Certificate Question
-
Sorry for the noob question, but I am trying to set up access to the web configurator using https:, and I am unsure about what I need to import to my browsers to have my self signed certs trusted. (I don't want Let's Encrypt as @jimp mentioned in one of his VPN talks that it's better to have a private CA so no external entity has access to the signing key.)
I created a root certificate for pfSense, which I used to sign an intermediate certificate. I use the intermediate certificate to issue the webConfigurator certificate and my VPN certificates.
I am assuming that I should use the Export CA action button to export the root certificate and import the exported file to the trust store on my browsers (Firefox, Chromium)--Am I correct?
Is the pfSense export format accepted by common browsers, or do I need to do some sort of conversion?
Maybe I should ask in the HAProxy forum, but I was wondering can I use the same certificate that I use for OpenVPN authentication to authenticate a client web browser on HAProxy. Is the pfSense export format compatable with Android and web browsers.
Thanks in advance for any advice/hints/suggestions.
-
@guardian said in Certificate Question:
I am assuming that I should use the Export CA action button to export the root certificate and import the exported file to the trust store on my browsers (Firefox, Chromium)--Am I correct?
Yes.
We're 2020 these day : there is no more "Yeah yeah, I'll accept the risk" : Firefox will just not let you visit the WebGUI. You're locked out.See :
https://forum.netgate.com/topic/125382/webconfigurator-default-certificate-expired-yesterday/20Making the certs - if you lost them, or whate ever, it's easy https://docs.netgate.com/pfsense/en/latest/book/config/advanced-admin.html#ssl-certificate
or use the WebGUI http access.
Take note that this SSH/console method will create the needed certs and switch to https for you. A browser like Firefox will now .... not letting you in, very needed to export the certs so the browser will trust your home mad certs.Use the console (SSH ! always activate the SSH access as it is some what more important as the GUI access) to switch back to "http", export the certs etc.
@guardian said in Certificate Question:
Is the pfSense export format accepted
Yes - the certs will be accepted.
@guardian said in Certificate Question:
HAProxy
is a front end for web servers. If these are publicly visible, the home made certs will be to much of a hassle. Trusted cerst are way easy to handle (set it and forget it). You could use the acme package, that uss Let's Encryp to obtain a wild card cert - for your web servers and/or HA proxy. You'll be needing a domain name, though, the one that you have to pay for every year.
-
@Gertjan said in Certificate Question:
@guardian said in Certificate Question:
I am assuming that I should use the Export CA action button to export the root certificate and import the exported file to the trust store on my browsers (Firefox, Chromium)--Am I correct?
Yes.
We're 2020 these day : there is no more "Yeah yeah, I'll accept the risk" : Firefox will just not let you visit the WebGUI. You're locked out.See :
https://forum.netgate.com/topic/125382/webconfigurator-default-certificate-expired-yesterday/20Making the certs - if you lost them, or whate ever, it's easy https://docs.netgate.com/pfsense/en/latest/book/config/advanced-admin.html#ssl-certificate
or use the WebGUI http access.
Take note that this SSH/console method will create the needed certs and switch to https for you. A browser like Firefox will now .... not letting you in, very needed to export the certs so the browser will trust your home mad certs.Use the console (SSH ! always activate the SSH access as it is some what more important as the GUI access) to switch back to "http", export the certs etc.
Thanks for the warning @Gertjan ... I didn't realize that you couldn't make https optional. A lot of GUIs will accept both. I saw the command for generating a new certificate, but I was wondering if there was a command to switch from https to http from the cli?
@guardian said in Certificate Question:
Is the pfSense export format accepted
Yes - the certs will be accepted.
@guardian said in Certificate Question:
HAProxy
is a front end for web servers. If these are publicly visible, the home made certs will be to much of a hassle. Trusted cerst are way easy to handle (set it and forget it). You could use the acme package, that uss Let's Encryp to obtain a wild card cert - for your web servers and/or HA proxy. You'll be needing a domain name, though, the one that you have to pay for every year.
Why too much of a hassle? I want access from the public internet for certain web services that I am running, but access is only for myself and my wife. I'm fine with creating a cert 1/year, and dropping it into the browsers on our phones.
Am I missing something?
I should mention that my ISP has a very non-descript mechanical dns entry that I can use to find my servers. Let's Encrypt/Registered Domain will give me a lot of extra visibility that I don't want/need-just likely to attract more script kiddies/scanners etc.
-
@guardian said in Certificate Question:
I didn't realize that you couldn't make https optional.
These :
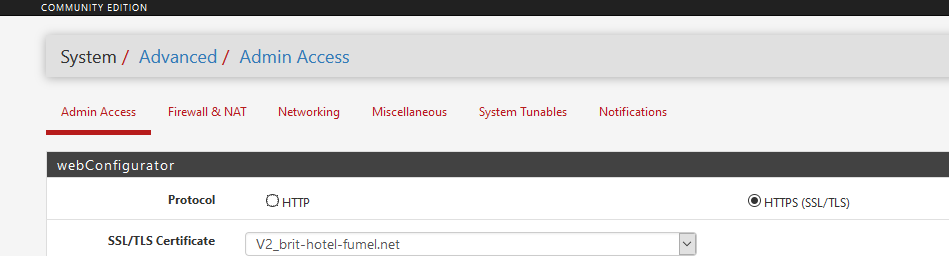
are called radio button.
Last century, devices like radios had button that permitted you to select between AM and FM.
Pressing one releases the other one. Only one "mode" can be active at any time
pfSense is less a gadget, more a security device.
The welcome screen is http, otherwise you would be locked out from start.
You set up your 'things' and then you enable https - leaving the not secure http.
True, some devices accept http only, http and https, and http only. For a security device the second wouldn't make sense. -
To your question about haproxy and cert auth, yes I believe its possible to do this.. Since like version 1.8 or something. Current version of haproxy-dev is 2 something so you should be fine.
I have not set this up, so not sure how easy or difficult it might be.. But yeah that sort of question would be better suited for that section of the forum.
If what your wanting to do is allow access to resources for you and your wife - wouldn't just vpn be easier solution?
-
@guardian said in Certificate Question:
I am trying to set up access to the web configurator using https:
I don't want Let's Encrypt as @jimp mentioned in one of his VPN talks that it's better to have a private CA so no external entity has access to the signing key.Those two are not mutually exclusive. You can use Let's Encrypt for the GUI cert and a self-signed structure for VPNs. You don't have to use the same for both (and usually you can't, the main exception being that you can use Let's Encrypt for a server cert with IKEv2 and either EAP-MSCHAPv2 or EAP-RADIUS)
Some people prefer using a self-signed CA/Server cert for the GUI but personally I find that a bigger pain than using Let's Encrypt since I don't have to touch the clients for the GUI cert to be validated properly.
-
@jimp said in Certificate Question:
I don't have to touch the clients for the GUI cert to be validated properly.
Well it should only be once, and then they will trust any certs you create - for other things that use https for their gui that doesn't support acme, like switches and printers, etc. And browsers hitting your admin gui should be very limited anyway ;)
It use to be less of a hassle when you could just create a 10 year cert, but now browsers pretty soon are going to want a new signed cert every other week ;)
-
Thanks @Gertjan, @johnpoz, @jimp I appreciate your input/knowledge so if you think I'm off base with my thinking I'd appreciate input.
@Gertjan said in Certificate Question:
@guardian said in Certificate Question:
I didn't realize that you couldn't make https optional.
These :
[ Image deleted ]
are called radio button.
I realize that... I just hadn't checked... got it confused with FreeNAS. If you click the https: button, it enforces https, if you check http:, you have your choice -- which I think makes sense. If you want to enforce https:, you can, and if you want to allow http, you have the option to upgrade on a case by case basis.
pfSense is less a gadget, more a security device.Agreed, pfSense is an excellent peice of entrerprise grade software(/hardware) for a user that has a high level of technical skill... If you don't understand the implications of using http vs https I don't know how you would configue a pfSense box! :)
On my network the only argument for https is to prevent sniffing by malware. My wife is the only other user and she doesn't have the skills to "sniff traffic" even if she wanted to. Having said that, I am doing my best to run a network/system to the highest standard that I can that makes sense.
@johnpoz said in Certificate Question:
To your question about haproxy and cert auth, yes I believe its possible to do this.. Since like version 1.8 or something. Current version of haproxy-dev is 2 something so you should be fine.
I have not set this up, so not sure how easy or difficult it might be.. But yeah that sort of question would be better suited for that section of the forum.
If what your wanting to do is allow access to resources for you and your wife - wouldn't just vpn be easier solution?
Easier to set up, but 2 big problems:
- Firing up a VPN just to update a calander or similar quick interaction with a web app is way to cumbersome for my wife. (And not something I'm really happy about either)
- Because of battery life, it doesn't make sense to leave a VPN running all day to allow a dozen or so convenient access to web apps.
If the back end web apps are VLAN'd, I'm thinking that the cert may be good enough security (and possibly a password). While I'm sure it is possible to exfil a cert from an android phone, IIUC it is a more difficult and less common attack. I would think that it would therefore be a targeted attack rather than blanket data harvesting.
@jimp said in Certificate Question:
@guardian said in Certificate Question:
I am trying to set up access to the web configurator using https:
I don't want Let's Encrypt as @jimp mentioned in one of his VPN talks that it's better to have a private CA so no external entity has access to the signing key.Those two are not mutually exclusive. You can use Let's Encrypt for the GUI cert and a self-signed structure for VPNs. You don't have to use the same for both (and usually you can't, the main exception being that you can use Let's Encrypt for a server cert with IKEv2 and either EAP-MSCHAPv2 or EAP-RADIUS)
Some people prefer using a self-signed CA/Server cert for the GUI but personally I find that a bigger pain than using Let's Encrypt since I don't have to touch the clients for the GUI cert to be validated properly.
Agreed... especially if you have a large number of (unskilled) users--given the market you work in I understand completely.
I was hoping to stay under the radar by not registering a domain/using Let's Encrypt. Non targeted attacks don't happen if the attacker doesn't know there is something to hack.
If the CA is inside my firewall, nobody can get it unless I am already owned. Given how widespread and the easy setup for Let's Encrypt, I'm suspecting that it may be/or has secretly been compromised by a three letter agency, who is likely to eventually let it leak. LE is more than good enough to prevent traffic injection/ad jacking/snooping for most web traffic.
Do you think I am being too paranoid?
@johnpoz said in Certificate Question:
@jimp said in Certificate Question:
I don't have to touch the clients for the GUI cert to be validated properly.
Well it should only be once, and then they will trust any certs you create - for other things that use https for their gui that doesn't support acme, like switches and printers, etc. And browsers hitting your admin gui should be very limited anyway ;)
It use to be less of a hassle when you could just create a 10 year cert, but now browsers pretty soon are going to want a new signed cert every other week ;)
Does the 1 year apply to the root CA as well? I do device certs 1/year, but I have a 10 year signing certificate. (Other than Apple which I don't/won't use) Is this a problem?
-
No the CAs age limits are fine - its browsers all lowering the age of certs they are accepting is the problem.
Firefox is going with a 398 day age limit I do believe.
-
@guardian said in Certificate Question:
I was hoping to stay under the radar by not registering a domain/using Let's Encrypt. Non targeted attacks don't happen if the attacker doesn't know there is something to hack.
Other concerns aside, that's a non-issue with properly configured DNS. If you do DNS-based TXT updates for Let's Encrypt, there do not have to be any public A/AAAA records for the hosts, and the TXT records are short-lived, only existing while the Let's Encrypt verification is being performed.
-
@guardian said in Certificate Question:
but I was wondering if there was a command to switch from https to http from the cli?
There are 2 ways :
Use option 15 to get back in the previous situation.
Option 2 or 3 - have to check with the manual. -
@Gertjan said in Certificate Question:
@guardian said in Certificate Question:
but I was wondering if there was a command to switch from https to http from the cli?
There are 2 ways :
Use option 15 to get back in the previous situation.
IIUC this is only if the last configuration was http:, and any other changes are killed as well.Option 2 or 3 - have to check with the manual.
Sorry, I don't understand this - can you please explain further. -
@guardian said in Certificate Question:
Sorry, I don't understand this
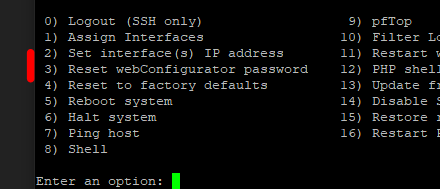
One of these reset the GUI access to http. The manual will tell you more.
@guardian said in Certificate Question:
IIUC this is only if the last configuration was http
It must be the last setting change, the one you can cancel.
If you change from http to https, and you lose access because https won't work for you, you loose contact with the GUI. Rephrase that : you loose the ability to make changes ^^