IPSEC firewall rules udp/4500
-
Hello,
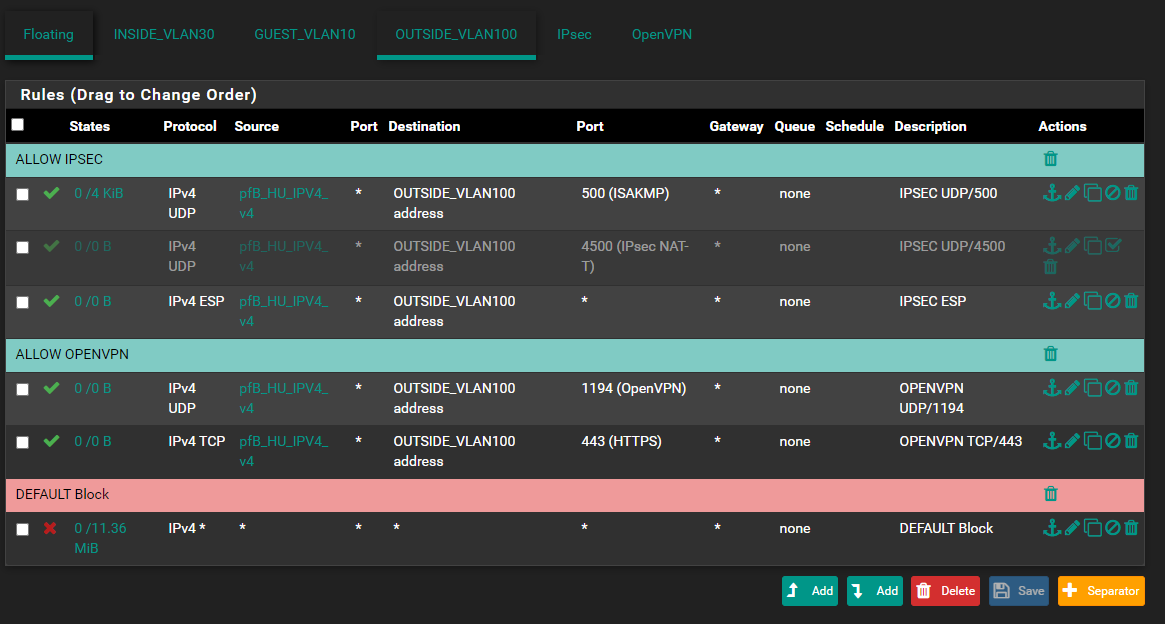
Please enlighten me, struggling to understand why my IPSEC mobile client can connect even if the udp/4500 rule is disabled.
So OUTSIDE is my WAN interface udp/500, udp/4500(disabled), ESP is allowed beside my OpenVPN ports and "Disable all auto-added VPN rules." IS checked.
I have tested on my notebook with a mobile hotspot and in the meantime checked the packets with wireshark.
UDP/4500 with ESP payload is flowing seemlessly.Why can I connect if the 4500 rule is disabled? Is this some kind of stateful behaviour?
WAN rules:
Thank you.
-
@mind12 The two most obvious options:
1: After you disable the rule you need to reload states if you used to connection up until disabling the rule. Otherwise the state is still present and allowed in pfSense.
2: Du you by any chance have a floating rule allowing the traffic?
-
@keyser
Thank you, your assumption was great.
It was option 1 and the previous states that had allowed the connection the new connection.
I guessed if I disconnect the VPN properly the firewall states also disapper "instantly" but it's not the case. Maybe I should have waited a little bit more before testing the connection again.Anyway it's such a relief that not my firewall rules were bad with a firewall hole somewhere.
-
@keyser said in IPSEC firewall rules udp/4500:
@mind12 The two most obvious options:
1: After you disable the rule you need to reload states if you used to connection up until disabling the rule. Otherwise the state is still present and allowed in pfSense.
I was wondering if you refered to "Diagnostics > States >Reset States " or something else, because "Resetting the state table is disruptive, but clients may immediately reconnect provided they are still passed by the current firewall rules."
-
@metisit Hi, almost, Diagnostics/States/states and I manually removed the respective connections using the bin button.