SNORT blocking too much
-
I have followed exactly the guide and also for steps, all is set like you mentioned. I miss still this information
-
@interessierter said in SNORT blocking too much:
I have followed exactly the guide and also for steps, all is set like you mentioned. I miss still this information
Then you don't have traffic matching those rules in your network. Remember I said the rules will not detect everything because they are not actively maintained by the original author.
Go back and read my additional comments at the end of my post above and follow that link I included.
-
Hi!
I don t believe that. First of all the table is simply missing in my view. And I expect that the rules now amazon, Netflix, O365 whatever. I have simply nothing. Yes I will review the Blog.
PS: The thread is from 2017, thats the reason why the first ask is not 100% match the last one
thanks
-
@interessierter said in SNORT blocking too much:
Hi!
I don t believe that. First of all the table is simply missing in my view. And I expect that the rules now amazon, Netflix, O365 whatever. I have simply nothing. Yes I will review the Blog.
PS: The thread is from 2017, thats the reason why the first ask is not 100% match the last one
thanks
What table is missing from your view, and where (which tab)?
If you are talking about that very last graphic on the page, that is not an actual table in the application. The person creating that article just cut and then pasted individual alert lines from the regular ALERTS tab entries and then put them in separate sections for illustration. There is not and never was a table in Snort formatted that way.
Is this what you think is missing? This is not a real table in Snort. This was created by the author of the documentation article for illustration purposes.
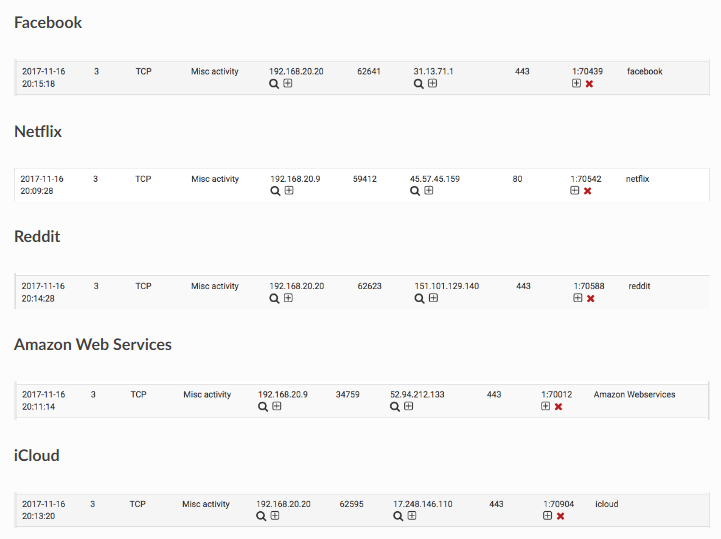
To help you find stuff on the ALERTS tab, several of the columns are sortable. Click the column headers to sort on that field. Where you see "facebook", "reddit" and other values in the screenshot above, look for those under the Description column of the ALERTS tab. As I mentioned, the image in the documentation was created by copying just a single line from the ALERTS tab view in the pfSense GUI. So each of the little light-gray background boxes in the image is a cut-and-pasted single line entry from the ALERTS tab.
-
I have spent three years so far learning IDS/IPS ... from being a neophyte implementing all rules to where I am today ... and guess what, I am still learning. It a never ending process ... one cannot simply install the package, have some ice cream, and forget about it. Right now, Suricata's STREAM excessive retransmissions is pulling my hair.
-
I have no started to whitelist all my topics, now its working. Sometimes the performance is not the best.
However how is than a big company doing that? There are always changes in the infrastructure and applications, the users start very often different clients to use. Can not believe that there is always one guy sitting the entire day to whitelist parts of the connections. Thats way I was asking for pattern file to whiteliste "defaults"
-
@interessierter said in SNORT blocking too much:
Can not believe that there is always one guy sitting the entire day to whitelist parts of the connections.
That's why others told you to turn off blocking so you can sort out your network need. It seems that you also had enabled all rules then started complaining ... not cool!
-
@interessierter said in SNORT blocking too much:
However how is than a big company doing that?
Mostly by actually paying some guys in a corner that's maintaining the lists. Not knowing that that guys exists gives the impression security is for free. But the one who makes the pay checks knows better.
Or, as usual, by paying monthly fees to have have access to well maintained feeds.edit : it's most probably a combination of the two options mentioned above.
-
Guys please stop this.
I m working in the IT area since more than 10 years +. I have not the impression that security is for free, and I also didn t expected that I install it and take ice cream or what ever.When I m a company with 100.000 employee s it get hard to "know" my traffic. Because of that, I was expecting that there are pattern available that allow the minimum of default traffic like normal webpages. When the snort rules gets sold to enterprise customers, than I was expecting here a bit more.
Good, it seems like that is here, and in Snort not the case. Sowe can close the thread. The rest of the posts does not help here
-
@interessierter said in SNORT blocking too much:
Guys please stop this.
Not meant to be personal ^^
Didn't know what you know, but now I get the picture.@interessierter said in SNORT blocking too much:
When I m a company with 100.000 employee s it get hard to "know" my traffic
The easy one : that corner guy exists !!!
But ok, serious : as you said "100 000" means a totally random bit stream is what snort will be seeing.
DPI became already quiet impossible then : TLS killed the access real to the data payload years. A solution that still might pull it off : Use a proxy on/in front of your snort device, have it "unpacked" all traffic, scan, and pack it back into TLS again.
This proxy device would be situated on pfSense, but in front of it. Centralized administration of all devices in the network would be needed to handle the 'cert' issues.For a small group of persons (small society or even family) it's actually possible to find some common patterns, but a huge group will always trigger some (random) pattern/rule. You're talking of several OS's - thousands of application, that can all have there "network errors", that might trigger some rule.
Keep in mind : snort is somewhat limited to the packet headers, or "headers in headers" and some transport flags. It's like reading a postal envelop, and drawing a conclusion when seeing the destination and sender, and the type of letter, and their occurrence.Btw : for purely learning how DPI works, I've been using snort and friends for some years in the past. It became a close to 7/7 daily job to maintain traffic flowing. And I was using the rules accessible by subscription.
I'm still using it (DPI) today, on my mail server, as that one still 'sees' the traffic 'in clear' in the mail boxes.IMHO : I lost somewhat of the faith in the usefulness of DPI as it exists today. It's goes totally against the all TLS hype.
@interessierter said in SNORT blocking too much:
When the snort rules gets sold to enterprise customers, than I was expecting here a bit more.
Rule support should be found there where they are created ;)