Dual LAN setup with OpenVPN client troubles
-
My pfsense setup has been running great for 4 months now, but now I would like to add a second LAN interface to the mix. In a nutshell, I would like my primary LAN (172.16.0.x) to continue to route traffic over my secure OpenVPN client and the LAN2 (172.18.0.x) to route its traffic directly to the primary WAN interface. So far, I can't seem to get the LAN2 connection to connect to the internet unless it is bound to the OpenVPN, OPT1, interface.
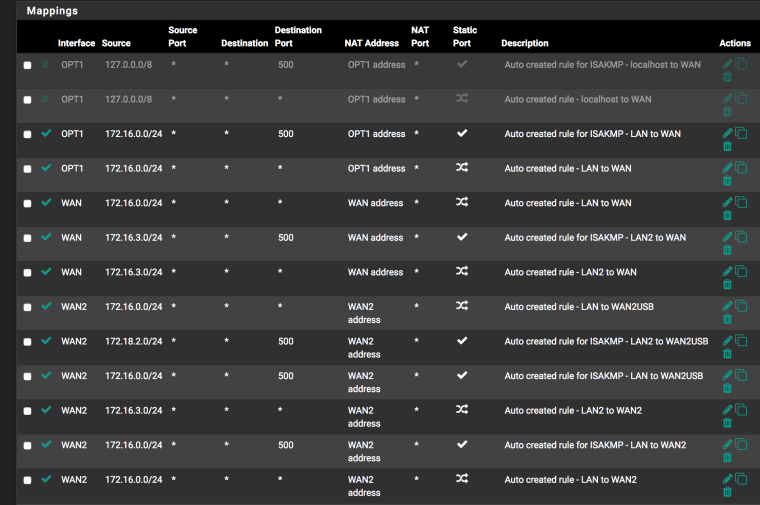
After adding a second LAN2 interface and setting the outbound NAT to the WAN interface, I can only reach the targets on the local network. If I take the LAN2 interface and configure its outbound traffic to the same OPT1 interface, it routes successfully to the internet. Can I not have one LAN on OPT1/OpenVPN and the other LAN interface connected to the the WAN interface? Is there some magic setting in NAT:Outbound section that I missed? The current mode is set to Manual Outbound NAT.
-
@trevorone Does anyone have any suggestions regarding a resolution to my problem? I have tried just about everything that I can think of.
-
@trevorone I was just about to nuke my install and start over, but I finally got my LAN 2 interface to route to the internet rather than just the local subnets. I had to go to Firewall>Rules>Edit>Advanced and select a gateway for LAN2. Originally, the LAN2 rules were set to Default (which is specified in System>Routing>Gateway), but for some reason, it refused to acknowledge my default gateway preference .
Now I have LAN1 routing over my secure OpenVPN client and LAN2 routing via my ISP. My pfsense router is also configured with dual WAN interfaces in a gateway group to allow continued connectivity should either ISP connection fail. Maybe this is why I had to specify a specific gateway ... thoughts?
-
@trevorone said in Dual LAN setup with OpenVPN client troubles:
Advanced and select a gateway for LAN2
If you mean you setup a gateway in the rlan2 rules to use - that is different. If your default route on pfsense was to use your vpn connection. Then yes you would have to allow a rule that forces it out a different gateway. Do you have a rule above this to allow lan2 to talk to lan1? Do you not want lan2 to talk to lan1?
-
@johnpoz I was testing this in my lab first. I have LAN1 on 172.16.0.1 and LAN2 on 172.16.3.1. From the beginning, I could reach LAN1 from LAN2 and vice versa. I could also reach targets upstream on WAN1/WAN2 networks, but never anything beyond (the Internet) unless the OVPN Client was connected with traffic flowing thru OPT1. LAN2 would not route to the internet unless it, too, was bound to OPT1 via a manual outbound NAT rule. I could essentially ping anything on the local subnets but not the internet. This was not the case when I initially setup the router with only a LAN/WAN interface and no VPN/OPT1 interfaces. There must be a setting or rule some where that forcing everything to the OPVN Client gateway. Anyway, while banging my head against the wall late last night, I decided to try Firewall>Rules>Edit>Advanced and setting the default gateway manually. That worked like a charm.
LAN1 still fails to route to the internet unless OPT1/OPVN client is online, but I am perfectly fine with that arrangement. I just wanted LAN2 traffic to go directly out to my ISP WAN1 interface without the VPN.
-
@trevorone said in Dual LAN setup with OpenVPN client troubles:
From the beginning, I could reach LAN1 from LAN2 and vice versa
No you couldn't not without rules.. the only interface that has default any any is lan.. Once you add another interface you would have to create rules to allow traffic. Which wan is used to access something would be based upon you routing and what happens or doesn't happen with that traffic once it leaves pfsense would be up to what you have upstream, are you natting it outbound, etc.
You want help figuring out what you did wrong, or what your doing wrong.. Your going to have to give more detail. How about a simple drawing of how you have everything connected. Seems like your pfsense is downstream and not at the edge..
-
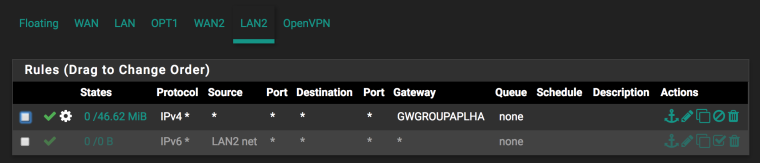
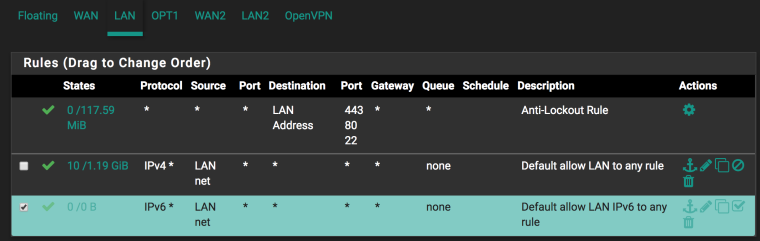
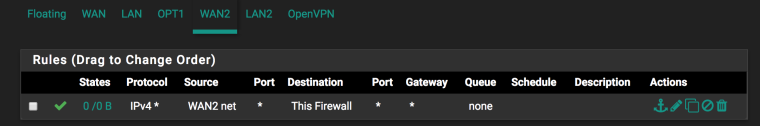
@johnpoz !
Thanks for the feedback John. I never said that I did not have rules, I just do not recall setting up any rules aside from my initial router configuration and the setup of the OVPN/OPT interface. Prior to setting up OVPN, my NAT Outbound was set to Automatic. My firewall rules were set as illustrated in the screen captures below. After following the instructions for OVPN client setup, I set my NAT Outbound to manual. I just added the LAN2 interface a few weeks ago and finally got around to testing it out earlier this week. The perplexing thing is that I could ping targets on the local subnets (172.16.0.x/172.16.3.x) and the WANs (10.0.2.1/10.0.16.1) but not the internet, so I figured that it had to be something (rule or some setting) preventing a connection out.Again, thanks for the feedback. I am still new to the world of pfsense and I am still learning.

-
@trevorone said in Dual LAN setup with OpenVPN client troubles:
After following the instructions for OVPN client setup, I set my NAT Outbound to manual
Flawed instructions if you ask me - there is no reason to go full manual just because you want to add a vpn client. Hybrid works fine here. Now you can add your manual outbound nats you might need for a vpn client connection along with letting pfsense do what it does best and take care of the behind the scene requirements.
Why do you have rules on your wan allowing unfiltered access to anything on firewall?
And your lan2 rules are forcing traffic out a gateway before you allow traffic to say lan.. Really suggest you read up on policy routing if that is what you want to do.
https://www.netgate.com/docs/pfsense/routing/directing-traffic-with-policy-routing.html
-
@johnpoz I did switch it hybrid at one point, but since I was having so much trouble, I decided to follow the instructions verbatim until I got the connectivity problem figured out. I will have to read up on policy routing. Is it not required for dual wan setup? BTW, the LAN2/GWGroupAlpha was the only way that I could get LAN2 to the Internet. Prior to selecting that, I was stuck in local traffic lanes only. And regarding those wide open WAN rules, I would definitely lock that down before putting this in a production situation. I just wanted to get things up and running quickly as a proof of concept. The initial basic router setup was easy. Then I added an OVPN client and the second WAN. This is where things started to turn custard I guess. The LAN2 addition was the last major change over the past week. Each change has been a learning experience. Thanks again for the guidance. I am just a young padawan ...
-
Why would you think you need a wan rules at all? Where you access the gui from you wan side? Out of the box pfsense has zero rules on the wan.. Because unless you want to run a service or port forward there is nothing actually required to be able to hit from the wan unsolicited.
The only time you would need to put anything on wan interface if for a specific something. And btw allowing traffic to "this firewall" means your allowing access to ANY ip on the firewall, even the lan IP..
-
@johnpoz Thanks for breaking that down. Not sure what I was thinking. I started cleaning things up right after getting your previous thread.