Sharing a Port with OpenVPN and a Web Server
-
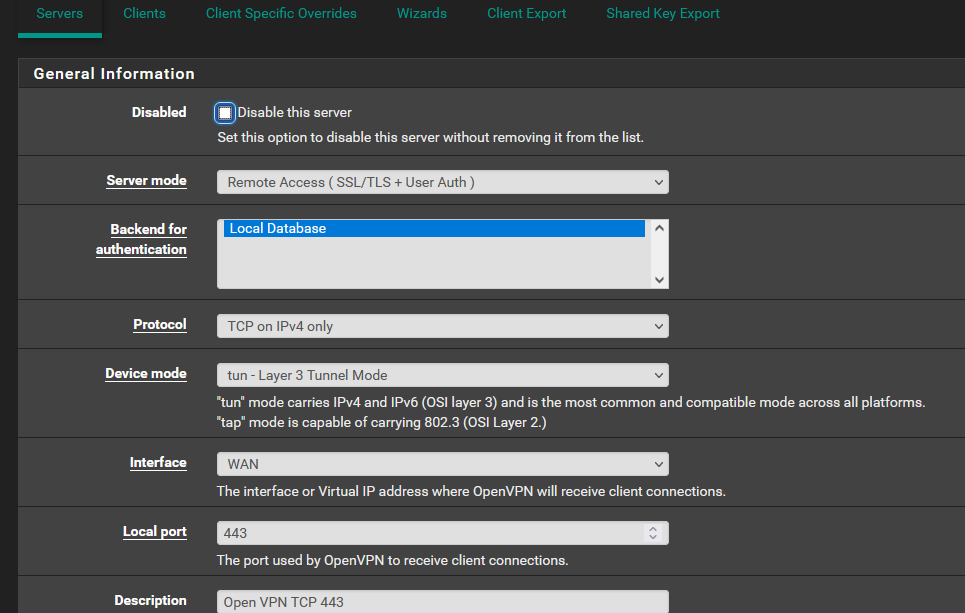
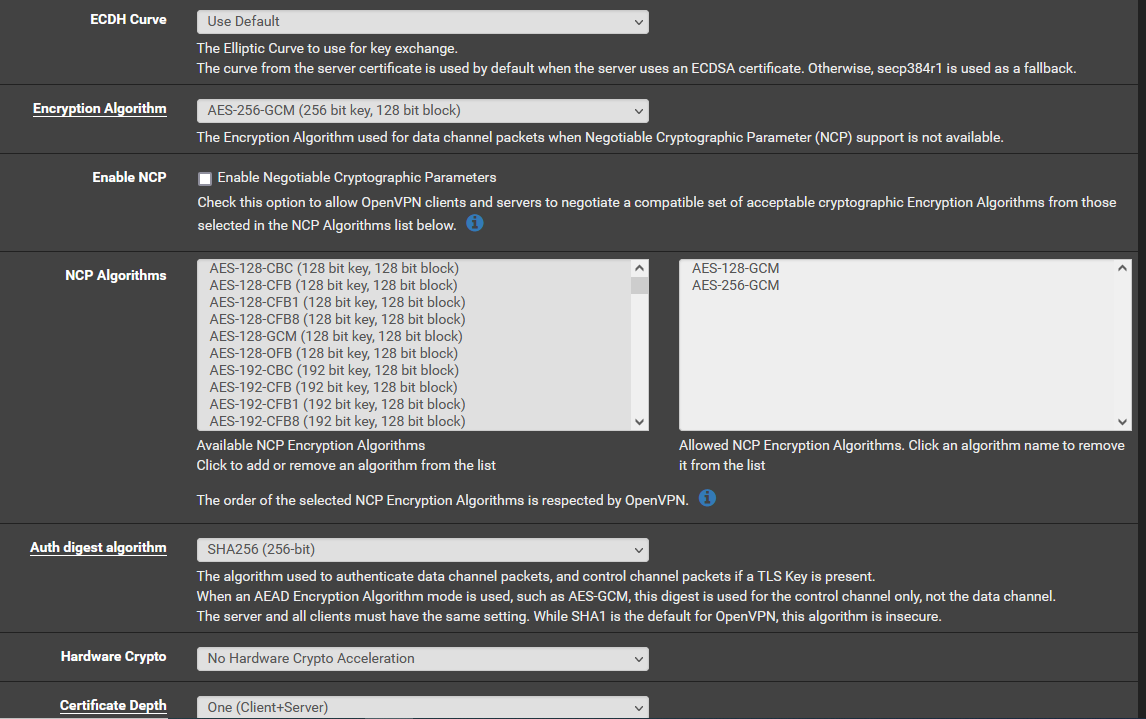
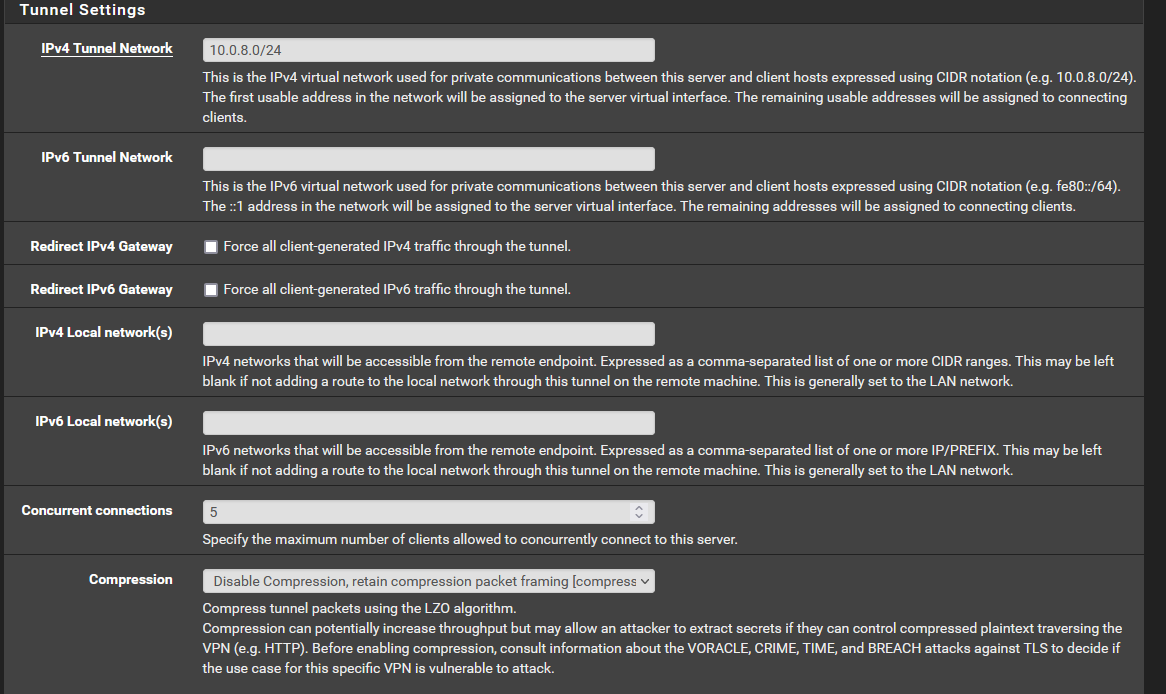
I'm hoping someone can help me with a firewall configuration issue. I use OpenVPN on my pfSense box. Using UDP 1194, no problem, everything connects. However, I also want to use TCP 443 as many WiFi hotspots only allow ports 80 and 443. To connect to my OpenVPN server, I would need to connect via TCP 443. I followed the direction on Netgate https://docs.netgate.com/pfsense/en/latest/vpn/openvpn/port-share.html
I added the custom line to my server. However, I'm not clear what goes in the firewall rules i.e. "add a firewall rule to pass traffic to the WAN IP address or VIP used for OpenVPN on port 443" My box runs on 192.168.1.1. Can anyone suggest a configuration for my firewall? Thanks.
-
@frankzappa said in Sharing a Port with OpenVPN and a Web Server:
However, I'm not clear what goes in the firewall rules i.e. "add a firewall rule to pass traffic to the WAN IP address or VIP used for OpenVPN on port 443"
You have to pass 443 to that IP the OpenVPN is listening on.
If it's listening on WAN address allow access to WAN address, if it's listening on localhost using a NAT rule allow 443 access to 127.0.0.1.Ensure that you have no other port forwarding rule for 443 in place.
@frankzappa said in Sharing a Port with OpenVPN and a Web Server:
My box runs on 192.168.1.1.
Since your pfSense is behind a router, you have to forward 443 on the router to pfSense.
-
@viragomann
Thanks viragomann. This is where I get confused. My pfSense box runs on 192.168.1.1 as does my OpenVPN server (as part of pfSense package). I want to be able to access my LAN from the WAN using TCP 443. Not sure what the configuration should look like on the firewall. Thanks -
so you want openvpn to listen on both 1194 udp and 443 tcp - is that right. If so just fire up another instance of openvpn.
The reason you would want to share ports, if is your already using 443 say as a forward to some https server behind pfsense.
if you want vpn on 443, and say web server behind pfsense - then yes you can use openvpn share point.. I found it better response to do this with haproxy for your 443 service behind pfsense.
-
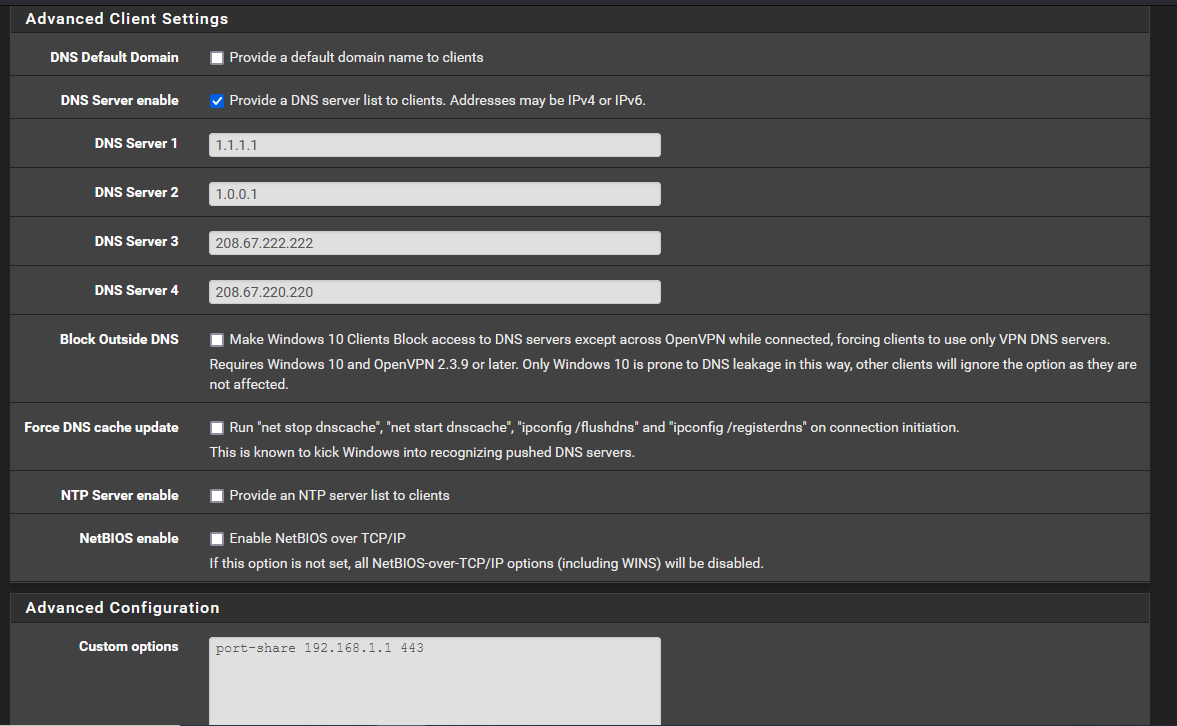
Thanks johnpoz. I'm not running a server behind pfsense. I do want openvpn to listen on both 1194 udp and 443 tcp. I don't know if I'm already using port 443 although I thought if I accessed the pfSense GUI via https, it uses tcp 443, correct?
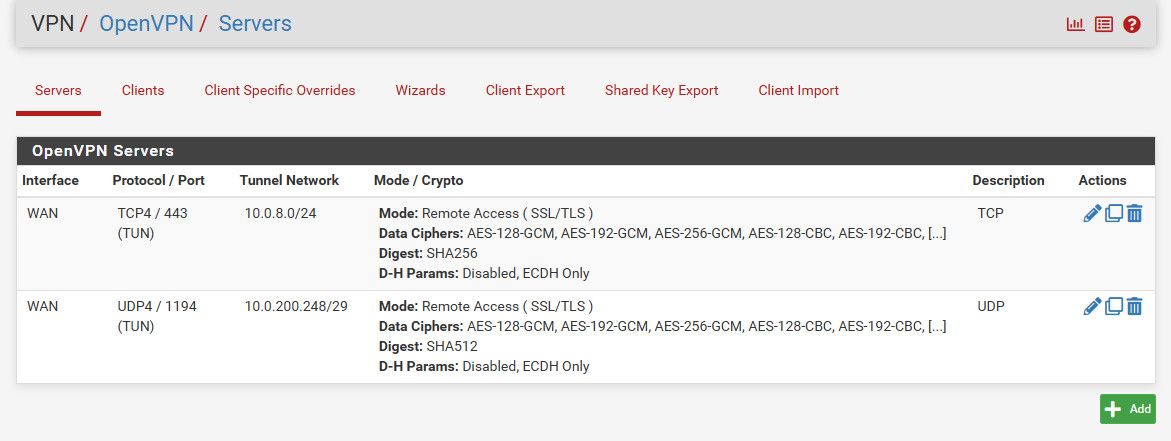
That said, I'm still having trouble accessing my LAN using UDP 1194 or TCP 443. I currently have two instances of OpenVPN running (1194 and 443).
I can't figure out (from the WAN) how to access my LAN. What firewall settings do I need (as well as NAT)?
-
What port openvpn listens on has nothing to do with accessing your lan devices. Your going to have to show what you did for your setup. Did you put in your lan as the local network?
Keep in mind a common issue users run into is the device they are accessing own firewall, not allowing the tunnel network you are using..
As to pfsense using 443? Did you use that for https.. Out of the box pfsense only listens on 80.. You would have to enable https, and it allows you to pick the port. I use 8443 for example.
My box runs on 192.168.1.1
That is the default lan IP of pfsense, your wan is public IP? Your actually making a connection? Can you ping 192.168.1.1, but not say 192.168.1.X a device on your lan?
-
-
@johnpoz said in Sharing a Port with OpenVPN and a Web Server:
Your actually making a connection? Can you ping 192.168.1.1, but not say 192.168.1.X a device on your lan?
Correct. I can ping 192.168.1.1 bit nothing else on my LAN e.g. 192.168.1.20
-
@frankzappa
Actually, disregard the previous post. From my LAN, connected to OpenVPN 443, I can now ping everything on LAN (from within LAN). -
@frankzappa
I still can't access the internet, or my local LAN from the WAN using TCP 443. Not sure what I'm doing wrong. -
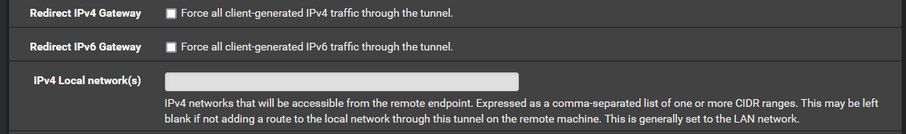
@frankzappa You have not local network setup, nor are you redirecting all traffic through the vpn.. So no you wouldn't access anything through that tunnel..
You need to set the local network(s) up, or you need to route everything through the tunnel.
How would the remote client know to go down the tunnel to get anywhere?
And why do you have port share setup?? You do not want or need that..
-
@johnpoz
Thanks. Not sure what you mean (or how to) "set the local network(s) up, or you need to route everything through the tunnel" How do I do that? -
@frankzappa
Ok, I think I figured out setting up the local network. I added 192.168.1.0/24 in the window. However, my iPhone (wifi off/connected only to phone data) won't even connect to my OpenVPN server on TCP 443. However, UDP 1194 works fine. Something I'm missing? -
@johnpoz
Thanks again johnpoz. I'm almost there. I can connect from WAN to OpenVPN on TCP 443 and UDP 1194. Two remaining issues:- I can't connect to my local NAS. I can ping it, but can't connect via OpenVPN. Same for everything else on LAN.
- When I run a security scan (Shields Up) It gives me the giant red "FAILED" as it shows port 443 wide open (saying it's unsafe to have this open).
Is there any way to prevent port scanners from showing TCP 443 wide open? It doesn't show UDP 1194 as open (and yet it is).
Thanks
-
The scanner doesn't scan udp that is why its not showing 1194.
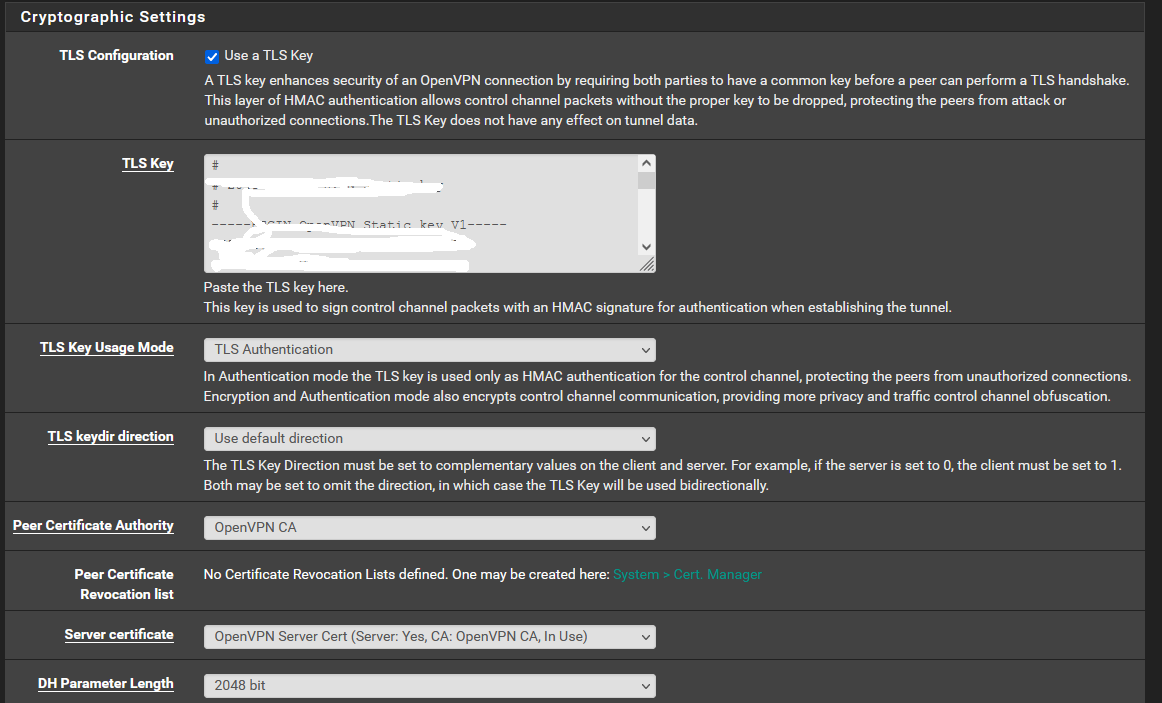
No there is no way to have the port closed, but yet people connect ;) Your vpn is pretty freaking secure.. And openvpn will just drop packets that are not vpn packets from your clients.. look into what tls key does.. "correct HMAC signature"
To you nas.. Look to the nas firewall - I highly doubt it allows something other your lan network, ie your tunnel network (vpn client IP) to access its shares, etc.. it might allow ping.
If you can ping it.. Then you have connectivity and issue is pretty much 99.9999 sure is local firewall of the device.. Unless on your openvpn interface rules you limited that to icmp? It defaults to any any..
-
@johnpoz
Thanks Again. I'll play around with NAS firewall to see if that's the issue.