DNS Forwarder Host Overrides and Domain Overrides
-
And that is not their IP... Anyone from the internet could hit that!
For example say I was one of your users.. And I needed to get to this RDP... You would lock the rule down to my IP 64.53.A.B - going to your IP 24.211.x.x only my IP could hit that, if they were coming from 64.53.A.C they wouldn't get forwarded.
You can create a alias that contains all the IPs of your users.. Which works when you know what the user IPs are.. Or they have dynamic IPs setup via ddns.. Where name say john.somedomain.tld gets update if my IP say changed to 64.53.A.Z
The simpler solution where you don't need to know the uses IP is setup a VPN... Where they have to have the credentials to auth to the VPN.. this is cert that you have issued them, and a username and password.. And ONLY once they have authed to the vpn can they even access the remote desktop box... And then they have to auth to that..
With how you have it setup - anyone from anywhere could hit your IP.. And try and access rdp - and once they see oh rdp... They can brute force trying to guess the username/password - or as with that issue I linked to there is some exploit they don't even have to auth..
Remote desktop open to the public internet is very risky!!! I would never suggest anyone do that! Ever!!! Changing your port and trying to hide doesn't really make it any more secure.. The old saying "security through obscurity is not security"
edit: I just looked - look at the hits to your "changed" port 3391
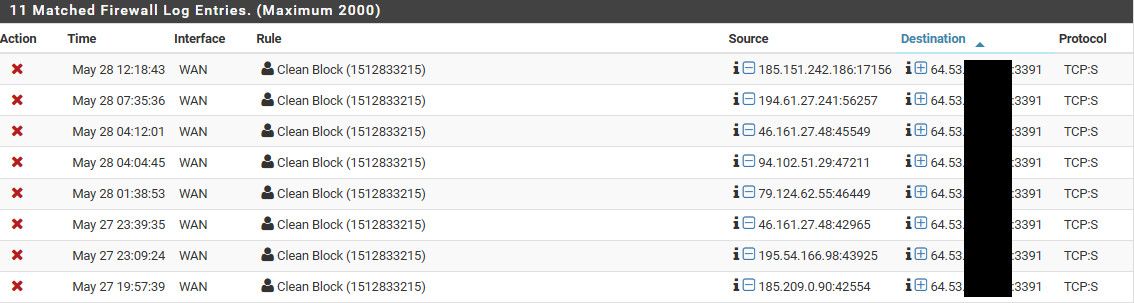
In the last 24 hours or so.. Those IPs are from all over.. That first one 185.151 is from russia.. that next one is from the netherlands... Trying to hide your port is not security.
I don't have that port forwarded, its just dropped by pfsense (it doing its job).. But my point is showing that there is plenty of bad stuff out there looking for stuff you have open trying to do bad stuff..
-
I understand. I will have to do some research on the VPN and what it will take.
I keep hearing how expensive setting up VPN's can be.
RDP was pretty easy, but I see the security concerns it can create.
I appreciate the honest assessment. -
@gus17 said in DNS Forwarder Host Overrides and Domain Overrides:
I keep hearing how expensive setting up VPN's can be.
Huh? Pfsense is your vpn server, does it out of the box.. All you need to do is set it up.. Clicky clicky ;)
https://docs.netgate.com/pfsense/en/latest/vpn/openvpn/openvpn-remote-access-server.html
Here is video netgate put out pretty recent
https://www.youtube.com/watch?v=jQHqPq7ftz4Depending what exactly your users are doing - you might not even need them to rdp to anything... If they are just accessing say some file shares or whatever.. A vpn lets the user be like they are on the local network - just a bit slower because you constrained be the speed of the sites internet connection, and or the remote users connection..
-
Going through OpenVPN setup wizard?
-
Yup all there is too it.. Should really take you all of like 2 minutes ;)
The hardest part is training the users ;) But it comes down to giving them a config file, or even just an exe to run that will install the client on their machine and have the details of how to connect.
One possible issue is if they are using the same local network as what your using for example if your local network is 192.168.1/24 - this is common.. It's best if your work location network is something odd say something like 192.168.42/24 or 172.29.14/24
-
Ok, let me take run at it.
I am referencing the book you have linked.
Here goes. -
Easy way is test connection from your phone, there is an app for ios or android.. I connect in all the time from my phone..
-
Will do.
Thanks again. -
Quick question, not sure what to put in for tunnel network?
-
I believe it defaults to 10.0.8/24 - this is fine.. Any network that is unlikely to overlap either your remote user or your sites network is fine.