Working Configuration: DLNA across VLAN's
-
Hi Guys
I though I should share with you a working configuration with DLNA across VLAN's. My configuration is as below. I use a Synology NAS with a media server (IOT VLAN) while my devices are on LAN.
pfsense version 2.4.3-RELEASE-p1NAS - 192.168.11.11 ; VLAN 11; Interface IOT. Default GW 192.168.11.1 (pfsense)
LAN - 192.168.1.0/24 ; Untagged; Interface LAN. Default GW 192.168.1.1(psfense)I use ubiquity AP's and Switch for Layer 2 communications. Assuming you have communication setup correctly between the networks (so LAN can access IOT VLAN), the following was what I did
-
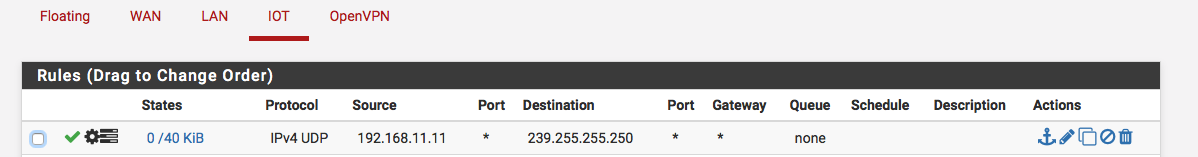
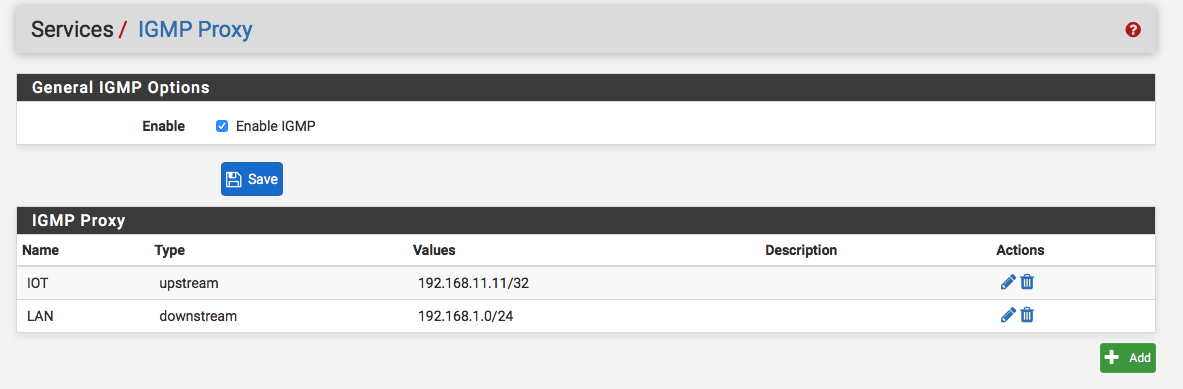
Enable IGMP

-
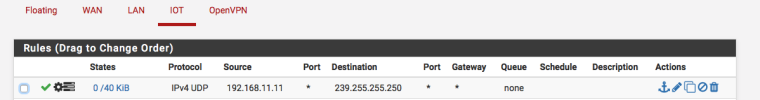
On the Firewall rules for IOT allow multicast to pass. Very important - tick Allow IP options under advanced options when you create this rule. It isn't shown it in the screenshot below.
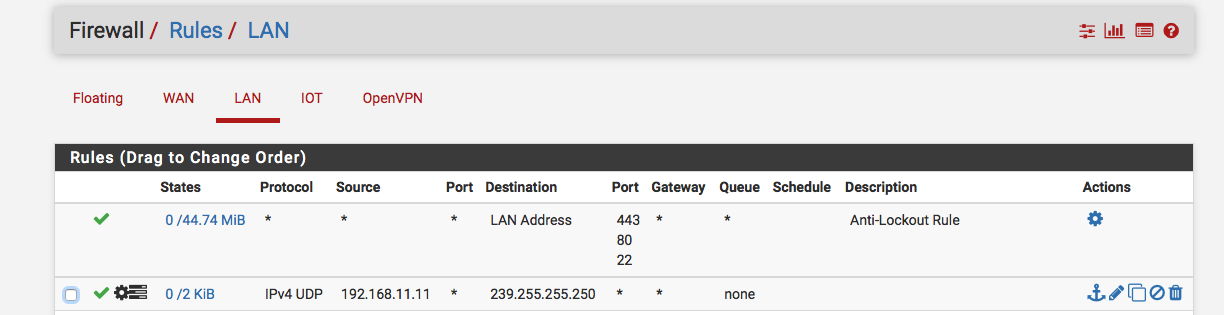
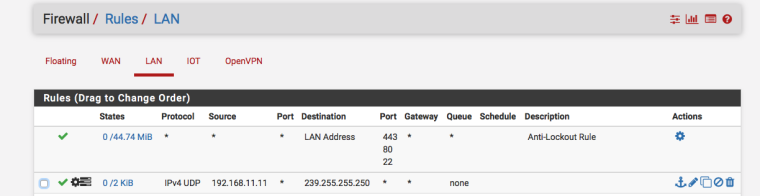
- On the Firewall rules for LAN, accept multicast traffic. Very important - tick Allow IP options under advanced options when you create this rule. It isn't shown it in the screenshot below.
 .
.I went to Status>System Logs>System> General and saw the messages related to "The source address 192.168.1.52 for group 239.255.255.250, is not in any valid net for upstream VIF."
Restarted the IGMP proxy and Gold :) . I still see the error messages ""The source address 192.168.1.52 for group 239.255.255.250, is not in any valid net for upstream VIF." but the configuration works.
P:S - Make sure that the media service is actually working by connecting your device to the IOT vlan and discovering the media player via DLNA.
-
-
Hmm, I would not expect that firewall rule on LAN to ever match anything since packets coming into the LAN interface can never have source IP 192.168.11.11 if the two subnet are correctly separated.
But if it works for you.....

Steve
-
He doesn't have proper layer 2 isolation if his lan is seeing traffic hit that rule.. There should NEVER be a way that 192.168.11 would be source of traffic into the lan that is 192.168.1
Since it shows it has hits - then clearly he has multiple layer 3 networks on the same layer 2 and does NOT have the isolation he thinks he does.. Maybe he has tp-link switch that doesn't actually do vlans correctly and all ports are always in vlan 1.
edit: Oh he has a unifi switch, from what i read over on their forums vlans can be a bit finicky to setup correctly.
-
Well, I would agree that i shouldn’t be seeing traffic coming from the 11.11 into 11.1 subnet (which is the expected and observered behaviour for all other traffic except for the multicast) . I dont know how IGMP proxy works. Perhaps it does preserve the source IP when reflecting the multicast ? I’ll read up some more on it.
The VLAN’s are setup correctly. Without an explicit allow, the two segments dont talk to each other. The only layer 3 device between the two is pfsense.
P.S - VLAN’s on ubiquity are super easy

-
Dude sorry but no even with your igmp proxy it is NOT possible to see that - you have a problem with your vlans..
You have Vlan X and Y... You would NEVER see source traffic from Y into the X interface... Its just not possible without either machine with network settings of Y sitting on the X vlan. Or a cross connection between your vlans.. Your vlans are not isolated at layer 2 like you think they are if you are seeing such traffic.
-
The pf antispoof rules that are applied by default should block that traffic anyway and are above the user rules.
Something isn't right there. Is that counter still increasing? Did you change the rule previously maybe?Steve