am lost on how to set up a 2nd SSID on the Unify using a VLAN (I get the Unify setup, just not the Pfsense config). I do not have a managed switch and I do not have a USG. Thanks.
-
i have a 3100 but i am using a 60W UBNT switch to power my Nano AP
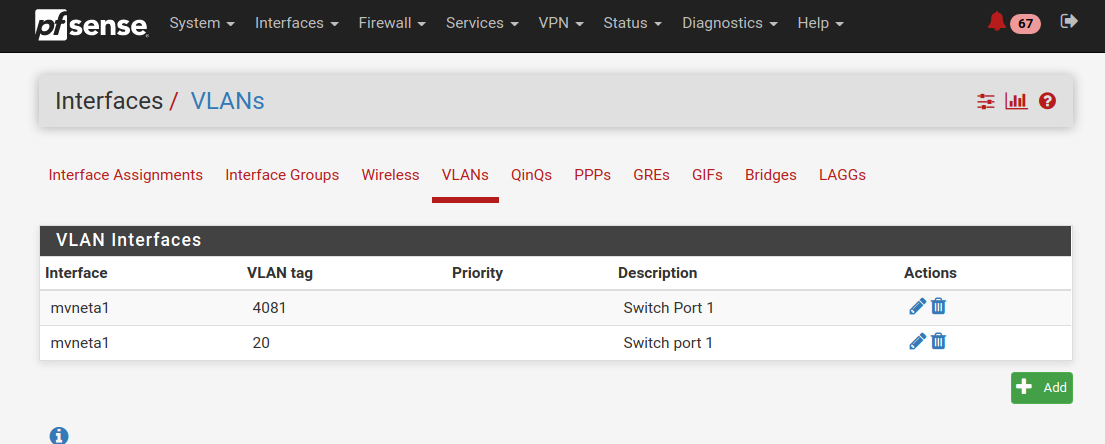
as long as you have the interface created with the correct vlan data. then under interface assignment > Vlans created and correct.
it should work
-
I'm using it too, with a cheap switch, 802.1q capable.
-
@Gordon-Shumway said in SG-3100 LAN port with Unify AP and multiple VLANs:
nify using a VLAN (I get the Unify setup, just not the Pfsense config).
You would set it up exactly how you would setup any other vlan... Create the vlan on pfsense with whatever tag ID your using..
-
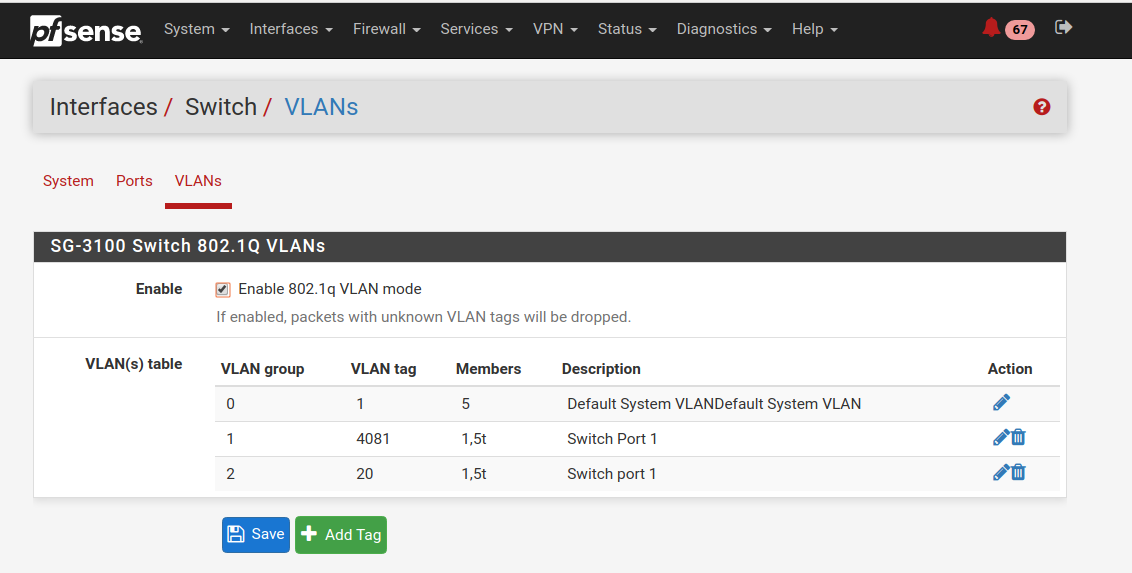
Since this is the "LAN 1" switch port which had to be configured with a VLAN to begin with, should the additional VLANs on mvneta1 be configured under Interfaces>Switch>VLANs or Interfaces>Assignments>VLANs ... or both? The Wifi device is connecting to the Unify SSID that has the matching VLAN ID but not getting a DHCP address (DHCP and firewall rules are configured). Thanks
-
Yes you will have to create the vlan on pfsense, and then assign those vlans to the port your going to be bringing in the vlans on with the different tags for your different ssids.. I have 3100 at the office that we do some vlans on, when I get a chance I will log in and grab some screenshots and post them here as example... Its no different - doesn't matter if wired or wireless downstream for the vlans... Pfsense could care less if they are wireless users or wired users, etc.. He doesn't know or even care... The traffic is either tagged or it isn't that hits his interface be it a normal nic, or a switch port.
-
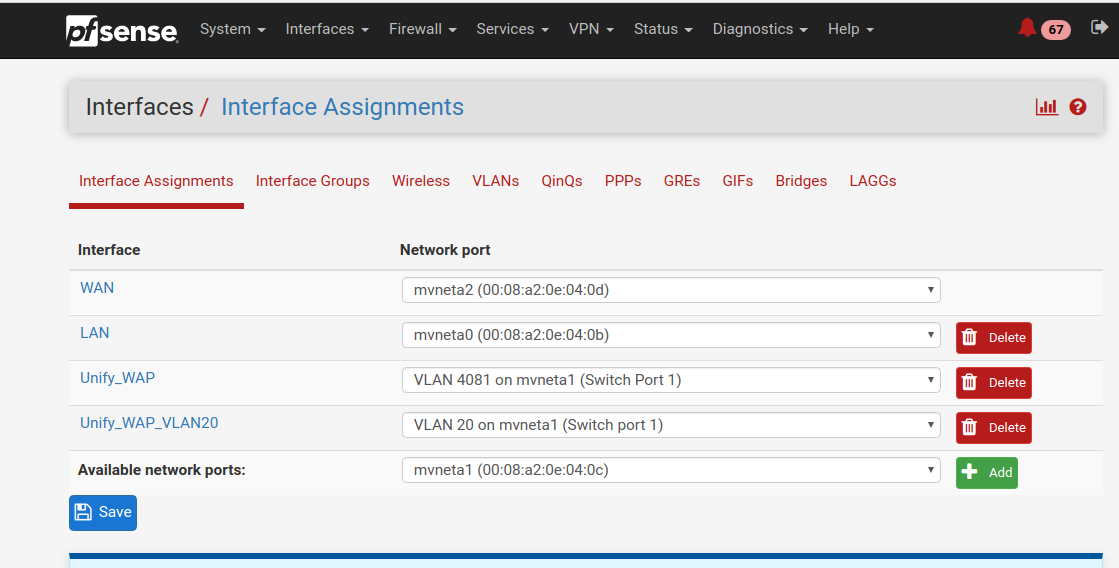
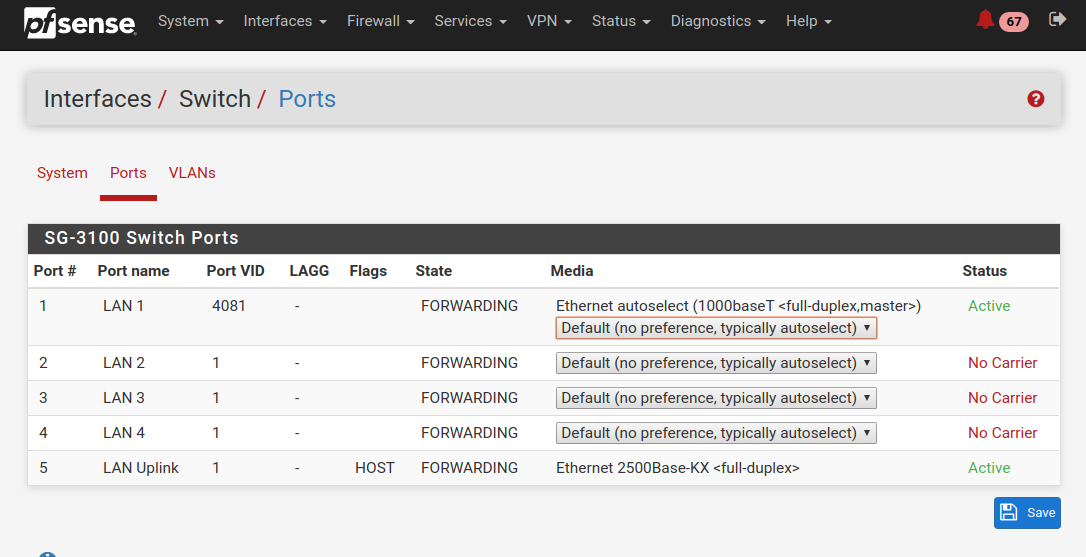
I have attached some screenshots. If you have the time can you take a look and see if I did anything blatantly stupid? Thanks!
-
I would say this is pretty stupid... What are all the alerts?
-
They are complaints after installing pfBlockerNG. Apparently I have to go through a registration process. I have not dug into it yet.
pfBlockerNG MaxMind - MaxMind now requires a License Key! Review the IP tab: MaxMind settings for more information. @ 2020-03-22 19:41:01
pfBlockerNG MaxMind - MaxMind now requires a License Key! Review the IP tab: MaxMind settings for more information. @ 2020-03-22 20:01:27 -
Well I take it from your AP your wanting to do more than 1 vlan right? You only have that switchport with vlan 20 on it.. would need all your vlans on the port your AP connected too.. And 1 can be untagged.. The others would be tagged.
If connected to port 1.. Why do you have 20 untagged on port 1 and 4081... That not going to work.,
-
@johnpoz
Yes. I'd like to have 3 SSID's on the Unify: private, guest, and IOT. According to Netgate support, the 4081 business was apparently the only way I was going to be able to use LAN ports 1-4 on the SG3100 which are all part of the mvneta1 switch. The netgate docs showed that I needed to tag each port with a unique VLAN and PVID to make them work. I'm not quite sure if this is the right configuration for me to be able to plug in the Unify AP in LAN port 1 or not but a non VLAN tagged SSID seems to be getting an IP from the DHCP server but VLAN 20 is not. -
Well add the vlans you created to the port they are connected too... You can only have 1 untagged vlan.. All others have to be tagged. Looks to me on port 1 you have your lan vlan 4081 and 20 both untagged.
-
@johnpoz
Yes. I'd like to have 3 SSID's on the Unify: private, guest, and IOT. According to Netgate support, the 4081 business was apparently the only way I was going to be able to use LAN ports 1-4 on the SG3100 which are all part of the mvneta1 switch. The netgate docs showed that I needed to tag each port with a unique VLAN and PVID to make them work. I'm not quite sure if this is the right configuration for me to be able to plug in the Unify AP in LAN port 1 or not but a non VLAN tagged SSID seems to be getting an IP from the DHCP server but VLAN 20 is not. image url)
image url)I aded the additional VLANs, all tagged, and changed VLAN Group 1 to 1,5t and it seems that fixed everything. Thanks very much for your assistance. Now on to firewall rules!
-
2 weeks ago i installed a "Dual SSID" UBI AP AC Pro.
I installed the Unifi Controller on a VM DEB10 server , and configured it for the two "Tagged Vlans"Then i connected to a switch port (not directly to pfSense) , but the recipe is the same.
You need to keep in mind that the "Controller & AP" talks untagged , so whetever Vlan you make untagged on the port , has to be able to talk to the UBI Controller
AP Switch port
AP Native : Controller Lan communication Vlan , untagged.
SSID-1 : Tagged
SSID-2 : Tagged/Bingo