VLANs, What am I doing wrong?
-
@johnpoz Bah... I was going to say the bottom line is the OP has his trunk port misconfigured, but after re-reading the thread, I noticed you posted that... and not the OP... smh.
Either way, re-verifying the config on his trunk port is still a valid step. I would also verify the config on the access ports, which we could help with if we could see the config as @johnpoz suggested.
-
From the link he posted - yeah the port connected to pfsense g2 is just access.. So no vlans are going to work.. And not sure how he would even be getting any ips via dhcp that is for sure.. Not from pfsense.
-
For simplicity, I set the ports to only use VLAN 99:
cisco#show vlan VLAN Name Status Ports ---- -------------------------------- --------- ------------------------------- 1 default active 10 IOT active 20 LCHR active 99 MGMT active Fa0/2, Gi0/2 100 BLACKHOLE active Fa0/1, Fa0/3, Fa0/4, Fa0/5 Fa0/6, Fa0/7, Fa0/8, Fa0/9 Fa0/10, Fa0/11, Fa0/12, Fa0/13 Fa0/14, Fa0/15, Fa0/16, Fa0/17 Fa0/18, Fa0/19, Fa0/20, Fa0/21 Fa0/22, Fa0/23, Fa0/24, Gi0/1 1002 fddi-default act/unsup 1003 token-ring-default act/unsup 1004 fddinet-default act/unsup 1005 trnet-default act/unsup VLAN Type SAID MTU Parent RingNo BridgeNo Stp BrdgMode Trans1 Trans2 ---- ----- ---------- ----- ------ ------ -------- ---- -------- ------ ------ 1 enet 100001 1500 - - - - - 0 0 10 enet 100010 1500 - - - - - 0 0 20 enet 100020 1500 - - - - - 0 0 99 enet 100099 1500 - - - - - 0 0 100 enet 100100 1500 - - - - - 0 0 1002 fddi 101002 1500 - - - - - 0 0 1003 tr 101003 1500 - - - - - 0 0 1004 fdnet 101004 1500 - - - ieee - 0 0 1005 trnet 101005 1500 - - - ibm - 0 0 Remote SPAN VLANs ------------------------------------------------------------------------------ Primary Secondary Type Ports ------- --------- ----------------- ------------------------------------------cisco#show ip int br Interface IP-Address OK? Method Status Protocol Vlan1 unassigned YES manual up down FastEthernet0/1 unassigned YES unset administratively down down FastEthernet0/2 unassigned YES unset up up FastEthernet0/3 unassigned YES unset administratively down down FastEthernet0/4 unassigned YES unset administratively down down FastEthernet0/5 unassigned YES unset administratively down down FastEthernet0/6 unassigned YES unset administratively down down FastEthernet0/7 unassigned YES unset administratively down down FastEthernet0/8 unassigned YES unset administratively down down FastEthernet0/9 unassigned YES unset administratively down down FastEthernet0/10 unassigned YES unset administratively down down FastEthernet0/11 unassigned YES unset administratively down down FastEthernet0/12 unassigned YES unset administratively down down FastEthernet0/13 unassigned YES unset administratively down down FastEthernet0/14 unassigned YES unset administratively down down FastEthernet0/15 unassigned YES unset administratively down down FastEthernet0/16 unassigned YES unset administratively down down FastEthernet0/17 unassigned YES unset administratively down down FastEthernet0/18 unassigned YES unset administratively down down FastEthernet0/19 unassigned YES unset administratively down down FastEthernet0/20 unassigned YES unset administratively down down FastEthernet0/21 unassigned YES unset administratively down down FastEthernet0/22 unassigned YES unset administratively down down FastEthernet0/23 unassigned YES unset administratively down down FastEthernet0/24 unassigned YES unset administratively down down GigabitEthernet0/1 unassigned YES unset administratively down down GigabitEthernet0/2 unassigned YES unset up up@johnpoz The reason why this is a 10/100 is because a) it was free, and b) it's strictly for IOT shit that doesn't need anything faster. I'm using it to learn with. I have a second gbe switch that I use for my actual network. I've also swapped the AP for my laptop and VLANs still refuse to work, so either the switch config is wrong or PFSense is configured wrong. But from what I can tell, everything is correct (as I did set Gi0/2 to trunk mode after posting in the Cisco forum)
@NogBadTheBad What's wrong with Realtek? I understand that they're not great, but according to the PFSense docs, re# NICs should work with VLANs:
Ethernet interfaces with VLAN hardware support:ae(4), age(4), alc(4), ale(4), bce(4), bge(4), bxe(4), cxgb(4), cxgbe(4), em(4), igb(4), ixgb(4), ixgbe(4), jme(4), msk(4), mxge(4), nxge(4), nge(4), re(4), sge(4), stge(4), ti(4), txp(4), vge(4)
It also looks like you set the IP address/default gateway for vlan999. Stupid question, but is that for SSH access? When I started messing with VLANs on this switch, SSH stopped working so I've been having to use a console cable..
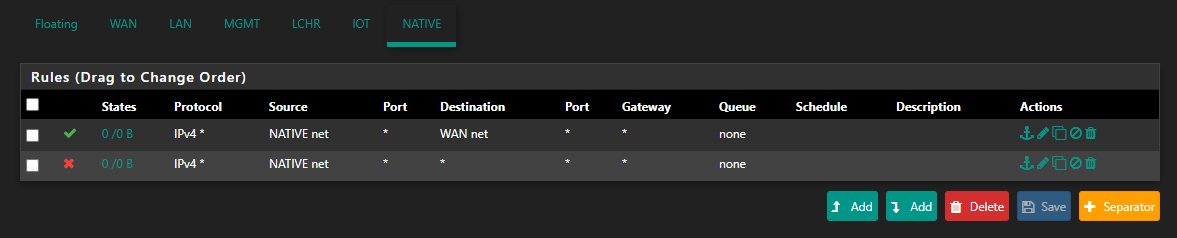
@netblues I only posted the firewall rules for one of the NICs because they're all the same:
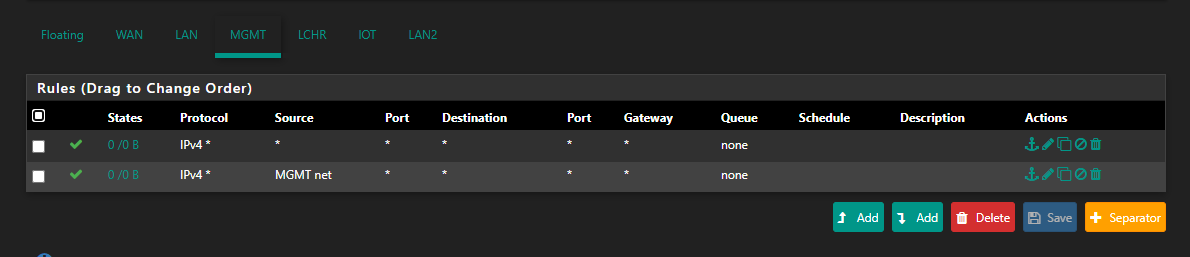 (I added the * -> * rule before reading your post but after making my post with the rules to see if it would make any difference. Spoiler alert, it doesn't.)
(I added the * -> * rule before reading your post but after making my post with the rules to see if it would make any difference. Spoiler alert, it doesn't.)
-
How do you think anything would work for vlans if you don't have the port connected to pfsense in trunk?
For vlans to work on pfsense. To talk to the other vlans. They have to be allowed on the port that is connected to pfsense.
I take it that is g2? Where is the config showing its trunked, and allowing the vlans you want to use?
From your latest showing - only vlan 99 is allowed. Which seems to be native untagged, so pfsense would see it on the native interface.
So sure your laptop in also in vlan 99, fa2 I take it.. Would be able to talk to any vlan IP on pfsense with your rules.
Does your laptop get an IP? Please post the config of the interfaces F2 and G2..
-
@johnpoz Here's a super basic image of my actual network:
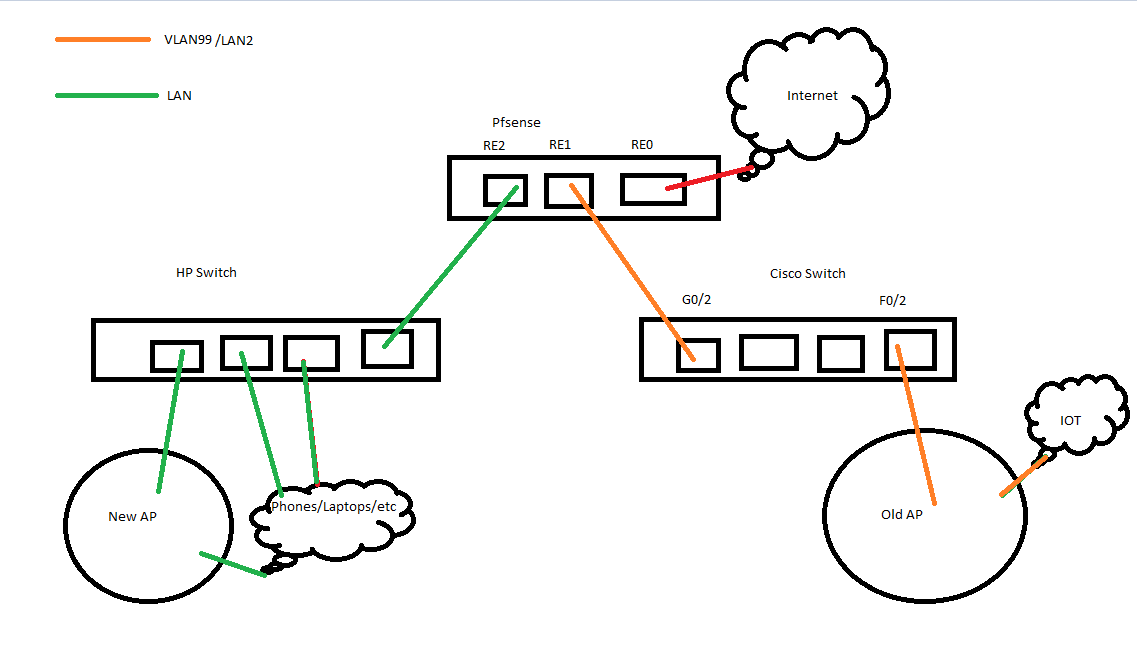
I do I have VLAN99/LAN2 (RE1) connected to G0/2 on the Cisco switch and F0/2 connected to the AP (or my laptop when I'm testing whether DHCP works or not).I think that answers your questions? Everything is wired up correctly, LAN2 is only active because it's the only interface in Pfsense I can get to work.
I don't fully understand tagged/untagged, or what you're referencing when you say native. This is what I'm trying to learn.
cisco#show running-config interface g0/2 Building configuration... Current configuration : 170 bytes ! interface GigabitEthernet0/2 switchport access vlan 99 switchport trunk encapsulation dot1q switchport trunk allowed vlan 1-99,101-4094 switchport mode access end cisco#show running-config interface f0/2 Building configuration... Current configuration : 156 bytes ! interface FastEthernet0/2 switchport access vlan 99 switchport trunk encapsulation dot1q switchport trunk allowed vlan 99 switchport mode access endPosting this now so I can edit in a few to see if DHCP works for my laptop.
Update: I disabled LAN2 and it DHCP failed to work.
-
@apathia said in VLANs, What am I doing wrong?:
switchport access vlan 99
switchport trunk encapsulation dot1qThat is wrong.. Which is it access or trunk?
Its either a trunk port, that carry vlan (tags).. Or its an access port that is not tagged or native.
Since your trying to use your re2 port with untagged vlan (your vlan 99 I believe).. Then your configuration should be trunk, with a native vlan set.. See my above example..
interface gigabitethernet5 description "sg4860 WLan and vlans" switchport trunk allowed vlan add 3-4,6-7,19 switchport trunk native vlan 2This carries vlans 3,4,6,7 and 19 as TAGGED, ie vlan in pfsense. And untagged.. The native interface.. So for example here are my interfaces from pfsense where I am currently using some of those vlans. (4 and 6)
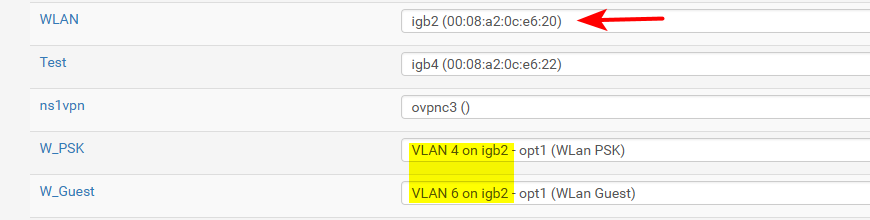
In this case traffic that is in vlan 4 or 6 is tagged, and pfsense sees the tags on my igb2, and knows that traffic is for vlan 4 or 6. While any traffic that is untagged.. in my case on the switch that is vlan 2.. Pfsense just see that traffic for the interface igb2 directly.. It is still a vlan on my switch.. Its just pfsense doesn't know that it is, and its just native traffic (untagged traffic)..
You can run many vlans on a port that are tagged. Cisco calls this a trunk port. If you also want to carry upto 1 vlan that is untagged, that is a native vlan for pfsense on a trunk port.
On a port in cisco where is is not tagged traffic, that would be a access port.. And the device connected that port doesn't see any tags.. This is where you would connect say a pc, or laptop or iot device. When you send traffic to your AP.. That will have say different SSIDs on different vlans. Then those are tagged, ie a trunk port.
-
@johnpoz I still don't entirely understand, but I managed to get it to work:
cisco#show running-config int f0/2 Building configuration... Current configuration : 159 bytes ! interface FastEthernet0/2 description "Wlan" switchport trunk encapsulation dot1q switchport trunk allowed vlan 1-99,101-4094 switchport mode trunk end cisco#show running-config int g0/2 Building configuration... Current configuration : 164 bytes ! interface GigabitEthernet0/2 description "rooter" switchport trunk encapsulation dot1q switchport trunk allowed vlan 1-99,101-4094 switchport mode trunk endI don't know why g0/2 was set to access, unless I mistyped something but today I learned how to actually check the interface config (thanks for asking for that, made me google it and find out how to do it).
-
While that would allow vlans to work... Are you using vlan 1 as native?
You seem to be allowing everything but vlan 100.. Even 1.. Which is never really tagged. This is the default vlan of switches.
I would change your allowed to be only vlans your actually using.. Or will use shortly.
But if you want to talk the network you have on re1, lan2 - you need to set that as native (untagged).. If your saying everything is working, I take it that is just whatever your using as vlan 1 on your switch?
Another option is just not use any untagged network on this interface. Set lan2 to be a vlan.. But unless you have gotten deep into the weeds with unifi, AP management IP needs to on a untagged vlan. They support vlans - I find it highly unlikely you have set that up.
Here this might help on what I mean by native
https://networklessons.com/switching/802-1q-native-vlan-cisco-ios-switchSince you seem to be using a different physical switch for network attached to re2, vlan 1 as your native is ok. But you need to make sure you understand tag vs untagged, and when they are and when they are not tagged.
-
Agreed. If you're essentially going to allow all VLANs, I would just remove the switchport trunk allowed command altogether.
Although, best practice is to only allow the VLANs that are in use over the trunk.
-
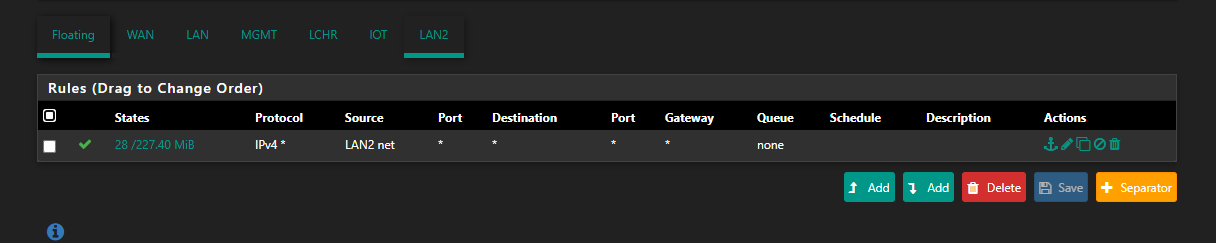
@johnpoz I think I get it now. LAN2/RE1 is on the physical interface so it's "untagged". The switch throws this on VLAN1 as that's the default VLAN for anything without a tag?
So essentially, the switch acts as if every packet is tagged, either explicitly or not. Non-explicit packets are thrown on the Native VLAN?
If that's what it means then that does make sense. I also only used sw tr all vlan all because I was initially having issues with adding specific VLANs although that may have been due to having g0/2 misconfigured as access instead of trunk.
Now that I have VLANs working, my AP is working just fine and assigning devices to the correct subnets.
Thanks for all the help!
My current config, btw:
cisco#show running-config int g0/2 Building configuration... Current configuration : 159 bytes ! interface GigabitEthernet0/2 description "rooter" switchport trunk encapsulation dot1q switchport trunk allowed vlan 10,20,99 switchport mode trunk end cisco#show running-config int f0/2 Building configuration... Current configuration : 154 bytes ! interface FastEthernet0/2 description "Wlan" switchport trunk encapsulation dot1q switchport trunk allowed vlan 10,20,99 switchport mode trunk end -
Yeah that looks better.. And is fine if your using vlan 1 as native.
I don't personally use vlan 1, this is habit from corp experience where vlan 1 is always disabled. And management lan is set to some other vlan.
But there is really nothing technically wrong with doing that. But if your going to say at some point connect your other port into the same physical switch.. And run a network on the physical port along with vlans as well on that other port.
You will need to understand how to change the native vlan on a trunk port, along with also understanding what pvid is. This where you set what vlan a switch puts untagged traffic into when it sees ingress into the port.
Your old school cisco for sure can help you with understanding these concept. Cisco terms might be a bit different than other makers.. In general if you know what a tag or untagged vlan, and how the switch handles ingress traffic without a tag you will be cooking with gas ;)
Glad you finally got it working how you want.
For your next assignment ;) If you choose to accept it ;)
Figure out how to put your AP management IP onto a tagged vlan..
And how to change your native vlan g2 to something other than vlan1.. -
Figure out how to put your AP management IP onto a tagged vlan..
You mean this?
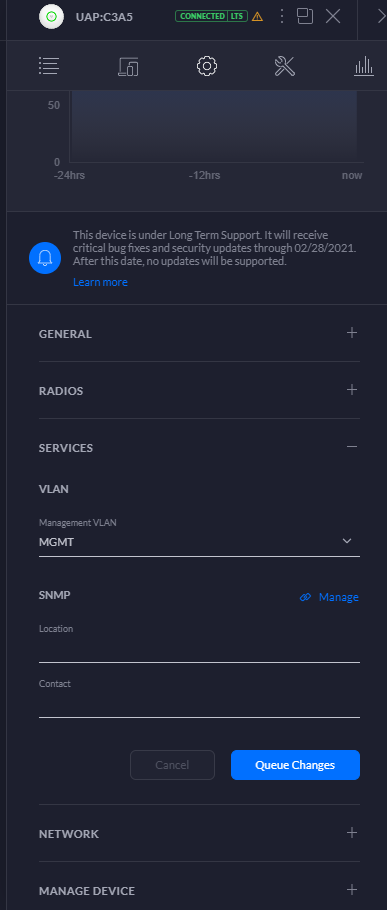
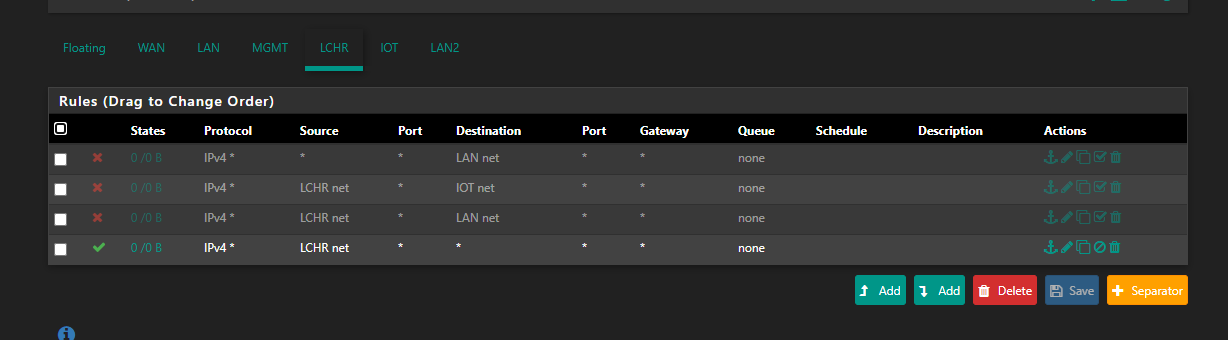
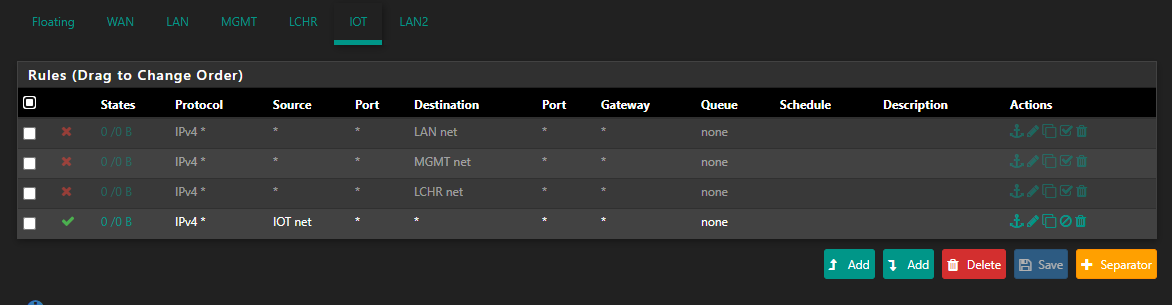
It was why I created the MGMT VLAN in the first place lol.. Once I figured out how to actually get the VLANs across the switch, the rest was relatively easy. Took me a bit to figure out why the AP would keep going offline when I switched it to the MGMT VLAN but I quickly clued into the PFSense rules, which again is what my plan was in the first place.
And how to change your native vlan g2 to something other than vlan1..
cisco#show running-config int g0/2 Building configuration... Current configuration : 191 bytes ! interface GigabitEthernet0/2 description "rooter" switchport trunk encapsulation dot1q switchport trunk native vlan 2 switchport trunk allowed vlan 10,20,99 switchport mode trunk end cisco# -
Do you have a vlan 2? Did you create one? ;)
Or just copy that command from my example ;)
But see how fast it clicks into place once you get what tagged and untagged mean.
Welcome to the world of vlans! Now you just need a switch that isn't 20 years old, and does gig on all its ports ;) I would go insane with 100mbps.. Be like watching paint dry trying to move files around.. Gig is even a bottleneck, I connected my pc to my nas via 2.5gbps so could move the files back and forth when I work on them.. ;)
But that switch is great for a lab.. How much juice does it draw? You might not want to leave it on 24/7 - those old things use to suck up some juice for sure.. 100w?
-
@johnpoz
I do now:
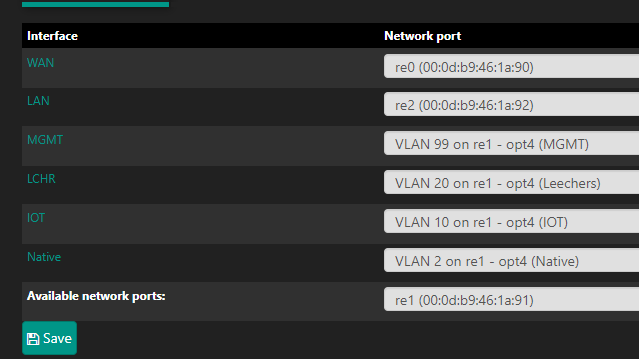
This I presume means that if I enable another port on the cisco, remove it from the BlackHole VLAN, and plug something in then it'll default to VLAN 2?
RE2/LAN is connected to an HP 2920-24G-PoE+ Switch. Not new, but not 10/100 either. This is what I use as my main network. I plan on getting VLANs set up on it too, but I also don't want to accidentally take myself offline when I mess things up so I want a decent handle on VLANs before I do anything with it. My "file server" is currently my media center PC so I don't have to worry about network transfer speeds too much as I play everything off it anyway. I do have an actual server (Intel something, can't remember which), but that thing not only sounds like a jet engine, but it also drastically increases my electric bill.
I don't think either of the switches suck up much juice, the HP switch is currently reporting ~10W from 3 POE devices connected to it so I can't imagine it's too much. Last months electricity bill was surprisingly on par with the previous years, despite me now working from home and having these two switches. I will say though, the Cisco is whisper quiet compared to the HP.
I might eventually chain the switches, Router --> HP --> Cisco, but I want to get a good handle on the VLANs and configuring things before doing that.
-
Does your HP also do vlans? If not I would do it that way I would do
router - cisco - hp
You can put a dumb switch downstream of a smart switch, and just everything on that dumb switch will just be 1 vlan.
What specific models of these switches? Can look up watch the cisco pulls. Is it 2950T-24, those are not all that bad only 30W max..
edit:
What do you want that rule to do? Your only going to be able to go to wan net, that doesn't allow you to do really anything.. Your not even allowing that network to query pfsense for dns.wan net is not the internet, its just the network your wan is attached to..
-
Is that a Unifi AP? If so, you can select an interface or VLAN when you configure it, though you can also move between one or the other later, as I had to do recently, when my pfsense firewall died. On my AP, the management interface is on my main LAN.
-
@johnpoz It's a WS-C3560-24PS-E, so looks like it it's 400+ W. The HP is an J9727A 2920-24G-PoE+ Switch, so it's also a managed switch. I think combined, they pull 800W max/
My goal with that rule was to restrict traffic, I was lazy and didn't want to add a separate rule restricting to the different VLANs but I guess that's not a thing.
@JKnott Yeah it is, I initially had it set up with defaults but now that I have a management VLAN, I've been moving appropriate devices over to it.
-
Well power MAX can for sure be misleading..
Great device to add to your tool belt, if you have any care to what devices draw.. Is a kill-a-watt meter..
Or a smart plug with power reading.. So you can plug a device in, and see what it actually draws.. Say leave it on the plug for 24 hours min.. And try and atleast use it a bit like you think you normally would..
Cost of elect can vary quite a bit.. But at the national average of like 12cents per kwh.. A 100W will cost you 100 Bucks a year. Not counting delivery cost of the elect as well, and taxes on that etc.. so going to be 100+ a year to run something that sucks 100w if left on 24/7/365
I have gotten pretty into how much something draws, even before I went solar.. So Im the blue line - guess when I went solar ;)
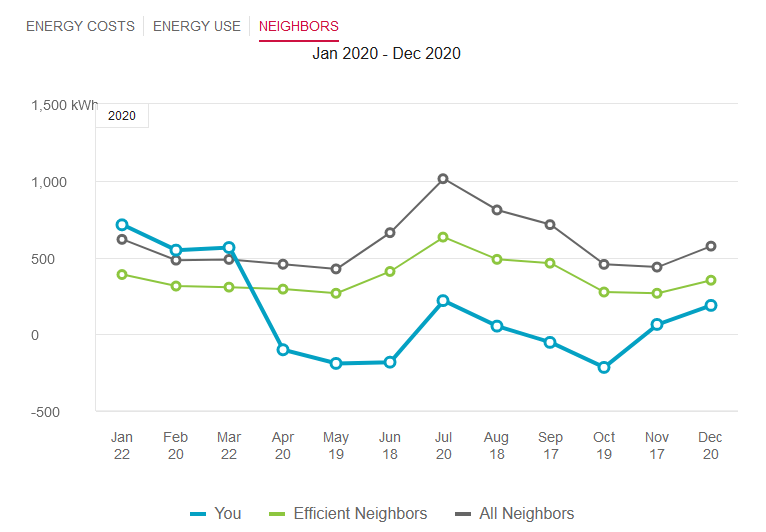
I always use to be above even my non efficient neighbors (all the networking/computer toys) ;) The part I like the most is where I am under the 0... This is where I produced more than I used.. Which is the goal..