pfSense using unreasonable amount of bandwidth while idle
-
If you have no ports open - then all of those rules are POINTLESS!!!
Your also behind a nat... So how do you think something from Asia is going to even get to you? All of those rules have zero hits...
That is not all the rules? For why if you have no port forwards... Default is deny, anything that is no a reply would be dropped hitting your wan.. Unsolicited no matter from where is dropped.. Those rules don't stop something behind pfsense from talking to something..
And again your behind a nat - do you have stuff forwarded to your 192.168 address.. How are you doing that you said your not in control of that router in front of you..
My point about that IP, is none of those are anything pfsense would generate traffic too.. It would be some client watching youtube or checking their mail for traffic to go there.
Maybe google drive?? A sync or watching a video would for sure account for such traffic..
-
Yeah, I was just reading and thinking that....
If you don't have a pass rule on WAN for something then those inbound pfBlocker rules are just loading up the firewall unnecessarily. All that is blocked by default anyway.
-
@stephen10
@johnpozIf you have no ports open - then all of those rules are POINTLESS!!!
I figured I'd get yelled at for that. Yes, they are pointless right now. In the past, a port was open on the exterior NAT, and on the pfsense. That port has since been closed, but may be opened again in the future. For ease of use, I left these rules in place.
Believe it or not, I do know how NAT works.
And again your behind a nat - do you have stuff forwarded to your 192.168 address.. How are you doing that you said your not in control of that router in front of you..
I'm not in control of it, but ports have been forwarded to me by someone else on occasion, for specific purposes.
My point about that IP, is none of those are anything pfsense would generate traffic too.. It would be some client watching youtube or checking their mail for traffic to go there.
Maybe google drive?? A sync or watching a video would for sure account for such traffic..
When this problem starts (overnight) the only things which should be happening are on a single computer:
- AV - Since it is largely ignored, it has automated AV on it which may do updates ovnight
- 0patch - since it is a Win7 device, 0patch is running on it to "micro patch" some vulnerabilities. This may do updates overnight.
- A custom script, which monitors a web server. Once in a great while, it will interact briefly with that server, but generally it just checks on it periodically and logs what it sees.
- NextCloud Sync Client (Files are very rarely changed, so this incurs a nominal amount of load)
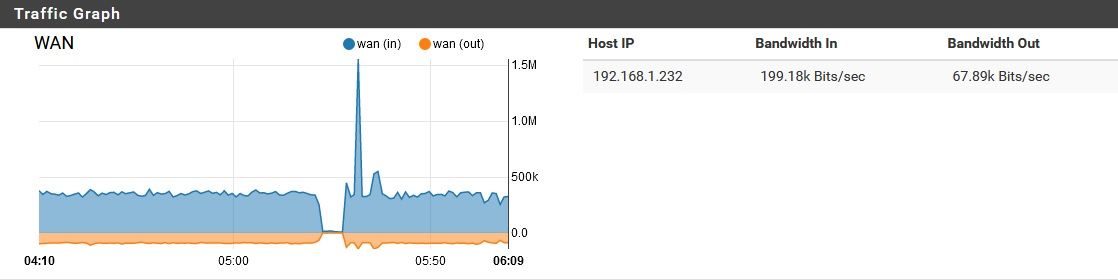
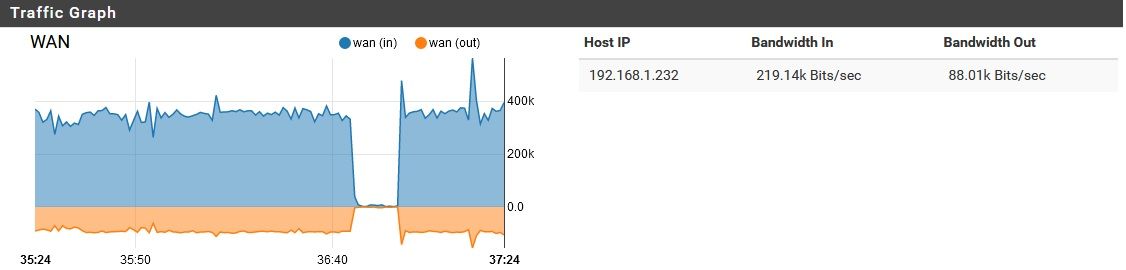
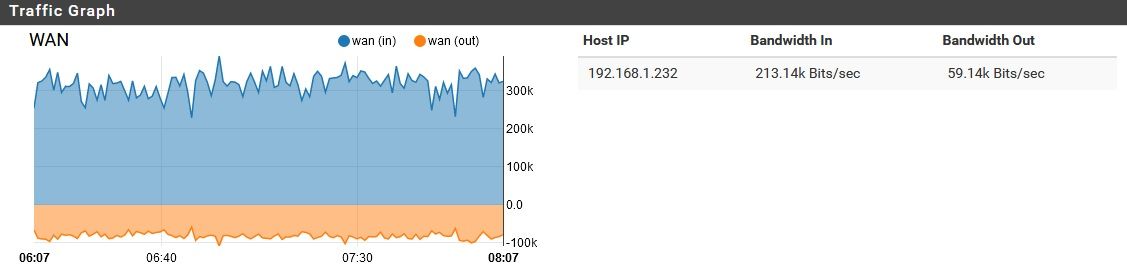
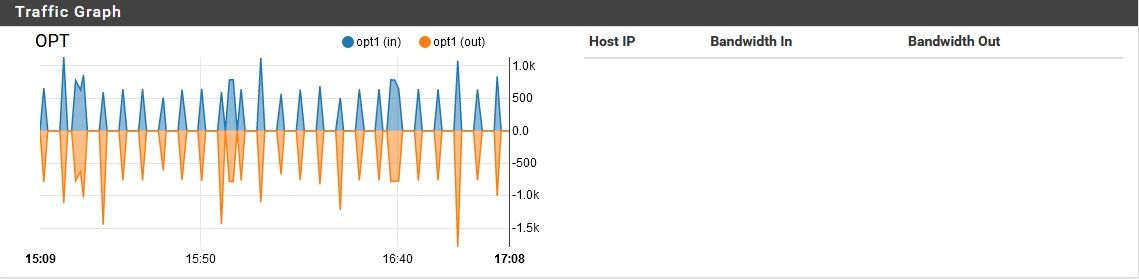
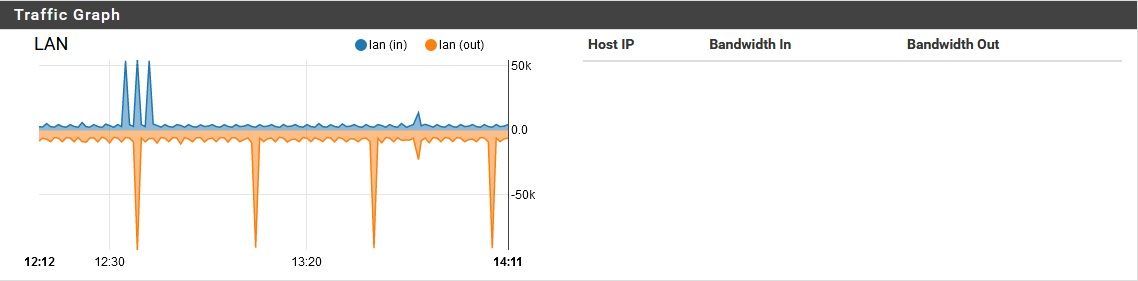
On average, this computer uses less that 1Kb/s of bandwidth, but will occasionally increase to as much a 5Kb/s, and even spike to around 2Mb/s for a few seconds, a couple times a week. As shown earlier, my problem involves a nominal amount of traffic moving through the LAN and OPT ports, while a sizable amount is moving through the WAN port.
-
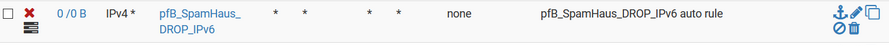
How is this rule not just completely pointless? You have a ipv4 rule with a IPv6 source of addresses.. Be it your going to open a port or not?
In your traffic graph or iptop, or darkstat -- look to see where the remote non pfsense IPs are in that traffic flow.. Its not insignificant - so should be easy enough to spot.. Clear your counters..
Now look in your state tables.. Pfsense would have zero reason to be sending traffic to that IP listed for example.. You hid the other one.. so have no idea what that is.. But that ip listed that has some traffic going to it - top of your list.. Is not something pfsense would ever talk to on its own from any sort of normal setup. And sure is not your dns your forwarding too.. So what is creating that traffic, its not pfsense. Unless its maybe something downloading some list? It is 443 traffic. And from pfsense top - it would be this 192.168.3.2 generating the traffic!! See the pftop exact same packet counts..
The only thing shown not matched up is thos pings from 192.168.1.1 - which pfsense would ping if that is its gateway.. But default is to send 0 size pings, and only 2 a second they would not account for 200k of data.
If it was just noise hitting your wan, there wouldn't be outbound traffic.. Pfsense if no ports open or actual reject rules does not answer noise.. its just dropped..
-
Using SSL/TLS encrypted DNS via 9.9.9.9??
Disable it and use the local resolver and delete all DNS entries under general -> setup.
Reboot.
Let us know.
-
@johnpoz said in pfSense using unreasonable amount of bandwidth while idle:
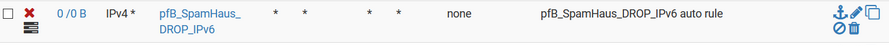
How is this rule not just completely pointless? You have a ipv4 rule with a IPv6 source of addresses.. Be it your going to open a port or not?
Yup, that would be useless. I just corrected it to IPv6--thanks.
In your traffic graph or iptop, or darkstat -- look to see where the remote non pfsense IPs are in that traffic flow.. Its not insignificant - so should be easy enough to spot.. Clear your counters..
Now look in your state tables.. Pfsense would have zero reason to be sending traffic to that IP listed for example.. You hid the other one.. so have no idea what that is.. But that ip listed that has some traffic going to it - top of your list.. Is not something pfsense would ever talk to on its own from any sort of normal setup. And sure is not your dns your forwarding too.. So what is creating that traffic, its not pfsense. Unless its maybe something downloading some list? It is 443 traffic. And from pfsense top - it would be this 192.168.3.2 generating the traffic!! See the pftop exact same packet counts..
Yes, but keep in mind, that includes the traffic load from the daytime, when PCs behind it are in use. Of course those entries have a lot of traffic...this is not just an idle lab environment. If I reboot the pfsense to reset these entries, the unwanted "noise" will also go away. The only way I can troubleshoot this is with dirty data. For example, the IP I masked was seeing moderate to heavy traffic for about 10 hours, due to user activity within the network. Then it stopped. Then a few hours later, pfsense suddenly got very talkative, but that did not outweigh the user activity from earlier.
The only thing shown not matched up is thos pings from 192.168.1.1 - which pfsense would ping if that is its gateway.. But default is to send 0 size pings, and only 2 a second they would not account for 200k of data.
If it was just noise hitting your wan, there wouldn't be outbound traffic.. Pfsense if no ports open or actual reject rules does not answer noise.. its just dropped..
Exactly, that's why I started this thread in the first place. Only after the pfsense's network goes quiet, does the pfSesne start communicating a great deal with the outside. Based on the utilization of each physical port, I can see that it is not coming from inside the network, so it must be the pfsense itself. Should it be doing this? No, I don't think so. Can I figure out why it might be? No, or I wouldn't be asking here. It is always possible that something is misconfigured, but I don't have any ideas what. Since my WAN ports are closed and I'm seeing 2-way traffic, I must surmise that pfSense is initiating this activity, and based on what we have discovered since then, it looks like the activity is being initiated with my upstream DNS.
As a side note, I noticed most of this traffic was going between my secondary DNS provider, which I figured meant that the primary couldn't give an answer, so the pfSense tried the secondary. On a whim, I replaced my secondary (formerly IBM's Quad-9) to CloudFlare's secondary (1.0.0.1). Although this noise doesn't always start every night, it has been almost every night. Last night though, it didn't. At this point it doesn't conclusively mean anything, but I'm going to check back on it in a while, and see if the noise returns. It would be surprising if this actually "fixed" the problem, but I'll give it some time and see.
-
@Cool_Corona said in pfSense using unreasonable amount of bandwidth while idle:
Using SSL/TLS encrypted DNS via 9.9.9.9??
Disable it and use the local resolver and delete all DNS entries under general -> setup.
Reboot.
Let us know.
DoH is currently disabled, but I did not clear the entries. I will try that soon, but as I just posted above, I also just cut Quad-9 out of the provider list. I don't want to try too many things at once. I'm also trying to get a clean pcap of the noise for johnpoz.
Thanks for the tip!
-
So pfBlocker isn't supposed to be doing DNS lookups, as stated earlier. However, it occurs to me that the DNSBL entries can be filtered against to Alexa top sites...could this mechanic result in any DNS queries?
-
So did turning of pfblocker stop the problem.. been a few days..
-
@johnpoz
I was still having this issue after flipping off the pfBlocker switch, but I did not reboot. I have rebooted the pfsense with pfBlocker disabled, and will monitor it to see how things go. -
Yes, after a reboot with pfblocker off, I am still seeing this DNS rubbish going on.
-
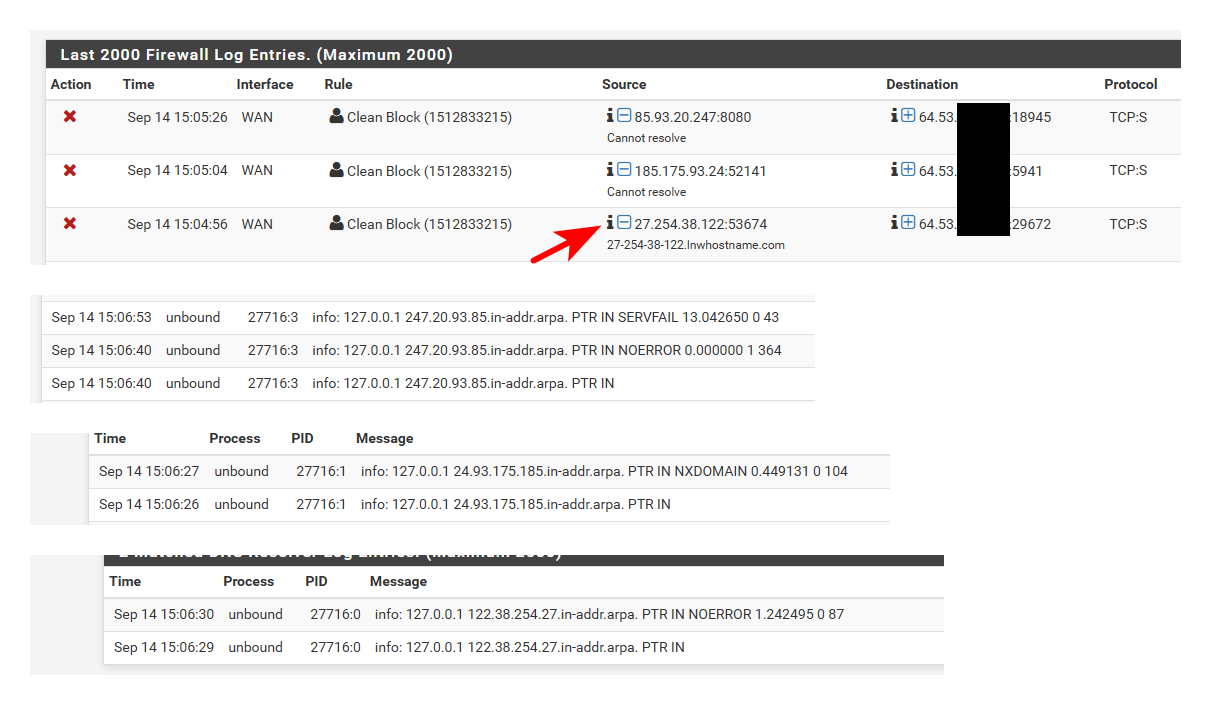
Well can tell you for sure that pfsense out of the box is not going to query "185.190.088.000" as a A query..
You have something asking pfsense for that.. Or something running on pfsense doing dns query to loopback asking for that.
Even if pfsense was asked to resolve an IP, say in the logs or something - it would do a PTR for it..
Example... I enabled logging in unbound. So now I get all queries asked for logged..
server: log-queries: yesI then go into say the firewall log and ask pfsense to tell me hey who is this IP hitting my server.
by clicking the little "i" it then tries to resolve that.. Via a PTR query.. Not a A query for some name with that the IP as the name.. Also why and the F would be asking for what is clearly a bogon..
What other things do you have installed on pfsense? Or what do you have doing queries to pfsense that your not seeing the query come in? A dns redirect setup would look like loopback is asking for the record.
The only thing pfsense itself would be asking for is hey I need to get the package list from netgate, hey lets check if there is a update, or hey I have a widget on the home page and need to pull the RSS feed, etc.
Can tell you for sure if there was something in pfsense out of the box causing this traffic, or even something common... The forums would be blowing up with hey why is there 300K of traffic all the time...
-
@johnpoz
Well, I don't have RSS feeds, or other such junk going on in the box. and the lookups are showing the source being the loopback. Here are the packages I have installed:
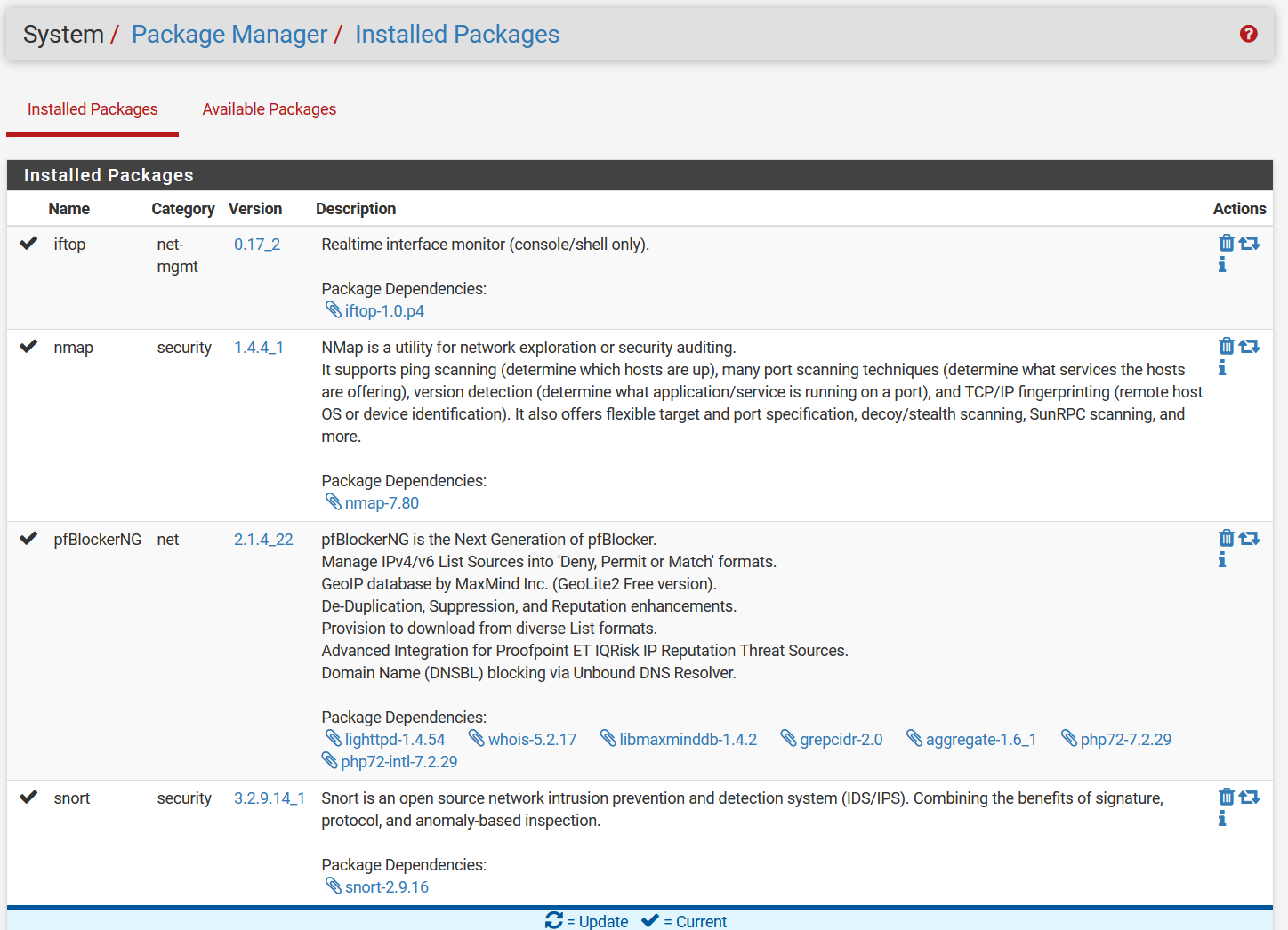
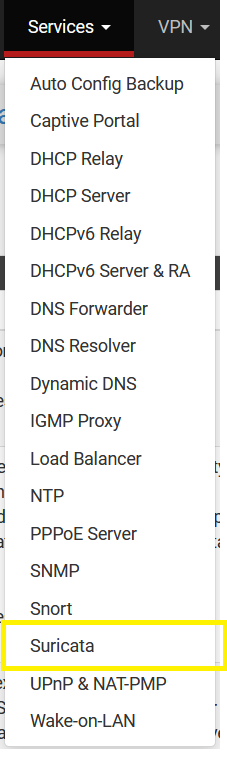
I haven't (side)loaded any other software outside of the package manager, or installed any of my own scrips. I formerly had Suricata installed also, but it wasn't working due to RUST, so I uninstalled it. Although the package manager shows it gone, I still have a few traces of it, indicating an incomplete uninstall.
I also previously installed then uninstalled Acme. To my knowledge, that was a clean uninstallCan tell you for sure if there was something in pfsense out of the box causing this traffic, or even something common... The forums would be blowing up with hey why is there 300K of traffic all the time...
Yeah, instead we have one single, ridiculously long thread...ugh.
So what now? Would it make any difference at all if I take a full backup, do a factory reset, then restore from the backup? I have a feeling that would bring the problem right back. I don't want to reconfigure from scratch, though.
-
well iftop or nmap sure wouldn't be doing it, they don't even run anything unless you run them.
I guess snort could be be doing it? In theory - it could try and look for IPs that hit your wan..
Thought you said you removed pfblocker? I would remove them completely, both pfblocker and snort.. Just to be 110% sure its not them..
But what I can tell you for sure is there nothing in pfsense out of the box that would try and look those such fqdn..
What I would prob do, is do a clean install of pfsense with min sort of setup, an out of the box sort of setup.. And do you get such queries now?
I can tell you for sure my setup isn't doing anything of the sort.. I have logging of all queries turned on in unbound, and see nothing even close to those nonsense lookups.
-
Snort and Suricata do zero DNS queries unless the user manually clicks the designated icon on the ALERTS tab. Neither package does anything on its own with the exception of using
curlto perform the daily rules update check. During that processcurlwill look up the IP for the rules download URLs. However, those lookups are a miniscule amount of traffic. -
I hear yeah - but what else could be doing queries for such nonsense.. Seeing queries like this..
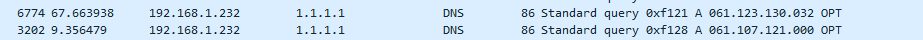
Lots and lots of them, and both A and AAA for just what looks to IPs, but not PTR queries but actual A and AAAA queries for what looks to be an IP.
I would say its some stupid client, but he states he is not doing any dns redirection, and log of the queries in unbound show they are from loopback.
-
There is no code within the PHP package that would do that (save for the
curlreference I mentioned), and I am quite familiar with the Snort binary code and know of nothing in there that would account for such activity.The last time I recall a discussion similar to this with mysterious DNS lookups it turned out to be a logging application of some type that was attempting to convert IP addresses to hostnames.
You know there is a setting on the pfSense firewall logging tab that turns this feature on, but I'm not sure if that is a permanent thing or just active while you have the firewall log tab open. It resolves IP to hostnames (or attempts to).
-
That is a good hint for sure.. You wouldn't be able to recall enough to find this thread where this was happening before? That might be a clue for sure.
I don't recall seeing such a thread.. But so many, and many are just the same over and over they all tend to blend together.
So you think it was something or could have something to do with logging in pfsense, or some package?? Prob the best clue we have had sofar in trying to track this down.
-
@johnpoz said in pfSense using unreasonable amount of bandwidth while idle:
That is a good hint for sure.. You wouldn't be able to recall enough to find this thread where this was happening before? That might be a clue for sure.
I don't recall seeing such a thread.. But so many, and many are just the same over and over they all tend to blend together.
So you think it was something or could have something to do with logging in pfsense, or some package?? Prob the best clue we have had sofar in trying to track this down.
I think it was a year ago or maybe a little more, but I don't recall more than that. My years are catching up with me. My memory has "read errors" sometimes now ...
 .
.Oh, and that Firewall Log thing is actually an icon you click on the page, not a parameter.
-
Looking in all the settings for logging - and I don't see anything that should or could do that.. Unless something really odd going on if sending logs to remote syslog???
@CyberMinion Do you have logs being sent to remote syslog?
Also what about looking in your cron jobs for something? You can install the cron package to get look see to what is in there.