Right config with HMA openVpn config
-
Hello, I want to configure pfSense as client of my HMA ( hide my ass ) VPN.
I found an old documentation, and it is not working
Anyone has managed to find the right parameters ?
for ref :
https://support.hidemyass.com/hc/en-us/articles/202720876-pfSense-configuration-for-routing-all-traffic-via-VPNthanks !
-
@smalldragoon
There might not be significant differences to the actual version.
From what I can see, only the login file part is not needed anymore. Instead you can set the login settings in the GUI.
However, you might have got over options from HMA to be set as shown in that old tutorial.What do you get? Any logs?
-
@viragomann
Hi Again ;-) , found 2 things :1 - port have changes ( now use 8080 for TCP and 553 for UDP )
2 - TCP config is not working as UDP works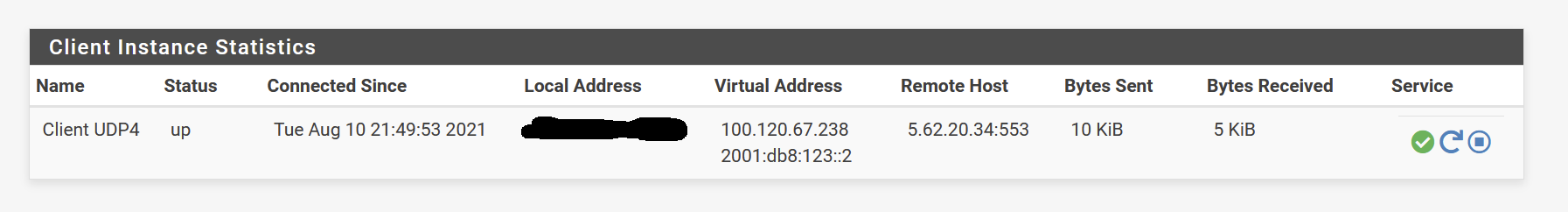
I trying now to redirect all traffic from only 1 IP from my LAN, following this French tutorial, but for now, I have weird behavior ( ping works but as soon as I do something else, I have nothing, and ping stops working )
ref : [https://vdupain.github.io/network/2013/09/24/configurer-un-client-openvpn-vers-hidemyass-hma-sous-pfsense/](link url)
But this is another topic, will create a new thread if I still get stucked. I'm cleaning all my tests now ;-) ... to restart on clean basis
Here are the VPN logs
Aug 10 21:56:09 openvpn 49089 Authenticate/Decrypt packet error: packet HMAC authentication failed Aug 10 21:56:02 openvpn 49089 Initialization Sequence Completed Aug 10 21:56:02 openvpn 49089 /usr/local/sbin/ovpn-linkup ovpnc2 1500 1625 100.120.23.60 255.255.254.0 init Aug 10 21:56:02 openvpn 49089 /sbin/ifconfig ovpnc2 inet6 -ifdisabled Aug 10 21:56:01 openvpn 49089 /sbin/ifconfig ovpnc2 inet6 2001:db8:123::2/64 mtu 1500 up Aug 10 21:56:01 openvpn 49089 /sbin/route add -net 100.120.22.0 100.120.22.1 255.255.254.0 Aug 10 21:56:01 openvpn 49089 /sbin/ifconfig ovpnc2 100.120.23.60 100.120.22.1 mtu 1500 netmask 255.255.254.0 up Aug 10 21:56:01 openvpn 49089 TUN/TAP device /dev/tun2 opened Aug 10 21:56:01 openvpn 49089 TUN/TAP device ovpnc2 exists previously, keep at program end Aug 10 21:56:00 openvpn 49089 /usr/local/sbin/ovpn-linkdown ovpnc2 1500 1625 100.120.48.147 255.255.254.0 init Aug 10 21:56:00 openvpn 49089 Closing TUN/TAP interface Aug 10 21:56:00 openvpn 49089 NOTE: Pulled options changed on restart, will need to close and reopen TUN/TAP device. Aug 10 21:56:00 openvpn 49089 Preserving previous TUN/TAP instance: ovpnc2 Aug 10 21:56:00 openvpn 49089 Incoming Data Channel: Using 256 bit message hash 'SHA256' for HMAC authentication Aug 10 21:56:00 openvpn 49089 Incoming Data Channel: Cipher 'AES-256-CBC' initialized with 256 bit key Aug 10 21:56:00 openvpn 49089 Outgoing Data Channel: Using 256 bit message hash 'SHA256' for HMAC authentication Aug 10 21:56:00 openvpn 49089 Outgoing Data Channel: Cipher 'AES-256-CBC' initialized with 256 bit key Aug 10 21:56:00 openvpn 49089 Using peer cipher 'AES-256-CBC' Aug 10 21:56:00 openvpn 49089 OPTIONS IMPORT: adjusting link_mtu to 1625 Aug 10 21:56:00 openvpn 49089 OPTIONS IMPORT: peer-id set Aug 10 21:56:00 openvpn 49089 OPTIONS IMPORT: route-related options modified Aug 10 21:56:00 openvpn 49089 OPTIONS IMPORT: --ifconfig/up options modified Aug 10 21:56:00 openvpn 49089 Socket Buffers: R=[196608->196608] S=[196608->196608] Aug 10 21:56:00 openvpn 49089 OPTIONS IMPORT: --sndbuf/--rcvbuf options modified Aug 10 21:56:00 openvpn 49089 OPTIONS IMPORT: compression parms modified Aug 10 21:56:00 openvpn 49089 OPTIONS IMPORT: explicit notify parm(s) modified Aug 10 21:56:00 openvpn 49089 OPTIONS IMPORT: timers and/or timeouts modified Aug 10 21:56:00 openvpn 49089 Options error: option 'route-ipv6' cannot be used in this context ([PUSH-OPTIONS]) Aug 10 21:56:00 openvpn 49089 Options error: option 'redirect-gateway' cannot be used in this context ([PUSH-OPTIONS]) Aug 10 21:56:00 openvpn 49089 Options error: option 'redirect-gateway' cannot be used in this context ([PUSH-OPTIONS]) Aug 10 21:56:00 openvpn 49089 Options error: option 'dhcp-option' cannot be used in this context ([PUSH-OPTIONS]) Aug 10 21:56:00 openvpn 49089 PUSH: Received control message: 'PUSH_REPLY,dhcp-option DNS 100.120.22.1,redirect-gateway def1,ping 9,ping-restart 30,explicit-exit-notify 1,sndbuf 196608,rcvbuf 196608,route-gateway 100.120.22.1,topology subnet,redirect-gateway def1,ifconfig-ipv6 2001:db8:123::2/64 2001:db8:123::1,route-ipv6 2000::/3 2001:db8:123::1,explicit-exit-notify 2,compress,ifconfig 100.120.23.60 255.255.254.0,peer-id 15' Aug 10 21:56:00 openvpn 49089 SENT CONTROL [server]: 'PUSH_REQUEST' (status=1) Aug 10 21:55:59 openvpn 49089 [server] Peer Connection Initiated with [AF_INET]5.62.20.34:553 Aug 10 21:55:59 openvpn 49089 Control Channel: TLSv1.2, cipher TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384, 2048 bit RSA Aug 10 21:55:59 openvpn 49089 WARNING: 'auth' is used inconsistently, local='auth SHA256', remote='auth SHA1' Aug 10 21:55:59 openvpn 49089 WARNING: 'link-mtu' is used inconsistently, local='link-mtu 1570', remote='link-mtu 1558' Aug 10 21:55:59 openvpn 49089 VERIFY OK: depth=0, C=UK, ST=London, L=London, O=Privax Ltd, OU=HMA Pro VPN, CN=server, emailAddress=info@privax.com Aug 10 21:55:59 openvpn 49089 VERIFY OK: nsCertType=SERVER Aug 10 21:55:59 openvpn 49089 VERIFY OK: depth=1, C=UK, ST=London, L=London, O=Privax Ltd, OU=HMA Pro VPN, CN=hidemyass.com, emailAddress=info@privax.com Aug 10 21:55:59 openvpn 49089 VERIFY WARNING: depth=1, unable to get certificate CRL: C=UK, ST=London, L=London, O=Privax Ltd, OU=HMA Pro VPN, CN=hidemyass.com, emailAddress=info@privax.com Aug 10 21:55:59 openvpn 49089 VERIFY WARNING: depth=0, unable to get certificate CRL: C=UK, ST=London, L=London, O=Privax Ltd, OU=HMA Pro VPN, CN=server, emailAddress=info@privax.com Aug 10 21:55:59 openvpn 49089 TLS: Initial packet from [AF_INET]5.62.20.34:553, sid=8110a782 31a7c483 Aug 10 21:55:59 openvpn 49089 UDPv4 link remote: [AF_INET]5.62.20.34:553 Aug 10 21:55:59 openvpn 49089 UDPv4 link local (bound): [AF_INET]:0 Aug 10 21:55:59 openvpn 49089 Socket Buffers: R=[42080->196608] S=[57344->196608] Aug 10 21:55:59 openvpn 49089 TCP/UDP: Preserving recently used remote address: [AF_INET]5.62.20.34:553 Aug 10 21:55:59 openvpn 49089 NOTE: the current --script-security setting may allow this configuration to call user-defined scripts Aug 10 21:55:59 openvpn 49089 WARNING: --ns-cert-type is DEPRECATED. Use --remote-cert-tls instead. Aug 10 21:55:49 openvpn 49089 Restart pause, 10 second(s) -
@smalldragoon
So the client is already up as shown in the screen.
Also the log lookw well, but there won't no traffic pass the tunnel, since you might have set route-nopull.BTW: the log shows your public IP. Should hide it.
-
@viragomann
Well, in the tutorial, it says to put this option as HMA use the replace gateway .
I have create a rule, in Lan which saysSRC : 1 IP address
port all
Dest ALL
and in advanced, I changed the GW , to the GW created by VPN.
If I reboot the PFsense, it works for ping, then .. if I do anything else, everythins stops working ( including ping ) -
@smalldragoon
Yeah, route-nopull is the correct setting to avoid get pushed the default route and do policy routing instead.Consider that the policy routing rule does not allow any internal traffic from the source IP, cause it directs any packet to the VPN gateway. This also applies for DNS.
Hence you have either use a public DNS on the concerned device or maybe redirect DNS on pfSense to a public server and direct this one over the VPN (both helps to avoide DNS leaking), or you add an additional firewall rule above of the policy to allow internal access (without the gateway stated).
-
@viragomann
Well, maybe I'm missing something
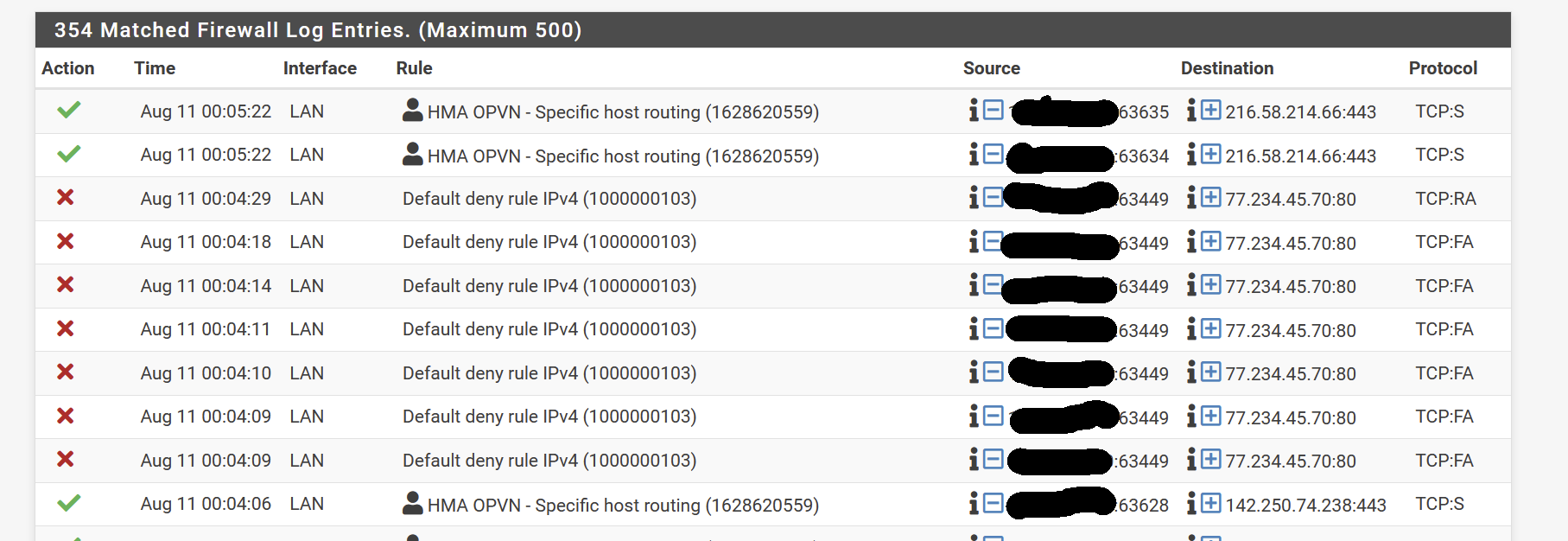
I did this anyway, with the hidden IP being my LAN computer IP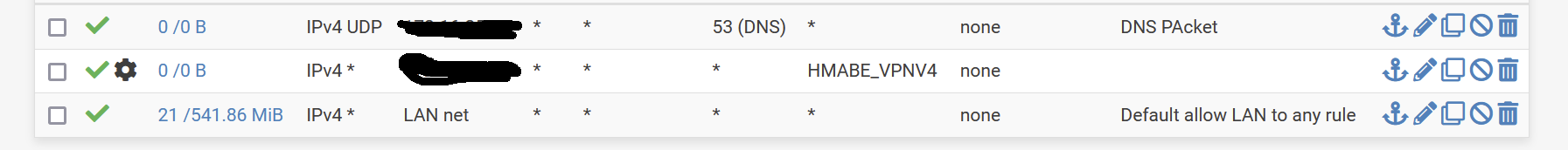
Resolution works ( as per the rules created using normal GW ) , but nothing else ....
-
@smalldragoon
Interestingly both rules don't show any traffic.
Could it be that there is another rule matching the traffic from the client before? Maybe a floating rule or one on an interface group which LAN is belonging to.To analyze I'd enable logging in the rule and add a proper description. So you can see in the firewall log, if the rules are applied.
-
@viragomann
Well, no groups of rules, my setup is pretty basic :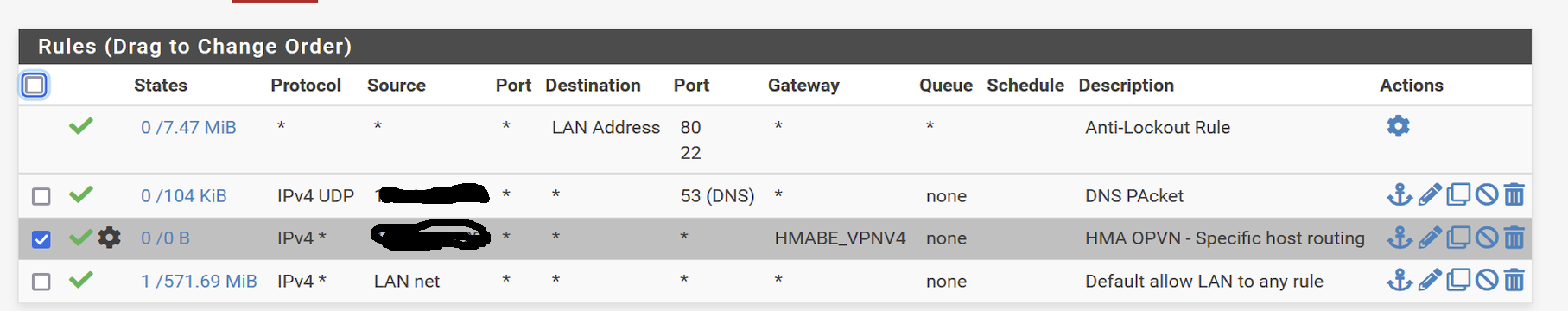
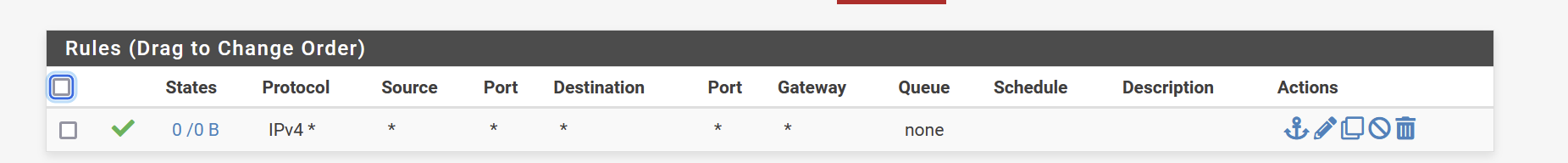
I have this setup for the HMA interface ?
-
@viragomann seems that the rules a default rule is triggered ? I don't have one ...
-
@smalldragoon said in Right config with HMA openVpn config:
I have this setup for the HMA interface ?
This rule only allows incoming traffic on the VPN. You do not need any rule here for outgoing connections.
The same is true for the OpenVPN tab.No idea why you traffic doesn't flow. Could be due to wrong settings in the OpenVPN client.
The tutorials you quoted are very old. The shown Advanced settings are deprecated and shouldn't be use anymore. Most of them can be set in the GUI nowadays or are default values.
You shouldn't use the showed settings. Simply follow the specifications of the provider and set it in the GUI. Only set / change options which are mentioned in the guidelines. -
@smalldragoon
One thought came up: Did you add an outbound NAT rule for the VPN? -
@viragomann
Well no, was not mentionned in the Tutorial and I assume it is the HMA server wich is doing the NAT at the end ?
they say here to change to manual outbound NAT, AON but that's all :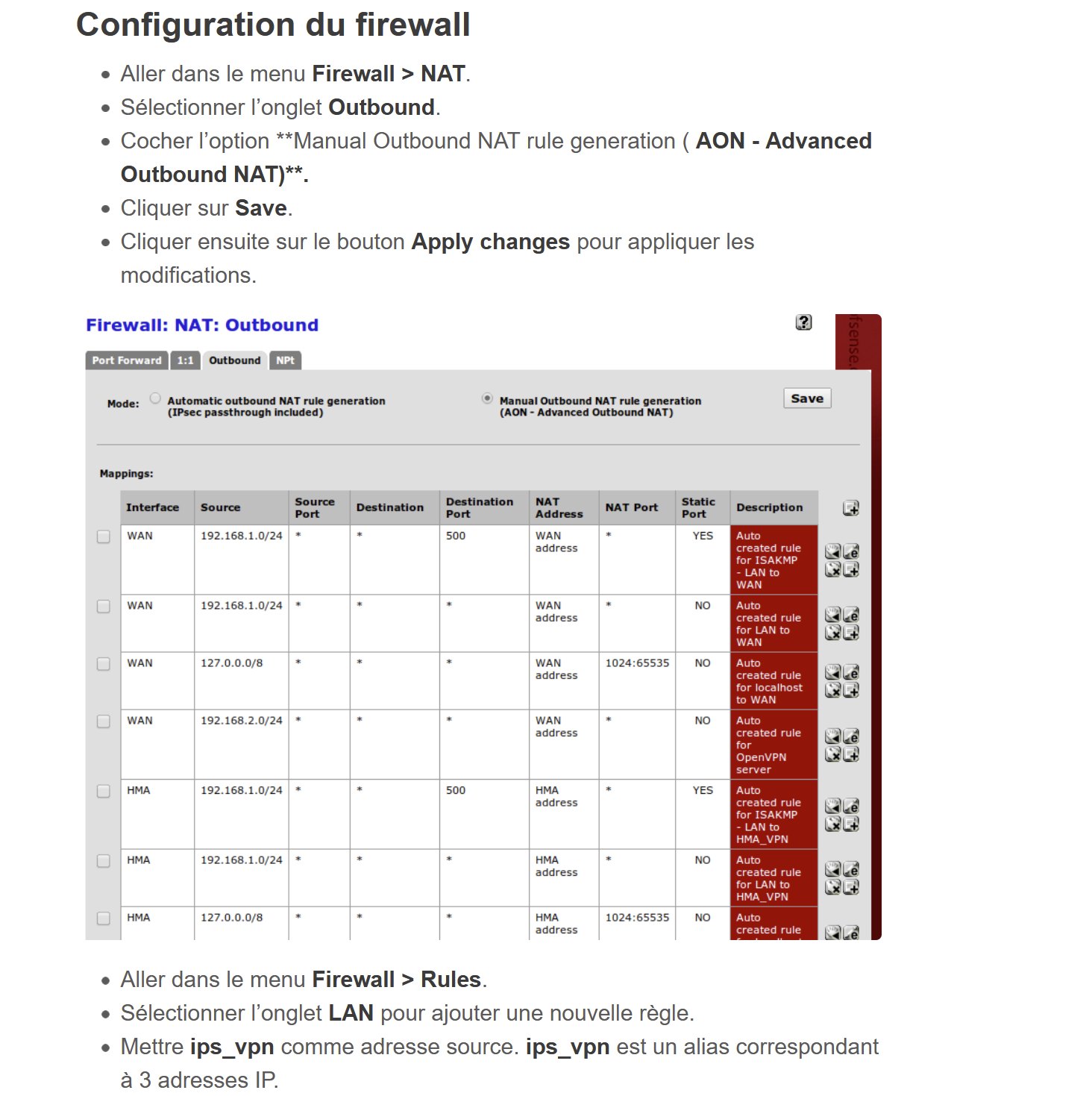
-
@smalldragoon said in Right config with HMA openVpn config:
was not mentionned in the Tutorial and I assume it is the HMA server wich is doing the NAT at the end ?
Might not be the best tutorials.
However, the screen shows two HMA rules.Anyway, it will not work without that.
But switch the Outbound NAT into the hybrid mode and save it.
Then add a rule:
interface: <your VPN interface>
Source: LAN, or only the IPs (alias) you need
dest.: any
translation: interface address -
@viragomann
switch to hybrid , done
Created as 1st rule :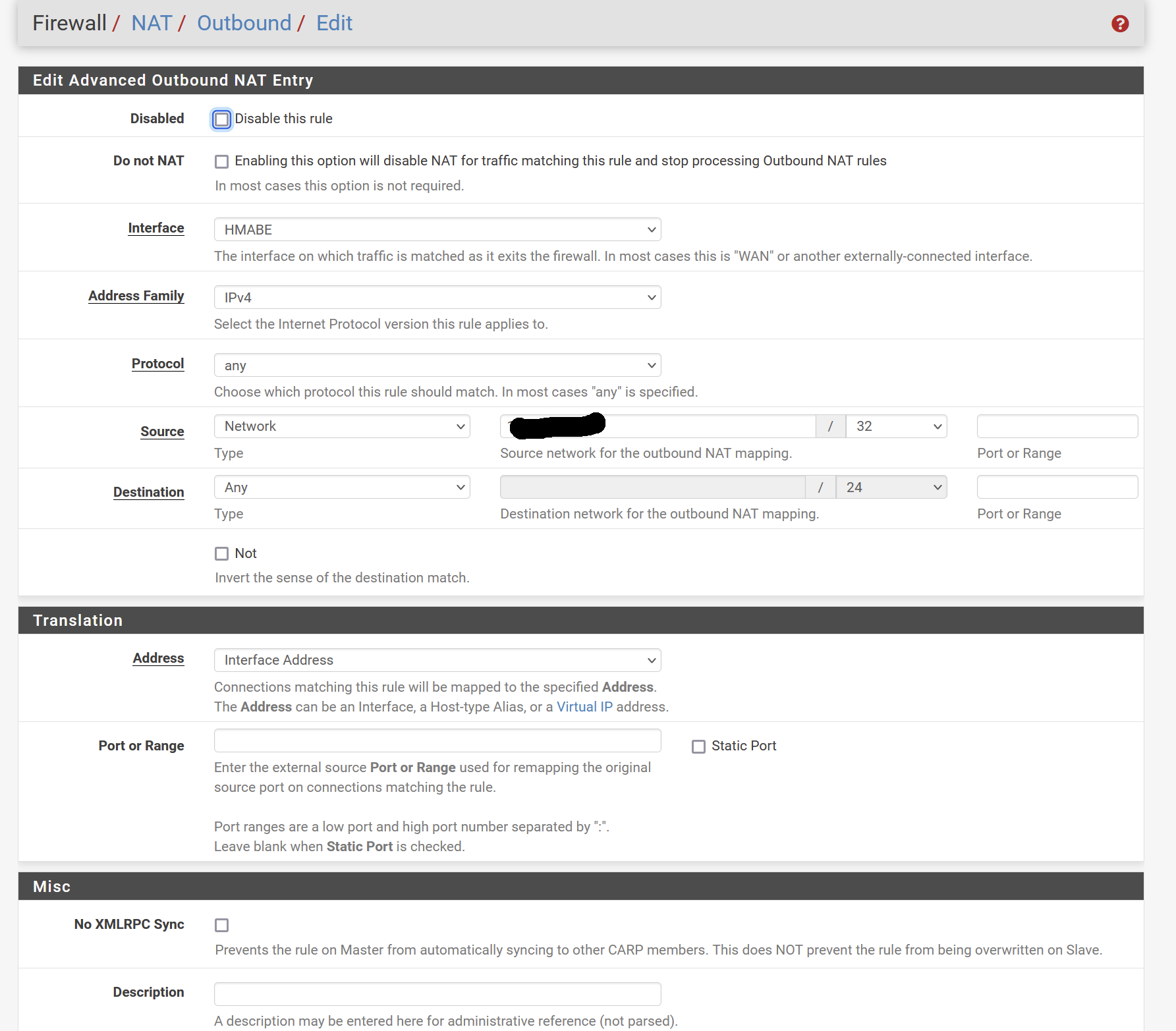
Where the hidden value is my LAN computer for tests
Still nothing :( -
@smalldragoon
Try a simple ping to a public IP like 8.8.8.8 on the client, while taking a packet capture on the VPN interface to see, what's going on. -
@viragomann
Hi, I rechecked evrything and followed one of your advice, to check VPN .. found that ( 2 first line , other to give conext ):Aug 13 14:51:30 openvpn 72184 Authenticate/Decrypt packet error: packet HMAC authentication failed Aug 13 14:51:21 openvpn 72184 Authenticate/Decrypt packet error: packet HMAC authentication failed Aug 13 14:51:18 openvpn 72184 MANAGEMENT: Client disconnected Aug 13 14:51:18 openvpn 72184 MANAGEMENT: CMD 'status 2' Aug 13 14:51:18 openvpn 72184 MANAGEMENT: CMD 'state 1' Aug 13 14:51:18 openvpn 72184 MANAGEMENT: Client connected from /var/etc/openvpn/client2/sock Aug 13 14:51:13 openvpn 72184 Initialization Sequence Completed Aug 13 14:51:13 openvpn 72184 WARNING: this configuration may cache passwords in memory -- use the auth-nocache option to prevent this Aug 13 14:51:13 openvpn 72184 /usr/local/sbin/ovpn-linkup ovpnc2 1500 1624 100.120.41.81 255.255.255.0 init Aug 13 14:51:13 openvpn 72184 /sbin/ifconfig ovpnc2 inet6 -ifdisabled Aug 13 14:51:12 openvpn 72184 /sbin/ifconfig ovpnc2 inet6 2001:db8:123::2/64 mtu 1500 up Aug 13 14:51:12 openvpn 72184 /sbin/route add -net 100.120.41.0 100.120.41.1 255.255.255.0 Aug 13 14:51:12 openvpn 72184 /sbin/ifconfig ovpnc2 100.120.41.81 100.120.41.1 mtu 1500 netmask 255.255.255.0 up Aug 13 14:51:12 openvpn 72184 TUN/TAP device /dev/tun2 opened Aug 13 14:51:12 openvpn 72184 TUN/TAP device ovpnc2 exists previously, keep at program end Aug 13 14:51:12 openvpn 72184 Incoming Data Channel: Using 256 bit message hash 'SHA256' for HMAC authentication Aug 13 14:51:12 openvpn 72184 Incoming Data Channel: Cipher 'AES-256-CBC' initialized with 256 bit key Aug 13 14:51:12 openvpn 72184 Outgoing Data Channel: Using 256 bit message hash 'SHA256' for HMAC authentication Aug 13 14:51:12 openvpn 72184 Outgoing Data Channel: Cipher 'AES-256-CBC' initialized with 256 bit key Aug 13 14:51:12 openvpn 72184 Using peer cipher 'AES-256-CBC' Aug 13 14:51:12 openvpn 72184 OPTIONS IMPORT: adjusting link_mtu to 1624 Aug 13 14:51:12 openvpn 72184 OPTIONS IMPORT: peer-id set Aug 13 14:51:12 openvpn 72184 OPTIONS IMPORT: route-related options modifiedsearched on google, seams related to TLS auth, which is not and must not be activated ... any insight ?
Thx -
@smalldragoon
Possibly something wrong in the client configuration.I already already advised to take the providers requirements for reference and set up all in the GUI instead obeying these age-old tutorials.
Since I whether know these nor your current configuration, I cannot contribute. -
@viragomann
Sorry, I though I would have said.
Provider is not advising really anything.
Ihave the .opvn files , that's all .
That's why I tried other sources -
@smalldragoon said in Right config with HMA openVpn config:
Ihave the .opvn files , that's all .
That may be all you need to configure the OpenVPN client accordingly.
If it uses TLS and there are certs inside, you have to extract them and import it in pfSense.