Unexpected DNS queries from PFsense
-
I have recently installed PFsense on an AWS VPC as a firewall/NAT device/DNS Forwarder. I am running PFblocker and Suricata for GeoIP blocking and IDS. All devices on the LAN subnet are set to use PFsense for their DNS server. PFsense is configured to use 1.1.1.1 for DNS and 0.us.pool.ntp.org for NTP.
Within less than a day, Suricata began to flag an enormous amount of traffic on port 53 (DNS) and port 123 (NTP) to some legitimate and mostly questionable (dfw0.clover.mattnordhoff.net) domains. The logs show over 40 requests every second which were not present at the original install.

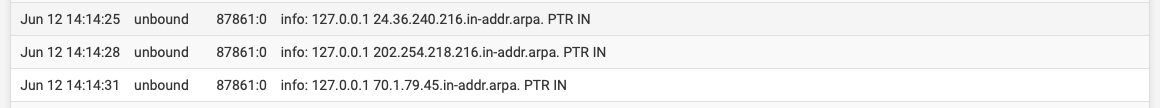
I have changed the unbound settings to log individual DNS queries and it appears that they are coming from PFsense itself (127.0.0.1) although I do not see nearly as many queries in the unbound logs as I do in Suricata.
Restarting PFsense causes the alerts to stop temporarily. I will update the post with approximately how long it takes for them to re-appear as I gain more information.
Has anyone experienced similar behavior on their systems or has some idea what is causing this? I am concerned that this may be a sign of a breach somewhere in my network, however I am still a new PFsense user so I wanted to confirm that this was abnormal behavior.
-
Two comments for you:
-
First, those DNS lookups are likely from a package that is doing reverse lookups on IP addresses in order to log domain names. As for your DNS setup, are you sure you have the DNS Resolver set to forwarding? The port 123 items are simply the
ntpddaemon contacting time servers in the pool. There can be a wide variety of NTP servers in the pool. -
Second, your Suricata alerts are actually bad checksum alerts and would indicate to me that you do not have all of the hardware offloading options disabled on the pfSense Advanced > Networking tab. You want to disable all of the hardware offloading options when using either of the IDS/IPS packages.
-
-
Thank you for your response! I appreciate your expertise as I am still new to pfSense and especially IDS/IPS.
I did confirm that unbound is configured to be the DNS Resolver and I am not using a DNS Forwarder. I have also disabled the hardware offloading options as you have suggested.
Thank you again for your input.
-
@johnmmason said in Unexpected DNS queries from PFsense:
Thank you for your response! I appreciate your expertise as I am still new to pfSense and especially IDS/IPS.
I did confirm that unbound is configured to be the DNS Resolver and I am not using a DNS Forwarder. I have also disabled the hardware offloading options as you have suggested.
Thank you again for your input.
Using Unbound in forwarding mode requires special configuration steps on the Unbound (DNS Resolver) tab. That's if you want Unbound to simply forward all DNS requests to 1.1.1.1 as you indicated. I personally would not do that and would instead allow Unbound to resolve like it is configured to do out of the box.
Also make sure you Google the terms "DNS forwarding vs DNS resolving" so you definitely know the difference between those two ways of looking up IP addresses for domain names. Many users come here confused on that point and conflate the two methods when they are in fact quite different. Don't know your skill level in the area of DNS, so just mentioning that in the event you are new to the field. Like I said, many users come here posting about DNS issues and it very quickly becomes apparent they went off and made unwise modifications to the out-of-the-box pfSense Unbound setup without actually understanding as much about what they were doing as they "thought" they did ...
 .
. -
@bmeeks Thank you, I will research that distinction. Based on your brief description, I think I was simply using the wrong term for what I wanted unbound to do! I am still very new to DNS and have tried to stay with the stock settings as much as possible, except for what is necessary for PFblocker. Thank you again for your input!