OpenVPN will not connect
-
@johnpoz said in OpenVPN will not connect:
@viragomann said in OpenVPN will not connect:
Many ISP routers and also other ones translate the source IP form incoming packets to their LAN IP when forwarding to an internal device.
Like what devices do this - this would be utterly moronic.. Never seen this.. Sure you could do such a thing on pfsense. But you would have to do it on purpose, ie a source nat..
Never seen some soho router that would do source natting even if you wanted to, let a lone on its own.
Where is the sniff on the wan when trying to access the openvpn? Lets see this please..
What do you mean about sniff on my Phone and WAN? i don't understand the question sorry.
If you mean where my phone then located i have tried all the time WIFI disabled on my phone.
-
Sniff on your pfsense wan, via diag, packet capture menu item for the port your listening on for openvpn. Then try and make a connection from your phone - or other client that is not on your network..
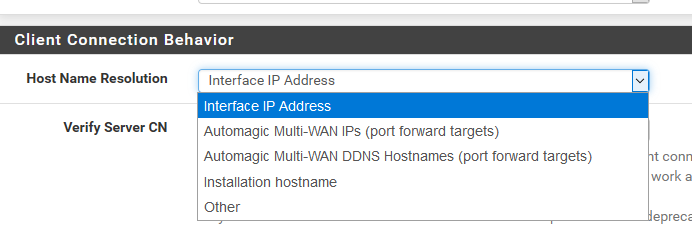
example
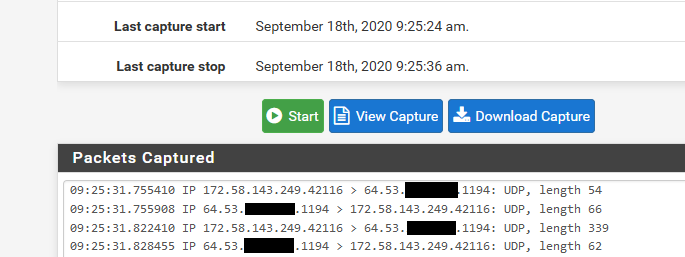
That is my phone coming from the 172.58 address (t-mobile) hitting my openvpn port (1194 udp) on my wan IP 64.53.x.x
-
@johnpoz said in OpenVPN will not connect:
Sniff on your pfsense wan, via diag, packet capture menu item for the port your listening on for openvpn. Then try and make a connection from your phone - or other client that is not on your network..
example
That is my phone coming from the 172.58 address (t-mobile) hitting my openvpn port (1194 udp) on my wan IP 64.53.x.x
Ohh learned something news!! Did that but nothing to see there. Tested another port which i have use for other thinks and i see that as well.
-
@erbalo said in OpenVPN will not connect:
Did that but nothing to see there
Well if you do not see anything there when you attempt to access vpn.. Then how would you connect? Pfsense can only work with traffic it actually sees.
You have something upstream blocking access then, so no you would never be able to connect to pfsense vpn until traffic actually gets to pfsense.
-
@johnpoz said in OpenVPN will not connect:
@erbalo said in OpenVPN will not connect:
Did that but nothing to see there
Well if you do not see anything there when you attempt to access vpn.. Then how would you connect? Pfsense can only work with traffic it actually sees.
You have something upstream blocking access then, so no you would never be able to connect to pfsense vpn until traffic actually gets to pfsense.
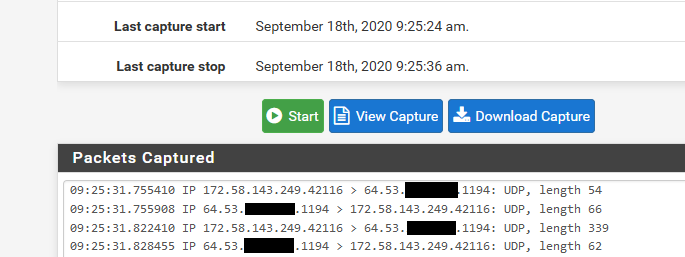
Thats right my problem, i can't get any traffic via VPN client to the pfsensen. I think should be somehting with my NAT port... What did you fill in here as Target IP address? Should that be the the Gateway IP address of my Pfsense?
-
@erbalo said in OpenVPN will not connect:
What did you fill in here as Target IP address? Should that be the the Gateway IP address of my Pfsense?
What? The openvpn wizard will setup the firewall rule to pfsense wan address.. You would not be doing a port forward for openvpn. Unless openvpn server was behind pfsense, and that is going to have its own problems with most likely asymmetrical traffic flow.
Again if you do not see traffic on pfsense WAN, then how would openvpn work? You need to validate your client is actually trying to talk to PUBLIC pfsense wan IP.. or if you have something natting in front of pfsense. Than that PUBLIC ip and that whatever is natting in front of pfsense is sending to pfsense wan IP.
-
@johnpoz said in OpenVPN will not connect:
@erbalo said in OpenVPN will not connect:
What did you fill in here as Target IP address? Should that be the the Gateway IP address of my Pfsense?
What? The openvpn wizard will setup the firewall rule to pfsense wan address.. You would not be doing a port forward for openvpn. Unless openvpn server was behind pfsense, and that is going to have its own problems with most likely asymmetrical traffic flow.
Again if you do not see traffic on pfsense WAN, then how would openvpn work? You need to validate your client is actually trying to talk to PUBLIC pfsense wan IP.. or if you have something natting in front of pfsense. Than that PUBLIC ip and that whatever is natting in front of pfsense is sending to pfsense wan IP.
On the all off the tutorials people saying "Via Wizard hit at the end to create firewall rules also, ports should be open on the NAT.." i am stuck on here

I think there somehting with my openVPN config or OpenVPNexport. Because i don't see any traffic when connecting from client, that file is not correct or is not comunicating with that public IP. Also on that Wizard i don't see any option to fill my public IP address..
-
You don't need to fill in anything with the openvpn wizard, other then select the wan interface! You do not have to put in a IP.
What IP or fqdn is your client pointing to?
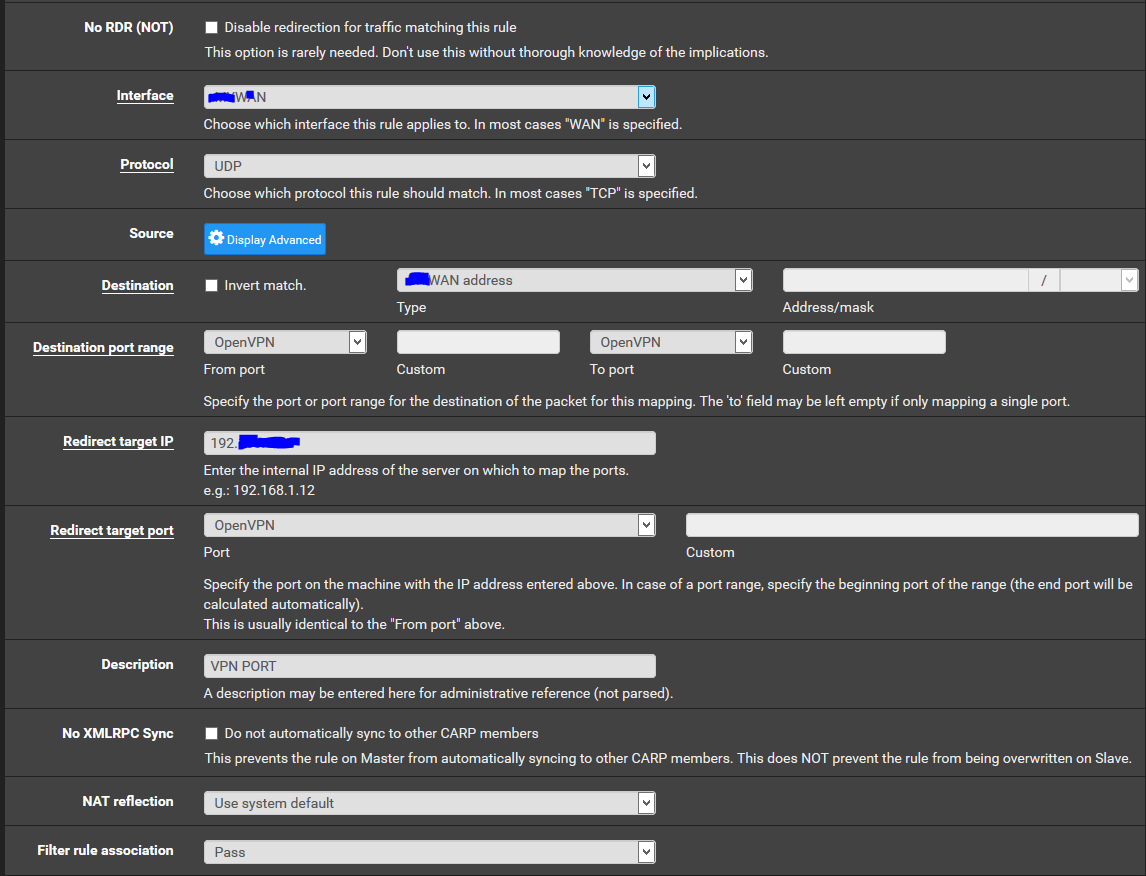
In the export wizard for your client, you can pick what you want the client to point to
ports should be open on the NAT.." i am stuck on here
Where does it say this???
https://docs.netgate.com/pfsense/en/latest/recipes/openvpn-ra.html -
So simple as that.... this was the solution... it was by me on interface IP address!!!! changed that to other and filled in my public IP on Other..
Another question, when i have created the OpenVPN via Wizard it have created an interface but not assigned in the assignments page. Do i need to assign that? (Without that VPN works now like a charm)
Available network ports: opvns1 (VPN)
-
No for Remote Access vpn setups you do not need to assign an interface.. You would adjust any firewall rules you wan in the openvpn tab on the firewall rules.
-
@johnpoz said in OpenVPN will not connect:
No for Remote Access vpn setups you do not need to assign an interface.. You would adjust any firewall rules you wan in the openvpn tab on the firewall rules.
I think that should be now correct, have only one OpenVPN rule there.
When connected via my Phone with VPN i like to use my pfblocker settings such as AD blocker etc.. what do i need to fill in the DNS or do i need to set redirect gateway on Openvpn server settings?
-
Well you would need to make sure your phone is sending all traffic down the vpn, ie internet not just your networks behind pfsense. Yes this would be the redirect all traffic setting.
Also you will need to make sure pfsense IP is being given as dns. And will also want to make sure your remote vpn clients IP (the tunnel network) is allowed to query unbound.
This would be done via your ACLs on unbound settings. Out of the box unbound would not allow this vpn tunnel networks IP to query it.
-
I have now problem when with connecting via OpenVPN. I get this error on pfsense Logs when trying to connect from Mobile Phone.
- TLS Error: incoming packet authentication failed from [AF_INET]xxxxxxxx:yyyy - Authenticate/Decrypt packet error: packet HMAC authentication failed -
@erbalo said in OpenVPN will not connect:
I have now problem
Undo the (latest) OpenVPN server settings change.
Or
Keep the OpenVPN server settings - ad export your OpenVPN client config again to be imported in your phone. -
@gertjan said in OpenVPN will not connect:
@erbalo said in OpenVPN will not connect:
I have now problemUndo the (latest) OpenVPN server settings change.
Or
Keep the OpenVPN server settings - ad export your OpenVPN client config again to be imported in your phone.I just undo that, the first problem was the following error code, just i receive now this error on the pfsense logs when connecting from mobile or PC.
xxx.xxx.xxx.xxx TLS Error: TLS handshake failed -
@erbalo said in OpenVPN will not connect:
xxx.xxx.xxx.xxx TLS Error: TLS handshake failed
The x.x.x.x is the IP of the device with the VPN client ?
-
@gertjan said in OpenVPN will not connect:
@erbalo said in OpenVPN will not connect:
xxx.xxx.xxx.xxx TLS Error: TLS handshake failed
The x.x.x.x is the IP of the device with the VPN client ?
Yes, it is.
-
Ok, Then this is as clear as it gets :
@gertjan said in OpenVPN will not connect:
TLS Error: TLS handshake failed
means : This :
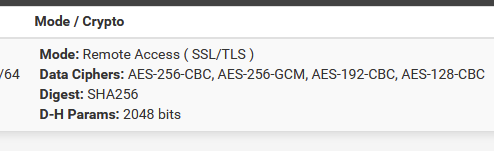
or, more specific : one or more items in this list (marked with a red cross ) :
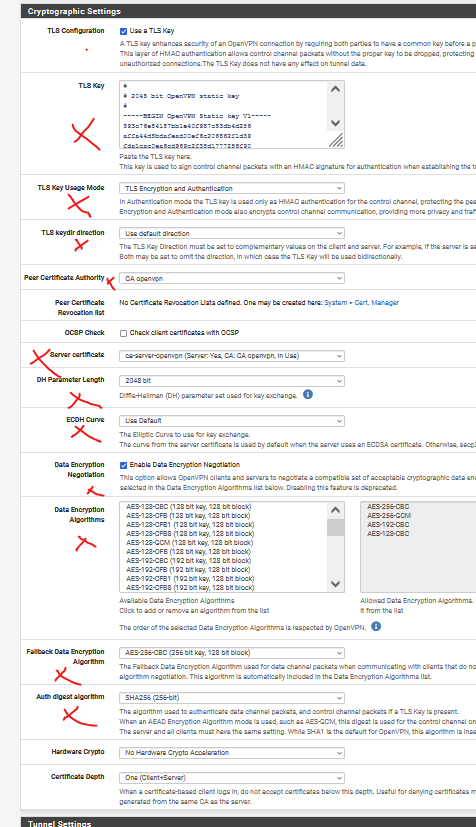
doesn't correspond with the OPVN client file (OpenVPN client settings).
The server disagrees with the client.
The servers throws out an 'error' : TLS Error: TLS handshake failed.edit : and before you think : "why does this happen to me ?"
The answer is a solid : "go talk with the admin".
We all see this error ones in a while. Rarely, it works 'right away'.
( at least, it never did for me ;) )What I normally do :
I compare the config file of the server and the client. These are small text files. Easy to read.
This is the old fashioned way of making to devices talk to each other : compare their settings on both sides - using a paper and pencil.Btw : also compare your OpenVPN server version number - and the OpenVPN client version number. If they differ, you also have to read the OpenVPN doc of both version, that is, the details of all the settings used. You're good for a visit at openvpn.org - the section 'manual'.
Just you know an OpenVPN setup can be activated in less then 8 minutes : do this https://www.youtube.com/watch?v=jQHqPq7ftz4 ;)