SSH works of pfSense but fail Linux server.
-
The problem is that I can’t login Linux game server via ssh or the game.
I can login to pfSense through the web or ssh.Here is my network config:
pfSense is setup as firewall only 192.168.0.1\24
Game server is a vm 192.168.0.30\24
The rest of my network resides behind cisco sg500 192.168.0.5\24
The cisco handles all routing on 10.0.0.0\17 networkI have gateway route setup for lan to the cisco switch
Static routes setup for all vlans on the cisco switch.
There are firewall rules to support the static routes.Here’s what works.
I have full access to pfSense through web or ssh via client behind the cisco switch. pfSense can check for updates and set the time from ntp server on a cisco routed vlan. My pc clients can reach the internet and inter-vlan works as it should. I can ping the game server. From an ESXI console window I can ping google.com and update the Linux server. The cisco switch is reachable though the 192.168.0.5 and its address on the 10.0.0.0 network.What does not work is game server though 192.168.0.30
-
Where are you trying to connect to it from?
Sounds like it might be an asymmetric routing issue.
You see TCP flagged traffic blocked?Steve
-
@F1Fish said in SSH works of pfSense but fail Linux server.:
192.168.0.1
Not optimal description.
I assume the pfSense is your def-gw to the internet.Have you routed the 10.0.0.0/17 network on the game machine to 192.168.0.5 , in order to enable return packets.
From your description , the ssh packages does not even pass the pfSense fw , in a functional setup.
-
I assume the pfSense is your def-gw to the internet.
You are right.
Have you routed the 10.0.0.0/17 network on the game machine to 192.168.0.5 , in order to enable return packets.
This statement I having a hard time achieving.
I've followd this artical to add the firewall to my network.
https://engineerworkshop.com/blog/how-to-set-up-vlans-on-an-l3-switch-hp-1910-with-pfsense/ -
Can we get a basic diagram of how these systems are connected?
-

-
Have you routed the 10.0.0.0/17 network on the game machine to 192.168.0.5 , in order to enable return packets.
If I'm understanding this correctly. A static routeon the game server will only give me Lan accses and no wan accses
From your description , the ssh packages does not even pass the pfSense fw , in a functional setup.
I can't ssh the game server. I see nothing in firewall log file for a failed attempt. But I can login to pfSense using ssh.
-
So your transit network is is this 192.168.0/24 ? You do not put hosts on a transit network.. This comes up like every day it seems..
And your trying to access the game server from some downstream network..
This is asymmetrical.. So no its not going to work without routes on the game server.
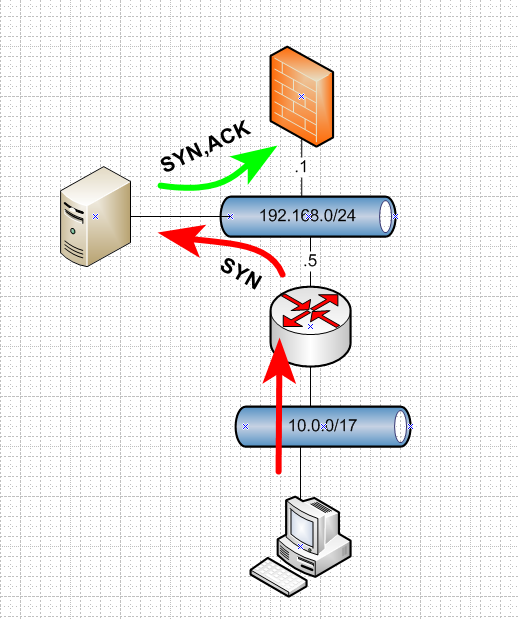
And take you don't even have default route on this game server, so it can not even send the syn,ack back??? Even with default route to 192.168.0.1 - pfsense would not allow it because it would be out of state.
You need a route on the gameserver saying hey to get to 10.0/17 talk to 192.168.0.5
-
johnpoz thank you for your help
The solution I used on game server was.
up /sbin/route add -net 10.0.0.0 netmask 255.255.128.0 gw 192.168.0.5
down /sbin/route del -net 10.0.0.0 netmask 255.255.128.0
Added to /etc/network/interfaces file.The DSL router (CenturyLink C1900A) I use did this automatically.
So I’m still looking for a solution I can implement on the firewall. -
If it was setup exactly like that then it probably did it 'automatically' by being a bad stateful firewall.

If it did not track TCP states for example that traffic would be allowed.
You can try setting
Bypass firewall rules for traffic on the same interfacein System > Adv > Firewall&NAT. Or you can force the traffic to be passed by allowing out of state TCP traffic.
https://docs.netgate.com/pfsense/en/latest/firewall/troubleshooting-blocked-log-entries-due-to-asymmetric-routing.html#manual-fixSteve
-
Or the actual correct solution which would be to remove asymmetrical traffic flow! ;)
While allowing out of state traffic can be a life saver in say an enterprise where something broken, and we can get it working like this - until proper fix/redesign can be done.
The correct solution is to not setup asymmetrical networks.. Just no point to it, other than lack of basic networking skills.
-
Yup. That.
If you add workarounds to allow the traffic it will probably come back to bite you at some point.
-
So your saying I should go with a router on a stick. Or move the game server tto a vlan routed by the switch. To clear up the asymmetrical network.
-
You need to take your server off the transit network... Be it you want it to be a vlan hanging off your downstream router, or a vlan off of your edge router (pfsense)..
But currently that network is transit (a network between 2 routers) putting hosts on it that need to talk or get talked too from network via one of the routers lead to asymmetrical traffic flow.
Throw another vlan on your pfsense and put your game server there, now you can actually firewall between your downstream networks and the server..