Need help with my VLAN firewall rules to make sure they do what I think they do
-
I'm setting up VLANs and FWs for the first time. I want to make sure my understanding is right and there aren't any obvious mistakes that I'm missing.
I have 4 VLANs:
VL10_dmz- a single server running numerous services in Docker
- some Docker containers will be internet accessible (HTTPs and Plex to start with)
- needs to be able to make HTTP, HTTPS, and FTP calls out for
apt - should only allow SSH in from
VL20_trust
VL20_trust- my home computers and Roku
- should be able to SSH to
VL10_dmz - should have un-restricted internet access
- devices should not be able to talk to each other unless I specify the allowed IPs/ports (nothing to start with)
- I don't think I can actually do this since they are all in the same VLAN and the switch will handle it, not pfSense
- Since my Roku is on the same VLAN as my iPhone, I assume I don't need any special rules for letting me use the iOS app to control the Roku
VL30_iot- IoT
- devices should be able to talk to each other but no other VLANs
- should have un-restricted internet access
- shouldn't be able to access pfSense
VL40_guest- Guest
- devices should not be able to talk to each other
- I don't think I can actually do this since they are all in the same VLAN and the switch will handle it, not pfSense
- should have un-restricted internet access
- shouldn't be able to access pfSense
These are the rules I've come up with:
interface: WAN
action address family protocol src des description blockIPv6anyanyanyblock everything IPv6 from WANblockIPv4anyanyanyblock everything IPv4 from WANinterface: LAN
action address family protocol src des description rejectIPv6anyanyany:anyreject everything IPv6 from LANpassIPv4udpLAN net127.0.1.1:NTP (123)port forwarding of NTP from LAN to pfSensepassIPv4tcp/udpLAN net127.0.1.1:DNS (53)port forwarding of DNS from LAN to pfSensepassIPv4tcp/udpLAN netLAN address:HTTP (80)pfSense anti-lockout rule for LAN: HTTPpassIPv4tcp/udpLAN netLAN address:HTTPS (443)pfSense anti-lockout rule for LAN: HTTPSpassIPv4tcp/udpLAN netLAN address:SSH (22)pfSense anti-lockout rule for LAN: SSHpassIPv4icmp/Echo requestLAN netany:anyallow pinging from LANpassIPv4tcp/udpLAN netany:anyallow LAN to access anythingrejectIPv4anyanyany:anyreject everything else IPv4 from LANinterface: V10_dmz
action address family protocol src des description rejectIPv6anyanyany:anyreject everything IPv6 from V10_dmzpassIPv4udpV10_dmz net127.0.1.1:NTP (123)port forwarding of NTP from V10_dmz to pfSensepassIPv4tcp/udpV10_dmz net127.0.1.1:DNS (53)port forwarding of DNS from V10_dmz to pfSensepassIPv4tcpV10_dmz net!Network=192.168.0.0/16:HTTPallow V10_dmz outside of the local network: HTTPpassIPv4tcpV10_dmz net!Network=192.168.0.0/16:HTTSallow V10_dmz outside of the local network: HTTPSpassIPv4tcpV10_dmz net!Network=192.168.0.0/16:FTPallow V10_dmz outside of the local network: FTPpassIPv4tcpV10_dmz net!Network=192.168.0.0/16:43allow V10_dmz outside of the local network: WHOISrejectIPv4anyanyany:anyreject everything else IPv4 from V10_dmzinterface: VL20_trust
action address family protocol src des description rejectIPv6anyanyany:anyreject everything IPv6 from VL20_trustpassIPv4udpVL20_trust net127.0.1.1:NTP (123)port forwarding of NTP from VL20_trust to pfSensepassIPv4tcp/udpVL20_trust net127.0.1.1:DNS (53)port forwarding of DNS from VL20_trust to pfSensepassIPv4tcp/udpVL20_trust netVL20_trust address:HTTP (80)pfSense anti-lockout rule for VL20_trust: HTTPpassIPv4tcp/udpVL20_trust netVL20_trust address:HTTPS (443)pfSense anti-lockout rule for VL20_trust: HTTPSpassIPv4tcp/udpVL20_trust netVL20_trust address:SSH (22)pfSense anti-lockout rule for VL20_trust: SSHpassIPv4icmp/Echo requestVL20_trust netany:anyallow pinging from VL20_trust to anythingpassIPv4tcpVL20_trust netVL10_dmz address:SSH (22)allow VL20_trust to SSH to VL10_dmzpassIPv4tcp/udpVL20_trust net!Network=192.168.0.0/16:anyallow internet for VL20_trustrejectIPv4anyanyany:anyreject everything else IPv4 from VL20_trustinterface: VL30_iot
action address family protocol src des description rejectIPv6anyanyany:anyreject everything IPv6 from VL30_iotpassIPv4udpVL30_iot net127.0.1.1:NTP (123)port forwarding of NTP from VL30_iot to pfSensepassIPv4tcp/udpVL30_iot net127.0.1.1:DNS (53)port forwarding of DNS from VL30_iot to pfSensepassIPv4tcp/udpVL30_iot net!Network=192.168.0.0/16:anyallow VL30_iot access to anything but the local network (the internet)rejectIPv4anyanyany:anyreject everything else IPv4 from VL30_iotinterface: VL40_guest
action address family protocol src des description rejectIPv6anyanyany:anyreject everything IPv6 from VL40_guestpassIPv4udpVL40_guest net127.0.1.1:NTP (123)port forwarding of NTP from VL40_guest to pfSensepassIPv4tcp/udpVL40_guest net127.0.1.1:DNS (53)port forwarding of DNS from VL40_guest to pfSensepassIPv4tcp/udpVL40_guest net!Network=192.168.0.0/16:anyallow VL40_guest access to anything but the local network (the internet)rejectIPv4anyanyany:anyreject everything else IPv4 from VL40_guest
One thing I am unsure of is if I need my reject rules. In theory, shouldn't it reject everything that doesn't match a previous rule?
-
You can't use 127.0.0.1 as a destination in a lan firewall rule. Its pointless
Use this firewall instead
And what do you mean by port forwarding of ntp from vlan to pf?
You are not natting anything inside your vlans, are you? -
@netblues said in Need help with my VLAN firewall rules to make sure they do what I think they do:
You can't use 127.0.0.1 as a destination in a lan firewall rule. Its pointless
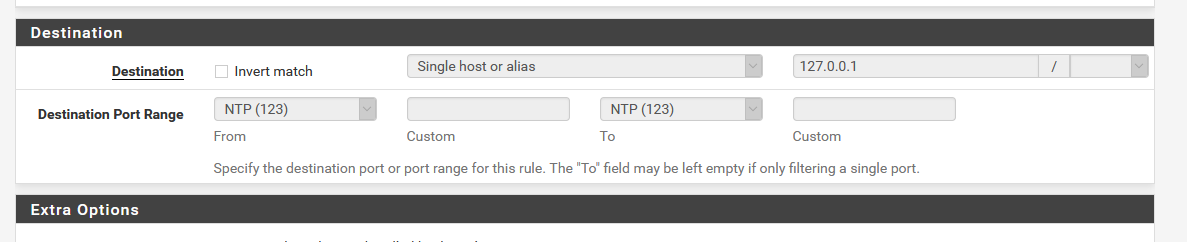
What do you mean? The pfSense guide has it: https://docs.netgate.com/pfsense/en/latest/recipes/dns-redirect.html. When I add that port-forward it will auto-create the FW rule and I can't edit the destination.
@netblues said in Need help with my VLAN firewall rules to make sure they do what I think they do:
And what do you mean by port forwarding of ntp from vlan to pf?
I want all NTP and DNS queries from any VLAN to be sent back to my pfSense box to handle them.
@netblues said in Need help with my VLAN firewall rules to make sure they do what I think they do:
You are not natting anything inside your vlans, are you?
Uh, not that I know of?
-
But I am having an issue. On my Windows machine (the only one I've tested so far), when I try to go to a site, it does a DNS query on the VLAN gateway. So if I am on the machine
192.168.10.100, the DNS query goes to192.168.10.1. But since I don't have any FW rule or redirect to handle that, it fails. The redirect says anything but192.168.10.1.Is my configuration wrong? What do I need to fix?
-
@imthenachoman Ah, I didn't get you were trying to redirect dns to pfsense in the first place.
Have you verified that normal dns resolution works using pfsense lan address as a resolver from your windows client?
You do have to allow dns requests (udp/tcp) to reach the configured lan interface address on pf.
-
I have not read all the above (rules) , and am not using DNS redirect. My guess is it happens like this.
The pfSense "redirect" would "catch all" traffic destined for port XXX (here 53/123) , and reroute it to the pfSense IP dest. 127.0.0.1 (localhost).
This would mean that pfSense would handle (answer) those requests.But in order for the request packet to be processed at all , you will have to allow it to enter the interface via a fw rule.
I'm only allowing DNS requests to "TFW" (this firewall) , meaning all pfSense interfaces , and have the pfSense IF set as DNS in all my DHCP definitions. If my clients try to ask another DNS ip , the package would be blocked.
But with your redirect setup (more elegant), i would expect that you can allow DNS to "any" in the firewall rule. As the redirect should catch all requests , and redirect them to he pfSense (localhost). And the client using a "foreign" dns , will still get an answer (from pfSense).
So you need two rules.
1: Allow DNS to enter via the interface.
2: Firewall redirect rule/Bingo
-
@netblues said in Need help with my VLAN firewall rules to make sure they do what I think they do:
Have you verified that normal dns resolution works using pfsense lan address as a resolver from your windows client?
I don't follow. From what I can tell, even on the default LAN interface, Windows was using
192.168.1.1as the DNS server and ergo not redirecting DNS queries back to pfSense because the redirect rule says! LAN addressand192.168.1.1isLAN address.You do have to allow dns requests (udp/tcp) to reach the configured lan interface address on pf.
Yes, isn't that what the port forwarding rules are? Those were addedautomatically when you add the redirect rule.
-
@bingo600 said in Need help with my VLAN firewall rules to make sure they do what I think they do:
The pfSense "redirect" would "catch all" traffic destined for port XXX (here 53/123) , and reroute it to the pfSense IP dest. 127.0.0.1 (localhost).
Yes but the issue is it's not. The redirect rule, per the instructions on the pfSense site, says to redirect all :53 traffic that is
notinterface address. However, Windows is sending DNS to the interface gateway which is theinterface address. -
I have not looked to closely at these rules.. But lot of them make no sense.
Why do you have block on wan? This is the default, there is not reason for those rules.
Also if your trying to redirect traffic for dns/ntp, why do you have 127.0.1.1 vs 127.0.0.1?
Other rules make no sense either. You have a "antilockout" rule listed to allow 22 to vlan20 address - when does ssh use UDP? But then you also have a rule allowing 22 to the dmz address? What is the point of that, ssh to pfsense vlan20 address is the same thing as ssh to its dmz address.. Did you mean dmz net?
Also you have a reject any any at the end? Why default is deny, there is no reason for that rule at the end? Do you specifically want to send a reject vs just drop? If so that ok that rule could have value. You understand the difference between reject and block right?
Same goes for all your ipv6 rules.. Deny is the default - there is no reason to put those rules in, if there is no allows for it anyway. Are you wanting to log or not log some of this traffic.. You don't state which rules are listed as logging or not logging..
Seems like you went to a lot of trouble to post up those rules in such a way.. with the markup and all.. But its not every easy to look at...
Would of been easier to just post up screenshot of the actual rules - including your port forwards.
From the way you posted those rules - I don't see how dns would work since your trying to redirect it to something that will not answer.. 127.0.1.1
Also ! rules, or inverse rules can be problematic if you have any vips setup, etc. I would suggest you use explicit deny rules..
-
@johnpoz said in Need help with my VLAN firewall rules to make sure they do what I think they do:
...
The
127.0.0.1is a typo. It should be127.0.0.1.You're right on the reject rules. This is my first time playing around with FW rules and I wasn't sure at first. I've cleaned my rules up.
when does ssh use UDP
My mistake. Will fix.
But then you also have a rule allowing 22 to the dmz address? What is the point of that
I want all devices in VL20_trust to be able to SSH to devices in VL10_dmz. But ignore that rule for now. I haven't actually added it cause I'm trying to get the other rules to work first.
Right now I am trying to make it so client DNS queries all go through pfSense. And they sorta are, but not how I expect.
Looking at just my current
LANrule I created a redirect as mentioned here: https://docs.netgate.com/pfsense/en/latest/recipes/dns-redirect.html. My understanding of the rule is:- traffic on
LAN - going to anywhere
notLAN addresson port53 - redirect to
127.0.0.1:53(pfSense)
But the client is getting
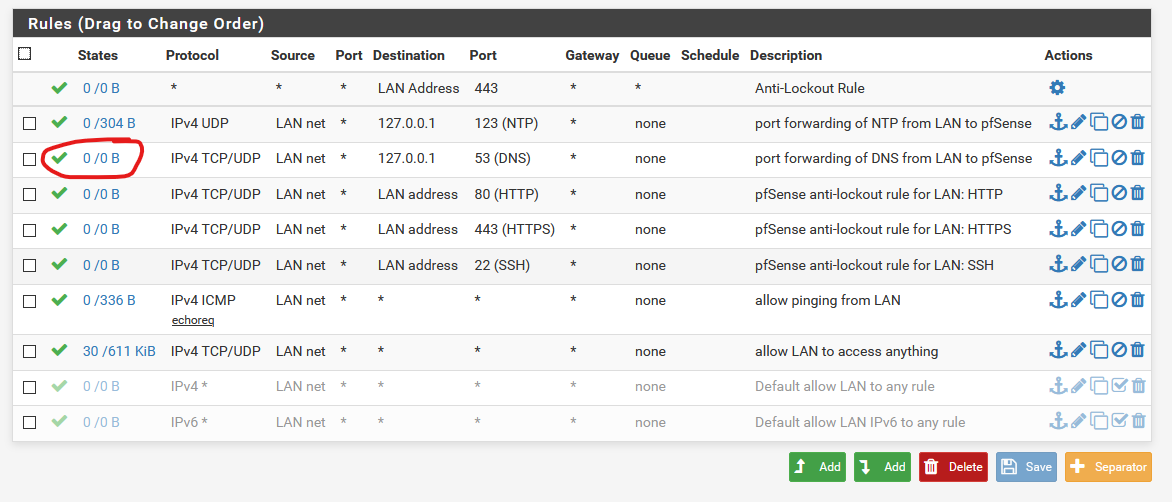
LAN address(192.168.1.1) as the DNS server so it is sending its DNS queries tointerface address(192.168.1.1). Ergo, the port forward rules don't get triggered.Below is picture of my port forward rule and
LANFW rules. No traffic is going to theLANDNSrule.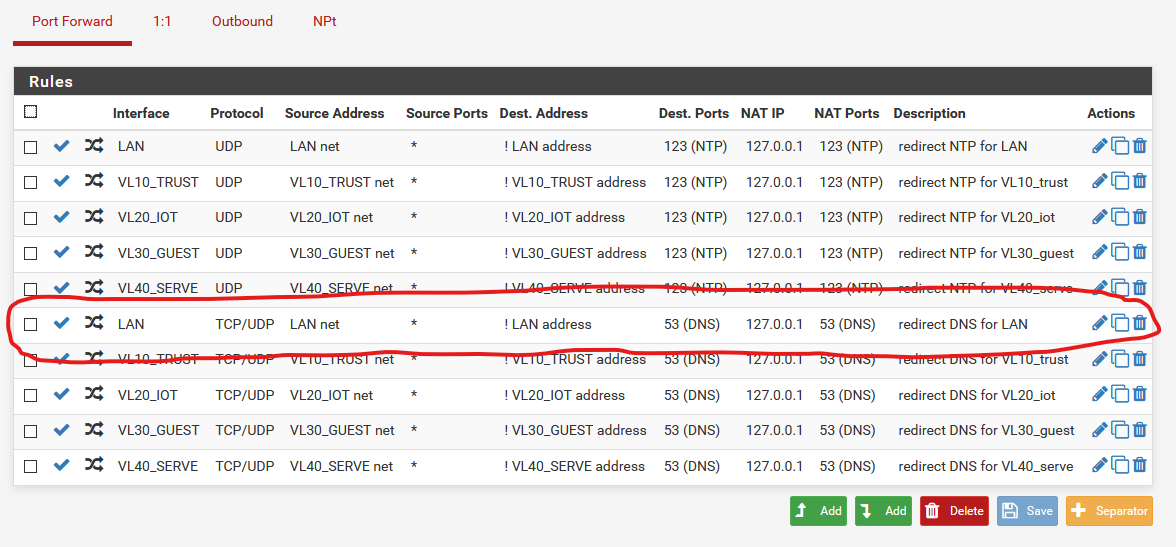
I followed the instructions in the recipe so I am not sure what is wrong. Is there something else I need to be doing? I feel like I am missing a step that is supposed to make it so DNS queries on LAN/VLAN address (like
192.168.1.1) also go to127.0.0.1:53? - traffic on
-
If your lan address is 192.168.1.1 on pfsense, that redirect would not come into play... Your port forward says if NOT lan address (192.168.1.1)
But your sending dns queries to 192.168.1.1..
If you want to test that rule, send directed dns query to say 8.8.8.8 or something..
-
I see. So the clients use the LAN/VLAN address as the DNS server. What do I need to do to make sure the DNS queries clients send, to the LAN/VLAN address, also get routed to 127.0.0.1? Another port forward rule?
-
@imthenachoman said in Need help with my VLAN firewall rules to make sure they do what I think they do:
I see. So the clients use the LAN/VLAN address as the DNS server. What do I need to do to make sure the DNS queries clients send, to the LAN/VLAN address, also get routed to 127.0.0.1? Another port forward rule?
How about changing from !LAN to "Any"
-
@imthenachoman said in Need help with my VLAN firewall rules to make sure they do what I think they do:
o the LAN/VLAN address, also get routed to 127.0.0.1? Another port forward rule?
what would it matter? They are going to the same place to be honest. They are still going to unbound be it loopback or 192.168.1.1 - still going to unbound.
-
Thanks. I was thinking that but then unsure since the pfsense recipe didn’t say that. I kinda assumed the recipe instructions would do what I need/expect — assuming it was written with the understanding that clients would get LAN IP as DNS server.
-
But the port forward rule says to forward anything NOT to the LAN IP. Since the clients are using the LAN IP as DNS server, the port forward rule never triggers. Or am I misunderstanding?
-
The forward rule is a "Catch any" and redirect to 127.0.0.1 (that's the pfsense).
The only thing not "Caught" is the DNS going directly to the LAN interface ... Who/what do you think handles the requests on the incomming Lan interface ??

/Bingo
-
I see. So I guess I need a FW rule to allow clients to access LAN address. I don’t think I have that right now. :/
-
EUREKA!
So I had to add another FW rule that says allow IPv4 TCP/UDP from LAN net to LAN net on 53. I can see that rule working.
Thanks all!
-
@imthenachoman said in Need help with my VLAN firewall rules to make sure they do what I think they do:
I don’t think I have that right now. :/
yeah you do
That rule allows anything - if there was not a specific deny above that - then it would be allowed.
Rules are evaluated top down. first rule to trigger wins, no other rules are evaluated. So if your trying to talk to 192.168.1.1 on 53 you have no rules above that any any rule that would block that or force it elsewhere - so its allowed. by your last rule.