Why are changes to avahi-daemon.conf not persistent?
-
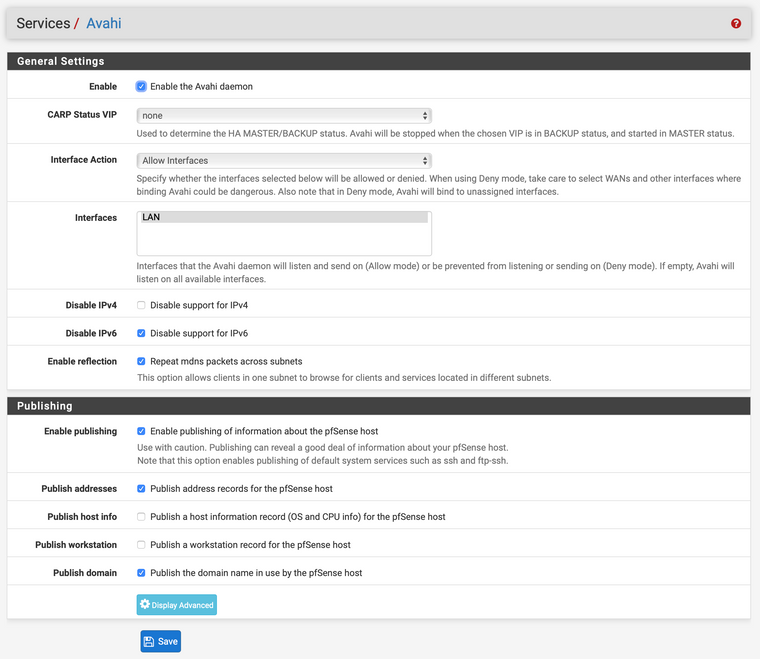
Edits to the Avahi configuration file at /usr/local/etc/avahi/avahi-daemon.conf for some reason do not survive a restart of the Avahi daemon. I do that by unchecking “Enable the Avahi daemon,” clicking the “Save” button, checking “Enable the Avahi daemon,” and clicking the “Save” button again.
Is there a way to prevent that?
In particular I would like to make these changes:
[server] allow-interfaces=mvneta0.4091, ovpns2 [wide-area] enable-wide-area=yesin hopes that that might get me closer to having my VPN-connected host see the other Macs on my home network. My family often asks me to fix things on their computers, while I am at work or traveling, and it would go a lot more smoothly, if I didn’t have to ask them what their LAN IP address is.
-
@DominikHoffmann for some reason this cannot be done from WebGUI?
-
@viktor_g I’d be happy to do it from the WebConfigurator, but I don’t know how, if there is a way. Please let me know, what you suggest.
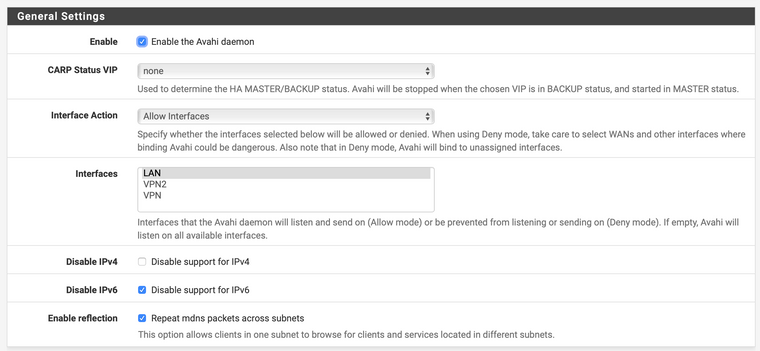
This is what the Avahi WebConfigurator looks like for me in the current version of pfSense (2.4.5-RELEASE):
Regardless, is there another configuration file for Avahi from which /usr/local/etc/avahi/avahi-daemon.conf is freshly minted, every time it starts up? If so, obviously that’s where I’d want to make changes.
-
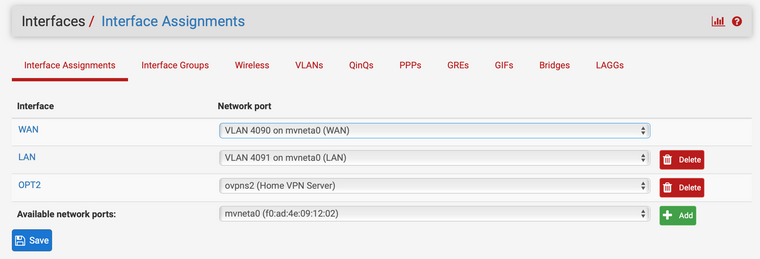
@DominikHoffmann You need to assign
ovpns2interface on the Interfaces / Assign tab, and then select both LAN and ovpns2 interfaces in the Avahi WebGUI -
-
So, I just realized that I have to click on “OPT2” and actually enable that interface, which it hadn’t bin. However, this also breaks any kind of routing between OPT2 and LAN. I am not sure, how to deal with that.
-
@DominikHoffmann said in Why are changes to avahi-daemon.conf not persistent?:
However, this also breaks any kind of routing between OPT2 and LAN. I am not sure, how to deal with that.
It's all about finishing your OpenVPN server setup ...
Initially, the OpenVPN Server process creates some kind of virtual interface that it uses to 'inject' traffic into the pfSense router - and send replies back to the connected OpenVPN clients.
As you can see bellow, this is the OpenVPN "Interface" shown - you can't set an IP (network) for it, as this is handled by OpenVPN server internally. Neither a DHCP server, etc. And it can't be used by other services that do not understand these kind of interfaces.Like
(EDIT3 days later : see edit bellow )
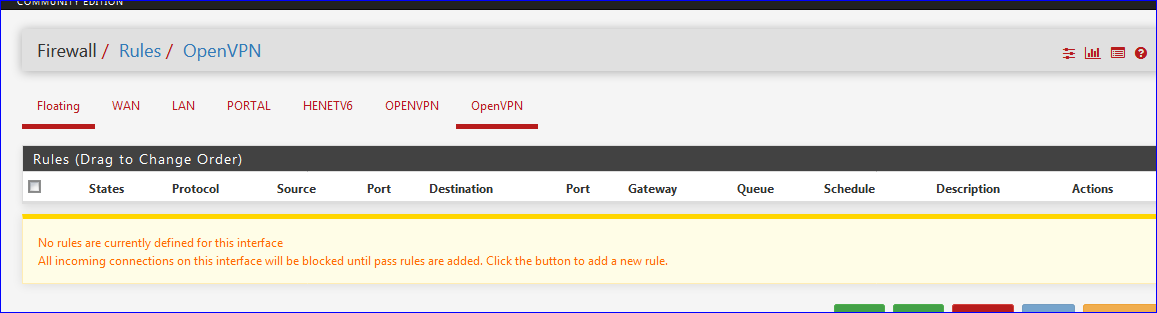
Traffic coming from the clients flow out of the 'OpenVPN' interface into the system. No firewall rules are needed to make this possible. Firewall rules work on incoming traffic into the interface. This will be the OpenVPN client 'reply' traffic, which will always match the outgoing requests.
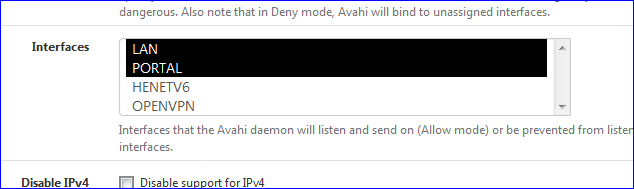
If you want to use Avahi to use this OpenVPN type interface, should should 'instantiate' the original OpenVPN interface, like I did (see image, mine is called "OPENVPN").
You still can't set an IP details on this interface - and the underlying -if any - firewall rules on the OpenVPN interface should be ported to the newly created OPENVPN interface.
True, I should have called OPENVPN to something like like VPNServerInterface which makes more sense.Now, you can see and use that interface in Avahi :
Btw : seriously : editing config files on pfSense ? You didn't know that these config files (hundreds) are created and maintained by the the GUI? That's what is exactly pfSense all about.
If not, one would install a native FreeBSD OS, SSH into it and set all these files up by hand. Like other routers still do today.
It works like this : pfSense maintains one big master configuration file, the config.xml - from this file, settings are shown in the GUI. If there are changes made- or a GUI is just saved by the admin, these settings are written back to the config.xml and the individual config files for the process, like avahi and it's config file.
When the systems starts, and process are started, their config files are rewritten/recreated.EDIT 21/06/2020 : A rule like this should be present :
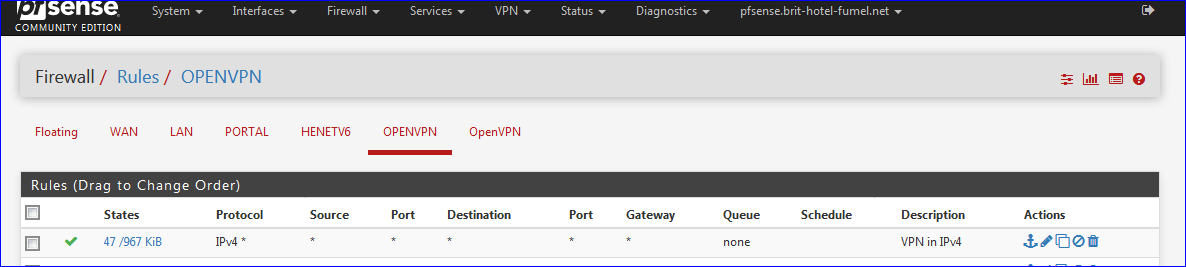
on the OpenVPN interface - I guess it is when you use the OpenVPN Wizard - so traffic can comes in and out.
-
Thanks very much, @Gertjan, for that explanation. I am still very much in the learning process about how pfSense works. I started using it a few years ago, because I was looking something that was under active development and would receive security updates reasonably frequently.
Right now I am also trying to digest what you said about defining an interface for your OpenVPN connection. In my current configuration everything works as expected, still sans mDNS routing between the LAN and the OpenVPN subnet.
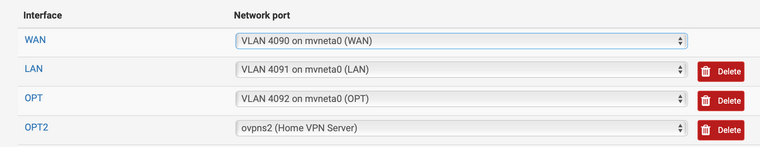
Enabling or even renaming OPT2 breaks, not the VPN connectivity itself but routing from the OpenVPN subnet to the LAN. In other words, subsequently, pings to 192.168.1.1 (the address of the pfSense box) time out.
Any idea, why?
-
See my edit above, my previous post.
A pass rule should be present on either the default OpenVPN interface tab, or the instantiated interface, yours is called OPT2.
Like :
Btw : I'm using Avahi myself to 'help' the access of devices on my LAN called 'PORTAL' (a captive portal network) so they can use my printers, present on the LAN network.
A firewall rule on the PORTAL interface enables access to the IP of these printers on the LAN interface.My iPhone doesn't enumerate these printers why I use the VPN connection (note : not using Wifi, using 4G and VPN)
I can use the LAN IP's of these printer to visit their 'web' interface from my iPhone. This time I'm using Wifi - not VPN, neither 4G. -
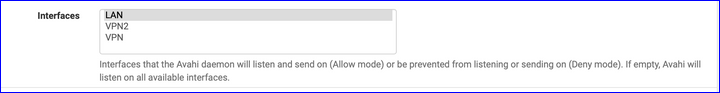
@Gertjan: I have these settings:
Avahi:
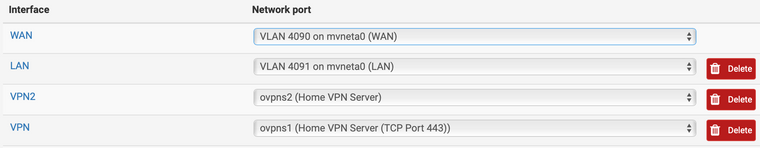
My interfaces are these:
And I have all sorts of firewall rules, very possibly redundant—I will eliminate the unnecessary ones through trial and error.
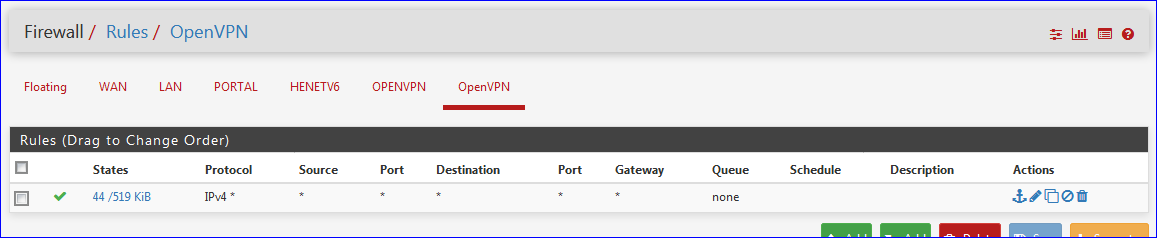
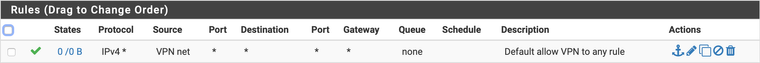
Firewall rule for the interface named “VPN”:
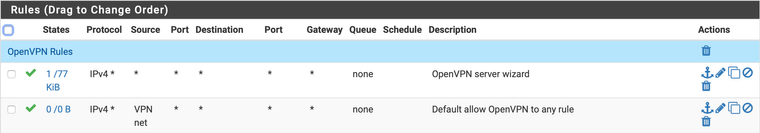
OpenVPN firewall rule:
Output of the macOS Discovery app, when the Mac is on the LAN:
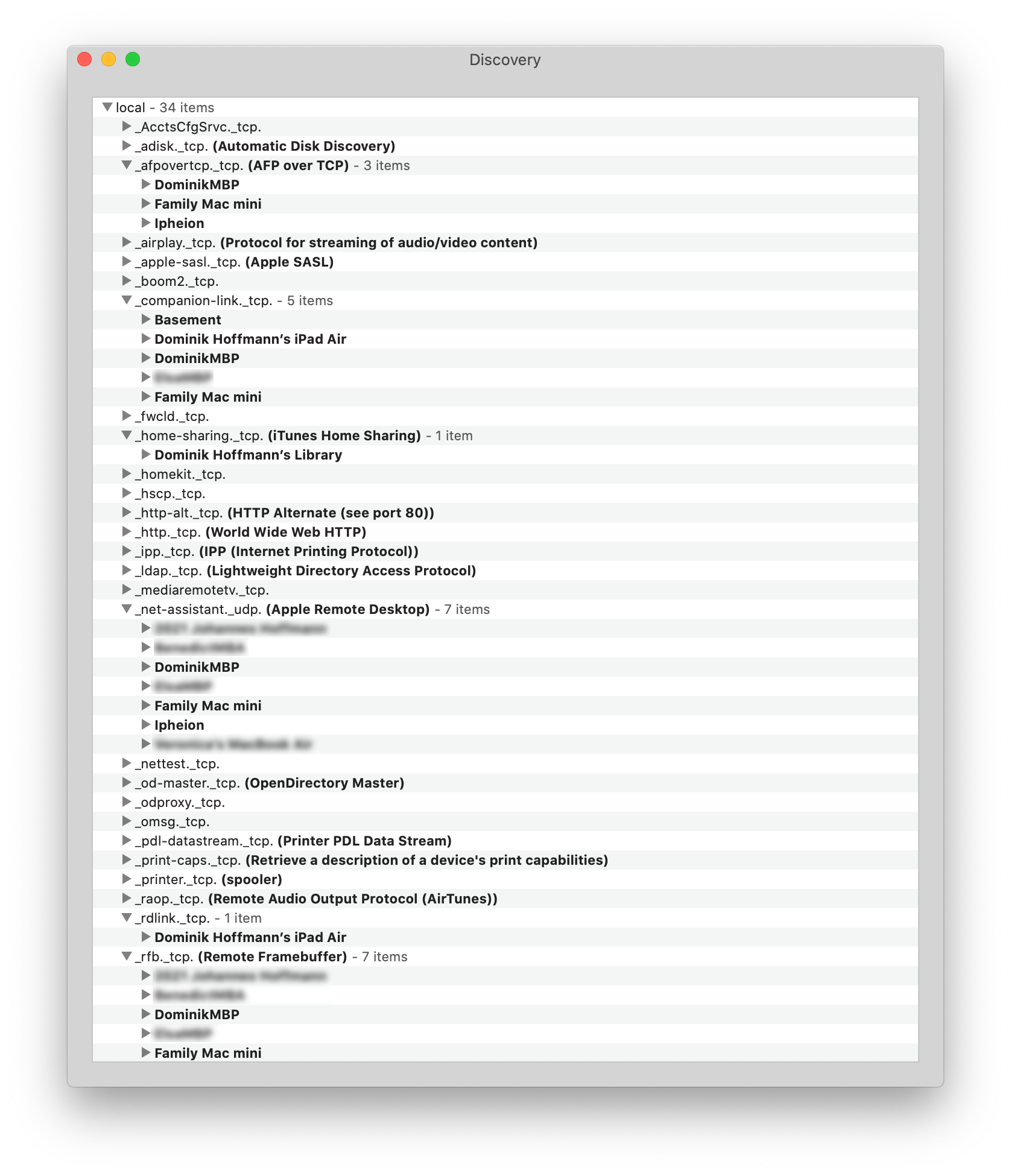
Discovery output, when my Mac is connected through OpenVPN:
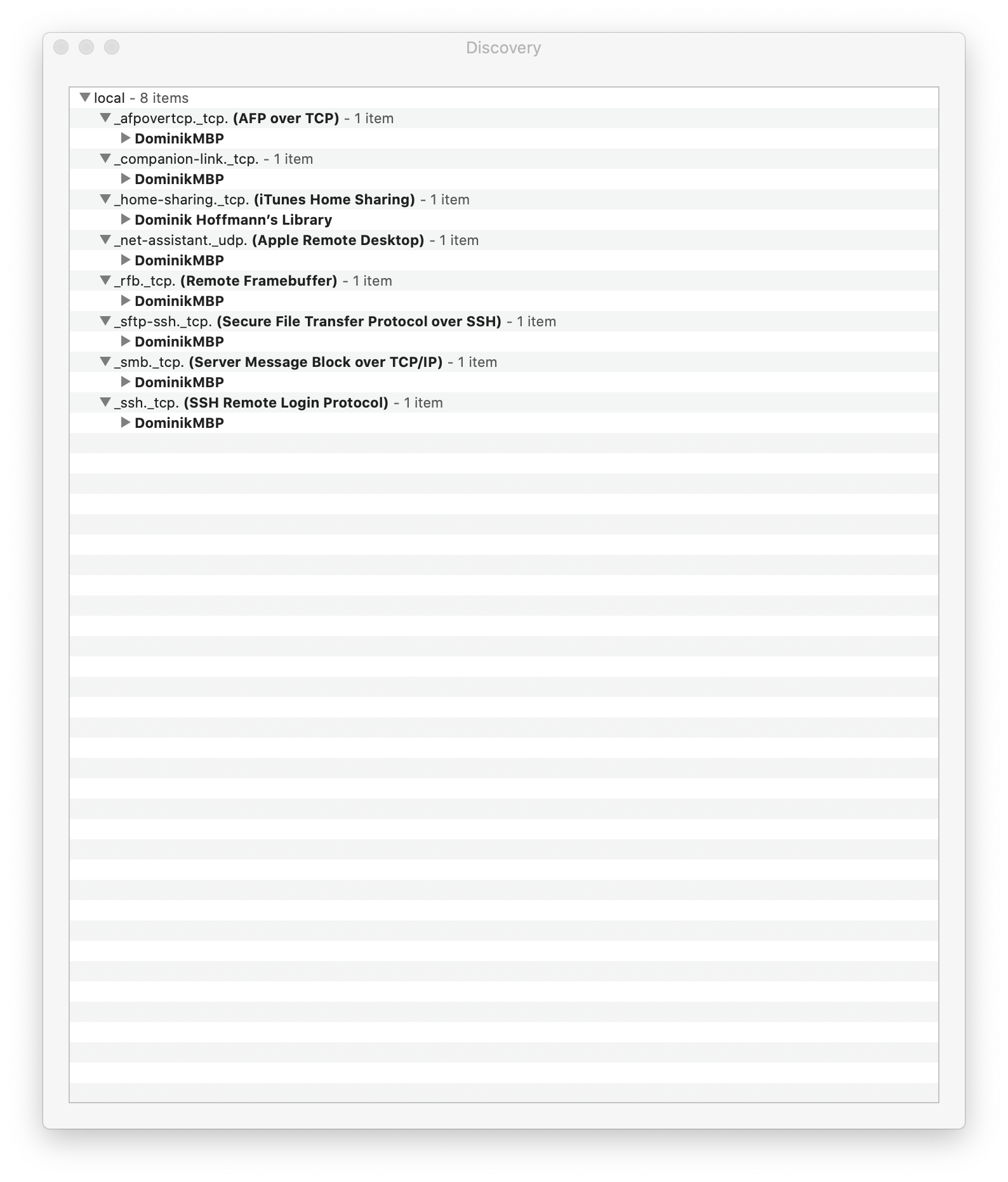
I would like the output to be the same in both situations. -
@DominikHoffmann said in Why are changes to avahi-daemon.conf not persistent?:
I would like the output to be the same in both situations.
Then why exclude / disallow the "VPN" type interface from Avahi as you did ?
Anyway, my phone connected to wifi, connected to VPN to the pfSense VPN server did not find any devices.
Avahi does the job for devices connected to my "wired" second LAN - not my VPN connected devices. -
@Gertjan: My Avahi configuration is set to “Allow Interfaces.” Do I have to highlight the interfaces I want to use? Why does the GUI not use checkboxes, which would be more unambiguous.
Is this
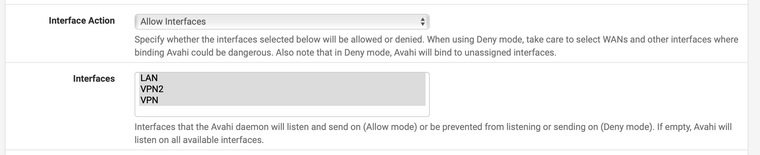
the way it should look?
-
@DominikHoffmann said in Why are changes to avahi-daemon.conf not persistent?:
the way it should look?
Yes.
All possible interfaces are listed, grey/black ones are actually bound to Avahi.See also avahi over vpn which shows clkearly that your question is known ...... answers are less.
-
I have found and tried to understand some of those search results. There have been users who claim they have succeeded, but then they aren’t around anymore to help. Witness Protection Program or something…
-
From 2010 : read the second post : https://forums.openvpn.net/viewtopic.php?t=7136
Good luck with setting up OpenVPN using tap ^^
-
@Gertjan:
Thanks very much for your help! Somehow I had irrationally wanted to stay away from using tap. Maybe I had read something about issues with tap versus using tun. However, with tap it works. Does exactly what I want it to do.When I have time, I will do a write-up of how to.