PfSense NetGate image in AWS using a public IP for an internal machine
-
Hi all,
Been using pfSense for a while and never had to register or post a question, speaks to how easy it is to use. 8)
The general idea of the connection is that there are 2 separate companies and the VPN only allows access to a single machine on either side, thereby preserving the security of each others network.
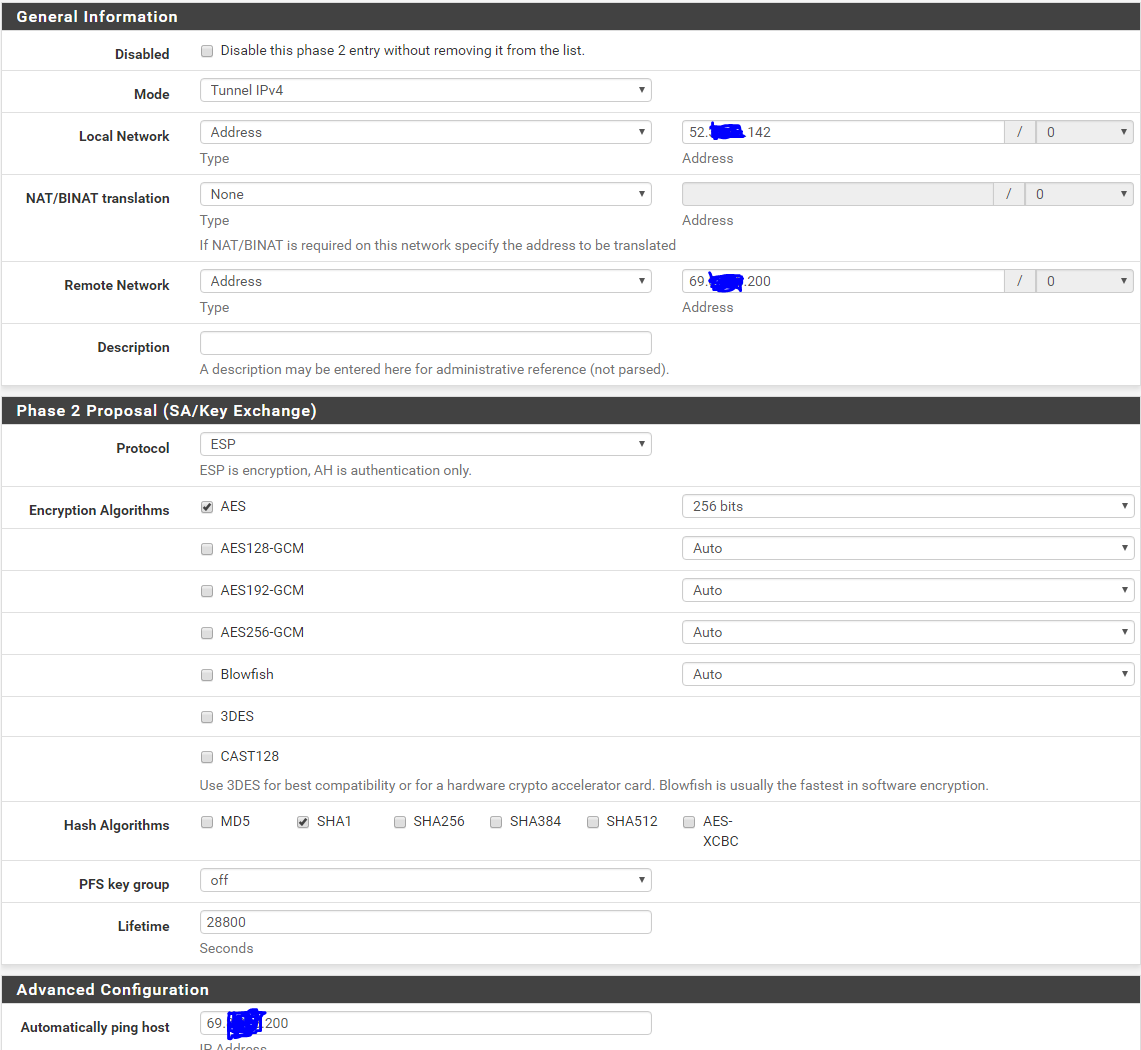
The other company has a requirement that I think is causing me an issue.Internet IP Address for the client hosts address (generally the client SQL server)
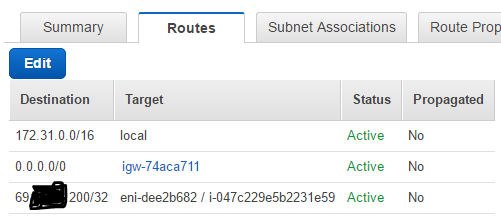
All VPN IP addresses must be Publicly Registered, Internet Routable and not in the Private Network Ranges of (10.0.0.0 to 10.255.255.255 , 172.16.0.0 to 172.31.255.255, 192.168.0.0 to 192.168.255.255)My VPC subnet that pfSense is on is 172.31.0.0/24. So, I figured this could be handled with an AWS routing table but I have played with that. No worky.
I have never seen the traffic counters on the IPSec move off from zero.I will dump what I can of the config information here so everyone can look and comment.
I need that one nugget that points me in the proper direction. (Been looking at this for too long)Thanks!!!
I am using the lastest netgate AMI and it is running fine, which was easy to do the initial setup on and get the IPSec VPN connected.
The Remote VPN public is 69.x.x.196
The Remote Host public is 69.x.x.200
The local VPN public is 52.x.x.77
The local VPN internal is 172.31.0.70 (wan)
The local pfSense has another internal is 172.31.0.10 (lan)
The local Host public is 52.x.x.142
The local host internal is 172.31.0.200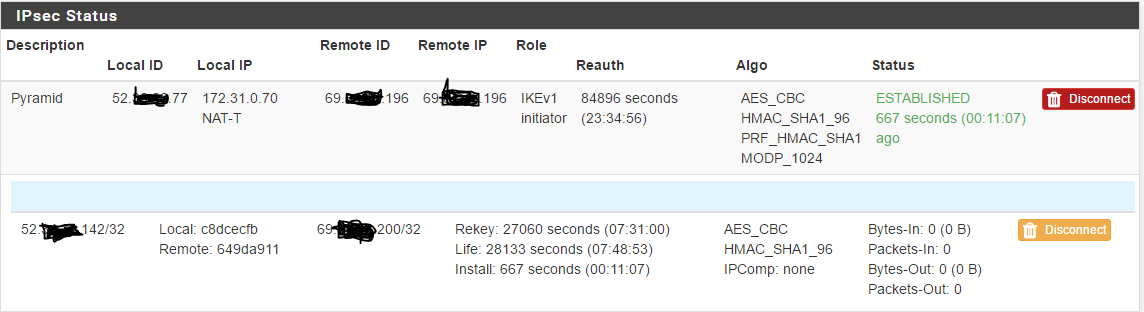
This is kinda where I am leaning to there being an issue. I have played with these alot.
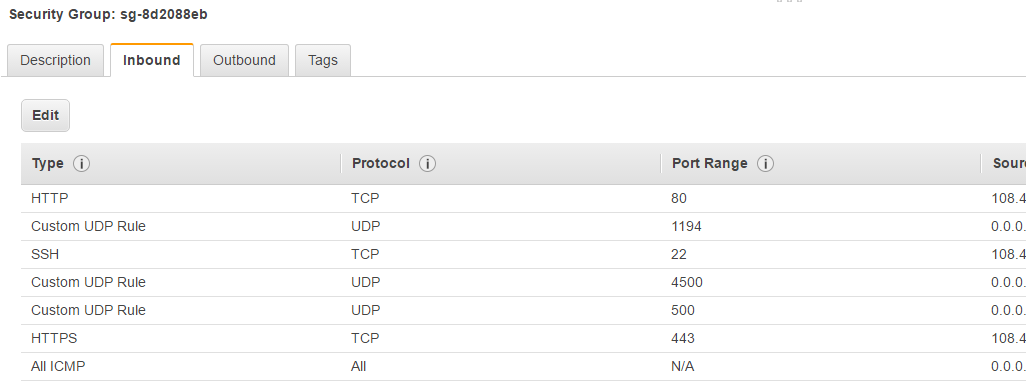
eni-dee2b682 is the wan side of pfsense, I had tried it with the lan side as well to no avail.
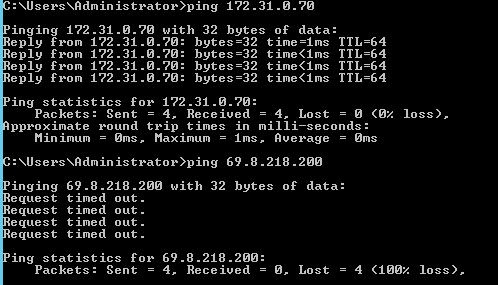
These are ping tests from 172.31.0.200 to a couple of the important IP's