Supposed General IPSec Vulnerability - Does it affect us?
-
Saw this yesterday, and was wondering if it might affect PFSense IPSec implementation?
Researchers Break IPsec VPN Connections with 20-Year-Old Protocol Flaw
The first paragraph mention the key points:
"A new Bleichenbacher oracle cryptographic attack has been set loose on the world, using a 20-year-old protocol flaw to compromise the Internet Key Exchange (IKE) protocol used to secure IP communications."Not that this is extremely actionable, or a looming threat, but it's made the rounds a little bit and might possibly make it across some CTO desk and cause some panic. So is the IPSec implementation used in PFSense, assuming the one from OpenBSD, affected by this "20-year-old protocol flaw"?
-
It does affect pfSense but there isn't much you can do aside from switching to RSA auth or using a stronger PSK.
From the note we received, it affects "all IKEv1 RFC 2409 compliant implementations which allow the authentication mode PSK and main mode of operation" and probably IKEv2 as well. Including strongSwan, and implementations from pretty much any vendor out there that supports IPsec.
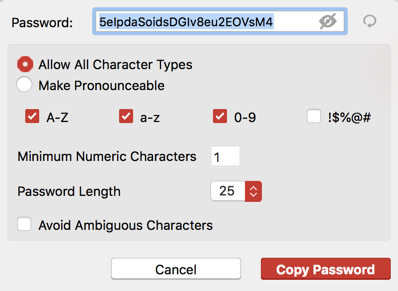
We have been improving the documentation and GUI encryption suggestions to push for more secure PSKs and other best practices as well. For example, I recently rewrote the IPsec site-to-site walkthrough and added some info about making a good PSK: https://www.netgate.com/docs/pfsense/vpn/ipsec/configuring-a-site-to-site-ipsec-vpn.html#securely-generating-a-pre-shared-key
On 2.4.4 there is also a button to generate a PSK for you, which uses the technique described there.
If strongSwan finds a way to prevent the attack and puts out an update, we'll get it ASAP, but there isn't any sign of that happening. And doing so might even break compatibility with other vendors, so we'll have to wait and see what happens either way.
-



And THAT is a useful post and useful information! LOL, I partly posted because I was hoping to get some practical information, and you guys delivered... AGAIN!
Thanks again PFSense Team, keep up the good work!


-
Something like this gets you 131 bits of entropy (> 128) for use as a PSK. But if this isn't a wake-up call to just switch to RSA, I don't know what is. Really good time to at least re-key to something strong.
-
Thankfully I apparently did use a random generator like that and my PSKeys are all over 25 characters. But yes, I'm going to work on switching all my IPSec VPNs to RSA... I guess at the time I set it up PSK was easiest, but it's time to go back an raise the bar.
Good part? I got us moved to PFSense several years ago, so every office has at least a SG-2220 or SG-1000, so updating everything is cake.


-
Since CERT has now also made the details of this issue public, I made our Redmine issue for it public: https://redmine.pfsense.org/issues/8667