OpenVPN Slow - local network test
-
@Rico
Also, wondering if I need to set the tunnel size.
Pinging at 1500 shows fragmentation. Setting it to 1472 shows no frag. (hitting a box on the remote network of course).What do you think?
-
I would take a look at this
https://community.openvpn.net/openvpn/wiki/Gigabit_Networks_Linux -
@johnpoz
Thanks, I did read this but going to go over again to see if I missed something.
I know it talks about jumbo frames....will try that and let everyone know what i find. -
Pls run those two via the command line or SSH and post the output here
openvpn --genkey --secret /tmp/secret time openvpn --test-crypto --secret /tmp/secret --verb 0 --tun-mtu 20000 --cipher aes-128-gcm-Rico
-
[2.4.5-RELEASE][admin@pfSense.seradex.local]/root: openvpn --genkey --secret /tm p/secret
[2.4.5-RELEASE][admin@pfSense.seradex.local]/root: time openvpn --test-crypto -- secret /tmp/secret --verb 0 --tun-mtu 20000 --cipher aes-128-gcm
Fri Jun 19 14:47:16 2020 disabling NCP mode (--ncp-disable) because not in P2MP client or server mode
10.007u 0.000s 0:10.00 100.0% 843+177k 0+0io 0pf+0w
[2.4.5-RELEASE][admin@pfSense.seradex.local]/root: -
@spyder0552
Also just did a test one using UDP and setting the tunnel size to 9000....but still same results -
Hmm with this output I'd expect more than ~165 Mbps but you will never get to 1 Gbps with this CPU and OpenVPN, not even close.
Run again your iperf via the tunnel and checktop -aSH- does the OpenVPN process run close to 100%?
Also for testing try with Encryption Algorithm set to None and try iperf via the tunnel again.-Rico
-
@Rico
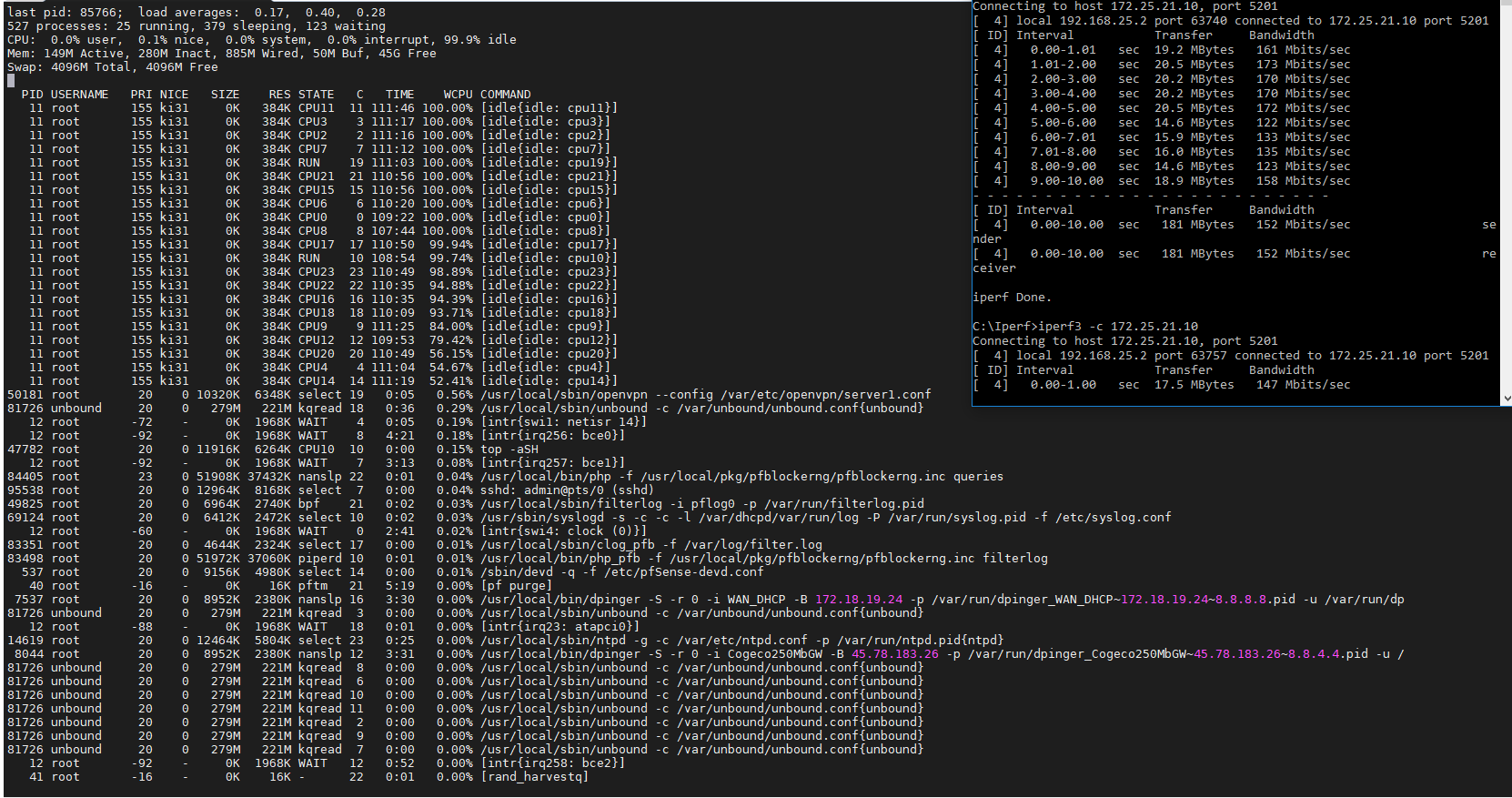
From what I see, no where near any cpu usage
-
@spyder0552
Back on this again now. Anyone have suggestions?
This is all on the same network using Cat6 cables. Just testing from a laptop to the wall to a device on the other side.
No VPN - Speed is fantastic.
OpenVPN tunnel - speed is pathetic.Any help would be appreciated before I have to dump this and look to another solution. I just can't believe that OpenVPN can't handle at least 400-600 Mbs.
Thanks all.
-
Did you try with Encryption Algorithm set to None for testing?
If you really aim for highspeed VPN traffic I think you need to try with IPsec.
-Rico
-
I'm about ready to head out - but I I want to try and see what my 4860 can do via this local sort of testing.. If find some time will do a local only test..
-
@johnpoz
Hi all.
So, still having the same issue. I have now setup a home lab and get the exact same results.
Test Lab:
Intel i5 with 32Gb Ram.
Using Windows HyperV as the host.
Pfsense and Windows10 as guest machines.Test 1 = laptop -> Firewall -> Windows 10
Get ~900 Mb/sTest 2 = Laptop with OpenVP -> Firewall -> Windows 10
Get ~ 170 Mb/sThis is the same results I am seeing at my office using Dell R610 with 24 CPU Xenon's.
Things I have tried:
- Enable/disable the network options Hardware TCP Seg and Large Receive Offload (check box set to disable them).
- Enable fast I/O (with it turned off, I go down to ~155-160)...so currently enabled.
- Snd/rcv buffers. Tried default and 2Mb. No significant change.
- Encryption at AES-128-CBC and GCM. No significant change.
So for anyone that wants to setup my test enviroment:
- Just setup a HyperV box.
- Add 2 virtual switches (one external and one internal).
- Create a VM for Pfsense and give it both virtual switches (WAN = External, LAN = Internal switch).
- Create a VM for a test box
- Put Iperf on the test box
- Create your PFsense with default OpenVPN (using TLS). Just run through the wizard.
I am sure if someone did this they would get to the same spot I am where the speed is just no where at what it should be capable of.
You can rule the hardware out to some extent as testing without the VPN shows near full speed (meaning the nics are talking to each other properly).Anyone willing to try my test?
-
@Rico
Hey, just replied below. Yes, I did try that on Friday and it did not make a difference.Is anyone out there trying this with Windows 10 clients? Perhaps this is a windows issue?
-
@spyder0552 said in OpenVPN Slow - local network test:
[2.4.5-RELEASE][admin@pfSense.seradex.local]/root: openvpn --genkey --secret /tm p/secret
[2.4.5-RELEASE][admin@pfSense.seradex.local]/root: time openvpn --test-crypto -- secret /tmp/secret --verb 0 --tun-mtu 20000 --cipher aes-128-gcm
Fri Jun 19 14:47:16 2020 disabling NCP mode (--ncp-disable) because not in P2MP client or server mode
10.007u 0.000s 0:10.00 100.0% 843+177k 0+0io 0pf+0w
[2.4.5-RELEASE][admin@pfSense.seradex.local]/root:By the looks of that ^^^ it theoretically could do ~320Mbps
How about testing both ways? (client>server - server>client)
Which I5 is that?Your top -aSH screenshot is timed wrong, ..... I guess.
-
@Pippin
Home test lab is i5-4690K (yeah..little dated...best I can get atm).I can't really get it to test from the inside out. The wall seems to be blocking it out. I guess the IP I would connect to would be the end point of the tunel...but not working it seems.
-
You can reverse test mode by using iperf3 -R
"-R, Reverse test mode – Server sends, client receives" -
@Pippin
WOW...actually slower in reverse. Averaged only 100 Mb/sBut if I drop the VPN and just go through the firewall, it goes up to 900
-
@spyder0552
Just to show the config on the client/server side
Client:
dev tun
persist-tun
persist-key
cipher AES-128-GCM
ncp-ciphers AES-128-GCM
auth SHA256
tls-client
client
resolv-retry infinite
remote 192.168.2.98 1194 udp4
verify-x509-name "OpenVPN-Server-Cert" name
auth-user-pass
pkcs12 pfSense-UDP4-1194-vpn.p12
tls-crypt pfSense-UDP4-1194-vpn-tls.key
remote-cert-tls serverServer:
dev ovpns1
verb 1
dev-type tun
dev-node /dev/tun1
writepid /var/run/openvpn_server1.pid
#user nobody
#group nobody
script-security 3
daemon
keepalive 10 60
ping-timer-rem
persist-tun
persist-key
proto udp4
cipher AES-128-GCM
auth SHA256
up /usr/local/sbin/ovpn-linkup
down /usr/local/sbin/ovpn-linkdown
client-connect /usr/local/sbin/openvpn.attributes.sh
client-disconnect /usr/local/sbin/openvpn.attributes.sh
local 192.168.2.98
tls-server
server 192.168.99.0 255.255.255.0
client-config-dir /var/etc/openvpn-csc/server1
username-as-common-name
plugin /usr/local/lib/openvpn/plugins/openvpn-plugin-auth-script.so /usr/local/sbin/ovpn_auth_verify_async user TG9jYWwgRGF0YWJhc2U= false server1 1194
tls-verify "/usr/local/sbin/ovpn_auth_verify tls 'OpenVPN-Server-Cert' 1"
lport 1194
management /var/etc/openvpn/server1.sock unix
push "route 192.168.1.0 255.255.255.0"
push "dhcp-option DOMAIN test.local"
push "dhcp-option DNS 8.8.8.8"
client-to-client
ca /var/etc/openvpn/server1.ca
cert /var/etc/openvpn/server1.cert
key /var/etc/openvpn/server1.key
dh /etc/dh-parameters.2048
tls-crypt /var/etc/openvpn/server1.tls-crypt
ncp-ciphers AES-128-GCM
persist-remote-ip
float
topology subnet
fast-io -
@spyder0552 said in OpenVPN Slow - local network test:
Just setup a HyperV box.
That doesn't seem like a legit test.. My test will be this
windows 10 PC --- sg4860--- NAS
Will set this up later.. But you don't show any of the mtu settings or txqueuelen..
-
Ok I just set this up...
With default everything on open seeing..
$ iperf3 -c 192.168.9.10 warning: Ignoring nonsense TCP MSS 334848 Connecting to host 192.168.9.10, port 5201 [ 5] local 10.0.100.2 port 52251 connected to 192.168.9.10 port 5201 [ ID] Interval Transfer Bitrate [ 5] 0.00-1.00 sec 25.5 MBytes 214 Mbits/sec [ 5] 1.00-2.00 sec 29.5 MBytes 248 Mbits/sec [ 5] 2.00-3.00 sec 32.4 MBytes 272 Mbits/sec [ 5] 3.00-4.00 sec 31.1 MBytes 261 Mbits/sec [ 5] 4.00-5.00 sec 29.5 MBytes 247 Mbits/sec [ 5] 5.00-6.00 sec 30.8 MBytes 258 Mbits/sec [ 5] 6.00-7.00 sec 30.6 MBytes 257 Mbits/sec [ 5] 7.00-8.00 sec 31.6 MBytes 265 Mbits/sec [ 5] 8.00-9.00 sec 31.0 MBytes 260 Mbits/sec [ 5] 9.00-10.00 sec 32.0 MBytes 268 Mbits/sec - - - - - - - - - - - - - - - - - - - - - - - - - [ ID] Interval Transfer Bitrate [ 5] 0.00-10.00 sec 304 MBytes 255 Mbits/sec sender [ 5] 0.00-10.01 sec 304 MBytes 255 Mbits/sec receiverLet me see if can tweak that a bit..
win10 pc (192.168.200.10) --- switch - 192.168.200.1 (test igb4) pfsense (sg4860) ( igb0 lan) 192.168.9.253 -- switch -- 192.168.9.10 (NAS)
Tweaking didn't make much difference to be honest, but using aes-128-gcm vs cbc was huge difference.. When changed to cbc vs gcm when to 130 vs mid 200's