Bypassing DNSBL for specific IPs
-
@yeleek Please note, if you do an update, disable and re-enable DNSBL that line will be modified again back to the standard entry. You will need to check each time and remove any leading "server:" to ensure your expected behavior works as expected.
Just an FYI as it caught me out and is now part of my standard checks following any modifications to the configuration of my pfSense
@ kevinmitky I am doing exactly what you described. I have my dnsbl view as the subnets and am specifying specific hosts on those subnets to bypass. These are Roku's devices that had news feeds that used block sites and I made a choice to allow it access for the convenience. Ensuring the host specific acl was before the subnet based ones was something I just do based on my background, but if you don't have it in that order, maybe that's an area to check. That and having to clear any host DNS caches made this a little more time consuming to test if I screwed up the config on pfSense :-)
-
Current syntax under Services > DNS Resolver > Custom Options with Pfblockerng enabled is:
private-domain: "plex.direct"
server:include: /var/unbound/pfb_dnsbl.conf**I have a multiple devices I want to bypass dnsbl (192.168.1.50, 192.168.1.51, 192.168.1.52) but everything else on 192.168.1.0/24 I want running through dnsbl so as I understand it I should just copy and paste the following into the custom options field of the DNS resolver for this:
*server: private-domain: "plex.direct" access-control-view: 192.168.1.50/32 bypass access-control-view: 192.168.1.51/32 bypass access-control-view: 192.168.1.52/32 bypass access-control-view: 192.168.1.0/24 dnsbl view: name: "bypass" view-first: yes view: name: "dnsbl" view-first: yes include: /var/unbound/pfb_dnsbl.*conf -
@TupleButter Basically yes. although in your samples you have some "*" in places I don't expect. i.e. *server:
In my active config the last line is: -
[Edited] My original was incorrect as it was changed following an update. You will need to keep checking this line if there are any changes, as it gets auto added with server: prefixing it.include: /var/unbound/pfb_dnsbl.*confTBH its been a while since I set this up, so not sure if you need to repeat the server: tag again.
As a note, if you ever enable blocking of banned or emerging hosts you will need to include that config file in each view
My custom options currently are: -
server: so-reuseport: no private-domain: "plex.direct" # bypass view for Roku IP addresses access-control-view: 192.168.1.51/32 bypass access-control-view: 192.168.1.61/32 bypass access-control-view: 192.168.1.83/32 bypass access-control-view: 2601:xxxx:xxxx:xxxx::/64 dnsbl access-control-view: 2601:xxxx:xxxx:xxxx::/64 dnsbl access-control-view: 2601:xxxx:xxxx:xxxx::/64 dnsbl access-control-view: 192.168.1.0/24 dnsbl access-control-view: 192.168.2.0/24 dnsbl access-control-view: 192.168.3.0/24 dnsbl view: name: "bypass" view-first: yes include: /var/unbound/host_entries.conf view: name: "dnsbl" view-first: yes include: /var/unbound/host_entries.conf # local-zone: "youtube.com" inform_deny # local-zone: "facebook.com" inform_deny include: /var/unbound/pfb_dnsbl.*confThis ensures plex works, unbound is multithreaded, includes my IPv6 subnets (obscured in example) provide bypass for selected hosts (in this case only Roku and they are IPv4 only), denies access to banned or emerging hosts.
The two commented out local-zone's are my sledge hammer approach to blocking social media for some of the younger members in the house when they get grounded! They are not currently grounded :-) -
I have followed the above and put this in my unbound custom options and it doesnt block the ads
server:
private-domain: "plex.direct"
access-control-view: 10.10.0.0/24 bypass
access-control-view: 10.0.0.0/24 dnsbl
access-control-view: 10.0.8.0/24 dnsbl
view:
name: "bypass"
view-first: yes
view:
name: "dnsbl"
view-first: yes
include: /var/unbound/pfb_dnsbl.*confif i get rid of everything and put it back to what it was before which was the below then i get adblocking but of course it happens on every network. I just want adblocking on my guest network and openvpn network for now
server:
private-domain: "plex.direct"
server:include: /var/unbound/pfb_dnsbl.*confMay someone help please?
-
@ryk48 said in Bypassing DNSBL for specific IPs:
rivate-domain: "plex.direct"
server:include: /var/unbound/pfb_dnsbl.*coRemove the server: from this line.
server:include: /var/unbound/pfb_dnsbl.*confIt should be like this: include: /var/unbound/pfb_dnsbl.*conf
Note that every time you perform a change in pfblocker, you will have to remove the "server:" from unbound custom options.
-
@mcury
Right.. Its what i did above and what my current config is. What i mentioned is what i had before i made the changes which was the config below without all access control stuff.I think my problem might be because im running an active directory domain and all my computers are set to use a windows dns server which forwards to pfsense to do dns over tls so im thinking no matter what network i put in the access control view it will be blocked if i do dnsbl on that network since pretty much everything has its dns set to my windows dns server, except the guest lan.
For example:
My windows dns server is on 10.10.0.0/24 network
my windows pcs are on 10.0.0.0/24
opendns computers are on 10.0.8.0/24
guest is on 192.168.10.0/24my windows pcs have their dns server set to the dns server on the 10.10 network so i think if i dnsbl on the 10.0.0.0/24 network its not working because windows computers dns are pointed to the dns server on the 10.10.0.0/24 network which wouldnt be dnsbl. Also i think id have the same problem on my opendns network as well since its dns servers also point to my windows dns server so i can rdp into network pcs. If i am wrong in how this works please chime in. Sounds like i might need dns servers for each network?
Ideally i just want to do dnsbl on my guest and opendns networks because i want guests to have adblock. I also want to connect to my openvpn server from my phone and browse the net on my phone with no ads and in addition have the ability to rdp into my pcs and servers but how can i achieve that when the opendns network dns points to the windows server network?
-
@ryk48 I have been looking for a pfsense solution to this for awhile. It seems the Unbound views might accomplish what I need as well, but what a pain in the ass to setup and manage. I have been investigating the Sensei plugin for Opnsense. It looks sooooo amazing and does exactly what you are asking about with ease. Policy based filtering! I just really like pfsense and didn’t want to have to reinstall my home router for one feature, but I am not seeing another option. Was hoping Sensei would be migrated to pfsense :P!
We’re you able to get this setup using unbound in pfsense?
-
@kezzla I was not. I figured since im having all of my devices on my network point to my AD DNS Server this wouldnt work. Guest lan would probably work but since i want to rdp from my phone and also block ads on my phone while connected to vpn to home this wouldnt work without affecting all pcs that use my ad dns servers.
-
Just found this thread and I think it might save my a$$ while stuck at home because of the covid19 pandemic... If I'm hijacking an existing thread, I'll move to a new one.
Basically I want all traffic on a specific VLAN (named DMZ with 192.168.2.0/24) totally bypass pfblocker & DNSBL in both directions (incoming and outgoing)... Based on OP's post, I added the following in unbound's custom options:
server: access-control-view: 192.168.2.0/24 bypass access-control-view: 192.168.1.0/24 dnsbl access-control-view: 192.168.3.0/24 dnsbl view: name: "bypass" view-first: yes view: name: "dnsbl" view-first: yes include: /var/unbound/pfb_dnsbl.*confFor some reasons, even after restarting unbound, DNSBL and even rebooting pfsense, I still see tons of alerts in the Reports tab of pfblocker. Using a machine on VLAN, pages are still being blocked. Clearly this is not working for me. What am I doing wrong?
Some of my settings (if it helps):
- WAN is WAN... LAN1, LAN2 and DMZ are VLAN's based on LAN physical interface
- WAN is the only interface selected in pfblockerNG's Inbound Firewall Rules
- LAN1 & LAN2 are the only interfaces selected in pfblockerNG's Outbound Firewall Rules
- LAN1 & LAN2 are the only interfaces selected in DNSBL's "Permit Firewall Rules"
-
I did a quick check on my pfSense version 2.4.5-RELEASE and pfBlockerNG 2.1.4_22 and checked I can bypass a single hosts (/32) and also changed my LAN subnet to bypass (/24) and all worked as expected.
On my setup however I do have to make sure my test PC has IPv6 disabled for DNS so it correctly matched the unbound views.
Clutching at straws, my config is not nicely indented like yours, as you will see from my original reply earlier in this thread, that did seem to cause me problems, but did not spend much time verifying it as I just removed all leading spaces and it mainly worked as expected after that.
-
This is really strange....
- If I remove the leading spaces, I cannot save the config
The following input errors were detected: The generated config file cannot be parsed by unbound. Please correct the following errors: [1586258288] unbound-checkconf[11766:0] error: local-data in redirect zone must reside at top of zone, not at zz.zeroredirect1.com 60 IN A 10.10.10.1 [1586258288] unbound-checkconf[11766:0] fatal error: Could not set up views- I had removed the leading "server:" in front of the last line to look like this:
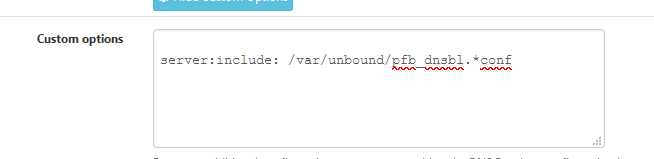
include: /var/unbound/pfb_dnsbl.*confBut every time I login to pfsense and try to modify the unbound settings, it is back to this:
server:include: /var/unbound/pfb_dnsbl.*confIs the package pfblockerNG doing this???
-
@pftdm007 said in Bypassing DNSBL for specific IPs:
Is the package pfblockerNG doing this???
Yep.
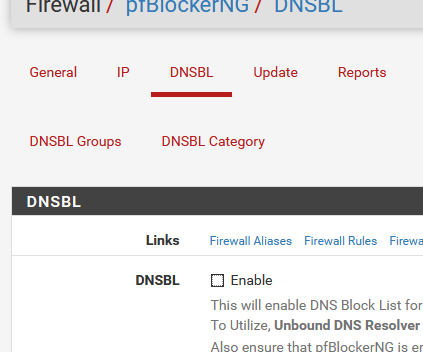
You know now how pfBlockerNG-devel communicates the list with IPs to be blocked to unbound ^^Before you install, the custom options box (unbound) is empty :
When you dissable pfBlockerNG-debel, and re activate it :
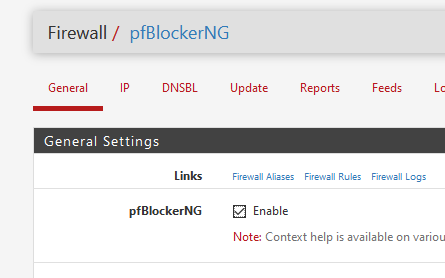
it will add this line to the custom options (unbound) :
The first time you installed pfBockerng-devel, there was even a first comment line :
-
Okayyyy... but...? That doesnt explain why the custom options with views dont work (and dont work if I remove the leading spaces), and how to prevent pfblockerNG from adding the redundant "server:" statement in front of the line....
Others in this thread have successfully used views while using pfblockerNG so there's something I am doing wrong...
-
Which version of pfBlockerNG is installed?
Although I did upgrade mine last night to -deval 2.2.5_30 and quickly ran the same test and it still works fine.Note: upgrading, installing, disabling / enabling etc. will always add the "server:" prefix to the include line. I just have a note to always check and remove it. Am not aware of any workaround.
Based on your error there is another thread from 2016
DNS Resolver cannot be modified or changedSeems to be something regarding the System Domain Local Zone type setting. Mine is Transparent which seems to be OK and allows me to save the config and views do work. If its not this, there must be something else, so will need a little more info on your setup and config.
i.e. Do you have IPv6 configured? That will change a number of things that need additional configuration.
-
@pftdm007 said in Bypassing DNSBL for specific IPs:
and how to prevent pfblockerNG from adding the redundant "server:" statement in front of the line....
Well ...
Have a keyboard ?
Here it is :/usr/local/pkg/pfblockerng/pfblockerng.inc line 1289
$unbound_include = "server:include: {$pfb['dnsbl_file']}.*conf";Take note : this line is still added at the end of the unbound config file. No analyses is done for Custom options already present.
When pfBlockerng installs, or when you re-enable DNSBL mode, that line is added. -
@Gertjan
Nice!Keyboards still rule!, As "Alexa, please make change to pfSense /usr/local . . . . @ line 1289" just isn't going to hack it anytime soon :-)
-
I really wouldn't ask Alexa to do this ......
Anyway, I tried it myself.Disabled :
and forced a Update > Reload >All.
My Unbound > Custom options box is now empty.
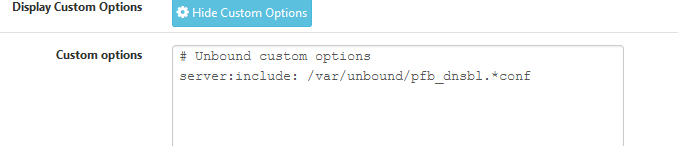
I added a single (needed !) line :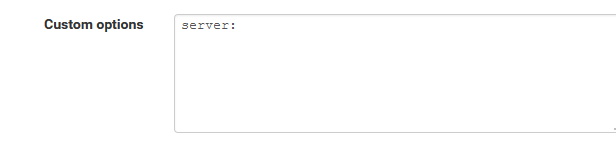
I edited the file mentioned above.
And activated DNSBL in pfBlokcerNG again :The result :
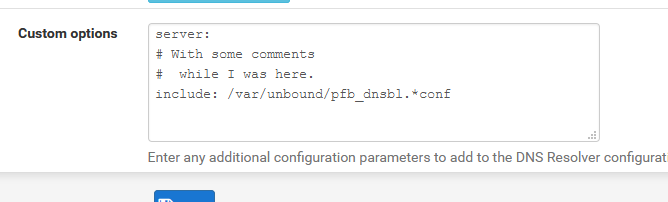
$unbound_include = "# With some comments\n# while I was here.\n include: {$pfb['dnsbl_file']}.*conf"; -
@horse2370 : pfBlockerNG-devel v2.2.5_30 is installed on my system. Seems to be the latest one. Also the thread you referred me to, seems to be a bug in Unbound or its implementation in pfsense? Still unfixed? The thread ends up dead with no answer.
If "upgrading, installing, disabling / enabling etc." will always put the "server:" statement back in unbound's custom options, then to me, pfBlockerNG's devs never intended their package to work with Unbound views. This is highly confirmed by @Gertjan's workaround to manually edit "/usr/local/pkg/pfblockerng/pfblockerng.inc"...
IMO, and this is only personal opinion, we should never have to fiddle with internal files like this way, even if it works. Especially on production systems. Will this file be overwritten once pfblockerNG is updated?
At least now I start to have a better picture on how these components interact with each others....
-
Just saw the last line of your post... No, I do not use IPV6 at all. Pretty much everything else is stock, with the exception of pfblockerNG and Snort. I also use VLAN's. Could you specify which setting you need more specifically? I will be glad to provide!
EDIT: some Unbound settings
Port 53
Enable SSL/TLS: Unchecked
SSL/TLS Cert: stock setting
Network ifaces: VLANs (see my initial post on this thread for details)
Outgoing ifaces: WAN
System Domain Local Zone Type: Transparent
DNSSEC: Checked
Python Module: Unchecked
DNS query FW: Unchecked
DHCP Registrations: Checked
Static DHCP: Checked
OpenVPN : Unchecked
Custom Options: (see my initial post on this thread for details) -
@pftdm007 said in Bypassing DNSBL for specific IPs:
Will this file be overwritten once pfblockerNG is updated?
It's part of the package - so a re install or upgrade will undo changes.
Or, before editing, make a copy of it.@pftdm007 said in Bypassing DNSBL for specific IPs:
pfBlockerNG's devs never intended their package to work with Unbound views.
It's just a way to have unbound to include a file with IP's - the scope is just 'server' (unbound dns) wide.
Btw : in my case, this file is empty, I'm not using DNSBL part of pfBlockerNG-devel - so it'a a no-op for me.
I could even wipe this line in the custom options.
( but shouldn't be surprised the DNDBL functionality wouldn't work anymore )