Big Enough State table
-
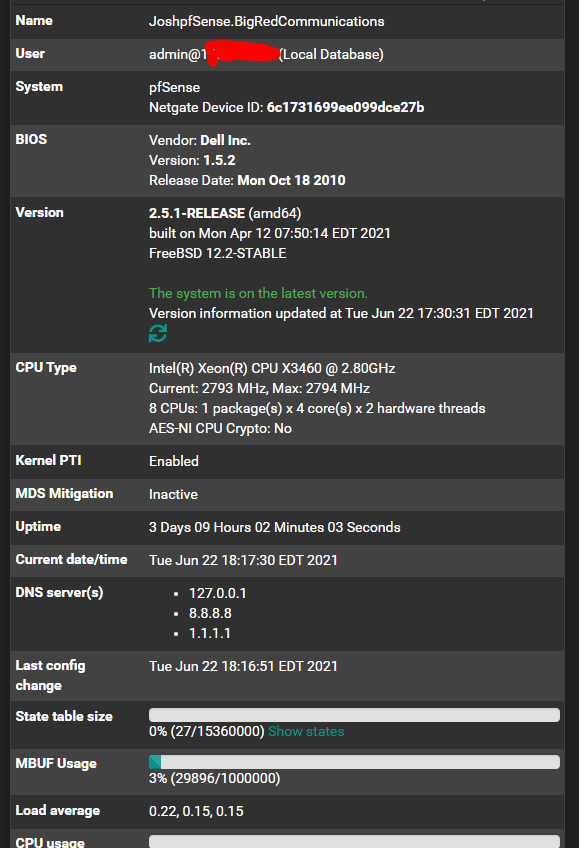
PfSense Newb and i kind of built this router so that i could have a beast for these large concerts im doing to just have an overkill of horse power. Goal is to get 10k to 20k clients connected and online. I was wondering if with these specs if i made the state table size either to small or to big. (15,360,000)Thank you in advance for the responses :)
-
@joshhboss You don't show how much RAM you have but I'll assume it's lots due to your state table size. The state table is held in memory and is limited by your RAM. 1 state = 1KB, 1000 states = 1 MB, 1M states = 1 GB etc. Each connection requires two states, one in one out. The number of states used varies per client depending on what they're doing. If your 20,000 users each accessed one simple Hello World web site, that will consume at least 40K states. Right now with a browser open with 11 tabs, a Nextcloud client and system stuff, I have 23 active states. If you err on the side of caution and assume 50 states per user, that's 1M states which can be held in a table 1G in size. Your table is 15x larger than that.
-
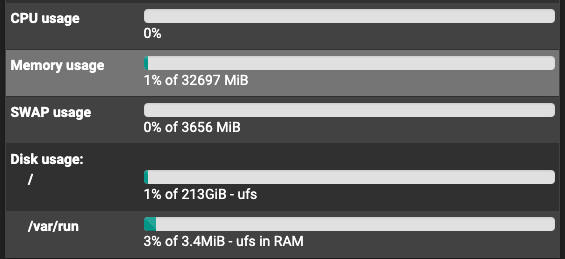
@kom i have 32 gigs of ram.. and actually building another pfsense server with 16 gigs of ram . ill be using both at the event..
Wow thanks for the explanation.. i cant believe i forgot to screen shot the ram size. -
-
Using that same style of thinking, the way you just broke down the 20K clients and the way they occupy states on the state table, how would i be able to determine how many public IPs i should request., i was thinking of using round robin in the source nat rules.
would it be 1,000,000 \ 65,536 = about 15.258? so get 16 publics?
Edit- Or wait would it actually be 500,000 since the port used to go out is the same port used to come back in, sorry i know its a Networking 101 type quesiton but im not sure.
Thank you ? -
@joshhboss I can't answer those questions because I have never had to manage a deployment at that scale. Unless someone else chimes in, you might want to consider contacting Netgate for a consultation quote.
-
Unrelated but useful nonetheless:
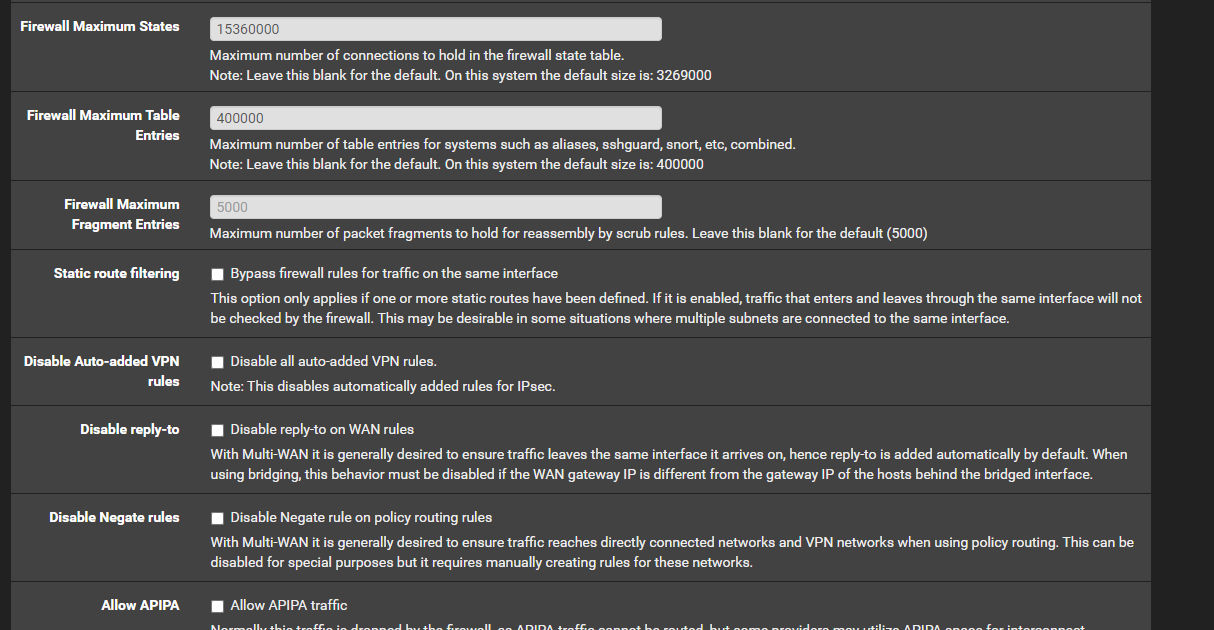
Firewall Maximum Table Entriesdefault of 400k is better bumped up to 500k if You will be dual-stack IPv4/IPv6 and doing BOGON filtering. The default was 200k years back. As the list grew it was bumped to 400k. In recent months I saw this insufficient sometimes so you may want to bump it to 500k while you're on that config page.
-
@mfld ill do that.. thanks a lot!