Last config change in shell
-
Does anyone know how to get the last config change (as seen on the system information widget on the dashboard) from the shell? Thanks!
-
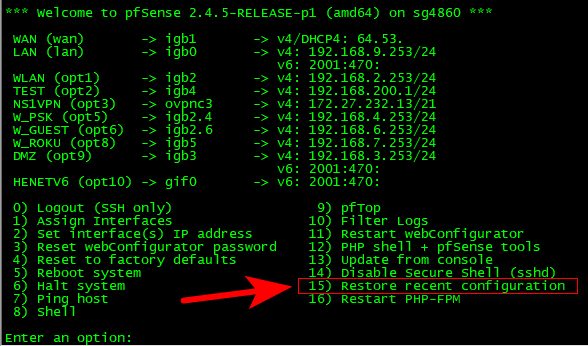
Option 15
-
Ah ha! That does have what I want but where is that located so I can grep it from a shell script? Thanks!
-
All of the configs are backed up here
/cf/conf/backupSo yeah I guess you could script something to restore a previous one..
Having a hard time coming up with a use case for that..
-
Yeah, I'm trying to make use of the mailreport package for systems that dont have monitoring and/or syslog available. This happens with family and friends sometimes and looking at a report for 10 seconds can save me/someone from an "emergency" repair. (Heaven forbid we are without internet for a short time!) On the other hand if there was more than a few of these people I would ask for $20 for my birthday each year and just spin up a cloud server to throw it at. For now though this works and the line below adds a nice touch to the report, which is still a work in progress. I've been using bash for many years and it provides a lot more leniency with my commands.
echo "Last config change:" && date -r `cat /cf/conf/backup/backup.cache | awk -F '[;:]' '{print $4}'` -
ah - that is nice.. So your not restoring it you just want to see it.. That makes sense..
You never stated restore ;) For some reason that was was thinking..
edit:
Simpler solution - don't let your friends/family access to change anything on their pfsense, if you are going to have to be the one to fix it ;)You know that saying about enough monkeys banging on enough typewriters, that is users - problem is there is a lot of gibberish that comes out before you get shakespeare.. Users tend to just click on shit in a gui, much like a monkey.. Until something works ;) heheheh
So best thing is if you don't want to waste a lot of paper and ink, and typewriters - best to not like the monkeys bang on them in the first place ;)
-
The monkeys are locked out but they can still cause a lot of trouble, haha. Actually, the cable companies cause the most trouble with connections that just stop working then people go unplugging things before calling the cable company because cable companies suck to deal with then who knows what the "support" person is going to have them do. One of the big reasons to use pfSense in these family/friend/home locations is that I can just say "nope, it's not the router" and have data to back that up if the cable company gives me trouble.
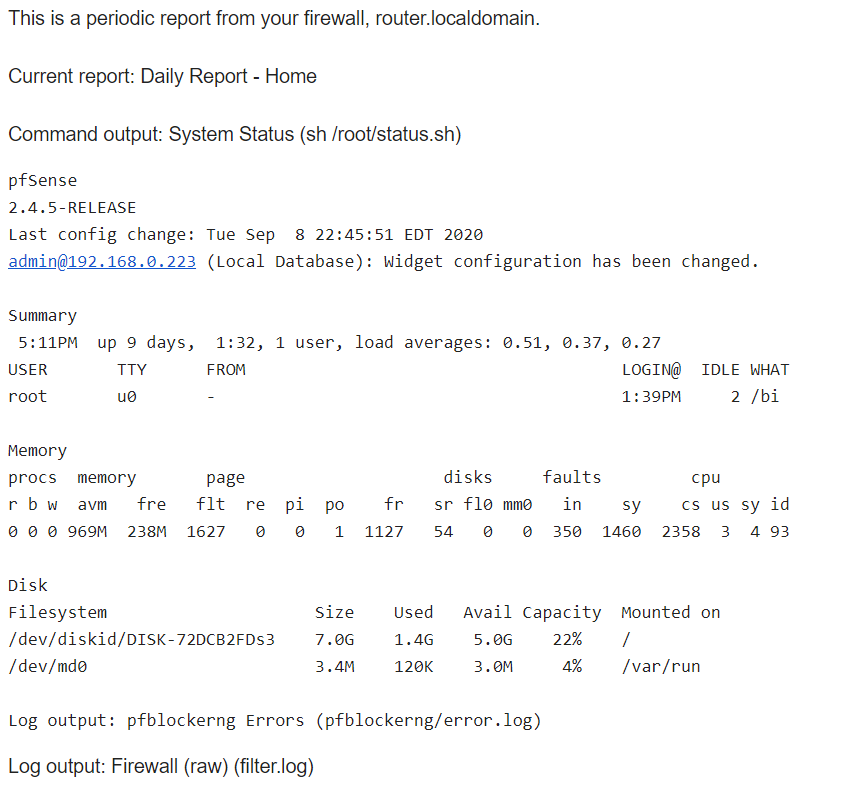
This is the (very) rough little script that I wrote last night for mailreport to run gives me piece of mind that I am correct without having to log in to look. Also, as I am configured in the advanced > email settings I know that pfSense will email me if something really bad happens and this provides me with just a little extra.
#!/usr/bin/env sh #The purpose of this script is to collect system information for use with mailreport package. #TODO: use regex for last config summary? .*\/[0-9]{10}\..* or .*\/[0-9]\{10\}\..* #Basic system summary cat /etc/platform /etc/version echo -n "Last config change: " ; date -r `cat /cf/conf/backup/backup.cache | awk -F '[;:]' '{print $4}'` && cat /cf/conf/backup/backup.cache | awk -F '["]' '{print $4}' echo echo "Summary" ; w echo echo "Memory" ; vmstat -ah echo echo "Disk" ; df -hl / /var/run #Optional troubleshooting information #echo #echo "Top CPU" #ps -auxf | head -1 && ps -auxf | sort -nr -k 3 | head -5 #echo #echo "Top MEM" #ps -auxf | head -1 && ps -auxf | sort -nr -k 4 | head -5 #echo #echo "Top TIME" #ps -auxf | head -1 && ps -auxf | sort -nr -k 10 | head -5 #Additional logs echo [ -f /var/log/pfblockerng/error.log ] && echo "Log output: pfblockerng Errors (pfblockerng/error.log)" && tail -n 20 /var/log/pfblockerng/error.log echoOutput looks like this followed by whatever logs you have mailreport attach. We will see how quickly the attached logs annoy me before I move them to the script so I can use grep for the date.
If I get more than a few friends/family doing this then it's going in some monitoring system (or I block their number, ha!), but for now there are just two and it is manageable this way.
Thanks for your help and listening to me rant!
-
@ex1580 said in Last config change in shell:
then people go unplugging things
That is never good with something like pfsense.. Its not a soho router ;)
-
Well this got out of hand pretty fast, haha. At least it was a good learning experience. It's not easy to get memory stats out of this thing! I have not finished editing to make sure everything is perfect and portable but for now this works well on an sg-1100 which is the target system(s). On to the next project!
#!/usr/bin/env sh #The purpose of this script is to collect system information for use with mailreport package. #TODO: See notes in comments - rounding memory calculations with bc #Variables for searching logs datesearchclog="`date '+%b %e'`" datesearchpfb="`date '+%m/%d/%y'`" #Basic system summary cat /etc/platform /etc/version echo -n "Last config change: " ; date -r `awk -F '[;:]' '{print $4}' /cf/conf/backup/backup.cache` && awk -F '["]' '{print $4}' /cf/conf/backup/backup.cache echo echo "SUMMARY - See load avg last 1, 5, and 15 minutes" ; w #CPU utilization checking cpuload="`uptime | /usr/bin/sed 's/^.*: //'`" cpuload5="`echo $cpuload | awk -F '[. ]' '{print $3}'`" if [ "$cpuload5" -gt "1" ]; then echo "WARNING! 5 MIN CPU LOAD HIGH:" $cpuload5 echo "Top CPU" ps -auxw | head -1 && ps -auxw | sort -nr -k 3 | head -5 echo "Top TIME" ps -auxw | head -1 && ps -auxw | sort -nr -k 10 | head -5 fi echo #MEM information and utilization checking #vmstat -ah top | head -4 | tail -1 totalmem="`sysctl -n vm.stats.vm.v_page_count`" if [ "$totalmem" -gt "0" ]; then inactivemem="`sysctl -n vm.stats.vm.v_inactive_count`" cachedmem="`sysctl -n vm.stats.vm.v_cache_count`" freemem="`sysctl -n vm.stats.vm.v_free_count`" usedmem=`echo "$totalmem - ($inactivemem + $cachedmem + $freemem)" | bc` memusage=`echo "($usedmem * 100) / $totalmem" | bc` #round with bc? physmem=`sysctl -n hw.physmem` physmemh=`echo "$physmem / (1024*1024)" | bc` #round with bc? echo "Mem:" $memusage"% of" $physmemh"M used." if [ "$memusage" -gt "60" ]; then echo "WARNING! MEMORY USED HIGH:" $memusage"%" echo "Top MEM" ps -auxw | head -1 && ps -auxw | sort -nr -k 4 | head -5 fi else echo "ERROR READING MEM PAGE COUNT!" fi echo #DISK information and utilization checking df -hl / /var/run diskused="`df -h / | /usr/bin/tail -n 1 | /usr/bin/awk '{ print $5 }' | /usr/bin/cut -d '%' -f 1`" if [ "$diskused" -gt "60" ]; then echo "WARNING! PERCENT DISK USED HIGH on /:" $diskused"%" fi echo #LOGS - provides more detail and filtering than mailreport package offers echo "Filtered Log Output" [ -f /var/log/pfblockerng/error.log ] && echo "Log output: pfblockerng Errors (pfblockerng/error.log)" && grep -e "$datesearchpfb" /var/log/pfblockerng/error.log && tail -n 20 #/var/log/pfblockerng/error.log ; echo echo [ -f /var/log/filter.log ] && echo "Log output: Firewall (raw) - Admin Interfaces GUEST (filter.log)" && clog /var/log/filter.log | grep -e "$datesearchclog" | egrep "1566350082" | tail -n 20 echo [ -f /var/log/filter.log ] && echo "Log output: Firewall (raw) - Combined Blocklist (filter.log)" && clog /var/log/filter.log | grep -e "$datesearchclog" | egrep "1597881531|1597881664" | tail -n 20 echo [ -f /var/log/filter.log ] && echo "Log output: Firewall (raw) - GeoIP Regions (filter.log)" && clog /var/log/filter.log | grep -e "$datesearchclog" | egrep "1599316667|1599316737" | tail -n 20 echo [ -f /var/log/gateways.log ] && echo "Log output: Gateway Events (gateways.log)" && clog /var/log/gateways.log | grep -e "$datesearchclog" | tail -n 20 echo [ -f /var/log/ntpd.log ] && echo "Log output: NTP (ntpd.log)" && clog /var/log/ntpd.log | grep -e "$datesearchclog" | tail -n 20 echo [ -f /var/log/routing.log ] && echo "Log output: Routing (routing.log)" && clog /var/log/routing.log | grep -e "$datesearchclog" | tail -n 20 echo [ -f /var/log/system.log ] && echo "Log output: System (system.log)" && clog /var/log/system.log | grep -e "$datesearchclog" | egrep "fail|emerg|alert|crit|err|warn" | tail -n 20 echo [ -f /var/log/watchdogd.log ] && echo "Log output: watchdogd (watchdogd.log)" && clog /var/log/watchdogd.log | grep -e "$datesearchclog" | tail -n 20 echo