[SOLVED] OpenVPN site to site SSL with NAT
-
Hey all-
This forum has been awesome and through searching I've solved almost all of my issues thus far. However, this one has me totally stumped.
I'm deploying remote site pfsense virtually for customers as a call-home device building a site to site between that virtual network and my datacenter monitoring network. I am running into the issue where the occaisional customer has built out an internal network that matches one of my internal networks and I need to be able to hide my network behind a NAT so that the customer's monitoring devices can successfully route back to my network instead of dumping out into theirs.
Here is a diagram of what I'm doing:
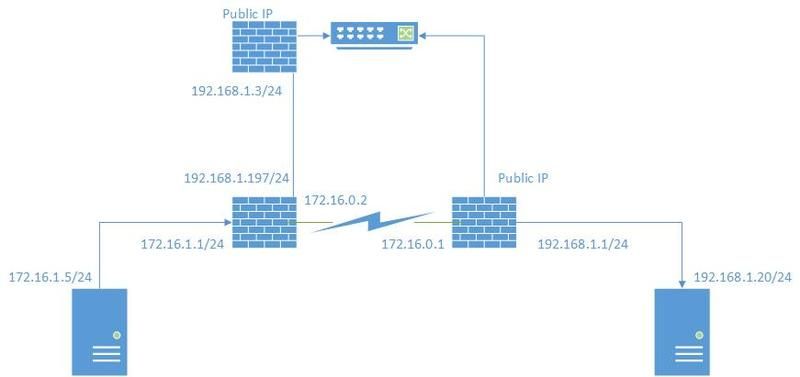
The VPN is up and operational in that I can ping 172.16.0.1 from 172.16.1.5. However, I can't get to any of the 192.168.1.0/24 addresses on the right hand side because the pfsense on the left assumes that traffic (rightly so) belongs locally off the WAN port.
What I would like to do is insert a NAT on the right hand side that presents 172.16.2.0/24 as a routable network and any time one of those IPs is connected to from the left side the right hand side passes them off to the corresponding 192.168.1.0/24 IP address.
I've done this before on Cisco over a site to site and that was ages ago. I've found a lot of references searching that "oh yeah, you can do it with OpenVPN but not with IPSec" and haven't been able to find exactly how to do it.
Thanks in advance!
EDIT:
To clarify, I need 172.16.1.5 on the customer side (left) to talk to 192.168.1.20 (and others) on my network side (right). To do that, I'd like to put a NAT in place in between them so 172.16.1.5 thinks it is talking to 172.16.2.20 when it is actually talking to 192.168.1.20.While I'll likely only need a handful of addresses mapped this way, I'd prefer to just set it up dynamically so I don't have to worry about mapping new servers as they come up.
-
Seems Photobucket is having issues. Attached my network diagram here.
I've also tested a 1:1 with the attached settings:
Interface: VPN
External Subnet (one I'm spoofing)
Internal IP: 192.168.1.0/24 (in the picture it is 172.16.1.33, but that is my test environment).
Destination IP: *** EDIT ***I left this blank in this case, but I've since changed it to be just the source subnet I want to NAT.What happens in this case is the client can ping the spoof address of 172.16.2.1, but the response claims to be 172.16.2.33.
HOWEVER, if I ping a different IP that isn't the default gateway, it returns with the right response.
In short:
I've solved my problem with a really simple 1:1 NAT (guess I should've tried it before asking).
Hopefully anyone needing this can find it.



