Pfsense with AP dhcp server settings
-
@JKnott ok, pfsense configured and I can confirm that works. my laptop receives vlan2 ip address when directly connected to port 3 from router(dedicated port for vlan2). but when connected to switch, the assigned vlan2 ports don't give ip.
I have an Avaya 5500 or Nortel 5520/48pwr.
I have configured vlan2 on the switch. I have assigned ports to it(pfsense router has dedicated port to 47 on switch). The port from ap is in "tagall(trunk)" mode. All other ports in "untagall(access)" mode. vlan1 works, assigns ip and has internet(also wifi). vlan2 works in router, but when plugged in switch and I plug laptop in assigned vlan2 port: nothing(no ip-address, even when I manually set ip: no internet or connection to router/switch).Switch does see which vlanids are active on the ports, those are all correct.
Do you guys have any ideas or can tell me which settings you had to do in switch?
-
@SlayrNeo Did you add the proper VLAN tag to the port that runs back to the pfsense box? It needs to be there, too.
From the post above, it looks like that's port 47, like you say.
Jeff
-
@akuma1x port 3 in pfsense is assigned vlan2 and gives ip to laptop with vlanid=2 when directly connected to port 3.
Avaya switch port 47:
index = 1/47
Vlanids = 2
Discarduntagged frames = false
filterunregisteredframes = true
defaultvlanid = 2
port priority = 0
tagging = untagall(access)In general:
Vlan 1 ports:
index = 1/xx
Vlanids = 1
Discarduntagged frames = false
filterunregisteredframes = true
defaultvlanid = 1
port priority = 0
tagging = untagall(access)Vlan 2 ports:
index = 1/xx
Vlanids = 2
Discarduntagged frames = false
filterunregisteredframes = true
defaultvlanid = 2
port priority = 0
tagging = untagall(access)Only Port 11(Cambium AP):
index = 1/11
Vlanids = 1,2
Discarduntagged frames = false
filterunregisteredframes = true
defaultvlanid = 1
port priority = 0
tagging = tagall(trunk)Cable from pfsense port3 to switch port 47. Then cable from vlan2 assigned port on switch to laptop: nothing(even when I manually add vlan2 id and/or ip address in vlan2 group).
-
@SlayrNeo To me, after reading all the steps you've tried, looks like something isn't cooperating in the switch. I don't know what else to tell you. I'm not familiar with that switch, so I can't help you troubleshoot it.
Can you reset the switch back to factory defaults, or is that not possible? It's a long shot, but maybe there's a setting in there somewhere that you're unaware of, that's keeping this all from working properly.
Jeff
-
Ok, maybe this helps.
When I try to ping lan connected devices(wired or wireless), I can ping everything on lan.
When I try to ping the managed switch on ip in lan, I get response.
When I try to ping the managed switch on ip in vlan2 with vlan2 interface I don't receive response.
When I try to ping the managed switch on ip from lan with vlan2 interface I receive response.Is this correct or should the outcomes from the last 2 be reversed? Otherwise this might be another symptom of my problem ;)
-
@SlayrNeo said in Pfsense with AP dhcp server settings:
Ok, maybe this helps.
When I try to ping lan connected devices(wired or wireless), I can ping everything on lan.That's normal, because devices on the SAME subnet never go thru the firewall. Therefore, no matter what your pfsense LAN rules look like, a ping from one machine to another machine, say thru a switch, on the same subnet, will most likely ALWAYS work.
When I try to ping the managed switch on ip in lan, I get response.
Same as above, same subnet traffic.
When I try to ping the managed switch on ip in vlan2 with vlan2 interface I don't receive response.
You probably don't have an appropriate firewall rule on your VLAN2 to allow/pass ping traffic to anywhere else. Attaching a screenshot of your VLAN2 firewall rules would help here.
When I try to ping the managed switch on ip from lan with vlan2 interface I receive response.
This is most likely because you have an ALLOW any LAN traffic to any destination, the default rule, on your pfsense LAN firewall rule tab.
Jeff
-
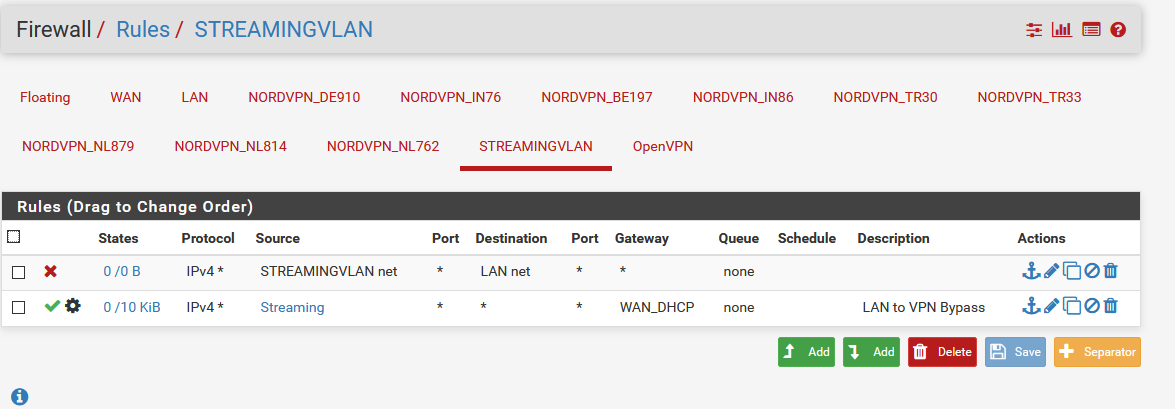
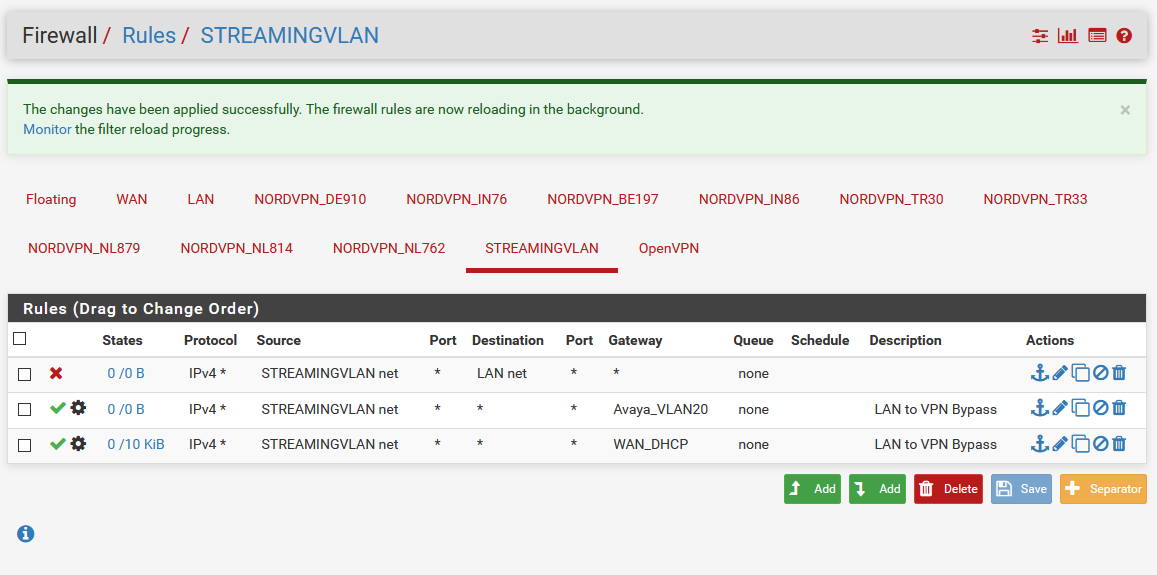
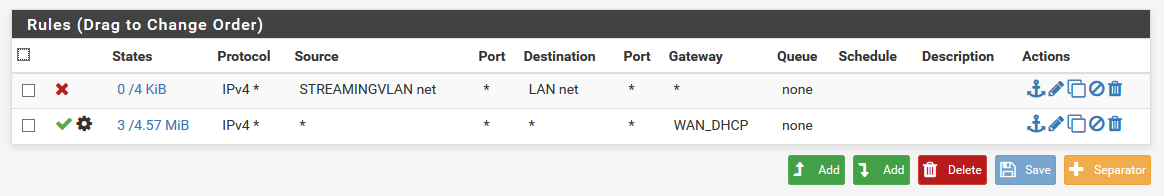
The rules on vlan:
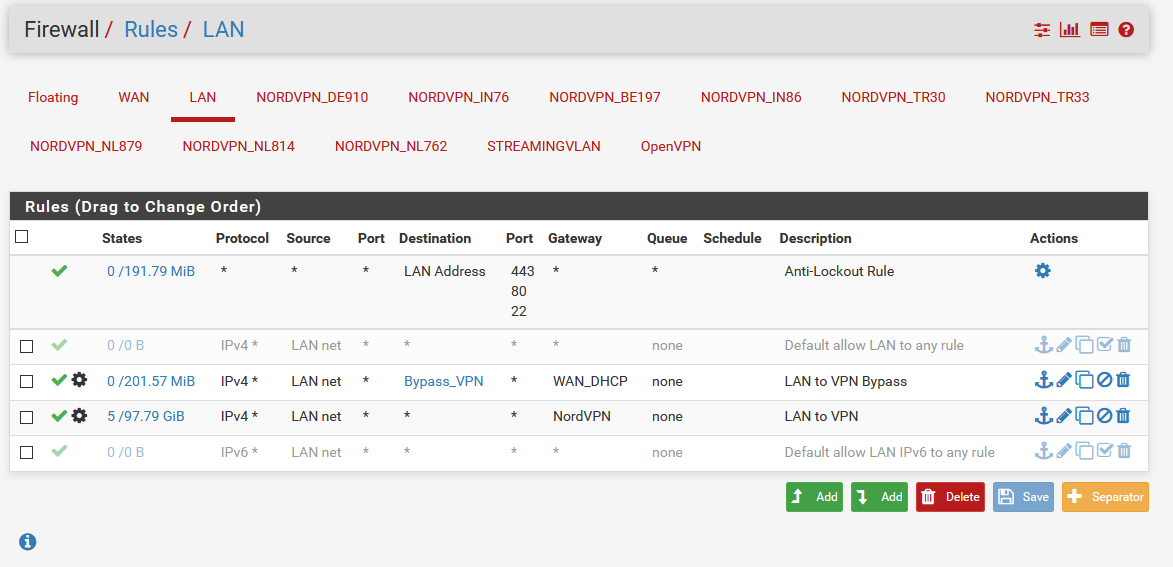
the rules on lan:
-
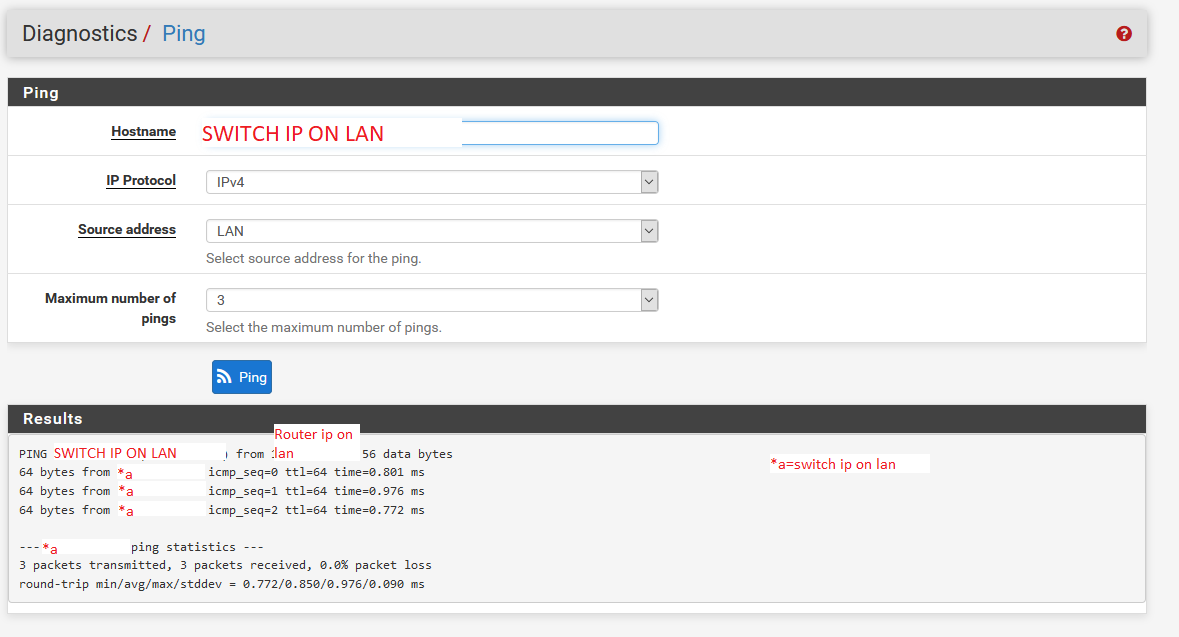
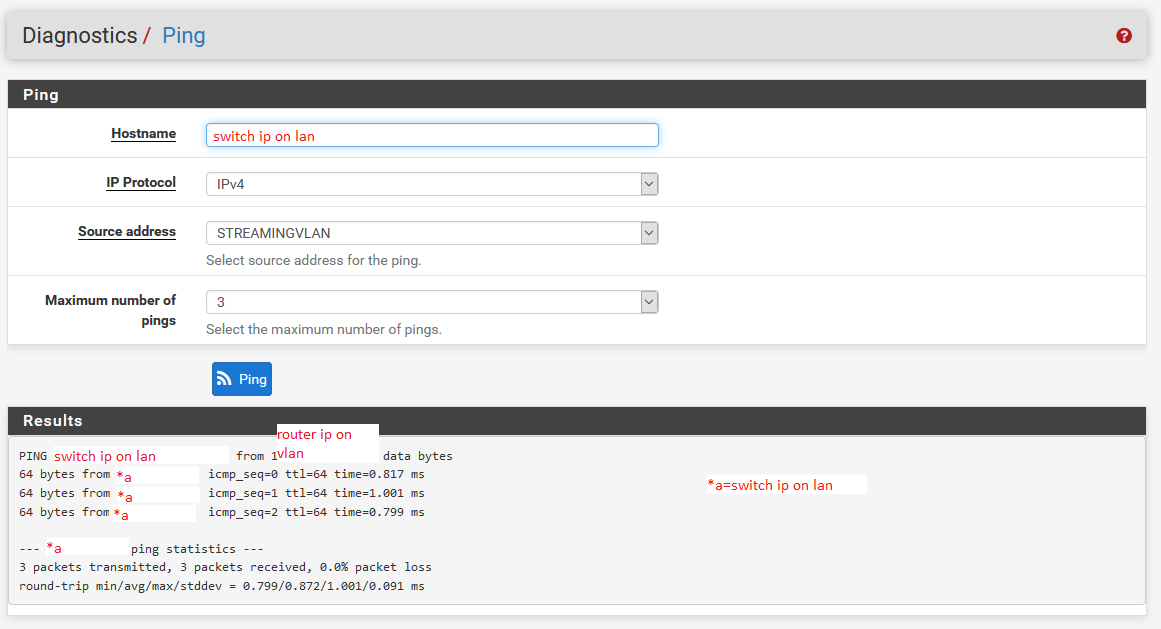
Ping from lan interface:
To lan switch ip:
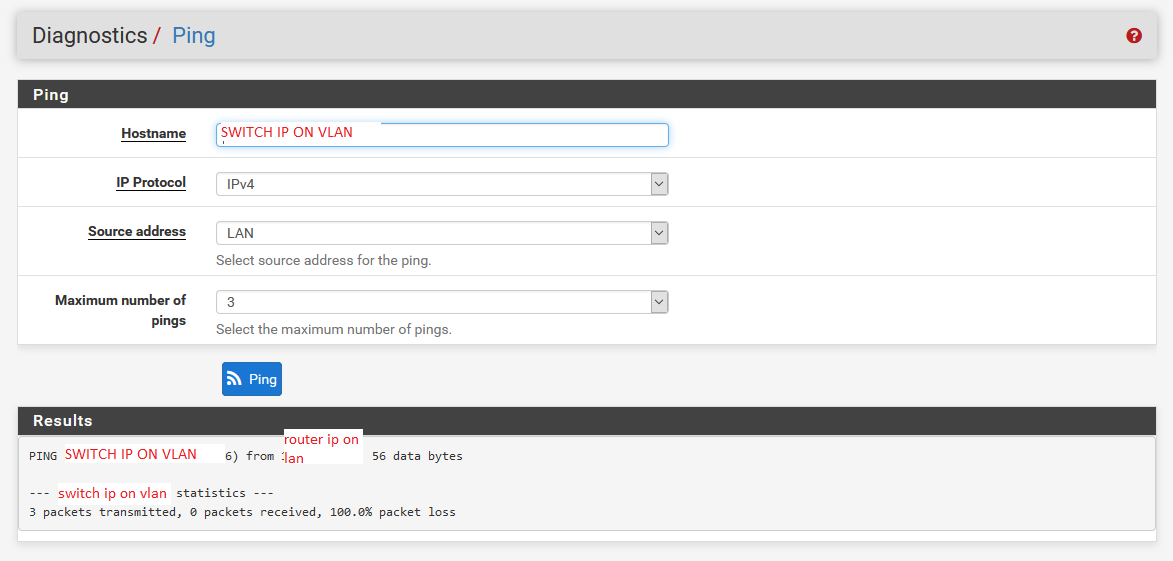
To vlan switch ip:
-
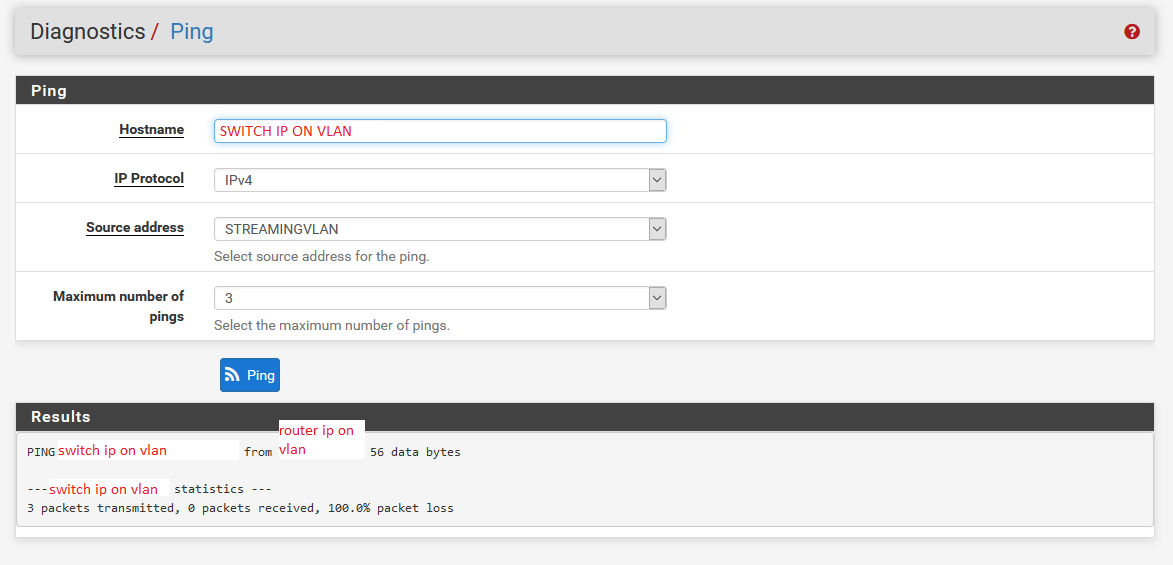
Ping from vlan interface:
To lan switch ip:
To vlan switch ip:
-
@SlayrNeo I'm pretty sure your ping from LAN to VLAN switch IP fails, since your LAN interface has no rules to get to the VLAN network. The 3 allow rules on the LAN tab are: anti-lockout, all LAN to the WAN-DHCP gateway, and all LAN to the NordVPN gateway. There is nothing there to keep traffic from LAN inside your internal networks. You are forcing all of it out the 2x gateways you've got there. You need to get that disabled "Default allow LAN to any rule" back online. Do you really want to force all of your LAN traffic out the NordVPN gateway like that?
And, I think the VLAN router to the switch IP on the same VLAN might be the same problem. You are forcing all VLAN traffic out thru the WAN_DHCP gateway. You also have an alias "Streaming", but you don't explain what those machines/hosts actually are. So, it's a mystery what's in there.
What you could do, to put some devices in these networks put thru the VPN and gateways you want, are to make aliases for just those machines, and use those aliases in an allow rule. Then below this allow rule, set the default allow any rule at the bottom. So, the "approved" machines in the alias will use the VPN gateway stuff first, and the "not approved' devices will use your default gateway next. Make sense?
Also, since these are internal private networks, you don't need to mask the IP addresses like you have.
Jeff
-
@akuma1x said in Pfsense with AP dhcp server settings:
@SlayrNeo I'm pretty sure your ping from LAN to VLAN switch IP fails, since your LAN interface has no rules to get to the VLAN network. The 3 allow rules on the LAN tab are: anti-lockout, all LAN to the WAN-DHCP gateway, and all LAN to the NordVPN gateway. There is nothing there to keep traffic from LAN inside your internal networks. You are forcing all of it out the 2x gateways you've got there. You need to get that disabled "Default allow LAN to any rule" back online. Do you really want to force all of your LAN traffic out the NordVPN gateway like that?
Yeah those rules are:
Specific websites just go to wan
Everything else is forced to vpn, don't want lan to connect to internet directly.And, I think the VLAN router to the switch IP on the same VLAN might be the same problem. You are forcing all VLAN traffic out thru the WAN_DHCP gateway. You also have an alias "Streaming", but you don't explain what those machines/hosts actually are. So, it's a mystery what's in there.
Alias streaming is all ip from 150-200. But now I think about it, maybe this is blocking the ip's from switch and router on vlan(under 100).
What you could do, to put some devices in these networks put thru the VPN and gateways you want, are to make aliases for just those machines, and use those aliases in an allow rule. Then below this allow rule, set the default allow any rule at the bottom. So, the "approved" machines in the alias will use the VPN gateway stuff first, and the "not approved' devices will use your default gateway next. Make sense?
Also, since these are internal private networks, you don't need to mask the IP addresses like you have.
Jeff
Beter safe thans sorry

Thanks, I will look into the vlan rule.
-
ok i tried to change rules:
What I also discovered: when I am on lan network I can connect to router with it's lan ip and it's vlan ip, but I can only connect to switch with it's lan ip.
still no automatic ip-address on the vlan 20 ports on switch...
What I also discovered was that the pfsense router sees 2 additional gateways. Those are the standard lan(vlan1 on switch), but it also sees the vlan20. Do I need to do something with this? As you can see in screenshot I tried to add it in rules, but still nothing(even with that rule disabled).
What I want:
Ports 1-24 and the ap on port 46 on switch on vlan1(standard lan) with dhcp connected on port 48. ALL traffic from devices connected to these need to go through vpn.Ports 25-36 and the ap on port 46 on switch vlan20 with dhcp connected on port 47. ALL traffic from devices connected to these need to go to wan(internet) directly.
First part works, second part nothing... ;)
-
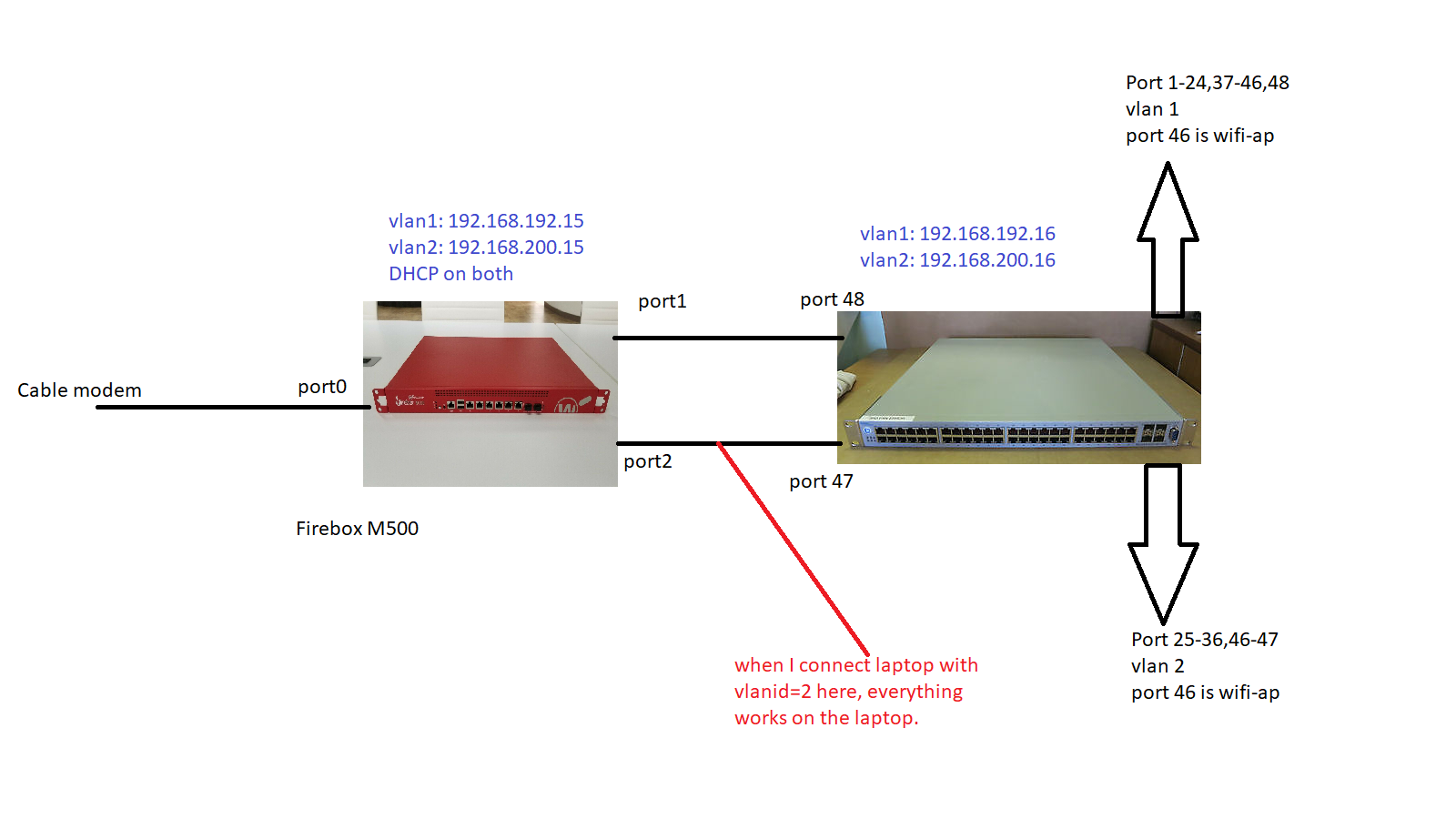
this is my setup
-
Ok, new switch (linksys) and now I am getting somewhere.
When connecting to vlan2 port on switch I get vlan2 ip from pfsense router and can access router.
When connecting to vlan2 wifi, I get vlan2 ip from pfsense router and can access router.
When connecting to port 3 on router(port1=wan, port2=lan, port3=vlan2) with laptop with configured vlan2 id, I get vlan2 ip from pfsense router and can access router.In all cases I have access to vlan2 devices and can't access lan devices. I have to use vlan2 ip from router to access it and can't access it with lan ip from router. So far so good.
Now the problem: in all cases I don't have internet on vlan2. I do have internet connection on lan net, but unfortunately not on vlan2. This looks like a pfsense problem(as plugging directly laptop on router gives same result). Uploaded above is the rule I have. First I had source: Streamingvlan-net in both rules, but that didn't work either.
Where do you think the problem is?
-
found it, I had to make a rule in Firewall-Nat-Outbound