Multiple WAN IP setup for servers
-
Through the virtues of changing ISP, I'm being provided a block of 16 IP's. Most of these will be used to deploy a few mail servers, which need their own respective public IP.
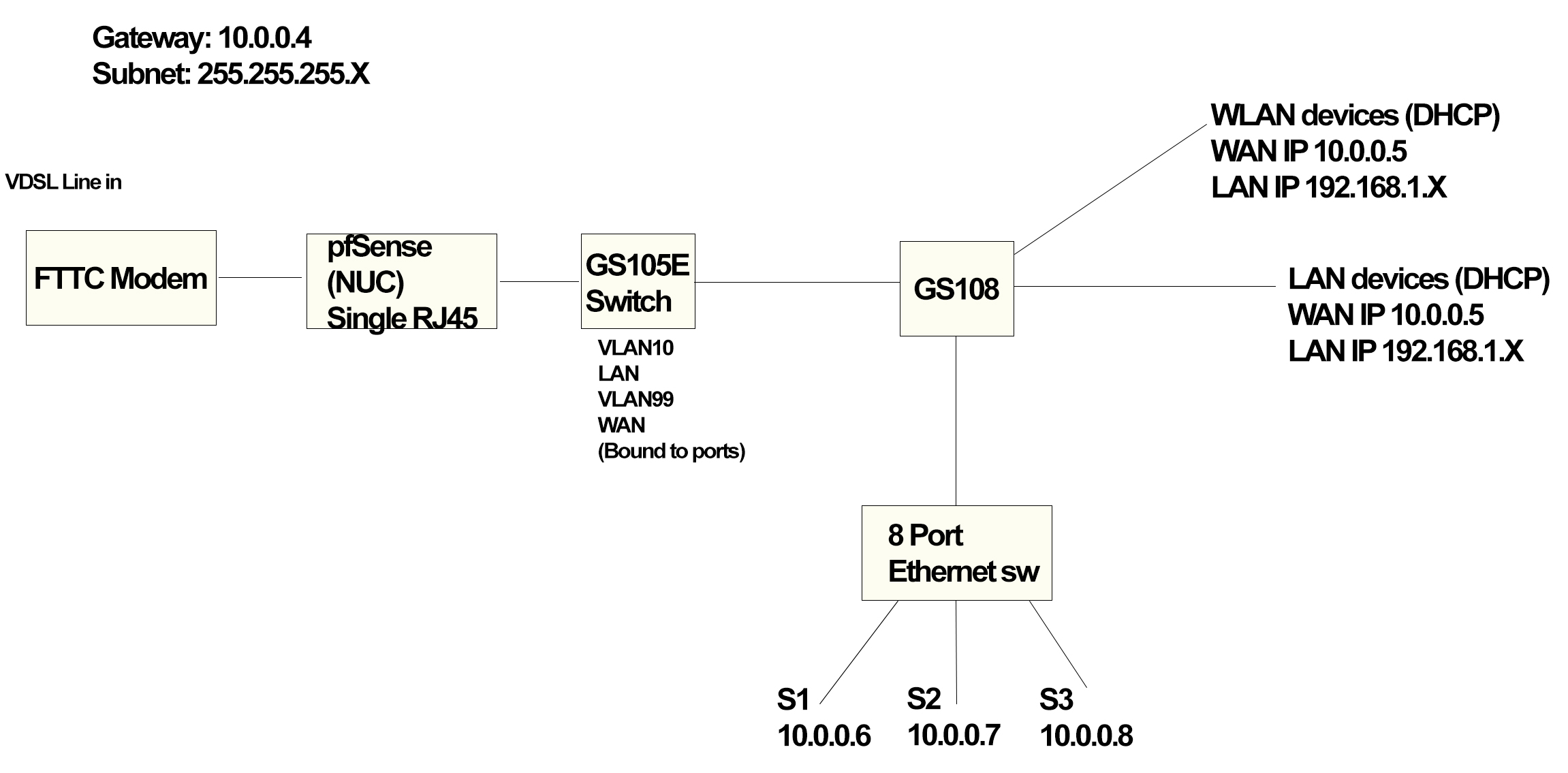
My pfSense setup is non-standard, where I'm using an Intel NUC (single RJ45) and VLAN's and a GS105E to set it up. LAN is VLAN 10, WAN is VLAN99 (very basic network map attached).
What I ideally want to do is ensure that the servers have their own public IP for use - so that different applications can be used on port 80 and 443 per server. From what I understand, I'd need to add the IP's as Virtual IPs. The home devices (like iPhones, laptops etc) will need to be under one public IP but will be NAT'ed via pfSense.
It's from this stage I'm confused.
The auto IP assigned will be used for the home devices via NAT. The additionals will be used for the server stuff. On each server, I need to be able to specify its public IP under the IPv4 settings. Will I be able to do this with the VIP setup and assign one IP per MAC? Or, do I need any additional hardware to get this to work as expected?
Network map attached. Imagine I'm being provided 10.0.0.1/28 from my ISP. Any guidance is appreciated (service is getting switched in September so have time to plan).
-
So your swaying you want to put these device direct on the public network vlan? Then why did you bring up VIP?
What auto assigned IP? Normally when you get a block of IPs - ie your /28 then this would be setup static? Gateway of 10.0.0.4 is ODD for a /28.. And with a /24 mask? Thought you said you had a /28 - which is 14 address not 16 btw..
If ISP gives you IPs to use - then yes they can be setup as VIPs on your wan. You then can use these vips as 1:1 Nat or normal port forwards. And yes you can outbound nat specific devices to these vips vs letting them nat to the actual IP you have on your wan.
Just change your outbound nat to hybrid and setup the nats you want for your outbound traffic from these machines to use.
-
@johnpoz said in Multiple WAN IP setup for servers:
What auto assigned IP? Normally when you get a block of IPs - ie your /28 then this would be setup static? Gateway of 10.0.0.4 is ODD for a /28.. And with a /24 mask? Thought you said you had a /28 - which is 14 address not 16 btw..
Total IP's assigned by the ISP is 16, with 14 usable yes. Sorry, ignore the 10.0.0.4 (I did the map last night - it'll be whatever the ISP specifies).
1:1 NAT sounds like the way to go it seems. So with the home devices that'll have one public IP and then NAT (on 192.168...) internally, I assume I'd have to set up the rule for these on the outbound NAT so traffic from these goes via that IP?
-
Yes if you want traffic that they initiate to go out that IP, return traffic should auto return via the IP it came in on. I believe its a been awhile since I have looked into that. But yes I do believe when you setup a 1:1 nat and that device sends an answer it will use the vip in the answer. If not it would not work. The point of the outbound nat is so that traffic your device creates will use the vip vs your normal IP.
Once you create the 1:1 nat you just need to create the firewall rules to allow the traffic you want to get to your inside IP. Should all be covered in the 1:1 nat section of the docs and the now available to everyone pfsense book will have more detailed info.. There may even be a hangout video which is also now available to everyone that goes over it.. Not sure but very possible.
https://www.netgate.com/docs/pfsense/book/nat/1-1-nat.html
-
If you need a specific outside address for inbound connections I would use a port forward. For outbound connections sourcing from a specific address I would use outbound NAT. If you need both inbound and outbound connections, or lots of port forwards, or you want to just forward all unsolicited traffic for an outside address to an inside host (like a Linksys "DMZ") I would probably think about using 1:1 NAT.
-
Potentially stupid question but when adding in the IPs in the vIP interface, do I list the entire subnet or individual IPs? And using what CIDR suffix?
Eg: Lets say I've been assigned 10.10.20.0/28, would I stick in 10.0.20.1/28? or 10.0.20.1/32 (denoting its a single IP)?
Trying to add it in as 10.10.20.0/28 obviously gives me the error that you can't add the network address as a vIP.
-
Depends on the type of VIP.
https://www.netgate.com/docs/pfsense/firewall/virtual-ip-address-feature-comparison.html
-
All working. I forgot to enable NAT Reflection (and I only had the bright idea of trying to go to https://virtualIP using my phone off WiFi. Thanks for your help guys!