Posisble bug or ?
-
I am puzzled a little so need to run it by smart people...
I have vino-server running and trying to see how those connections show in pfsense.
On a system I connect to I see:
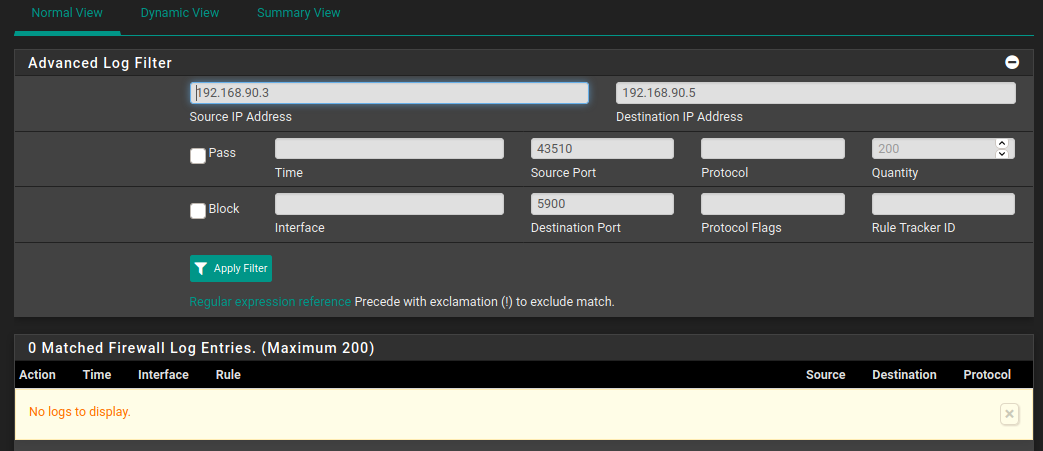
tcp 0 3586 192.168.90.5:5900 192.168.90.3:43510 ESTABLISHED 2560/vino-serverAnd yet, when I try to see "port 5900" via pfTop or Status/System Logs/ Firewall "Destination Port 5900" I see nothing !!!
I am sure it used to work before. So either I am missing some option or bug.
Anybody can confirm or otherwise?
Thx
-
The connection is logged when the connection is established - and only if logging is enabled on the rule passing it. The logs are circular and the oldest records are overwritten by the newest records.
To see active connections, use Diagnostics > States.
-
connections on the same subnet does not pass through pfSense
? -
Also true.
-
@Derelict said in Posisble bug or ?:
The connection is logged when the connection is established - and only if logging is enabled on the rule passing it. The logs are circular and the oldest records are overwritten by the newest records.
To see active connections, use Diagnostics > States.
I understand "when the connection is established" concept
And I see nothing related to port 5900 at all via Diagnostics > States -
@kiokoman said in Posisble bug or ?:
connections on the same subnet does not pass through pfSense
?Please elaborate !
-
from 192.168.90.3 to 192.168.90.5 the connection is direct and does not pass through pfsense.
you won't see any firewall log or states under pfsense -
@kiokoman said in Posisble bug or ?:
from 192.168.90.3 to 192.168.90.5 the connection is direct and does not pass through pfsense.
you won't see any firewall log or states under pfsenseHmm, I was going to say that I’ve seen it doing so, but you sound very confident
Is there any way to still see/enable this to be traceable?
-
Not in pfSense. At least not without changing your network configuration.
That traffic goes from 192.168.90.3 to 192.168.90.5 directly at layer 3. It probably goes through at least 1 switch at layer 2.
It never goes to pfSense at all so there's nothing it can do to see that.
What you could do, for example, is configure a mirror port on the switch and then analyse the traffic on that to get flow data.
You could bridge two ports in pfSense and make sure those systems were connected to different sides of the bridge. Then traffic would go through pfSense so you could see it and filter it. That is generally considered a bad idea unless you absolutely need it though.
Steve