OpenVPN and static IP for ALL clients
-
I have seen documentation on how to assign a static ip per vpn configuration but I need all my clients to have static ips, whatever IP the get the first time they connect should be the ip they always get.
Is there a setting for this?
Is there a setting for the config to always assign an available ip when creating a new client account?Thanks
-
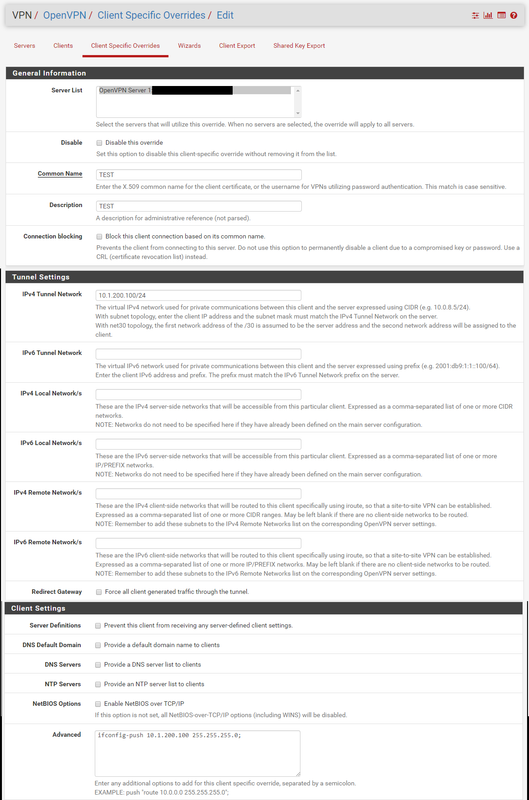
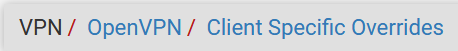
VPN > OpenVPN > Client Specific Overrides
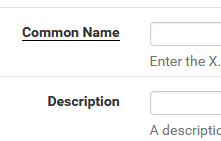
Make sure the Common Name matches the User Cert exactly. Define the User static IP in IPv4 Tunnel Network.
Say your tunnel network is 10.30.8.0/24 and you want this User to have 10.30.8.11 fill in 10.30.8.11/24-Rico
-
Thanks for your reply
This must be done per account
I am looking for a way for this to be done with every single account in some automated method -
Not that I'm aware of.
I always do this right after creation of the new User and Client Export. So this cost me like 5 more seconds, no big deal.
Why do you need static IPs anyway if you don't care about the actual IP the User gets? I need them because of a different Firewall Ruleset per User, so .11 and .12 could be a huge difference here in what the User can access or not.
-Rico
-
I use the endpoint to send data to them
I need to configure where to send data to.How does numbering work ? Every VPN need 3 ips?
-
Tunnel subnet size - 4 = nr. of clients
/24 - 4 = 252 clients
/25 - 4 = 124 clients
etc. -
@Rico
I just tried this myself and was not able to get the client to have a static IP.The server tunnel network is 10.1.200.0/24.
The client has its own cert.
That certs common name is entered in the Common Name field in the client override section.
Also the IPv4 Tunnel Network is 10.1.200.100/24 for the client override.Client just ends up getting the next available address from DHCP still...
-
hi there
client specific override the way it works.- IPv4 Tunnel Network ip that client shall receive eg 1.2.3.4/24
- in Advanced fill in: ifconfig-push 1.2.3.4 255.255.255.0;
- Server List select a / the server
3)Common Name & Description must be exactly the same as used when u created the user
i personally do a copy n paste in user management for username full name and the cert for the user4)restart openVPN serverEDIT: (not nescenecessary)- export your credentials .... done
what i learned that sometimes at the first connect of the client with client spec override
the assigned IP will not be assigned. DIsconnect the client, restart the openVPN service and it works, disconnecting and connecting after 5 minutes also works.if there are any improvements, or things to do better feel free to comment
brNP
-
Restarting the OpenVPN server because of adding some CSO? That would be a massive pain and I never had to do that.
I also nerver had to fill Advanced / ifconfig-push...-Rico
-
ok restartin is a true pain in the .. .
and it is workin without restarting. (true)without Advanced / ifconfig-push... not workin here
to true for all devices on some it does on some it does not
with Advanced / ifconfig-push... workin like a charm and no problemsout of the blue any side effect / disadvantages cuz of usin ifconfig-push ?
brNP
-
On my linux box, I have a script which creates client accounts and sets ips
can something like this be done? -
@noplan said in OpenVPN and static IP for ALL clients:
ifconfig-push 1.2.3.4 255.255.255.0;
What is wrong with the below setup?
The domain username is not TEST (it is DOMAIN\USERNAME, actually I don't even enter the DOMAIN\ part when authenticating with the OpenVPN prompt), but that shouldn't matter correct? It's just based off the CN name?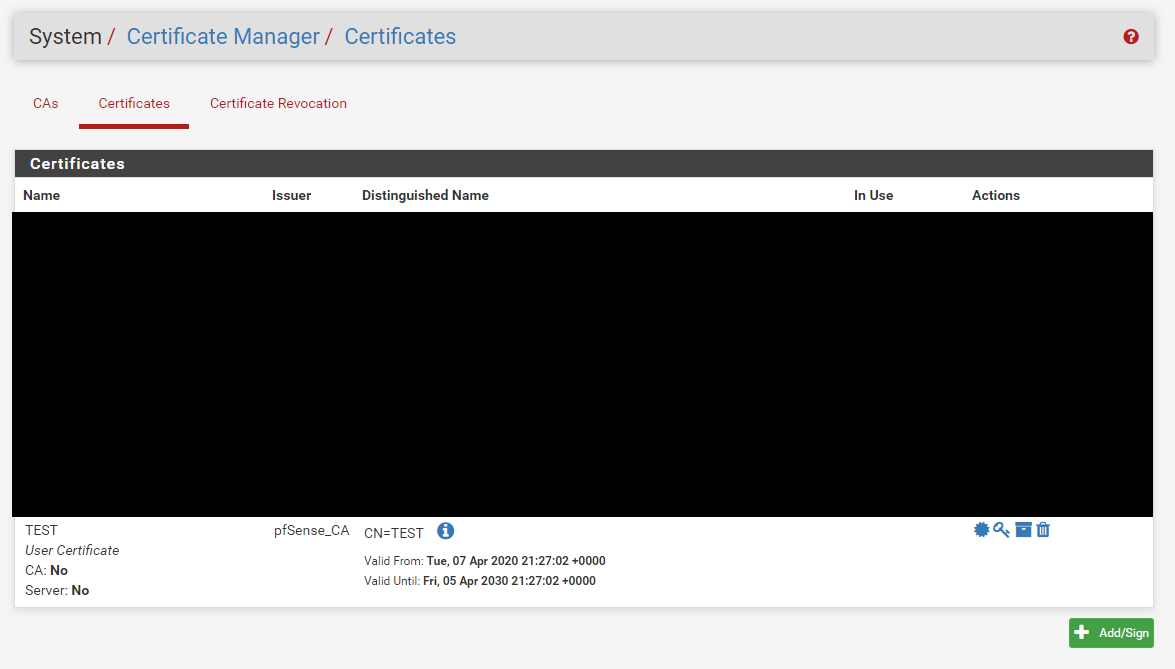
-
i use this here (and remember i use exact copy n paste) in:
and still in User Management:
u have to klick Crate a user certificate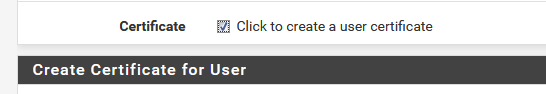
and in client spec overrides :
and it works ...
read my other comments in this post why i use Advanced / ifconfig-push...(edit 10/04/20 more screenshots as requested)
brNp
-
@noplan said in OpenVPN and static IP for ALL clients:
i use this here (and remember i use exact copy n paste) in:
and in:
and in client spec overrides :
and it works ...
read my other comments in this post why i use Advanced / ifconfig-push...brNp
Can you take larger screenshots to see more of the page? I'm not sure where this username field would be...
-
done added more screenshots
-
@noplan said in OpenVPN and static IP for ALL clients:
done added more screenshots
So my users are domain users. How would using the User Manager certificate work?
This link shows that using User Certificates is not part of the process.
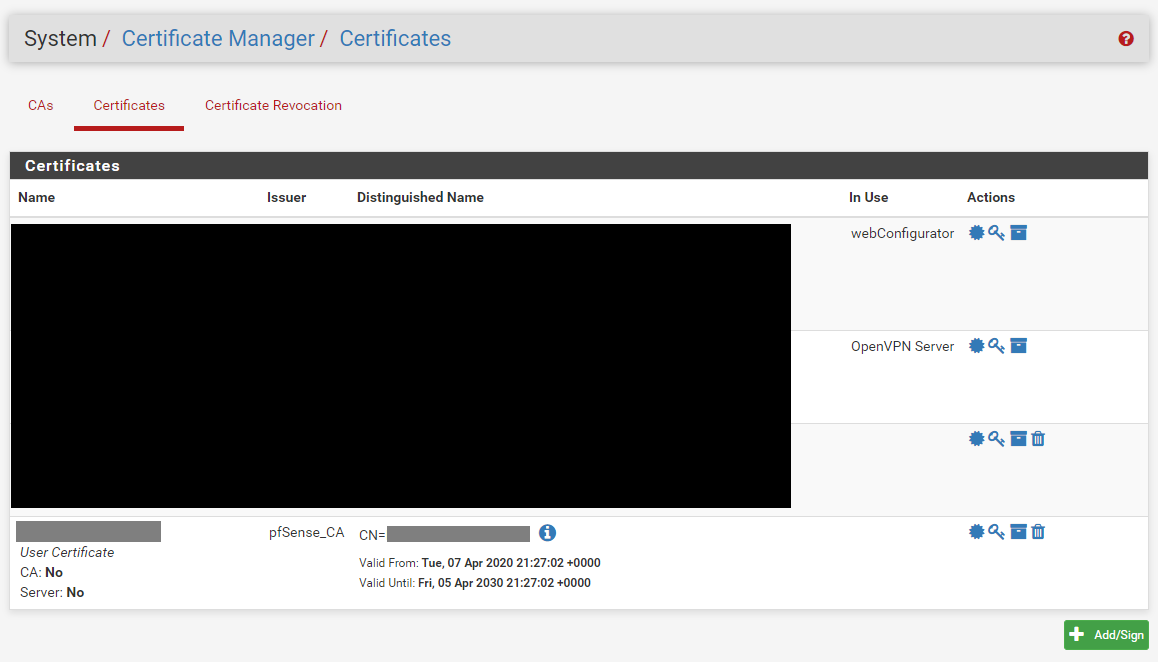
https://fastinetserver.wordpress.com/2013/03/09/pfsense-openvpn-static-ip-for-clients/Pictures for location reference
User Manager User Certificate
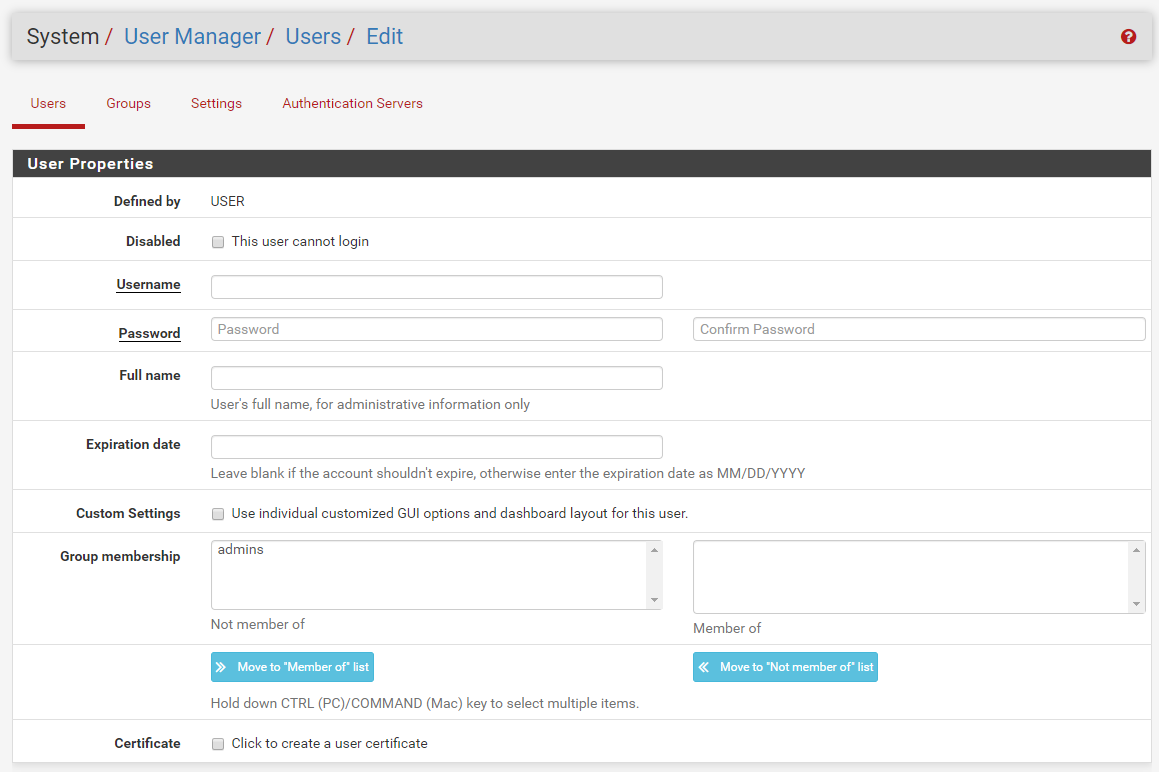
Certificate Manager Certificate
-
hey @ThePieMonster
dont get me wrong ...
add a user / click to add a user certificate
and follow the instructions here in that post. and test it if it works for you then go to the next step.
(all of the information you need is provided here)as far as i m concerned the link --> klick you provided is a) from 2013 and b) mentions as u can see in the screenshot
that User Certificates is part of the process.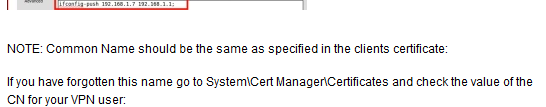
possibly the next step my be
check how to import the DOMAIN User Cert to pfS ore use the domainUserDB as Backend in pfS
and test the whole loop again, let me mention that it would be pretty sweet when you keep us all informed how it works / or even not. But this is not part of this topic i think, cuz static IP for VPN-clients is pretty much solved here.br nP
-
If you need per-client firewall rules, a more efficient way is to use Cisco-AVPair RADIUS ACLs:
https://docs.netgate.com/pfsense/en/latest/book/openvpn/controlling-client-parameters-via-radius.html -
oh yeah i like that, but lack of useCase :(
i think @ThePieMonster needs a static IP for his vpn-clients
but a static Ip only helps when rules are set ;) so whats NEXT ! -
As I mentioned the user cert is from the the Certificate Manager / Certificates section of pfSense, not from the User Manager section. There are two locations where a user certificate can be created.
I also found out today, that the common name, is not the CN name of the cert, that can be whatever you like, but the username of the domain user. Switching this info around in the client override solved the issue for me.
TLDR: CN = Domain Username, not Certificate name.