Beginner Home LAN Setup
-
Good Evening All,
Apologies if this has been asked but I do assure you I have read the forum previously for answers. In addition to this I've learnt as much as I can at this stage and have set up a virtual machine to assist me as well as completing courses on udemy. I'm currently learning and completing TAFE and as part of it want to expand my knowledge with PFSense. That and I quite enjoy it.
Ideally I would like advice on what Netgate product would suit me the best. At this stage I was looking at the SG-3100.
A bit about my environment. I have NBN FTTP, connected to my Asus 68U running Merlin.
Ideally, I want to still keep my Asus to have wireless capability. I would like multiple networks such as a DMZ for my cameras/robot vaccuum, guest network, my phone and other wireless devices connected on another network configured with a VPN and one just for IOT eg tv running netflix with the vpn off.
I have completed a networking course with Cisco but not in this environment but I do have understanding if I can get pointed in the right direction.
Thanks for reading and looking forward to the learning experience ahead. -
The SG-3100 may be overkill, but what I would be concerned about is the Marvell switch integrated into it. It took me some time to get used to the one in the SG-1100, and if you are starting out then you may want to eliminate the confusion. On the flip side, buying the hardware gives you the built in support for a year, but paying for separate support is $399/year, so that's an option if you want to roll your own hardware.
I did go the roll your own route with the Protectli hardware, which would run the Community edition and wouldn't come with pro support unless you get the subscription.
A couple of other options is to run pfSense in a VM as your primary router, but I wouldn't do that unless you had a L3 managed switch and a really good understanding of routing and VLANs.
One thing I always fall back to when playing and testing is GNS3 to create an isolated lab network to play with. I have the pfSense software virtualized in here and have a complete mock-up of my two home networks and the site-to-site VPN between them. It's by far the safest way to play and test stuff without upsetting the family, so that's always an option.
-
Hi jlw,
Thanks for your reply. Appreciate it! I'll look into the Protectli hardware. Also GNS3 sounds awesome and that will by far help me save money and when I've figured it out and ready to deploy know that it's going to work!
Thanks again.
-
@dave_v40 said in Beginner Home LAN Setup:
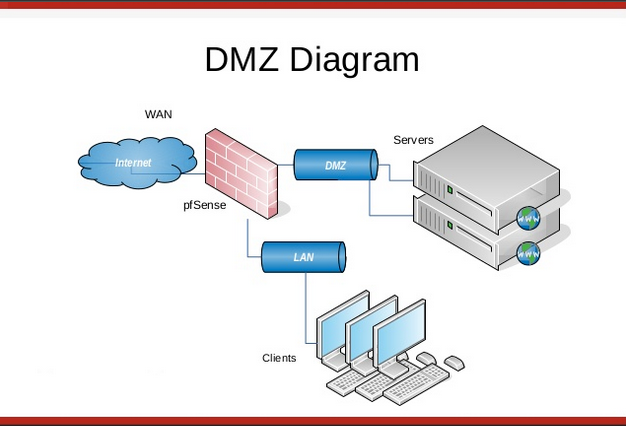
I would like multiple networks such as a DMZ
For that reason, I would not give up on the SG-3100 which you intuitively determined meet your needs now and future (next 5yrs)...bare in mind how many Ethernet ports you will need by looking at the image below.
-
You don’t need to have separate physical ports for a DMZ, it can be done using VLANs.
-
You would still need separate physical ports on the switching gear.
-
@jlw52761 I don't understand why you would not encourage another who has already determined that a Netgate device meets his or her network requirement and instead recommend another device that's about the same price. Makes no sense compared to the advantage the OP would gain choosing Netgate. I even saw the SG-3100 on Amazon for a crazy price. Your option would be two devices, the protectli ($220 - $700) and a managed switch ($50) and...appears to be overkill as well to use your words. It okay to point out potential issue such as the Marvell switch integration; however, that what the Netgate support is for. I believe if a person already identify a Netgate device for their need, our goal as forum members is to help the person to make the buying decision.
-
So the DMZ does not have to be a separate physical port, a VLAN can operate just fine for a DMZ in this case. As for the managed switch, sure, one could get by without it if one wants to have a separate unmanaged switch for every possible VLAN and enough physical ports on the firewall to support that. I have a managed L3 switch and use one physical port to run all of my VLANs, including my DMZs (yes, I have two DMZs) and everything is tidy and is controlled through the firewall rules. Now can there be an attack that breaks out of the VLAN? Sure, there can be an attack to get around just about anything if someone tries hard enough, but in my scenerio and possibly in the OP's environment, it's not worth the mitigation. In my enterprise environment, it is worth the mitigation. It's all case by case, no single t-shirt fits everything.
The reason I said that the SG-3100 MAY be overkill is, for $400 you get 3.6Gbps of L3 forwarding, ~500Mbps of VPN, and the 4 switched Gbe ports with two unswitched Gbe ports. Does the OP need this or could a SG-1100 better fit the OP's needs, or a "roll your own" solution. For me, I wanted something in-between the SG-3100 and SG-1100 in terms of packet forwarding, but I also wanted more storage for logging and more CPU/RAM for ancillary functions, so I went with the Protecli for about $220 (250GB SDD 8GB RAM), far less than the SG-3100 with nearly the same capabilities, minus the support package. For the record, I also own a SG-1100 and run that at my second house, so I do have experience with that device as well.
My stance is not to sell Netgate hardware, they have sales persons for that. The OP asked a question and I provided my opinion and a couple of options, and reasoning behind them. Since the OP is starting out, adding confusing elements such as the integrated Marvell switch may not be desired, which was one of the options I presented. Notice I said the SG-3100 MAY be overkill, not that it is. I also said that the OP MAY want to eliminate confusion. Nothing in my statements said anything negative, just that there are other options on the table, which is what the OP was after in the first place.
Now back to the SG-3100, it most definitely meets all of the OP's requirements, you can run OpenVPN on the appliance, have separate interfaces for LAN, DMZ, and WAN, but unless the OP wants to run only 4 VLANs (and 4 devices) internally and have unmanaged switches for each, then a L3 managed switch with VLANs will be present in the environment. So with that, does the OP really need all the physical ports on the firewall itself? Maybe, maybe not, it's really a personal preference of the OP at this point on how to configure the DMZ and wither or not he/she wants to have the DMZ on a physically separate port or on an external VLAN. If one of the LAN ports on the SG-3100 is used for the DMZ, it's just a VLAN on the Marvell switch anyway, making the entire conversation a moot point.
The OP asked for options, and has gotten options outside of just Netgate hardware. It's really up to the OP to decide what boxes he/she needs checked and what option fits the bill. Maybe the OP just wants turnkey with pro support, which I would say then look at the SG-1100 and SG-3100 and decide which checks the most boxes and fits your budget. If the OP is more about "getting hands dirty", then some of the other options I mentioned would be the route to go. Or, the OP could go for a blended option like I did, have the SG-1100 for the small stuff and the roll your own for the down and dirty.
-
@jlw52761 Thank you for your time and professionalism in presenting...I really appreciate that. Neither is I a Netgate sales person...The OP is an informed network person having taken a Cisco course...he stated, his needing multiple network such as a DMZ...he stated, he "would like advice on what Netgate product would suit me the best." He stated, his having multiple network toys and his looking at the SG-3100.
Personally, I would have recommend the XG-7100 desktop longterm...I am even thinking now of getting that SG-3100 from Amazon and flip it...on a second look, I get the reality check...it's the SG-1100. https://www.amazon.com/SG-3100-pfSense-Security-Gateway-Appliance/dp/B07JBWRQ3K