Can I use one of my 6 physical network ports to be a vpn port?
-
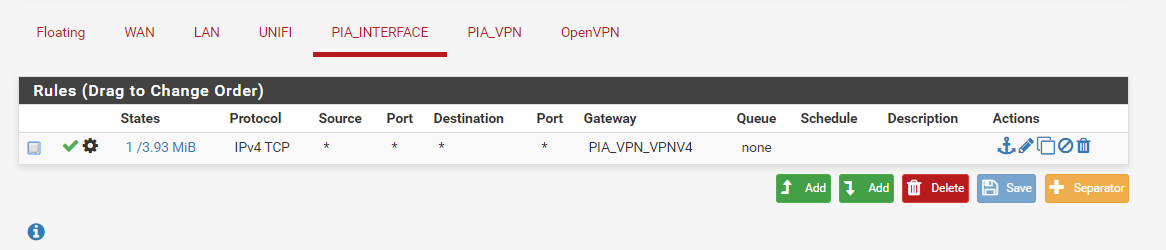
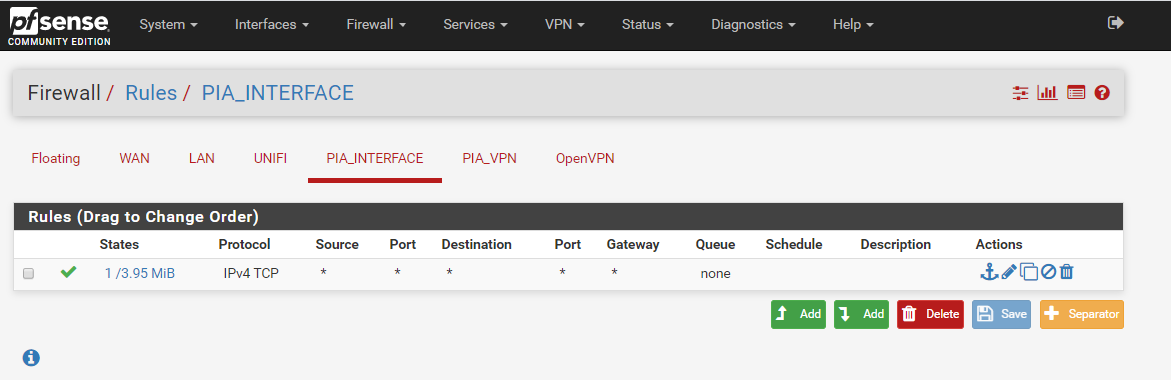
Now with your nat set to auto any clients on this network should work.. You created a any any rule on this interface right?
-
hmmm with nat set to auto, Windows changes from no internet shown on the connection to showing internet is now available but there is no response to the outside world, the other LAN & UNIFI interfaces are working fine
-
I have a Windows 10 Laptop solely connected to the vpn interface FYI
And yes I do have an any rule
-
I removed the gateway from the interface but still the same, no internet
-
well how is internet going to work with just TCP... dns is UDP... to lookup www.internet.com you need to be able to talk UDP.
-
A schoolboy error.. no idea how that happened!
I have just put everything back and its working!! I am so relieved! and yes it is so bloody easy now I know how it all comes together, you must have been pulling your hair out! I am going to do this again on another server just to prove to myself how easy it is :-)
All I have now is a dns leak but have seen plenty of info on how to resolve that!
Thanks so so much!
-
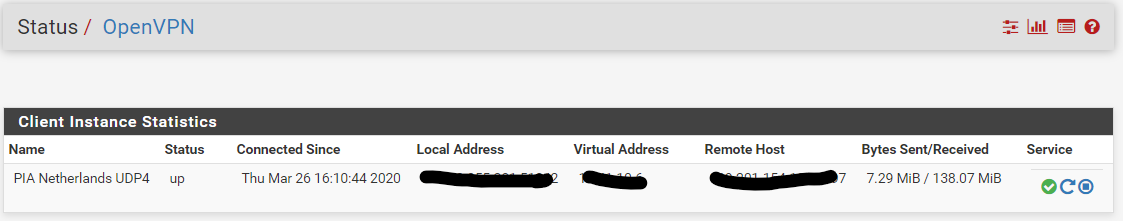
One think I have noticed though, although everything is working (apart from the DNS Leak)
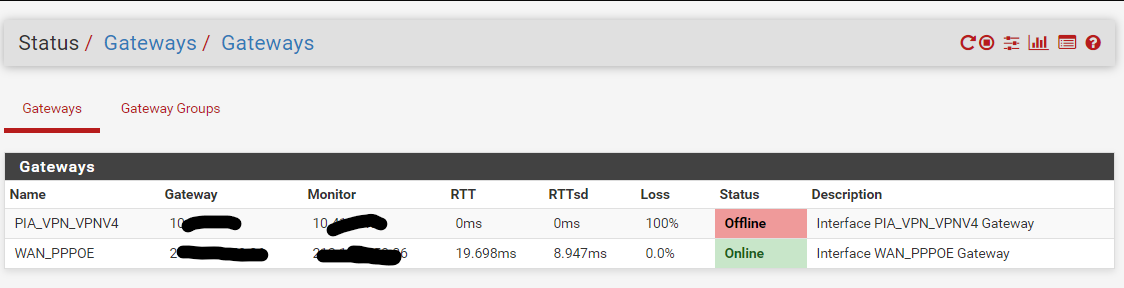
The VPN Gateway is showing as offline?
-
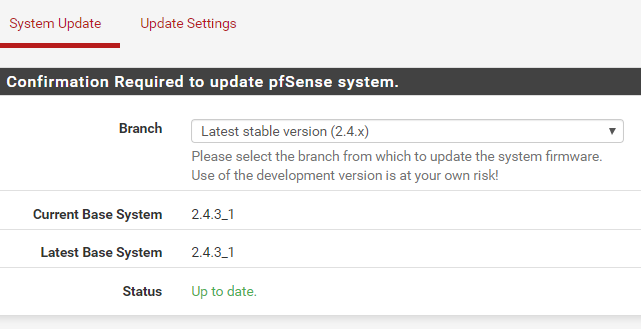
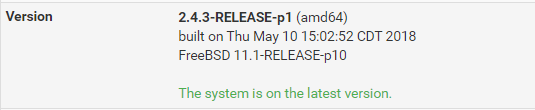
What version are you running? That is not current version..
Oh your in the status section.. Thats why it looks different.. Restart the vpn instance.
Really dude your hiding a 10 address?
-
haha, yes, I did hide the 10 address but not intentionally! :-D
-
That is not current.. current is
2.4.4-RELEASE-p3 (amd64)
built on Thu May 16 06:01:19 EDT 2019
FreeBSD 11.2-RELEASE-p10Well now 2.4.5 is, it just dropped..
Version 2.4.5 is available.
Version information updated at Thu Mar 26 11:19:06 CDT -
hmmm ok...
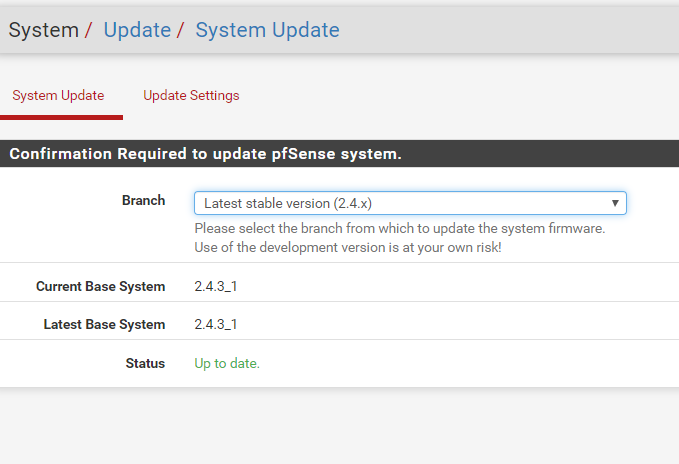
I run pfsense (for nearly 2 years now) as a vm on a HP Microserver running unraid, I wonder why it doesn't update automatically? I will look to see how to update now, are there any pitfalls I should be aware of jumping from 2.4.3 to 2.45?
Thank you
-
Well 2.4.5 just dropped like maybe an hour a ago.. at best... So prob wouldn't update just yet... Oh but your on a VM... Oh then just take a snapshot and click the button... Use to do that all the time when running on vm.. Even daily snapshots I would run - because could just rollback to the snapshot took before I clicked upgrade..
-
-
Because your system is hosed ;)
https://docs.netgate.com/pfsense/en/latest/install/upgrade-troubleshooting.html
pkg-static clean -ay; pkg-static install -fy pkg pfSense-repo pfSense-upgrade -
perhaps you are right!
 this doesn't look good!
this doesn't look good!Shell Output - pkg-static clean -ay; pkg-static install -fy pkg pfSense-repo pfSense-upgrade
The following package files will be deleted:
/var/cache/pkg/sqlite3-3.22.0_1-3c0de3fc74.txz
/var/cache/pkg/iprange-1.0.3-65464f6717.txz
/var/cache/pkg/sqlite3-3.22.0_1.txz
/var/cache/pkg/pfSense-rc-2.4.3_1-abfbca5302.txz
/var/cache/pkg/pfSense-rc-2.4.3_1.txz
/var/cache/pkg/pfSense-kernel-pfSense-2.4.3_1-bde115e399.txz
/var/cache/pkg/pfSense-base-2.4.3_1-bd208e4cff.txz
/var/cache/pkg/pfSense-kernel-pfSense-2.4.3_1.txz
/var/cache/pkg/pfSense-default-config-2.4.3_1-01f7a2a04f.txz
/var/cache/pkg/pfSense-default-config-2.4.3_1.txz
/var/cache/pkg/pfSense-base-2.4.3_1.txz
/var/cache/pkg/libnghttp2-1.31.1.txz
/var/cache/pkg/pfSense-pkg-pfBlockerNG-devel-2.2.5_10.txz
/var/cache/pkg/perl5-5.24.4-89340f9371.txz
/var/cache/pkg/perl5-5.24.4.txz
/var/cache/pkg/libnghttp2-1.31.1-24a10b90b7.txz
/var/cache/pkg/pfSense-pkg-pfBlockerNG-2.1.4_8-d9071a3c1b.txz
/var/cache/pkg/lighttpd-1.4.48_1-26b547d114.txz
/var/cache/pkg/pfSense-pkg-pfBlockerNG-2.1.4_8.txz
/var/cache/pkg/lua52-5.2.4-34ceb7a41c.txz
/var/cache/pkg/lighttpd-1.4.48_1.txz
/var/cache/pkg/whois-5.2.17.txz
/var/cache/pkg/lua52-5.2.4.txz
/var/cache/pkg/whois-5.2.17-3e6f851a29.txz
/var/cache/pkg/GeoIP-1.6.11-3a55b74664.txz
/var/cache/pkg/pecl-intl-3.0.0_11.txz
/var/cache/pkg/GeoIP-1.6.11.txz
/var/cache/pkg/grepcidr-2.0-cec890eb71.txz
/var/cache/pkg/grepcidr-2.0.txz
/var/cache/pkg/aggregate-1.6_1-c1ea4bf1a7.txz
/var/cache/pkg/aggregate-1.6_1.txz
/var/cache/pkg/pecl-intl-3.0.0_11-7e63ad3a02.txz
/var/cache/pkg/icu-60.2_1,1-66aa5ec8d3.txz
/var/cache/pkg/iprange-1.0.3.txz
/var/cache/pkg/icu-60.2_1,1.txz
/var/cache/pkg/pfSense-pkg-pfBlockerNG-devel-2.2.5_10-5af9141812.txz
/var/cache/pkg/pfSense-repo-2.4.3_3-97fc8a3f69.txz
/var/cache/pkg/pfSense-repo-2.4.3_3.txz
/var/cache/pkg/pfSense-upgrade-0.52-239e1a78fc.txz
/var/cache/pkg/pfSense-upgrade-0.52.txz
/var/cache/pkg/pfSense-repo-2.4.3_4-c159ba5343.txz
/var/cache/pkg/pfSense-repo-2.4.3_4.txz
/var/cache/pkg/pfSense-upgrade-0.53-7baf5452be.txz
/var/cache/pkg/pfSense-upgrade-0.53.txz
The cleanup will free 78 MiB
Deleting files: .......... done
All done
Updating pfSense-core repository catalogue...
pfSense-core repository is up to date.
Updating pfSense repository catalogue...
pfSense repository is up to date.
All repositories are up to date.
The following 3 package(s) will be affected (of 0 checked):Installed packages to be UPGRADED:
pfSense-repo: 2.4.3_3 -> 2.4.3_4 [pfSense]
pfSense-upgrade: 0.52 -> 0.53 [pfSense]Installed packages to be REINSTALLED:
pkg-1.10.3_1 [pfSense]Number of packages to be upgraded: 2
Number of packages to be reinstalled: 13 MiB to be downloaded.
[1/3] Fetching pkg-1.10.3_1.txz: .......... done
[2/3] Fetching pfSense-repo-2.4.3_4.txz: . done
[3/3] Fetching pfSense-upgrade-0.53.txz: .. done
Checking integrity...Assertion failed: (strcmp(uid, p->uid) != 0), function pkg_conflicts_check_local_path, file pkg_jobs_conflicts.c, line 386.
Child process pid=52858 terminated abnormally: Abort trap -
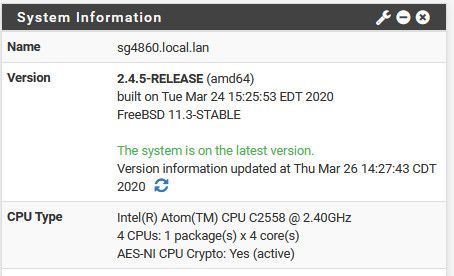
I just pulled the trigger to 2.4.5.. And I really still have like hour of so more work to do... But I was pretty confident.. Had my media, and my backup (just in case)..
Took a bit longer than I thought - but I'm up on new 2.4.5... Have to check that all packages are working, etc.. But clearly the internet is working ;)
-
Glad it worked for you!

Mine is defo looking hozed!
Shell Output - pfSense-upgrade -d -c
Updating repositories metadata...
Updating pfSense-core repository catalogue...
pfSense-core repository is up to date.
Updating pfSense repository catalogue...
pfSense repository is up to date.
All repositories are up to date.
Upgrading pfSense-repo...
Updating pfSense-core repository catalogue...
pfSense-core repository is up to date.
Updating pfSense repository catalogue...
pfSense repository is up to date.
All repositories are up to date.
Checking integrity...Assertion failed: (strcmp(uid, p->uid) != 0), function pkg_conflicts_check_local_path, file pkg_jobs_conflicts.c, line 386.
Child process pid=10408 terminated abnormally: Abort trap -
Well do a clean install of 2.4.5 would be my suggestion... You can load in your backup config file..
-
-
So when you get back - just curious question.. Did you really think that 2.4.3_1 was current? That they hadn't updated in like 2 years.. And you were just ok with that?