Bypassing DNSBL for specific IPs
-
Hi All,
I see this thread has been ongoing for a few years. How is that? Is there a systematic way to make suggestions so this gets added to pfBlockerNG-Devel? It seems like a reasonable request. If we can't get this added to the GUI is there something else the customer can do? i.e. whitelist the host for 15-60 minutes so they can get the info they need without getting blocked?
having end users manually point to a different DNS server just makes it a pain in the ass. Asking end users to run Opera in VPN mode is also extra steps and eventually I would want to block that as well except for a few users/ip addresses. Having a separate machine or VM on a different network is something our users would call us out on.
Do all the edits to these text files migrate during version upgrades or do we have to remember to re-do all the custom stuff we tinker with?
Thanks,
Joe -
@Gertjan I had this working 4 months back:
server: access-control-view: 192.168.0.20/32 bypass access-control-view: 192.168.0.0/24 dnsbl view: name: "bypass" view-first: yes view: name: "dnsbl" view-first: yes include: /var/unbound/pfb_dnsbl.*confbut later HDD of my custom firewall crashed, and Covid-19 lockdown began.
Meanwhile, I took firewall home, replaced HDD, upgraded pfSense to 2.4.5, upgraded pfblockerng-devel to 2.2.5_33. Now my bypass doesnt work. Everytime Firewall restarts or Enable/Disable pfblockerng, it changes unbound custom option to:
server: access-control-view: 192.168.0.20/32 bypass access-control-view: 192.168.0.0/24 dnsbl view: name: "bypass" view-first: yes view: name: "dnsbl" view-first: yes server:include: /var/unbound/pfb_dnsbl.*confi.e. it adds another server: clause in the last line. You mentioned that there can't be multiple server: clause.
bypass still doesnt work. Can you please help? -
Try this :
server: access-control-view: 192.168.0.20/32 bypass access-control-view: 192.168.0.0/24 dnsbl include: /var/unbound/pfb_dnsbl.*conf view: name: "bypass" view-first: yes view: name: "dnsbl" view-first: yes -
Thanks @Gertjan for responding quickly.
I tried what you suggested, but bypass still not working.
Additionally, when i tried to enable/disable pfBlockerNG(with above custom option), it moved the include: to the last line, with additional server: clause.
server: access-control-view: 192.168.0.16/30 bypass access-control-view: 192.168.0.26/32 bypass access-control-view: 192.168.0.0/24 dnsbl view: name: "bypass" view-first: yes view: name: "dnsbl" view-first: yes server:include: /var/unbound/pfb_dnsbl.*confAnymore ideas worth trying?
-
@Gertjan said in Bypassing DNSBL for specific IPs:
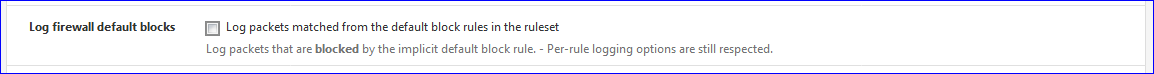
Most easy solution : stop login the hits on the default block rules. (see Log > Settings )
Sorry Gertjan, I am not following your suggestion here. Do you mean "the Settings tab under Status > System Logs"
-
@SmokinMoJoe said in Bypassing DNSBL for specific IPs:
Do you mean "the Settings tab under Status > System Logs"
Yep, this one:
@HiteshJain said in Bypassing DNSBL for specific IPs:
when i tried to enable/disable pfBlockerNG
pfBlockerNG is a program.
It's adds "server:include: /var/unbound/pfb_dnsbl.*conf" without taken in account if you have anything else already in there.
Normally, this isn't a big issue, because, normally, you do not need to enable and disable pfBlockerNG all the time.
And if you do, you have to visit the Resolver config page afterwards to "correct" the custom config options somewhat - if you have other, your own config settings entered.
The syntax has to be correct for unbound, who parses the config file.Btw : My proposition about how to format is : how I should do it.
There is another forum thread that details how to do so already, use that one to compare it with yours. -
@HiteshJain I have evolved the config I posted last month. It still allows pfblockerng to regenerate the configuration correctly, without corrupting it, and adds in a few addtional files which were needed.
# Allow these hosts to bypass pfblockerng server:access-control-view: 192.168.0.2/32 bypass # A view to bypass pfblockerng view: name: bypass view-first: no # This is needed to prevent falling back to the # global 'local-data' settings local-data: "dummy.entry 60 IN A 10.10.10.1" # Static host entries include: /var/unbound/host_entries.conf # dhcp lease entries include: /var/unbound/dhcpleases_entries.conf # Domain overrides include: /var/unbound/domainoverrides.conf server:include: /var/unbound/pfb_dnsbl.*conf -
-
@HiteshJain said in Bypassing DNSBL for specific IPs:
2 server: clause which as per @Gertjan cant be multiple.
I actually said this :
@Gertjan said in Bypassing DNSBL for specific IPs:
"server:" clause can't (there is only one server)
I guess I dive back into the manual ....
But before that : I've seen thousands of these type of files : you've seen one, you've seen them all.
See :
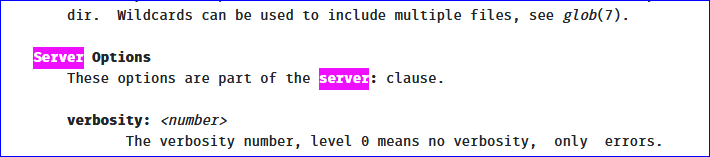
server clause - not server clauses.
Maybe several server: "Attribute keywords" can exist .... you tell me ;)
In real world examples I see only one ...
-
@Gertjan I didnt mean to offend you by quoting you. I apologize :). Probably, I misunderstood your statement because I dont have any idea on how Unbound works or even configured.
I got to read about Unbound only because google results directed me to pages where people more experienced than me mentioned about using custom options of Unbound to bypass few IPs , and I wanted exactly same in my pfSense.@Gertjan The way you explained in one of the earlier replies of yours, gave an impression that you know a lot about Unbound(& related stuff) and that impression is still maintained. I'd like to Thank you that you take time out to respond to newbie like me.
I tried to look at Unbound manual, but I gave up just after scrolling the page down to bottom of earth.
BTW, I am still searching for the right configuration thread from which I could compare my config. Current thread is most appropriate thread i could find so far.
Do you mind sharing the link of thread you mentioned earlier? -
@HiteshJain said in Bypassing DNSBL for specific IPs:
I didnt mean
Don't worry, non taken.
But I probably fckd up anyway. Have a look at the first messages in this thread :
The "include: /var/unbound/pfb_dnsbl.*conf" line should be part of the view: part that handles the "dnsbl". -
@Gertjan Unfortunately, bypass is still not working.

I have also tried to reinstall pfBlockerNG twice, once with 'Keep Settings' checked, another without it.
My pfSense doesnt seems to like bypassing IP.

-
I finally figured out the reason why the bypass and block wasn't working properly. It was silly mistake(s) on my part

The reason why bypass wasnt working:
In TCP/IP->DNS setting I entered the IP address of my server which is also domain controller for windows logins.
Since the DNS request was going to the DC controller first which in turn responds with 10.10.10.1 (blocked) because DC server was itself in the blocked list in Unbound settings.
I have now changed theTCP/IP settings to 'Obtain settings automatically', which is causing the DNS request being sent to Pfsense directly for resolution, and give me bypassed ip address.The reason why block wasnt working properly:
While trying different options to make things work, I enabled Youtube safe search option in DNSBL, which started to unblock youtube for blocked IP addresses. I have now turned it off(disabled) and things are working as expected.Now, bypass and block are working the way I wanted.


-
@horse2370 said in Bypassing DNSBL for specific IPs:
server:
access-control-view: 192.168.1.16/32 bypass
access-control-view: 192.168.1.0/24 dnsblview:
name: "bypass"
view-first: yes
view:
name: "dnsbl"
view-first: yes
include: /var/unbound/pfb_dnsbl.*confI've done this buy I'm still blocked on certain websites, but not all. Wierd!
Update: i had to manually add each URL in the DNSBL Whitelist
-
Couple of things to check
Make sure you do not have an extra server: statement at the very end of the DNS Resolver custom config section. This gets added by pfblockerNG automatically when it upgrades, enables etc. Sure you have, but have to ask as it still catches me out every now and then!
The other thing to check, is machine that is not being bypassed using IPv6. You will need to add a bypass for that IP address as well.
My example is for bypassing Roku's that are IPv4 only. If I was to bypass anything else on my network, I would need to add an additional bypass statement for the IPv6 /128 as most OS's now prefer IPv6 if it available.
Let me know....
-
I found a better solution for myself, and stopped using pfblockerng. I wanted to have better policy based dns blocking per network. I have my kids home doing school full time now thanks to covid. So I have them on their own vlan, and I block all kinds of stuff for their network. But on my own private network I just want ad-blocking only, and I can do this easily with NxFilter.
You can install NxFilter on pfSense:
GitHub - DeepWoods/nxfilter-pfsense: NxFilter install on pfSense
https://github.com/DeepWoods/nxfilter-pfsenseThen I found this vid on Youtube for a quick tutorial on setting it up:
Raspberry Pi Home Server - NxFilter Tutorial - YouTube
https://www.youtube.com/watch?v=l4mOFRQZoOU&t=2sSo I have disabled the pfSense resolver (unbound) and pfBlocker and am only using nxfilter for dns. My pfsense memory usage has come way down, and it feels snappier while browsing. For some reason, dns resolution would hang randomly from time to time when I was using pfblocker, got sick of debugging it.
Before this, I was using pfblocker for pretty much everything on my all my networks, and set up a pihole server in a VM on my freenas box. So dumb to just run a separate adblocking dns server, but that's what I did. So I have scrapped that VM now and my pfsense box is back to doing all the dns.
Just thought I would share, as someone might require similar functionality.
-
@horse2370 thanks I had a server:include: /var/unbound/pfb_dnsbl.*conf on the end!
-
Thank you to all who commented here. I didn't know views were possible in unbound until reviewing this post. I was working through implementing this in my use case which is different than others here. I wanted to comment and share in case anyone else has a similar issue.
tldr: listing only networks for bypassing dnsbl, with defaulting to use of dnsbl for clients
I have many networks (vpns, vlans, etc.), and wanted to configure the use of dnsbl as a default from any network except for specific clients or networks listed. In the examples above, each network has to be listed as either dnsbl or bypass. I didn't want to have to list all networks, and only list bypass IPs/networks since most will use dnsbl.
The key I found to get this working was to set
view-first: noThis wasn't entirely clear to me from the unbound documentation, but seems to work as ignoring the default settings.
I also tried entering a view network such below, to cover all possible private IPs. But these didn't work:
access-control-view: 172.16.0.0/12 bypass_dnsbl access-control-view: 192.168.0.0/16 bypass_dnsblMy working config is here:
server: include: /var/unbound/pfb_dnsbl.*conf access-control-view: 172.20.0.0/24 bypass_dnsbl #guest vlan view: name: "bypass_dnsbl" view-first: no include: /var/unbound/host_entries.conf #Host overrides AND DHCP reservations include: /var/unbound/dhcpleases_entries.conf #DHCP leasesI think this would also have the added benefit of pfblocker not re-adding the "include:" config, but not entirely sure since I have only added recently. If anyone notices an issue with this, please let me know!

-
Hello everyone, is there a possibility to allow a particular host or network to access a certain category of dnsbl? Example: IP 192.168.0.1 access the social networks category and continue with the rest blocked?
Thanks.
-
@fabioccoelho said in Bypassing DNSBL for specific IPs:
Hello everyone, is there a possibility to allow a particular host or network to access a certain category of dnsbl? Example: IP 192.168.0.1 access the social networks category and continue with the rest blocked?
Thanks.
Looks like its being worked on, good timing.
https://www.reddit.com/r/pfBlockerNG/comments/kdg5wq/preliminary_dnsbl_group_policy/Without these upcoming features, what you want to do would be pretty complicated. I have previously set up different pfsense/pfblocker instances to to accomplish this.