Bypassing DNSBL for specific IPs
-
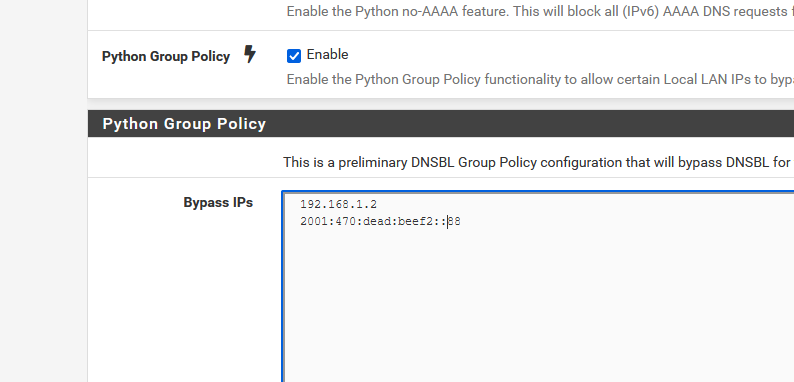
Just checking "Python Group Policy" does nothing.
It's stated that "Enable the Python Group Policy functionality to allow certain Local LAN IPs to bypass DNSBL"So certain local IPs have to be entered.
Like :
edit :
I didn't have any DNSBIl activated, so I activated one.
This one :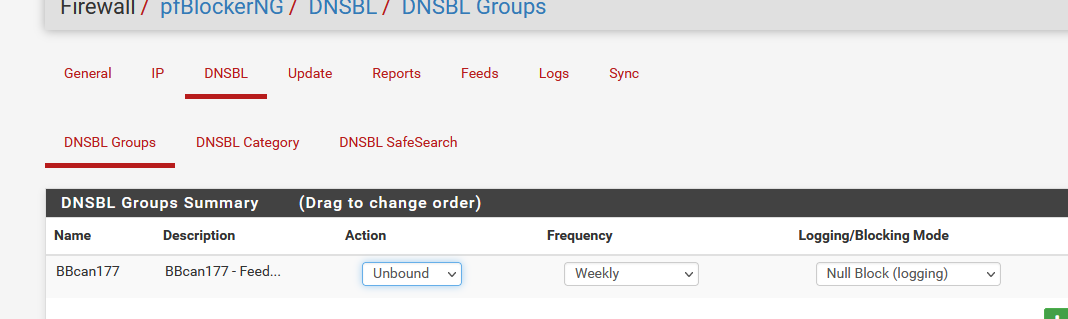
Take a look at the feed text, and you find the last entry :
avsvmcloud.comOn my PC with the IP 192.168.1.2 (on the policy list - see my image above) I could obtain an IP :
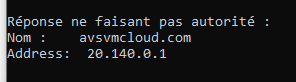
Or, on another PC using IP 192.168.1.9, I obtained "0.0.0.0" == DNSBL blocked ( I'm not using the build in pfBlockerNG web server, if I was, I would have received 10.10.10.1 ).
My conclusion : Group policy works.
I did not test IPv6 here. For IPv4 it worked.
-
@gertjan I added my local IP4 addresses under the group policy as host IP's with no subnet mask range e.g. /32 /24 etc.. I restarted pfsense, unbound, ran , update force, reload and still no dice. I love the way it works but I need to whitelist IP's to get around pfblocker/dnsbl/geoip restrictions I've set already. thanks!
-
@gertjan
As I can see there are no rules under "Deny". I have read there, that this issue could be from the installed version (2.1.4_26). Is this 2x version still in development? Is there a release date for the 3.x devel version? (Devel becomes non devel) -
@smokinmojoe I was literally saying this out loud to myself. This package has been available for quite some time and the fact that this request which is very reasonable and very obvious that is needed is not implemented really hurts my soul.
Yes, DNS sinkholing is great. You would think along the way someone would've thought to themselves "Gee, what if there's a user that shouldn't be restricted". Pretty much the follow-up to that thought was "ehh that would never happen. what an unlikely thing to think".
-
Not implemented ?
I just spend looking some time why my DNSBL didn't seem to work. Then I found out out wasn't working for the PC is was using, but it was working, for the PC right next to me.
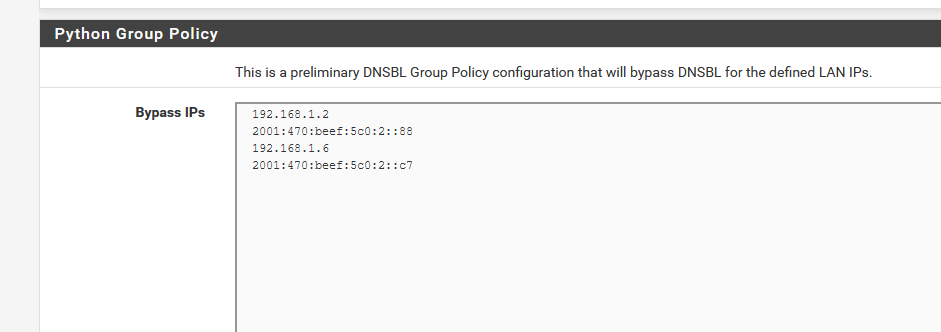
I recalled : I've added the IPv4 and IPv6 of the PC I'm using on the "Python Group Policy" list.Btw : Python Group Policy was added to the "pfBlockerNG-devel 3.1.0_1"", not the ancient 'pfBlockerNG 2.1.4_26'.
-
Unless there's something wrong in my config, I think I found a bug with bypassing DNSBL with the python feature...
For example, that if I add a client to the exclusion list (Python group policy) to bypass DNSBL, almost immediately after, DNSBL starts behaving very weirdly by allowing traffic from the unblocked client as it should, but randomly also from other clients. Sometimes it returns the 1x1 gif thingy, sometimes the webpage with "This website BLABLABLA has been blocked by the Network Administrator!"
(Edited this post after more troubleshooting)
-
Your are using the correct IP addresses ? Like :
When you change DNSBL settings :
Do a force realod all for pfBlocker.
Reset for every LAN device the local DNS cache.
Windows will need aipconfig /flushdns@pftdm007 said in Bypassing DNSBL for specific IPs:
Sometimes it returns the 1x1 gif thingy, sometimes the webpage with "This website BLABLABLA has been blocked by the Network Administrator!"
That what's left over from the DNSBL web server that wants to tell you a page has been blocked.
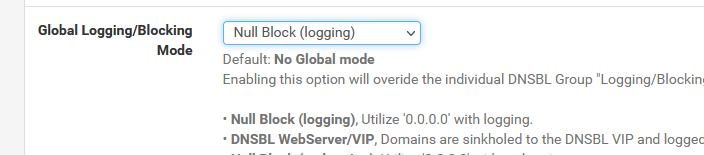
To make a long story short : don't use the DNSBL web server, because (repeat after me) "it is impossible to redirect a https request".Select :
-
@pftdm007 python mode is very iffy. I have found that using unbound custom dns options works way better to exclude hosts or networks from DNSBL where as python mode only allows /32 exclusions which isn’t very scalable at all. I would highly recommend that over python mode.
-
@gertjan said in Bypassing DNSBL for specific IPs:
Your are using the correct IP addresses ?
Yes. Client assigned IP's from pfsense's DHCP server.
@gertjan said in Bypassing DNSBL for specific IPs:
When you change DNSBL settings :
Do a force realod all for pfBlocker.
Reset for every LAN device the local DNS cache.I do a force reload on ALL (pfb and DNSBL). I usually close all browsers on all machines and retry, I haven't reset the local DNS cache per-se but will try. I only use linux boxes.
@gertjan said in Bypassing DNSBL for specific IPs:
don't use the DNSBL web server, because (repeat after me) "it is impossible to redirect a https request".
Okay I had No Global mode set and changed it to Null Block (logging). lets see if DNSBL is more stable and predictable.
-
Just following up on this -- (Thanks for your help!)
The Python Group Policy action works for whitelisting any clients, per host address e.g. 192.168.1.100 that we do not want DNSBL to filter.
However I have another problem, sort of in the same neighborhood.
I am using GeoIP as well using a domain name white list alias (domain a/s lookup enabled) that I created called "domain_whitelist_v4"
This is the alias URL in the fw:
https://127.0.0.1:443/pfblockerng/pfblockerng.php?pfb=pfB_domain_whitelist_v4
I'm trying to use the same GeoIP alias file " domain_whitelist_v4" in a DNSBL Group Feed source definition to not take action/block on.
The URL I set of the DNSBL group feed source definition is https://127.0.0.1:443/pfblockerng/pfblockerng.php?pfb=pfB_domain_whitelist_v4.txt
I have the action set to "Disabled" instead of Unbound.
I figure that If I update the GeoIP alias "domain_whitelist_v4" section, that I do not have to then also update the DNSBL Whitelist section too since their (DNSBL & GeoIP) are both referencing the same domain name list (domain_whitelist_v4). Instead I have to update in 2 places for domain reachability sometimes depending if its also being blocked via GeoIP
Ideally, I don't want to remove all filtering for some clients, but instead I'd like to update one alias file that covers both DNSBL (permit) and GeoIP (permit)
-
 P provels referenced this topic on
P provels referenced this topic on
-
Is there a way to bypass just one url request so it always goes to 8.8.8.8 for example?
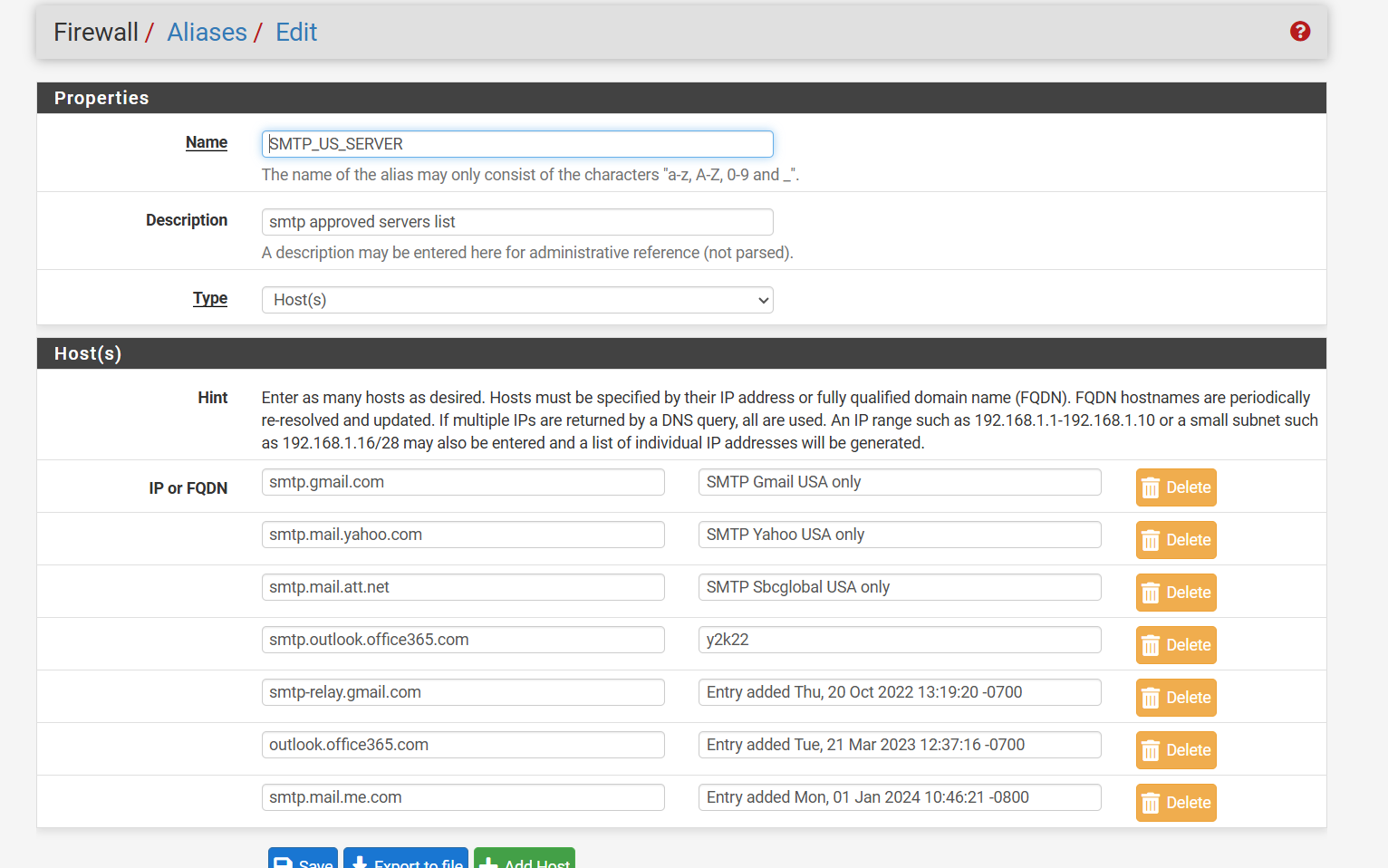
imap.gmail.com for example keeps getting saved inside my cache I use strict destination for my outgoing smtp and imap ports everything works except gmail because it uses so many rotating ip addresses.
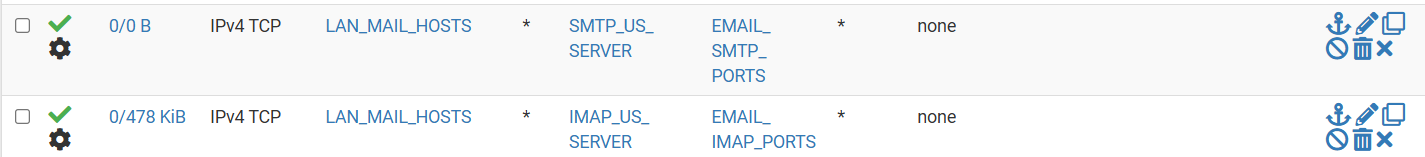
I have an alias that only allows outbound mail to go to servers we use.
Example outlook, gmail, yahoo, apple mail, and nothing else.
Maybe something like???
server: access-control-view: imap.gmail.com bypass view: name "bypass" view-first: yes forward-addr: 8.8.8.8@853????The goal is to never check the cache database for this address to just send it up stream so the authoritative server resolves it every time it is requested
You remember a couple of years ago some government offices were hacked because they had any any for outbound mail ports? This is my solution to fix this but gmail makes it difficult it is the only one that you have to refresh to get it to connect in mail applications everything else is fine with timeouts, google must change ip addresses every min or less at times for gmail.
-
@JonathanLee Try this:
forward-zone: name: "imap.gmail.com" forward-addr: 8.8.8.8 forward-no-cache: yesDidn't test it, so not sure if its going to work.
Got this info from the following link: https://unbound.docs.nlnetlabs.nl/en/latest/manpages/unbound.conf.html -
@mcury said in Bypassing DNSBL for specific IPs:
forward-zone:
name: "imap.gmail.com"
forward-addr: 8.8.8.8
forward-no-cache: yesThanks, I appreciate your help this also did not work. It came back.
I am trying it like this now before server:
forward-zone: name: "imap.gmail.com" forward-addr: 8.8.8.8 forward-no-cache: yes server: do-ip4: yes prefer-ip4: yes do-ip6: no prefer-ip6: no private-address: ::/0 dns64-ignore-aaaa: *.* do-not-query-address: :: do-not-query-address: ::1 do-not-query-address: ::/0I hope this works versus after server:
-
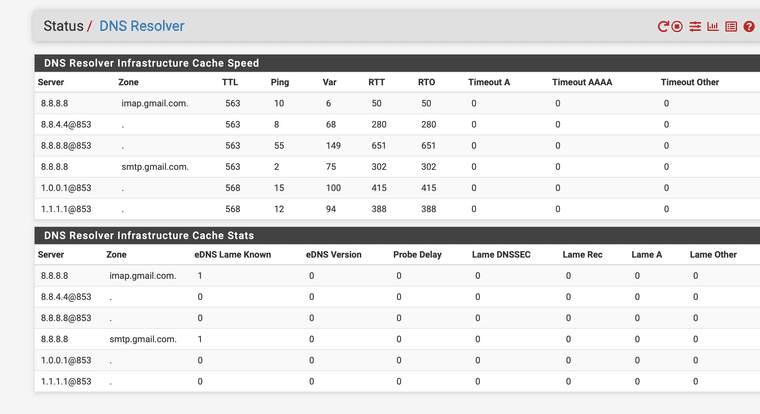
That seemed to fix it so now the email system can only send out to gmail and google will tell devices what ip to use each time without it changing gmail was driving me crazy
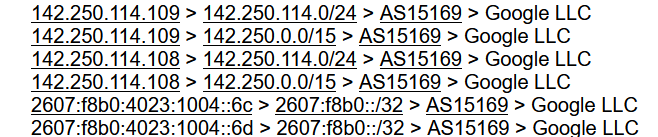
iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.250.141.108 Name: imap.gmail.com Address: 142.250.141.109 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.251.2.108 Name: imap.gmail.com Address: 142.251.2.109 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.251.2.108 Name: imap.gmail.com Address: 142.251.2.109 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.251.2.109 Name: imap.gmail.com Address: 142.251.2.108 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.250.141.109 Name: imap.gmail.com Address: 142.250.141.108 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.250.141.109 Name: imap.gmail.com Address: 142.250.141.108 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.250.141.109 Name: imap.gmail.com Address: 142.250.141.108 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.251.2.109 Name: imap.gmail.com Address: 142.251.2.108 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.250.141.109 Name: imap.gmail.com Address: 142.250.141.108 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.250.141.109 Name: imap.gmail.com Address: 142.250.141.108 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.251.2.109 Name: imap.gmail.com Address: 142.251.2.108 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.250.141.109 Name: imap.gmail.com Address: 142.250.141.108 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.250.141.108 Name: imap.gmail.com Address: 142.250.141.109 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.250.141.109 Name: imap.gmail.com Address: 142.250.141.108 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.250.141.108 Name: imap.gmail.com Address: 142.250.141.109 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.250.141.109 Name: imap.gmail.com Address: 142.250.141.108 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.250.141.108 Name: imap.gmail.com Address: 142.250.141.109 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.250.141.108 Name: imap.gmail.com Address: 142.250.141.109 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.251.2.109 Name: imap.gmail.com Address: 142.251.2.108 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.250.141.108 Name: imap.gmail.com Address: 142.250.141.109 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.251.2.109 Name: imap.gmail.com Address: 142.251.2.108 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.250.141.108 Name: imap.gmail.com Address: 142.250.141.109 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.250.141.109 Name: imap.gmail.com Address: 142.250.141.108 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.251.2.109 Name: imap.gmail.com Address: 142.251.2.108 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.250.141.108 Name: imap.gmail.com Address: 142.250.141.109 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.251.2.109 Name: imap.gmail.com Address: 142.251.2.108 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.250.141.108 Name: imap.gmail.com Address: 142.250.141.109 iMac:~ joanthanlee$ nslookup imap.gmail.com Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: Name: imap.gmail.com Address: 142.251.2.108 Name: imap.gmail.com Address: 142.251.2.109You can now see it change every time before it would cache it and resend it.
UPDATE: It still times out and shows errors like before, I wonder what the issue is with it having the old IP address weird right?
-
@JonathanLee said in Bypassing DNSBL for specific IPs:
UPDATE: It still times out and shows errors like before, I wonder what the issue is with it having the old IP address weird right?
So, as I see it, DNS is not caching anymore, however since you are using an alias with FQDNs, the firewall itself will cache those for 5 minutes (300 seconds).
https://docs.netgate.com/pfsense/en/latest/firewall/aliases.html
Instead of using this method (alias with FQDN), try creating a firewall rule just for imap.gmail.com using AS15169.
You can do it throuhg pfBlockerNG IP, not through DNSBL.
Edit: Another way would be to create an alias with all the IPs you were able to resolve using the nslookup above.
-
@mcury thanks for the reply I will test this soon and yet you know how it works out.
-
 P publictoiletbowl referenced this topic on
P publictoiletbowl referenced this topic on