Building my lan: do I need a managed switch for my VLANs?
-
What JP said id correct , you would have the possibility to route if you get a L3 switch. And don't need to enable that at the beginning.
I'm purely L2 , and everything has to pass my pfSense.
I have not missed L3 yet .... -
The reason you would get an L2 over an L3 is cost savings, and no plans of ever routing on it. I have no idea what I might want to do different on my home network, or what to test out..
If a more feature rich switch is in your budget - I would say get it.. Like I said you can never have too many features or options..
Like buying a car, not getting fully loaded. And then winter comes and gawd daggit, wish my seats were heated ;) Damn it what do you mean have to roll down these windows by hand.. What no SiriusXM? The radio only gets AM? WTF!!! ;)
-
@johnpoz said in Building my lan: do I need a managed switch for my VLANs?:
The reason you would get an L2 over an L3 is cost savings, and no plans of ever routing on it.
Totally agree - It was cost & 24/7 power usage , that made me chose the 1210's , i also have a few HP-1820. But like the D-Link's better , featurewise.
My home net is so small , that i don't have to think (worry) about segmenting due to # of clients.
I purely segment for security reasons , hence i would not want to do any L3 on the switch.
But you'll never know ...
When you might just wished you had ... -
For example - the unifi switches, all L2.. But the cost is inline with a sg350.. Why would I get that L2 vs a switch that can do L3 and more..
The USW-24 is $225 has 26 ports total, and 2 of those you have to use sfp module (extra cost)
The sg350-28 is $229 has 28 ports total, and can use up to 4 sfps (combo ports)Why would you not get the L3 capable switch. And 2 more ports for $4 ;)
But hey if you can find say a 24 port L2 that does all that you want currently. And is half the cost of 24 port that can do L3.. Then you might want to do that - but to be honest you find prob not all that much difference in cost.
-
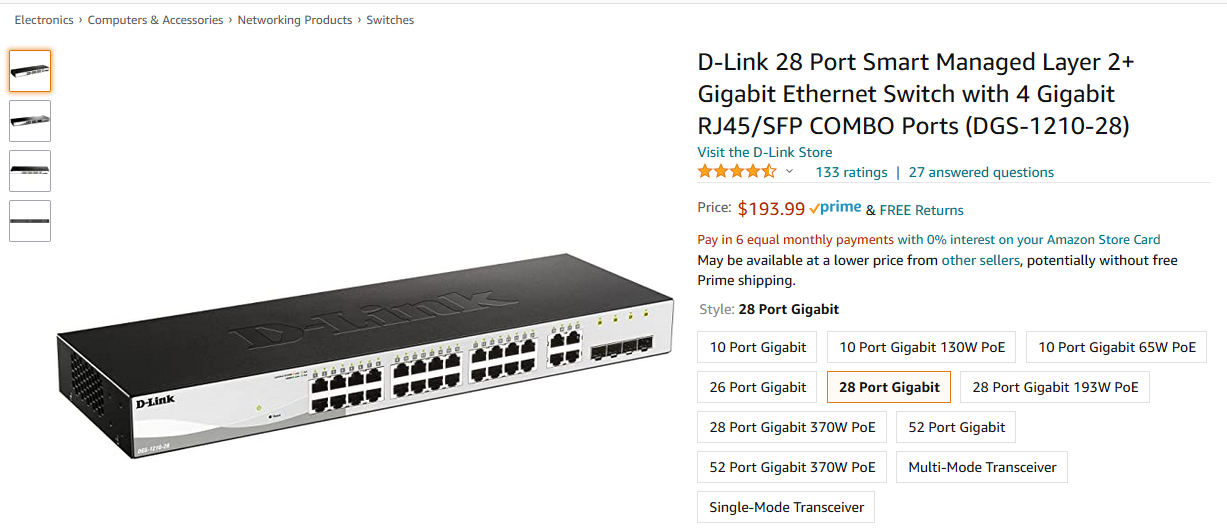
The 28 (24 plus 4 Dual) port DGS-1210-28 is $138 incl. shipping on Amazon.de
https://www.amazon.de/D-Link-DGS-1210-28-1000Mbit-SFP-Slots-l%C3%BCfterlos/dp/B008R7114W/
/Bingo
-
@bingo600 said in Building my lan: do I need a managed switch for my VLANs?:
DGS-1210-28
That good price... I show it as 193 here
-
Just bought a DLink DGS-1210-28.
Where can I find some tutorials how to setup it?Thanks
-
@valepe69 said in Building my lan: do I need a managed switch for my VLANs?:
Just bought a DLink DGS-1210-28.
Where can I find some tutorials how to setup it?Thanks
Google is your friend here.
The D-Links come with a default ip :
10.90.90.90 , and i think admin/admin for login. -
@bingo600 ok thanks.
Any tips about what to do and not to do setting up the switch? My LAN is composed by few VLANs.
Router will assign DHCP to the devices in these VLANs and it will allow or deny inter-vlan traffico.
Thanks again -
@valepe69 said in Building my lan: do I need a managed switch for my VLANs?:
@bingo600 ok thanks.
Any tips about what to do and not to do setting up the switch? My LAN is composed by few VLANs.
Router will assign DHCP to the devices in these VLANs and it will allow or deny inter-vlan traffico.
Thanks againIt might be smart to define the L2 vlans early.
The you can set the switch management ip to belong to a VlanDuring the initial management ip setup - Do NOT save the config , until it works.
That way you can always reboot , and get back to factory defaults.I seem to remember you can factorydefault the switch , by pressing a thin thing into the little reset hole , and wait for all switchport leds to lihht up yellow.
-
First off, you have to decide what's going on the VLANs and then plan from there. For example, I use a VLAN for guest WiFi and the 2nd SSID connects via a VLAN. In offices, VLANs are often used for VoIP phones, etc..
Then, once you've done that you have to ensure you use the same VLANs throughout, from pfsense to the switches, to whatever devcie, such as AP, etc..
-
@valepe69
How is it going , with the switch & Vlans -
@bingo600 Sorry, I haven't do anything yet. My times are stretching sometimes due to four little kids
-
@valepe69 said in Building my lan: do I need a managed switch for my VLANs?:
@bingo600 Sorry, I haven't do anything yet. My times are stretching sometimes due to four little kids
Whoaa
Configuring a few Vlans should be easy, compared to 4 small kids
Take care
/Bingo
-
@bingo600 yeah, I think so but some evenings I prefer the sofa to the pfSense box...

After VLANs, my next goal is to set the hairpin equivalent: DNS resolver (I read that I can't use forwarder because resolver is used by pfblockerng).
Luckily holidays are coming...
-
@valepe69 said in Building my lan: do I need a managed switch for my VLANs?:
set the hairpin equivalent: DNS resolver
huh? Resolver works and is the default out of box - there is nothing to do really. What do you mean by hairpin?
-
@johnpoz now I have an edgerouter. The hairpin Nat allows the clients to reach an internal server using the public domain.
I read that I should use DNS resolver to do that in pfSense. Am I right? -
ah you mean nat reflection..
You can continue to do nat reflection if you want. But better solution is just split dns, ie a host override. This can be done with unbound or the forwarder.
BTW, while unbound resolves out of the box. If you really have your heart set on forwarding - unbound can be set to forward as well.
-
@johnpoz well, I went to Nat reflection due a edgeos constraint.
Which is the best solution in pfSense? -
Best solution is always split dns.. No matter what your using as your router.
How would it ever be optimal to hairpin any traffic? It gets you nothing.. The only time it makes sense as a work around to do nat reflection. Is when the client on the same network as the services is forced to use some external dns. Or for whatever reason the IP your trying to access is hardcoded in some app your using or something.
If what your trying to access is via a fqdn, and whatever it is accessing it is using your local dns - then split dns and pointing the client to the local IP vs the public is the better solution.