Recommended settings for Cryptographic Hardware & Thermal Sensors [SG-4860, SG-3100]
-
Using pfSense 2.4.3 on SG-3100 or SG-4860 what are the recommended settings for System > Advanced > Miscellaneous > Cryptographic Hardware and Thermal Sensors?
Appliances from Netgate seem to ship with Cryptographic Hardware set to None and Thermal Sensors set to None/ACPI.
Are these right, and a little explanation of when one might want to use "aesni or "aesni, cryptodev" modes would be awesome. I've read a bunch of threads here that just left me confused. Thank you
edit: since people are asking, my config has:
- 1 openvpn server (aes-128-gcm)
- 5 openvpn clients (mix of aes-256-gcm and aes-256-cbc)
- 1 IPsec tunnel (IKEv2, AES256-GCM for both P1/P2)
-
For the SG-4860, AES-NI and the Intel Core settings for Cryptographic Hardware and Thermal Sensors can be selected.
Not sure about the SG-3100... I know it has an ARM CPU, so I think None/ACPI would apply best for thermal... but there may be other drivers already loaded for cryptographic acceleration. I know that AES-NI is an Intel-specific thing also... so that one wouldn't likely be selected. Hopefully someone from Netgate will come through and clear this one up. :)
-
After quickly experimenting, I discovered that (on the SG-4860) unless I set Thermal Sensors to "Intel Core", there was no Temp displayed on the dashboard. So that answers that part of the question.
Still looking for an official answer to the mysterious AESNI question...
-
not sure why you are asking a internet forum on what YOU need when we have no idea what your configuration is.
do you have a openvpn server or client setup on your device? if you don't, you don't need it enabled. if you DO. its wise to utilize it
hope that help
for thermal. you got that one figured out. i enabled it on both of my devices as well!
-
AES-NI applies to more than just OpenVPN... IPSEC also uses it. But it's mainly for VPN services because of the encryption, so if you're not using VPN functions of pfSense, it probably won't do much for you regardless of what it's set to.
Again, with an SG-4860, I would think that selecting AES-NI would be the correct setting. It has an Atom C2558 CPU, which has AES-NI support. Whether CryptoBSD is necessary or not, I don't know. I have an SG-2440 with the C2358 processor and use just AES-NI on mine without issue.
-
@bcruze said in Recommended settings for Cryptographic Hardware & Thermal Sensors [SG-4860, SG-3100]:
do you have a openvpn server or client setup on your device?
I do have both ovpn and IPsec tunnels, I updated my OP with details.
-
I, too, would like an official answer to this. But, looking at the OpenVPN section of the 2.4 release notes:
https://www.netgate.com/docs/pfsense/releases/2-4-new-features-and-changes.html#openvpn
I see the following:
This is a significant upgrade which includes support for a wide variety of new features, including AEAD ciphers such as AES-GCM.
AES-GCM can be accelerated by AES-NI, and is supported in SSL/TLS modes (not shared key)
I vaguely recall some old posts saying that without AES-GCM, AES-NI wouldn't be helpful in OpenVPN (something about the overhead with kernel calls to the hardware?). But, from the above, I'd say that since you're using 2.4.3 on that hardware, as long as you use the AES-xxx-GCM flavors of encryption, you'd want to turn AES-NI hardware support ON. That's my GUESS, though.
-
The questions I have still:
-
If AESNI generally speeds up these ciphers, why does Netgate ship its appliances with it disabled?
-
Still curious which situations benefit from having "aesni_cryptodev" (both) enabled
-
-
@luckman212
On Netgate hardware, I think it defaults to None because the cryptographic algorithm has to be supported (i.e., GCM). I also found an old thread:https://forum.netgate.com/topic/114212/aes-ni-cryptodev-openvpn-help-a-n00b-understand/17
with a response from Jimp in it:
With the BSD Cryptodev engine loaded along with the AES-NI module, OpenVPN would latch onto that instead of using AES-NI, resulting in lower speeds because the BSD Cryptodev hooks for AES-NI only supported AES-GCM, while claiming to support more. Before 2.4, you could not run without the BSD cryptodev engine active, and on 2.4 you can.
Now if you didn’t have the AES-NI module loaded, it wouldn’t matter, OpenVPN would latch onto it and use it to accelerate anything it could. But you couldn’t accelerate AES-GCM with IPsec without the AES-NI module loaded.
-
I don't have one to test but I thought I looked at a new SG-3100 for this question and it was enabled....
For what it's worth ours shows in its CPU Type section on the home page:
CPU: ARM Cortex-A9 r4p1 (ECO: 0x00000000)
Multiprocessing, Thumb2, Security, VMSAv7, Coherent Walk
2 CPUs:
SOC: Marvell 88F6820, TClock 250MHz, Frequency 1600MHz
Crypto: Marvell Cryptographic Engine and Security Accelerator...while a pfSense CE version running on a really old PC shows nothing, but has a line for AES:
Intel(R) Core(TM)2 Duo CPU E7500 @ 2.93GHz
2 CPUs: 1 package(s) x 2 core(s)
AES-NI CPU Crypto: NoWe have our 3100 set to BSD Crypto Device which I thought was the default.
If memory serves, if one enables a crypto setting and it doesn't work there is an error logged, perhaps just at bootup.
@bcruze , remember that pfSense 2.5+ will require hardware crypto support. Perhaps at that point they will autodetect it...?
-
I reread the blog post on 2.5 (https://www.netgate.com/blog/pfsense-2-5-and-aes-ni.html) and it says it requires AES NI not just any crypto, so assuming they aren't abandoning the new SG-3100 already, it seems like it should support AES-NI...?
"On ARM-based systems, the additional load from AES operations will be offloaded to on-die cryptographic accelerators, such as the one found on our SG-1000. ARM v8 CPUs include instructions like AES-NI that can be used to increase performance of the AES algorithm on these platforms."
Perhaps their definition of "like AES-NI" is "close enough"? If the SG-1000 is OK I have to believe the 3100 is OK also.
-
@teamits
The SG-3100 has an ARM processor so no AES-NI but that is ok because it has its own crypto.
"Crypto: Marvell Cryptographic Engine and Security Accelerator"I use OpenVPN with GCM and use settings BSD Crypto Device (cryptodev) and have none set for thermal sensors which by the way show the core temp. The core will show higher than you would typically see on a fan based system reading from a board location.
-
Good point on the temp, seeing 60+ degrees C was a bit scary at first!
-
To add a bit to the confusion, I saw this post from Chris on /r/PFSENSE that says
We are still aggressively working on the driver for the SG-3100; there is no setting you need to change to enable it. When it's included, you will want to select BSD crypto device
-
@luckman212 said in Recommended settings for Cryptographic Hardware & Thermal Sensors [SG-4860, SG-3100]:
To add a bit to the confusion, I saw this post from Chris on /r/PFSENSE that says
We are still aggressively working on the driver for the SG-3100; there is no setting you need to change to enable it. When it's included, you will want to select BSD crypto device
If you take it out of it's context it might be confusing, but it's rather simple:
- Until the driver is included there is no setting to enable crypto acceleration.
- When the driver is included you need to select BSD crypto device
-
I think there may have been some misreading there. We are working on the SG-1100 crypto hardware driver. The SG-3100 crypto is already supported via the CESA driver. You do need to choose BSD crypto device to use it there.
Steve
-
@stephenw10 said in Recommended settings for Cryptographic Hardware & Thermal Sensors [SG-4860, SG-3100]:
The SG-3100 crypto is already supported via the CESA driver. You do need to choose BSD crypto device to use it there.
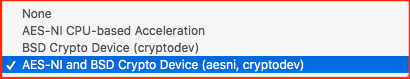
Ah that makes a bit more sense. Thanks for clearing that up Steve. So, should the setting be "cryptodev" or "aesni, cryptodev" then?
-
Only cryptodev.
AES-NI is x86.-Rico