Quad9 DNS-over-TLS setup with Unbound & forwarding in 2.4.4-RC
-
@occamsrazor said in Quad9 DNS-over-TLS setup with Unbound & forwarding in 2.4.4-RC:
Technically you could do it in one (
block tcp/udp from any to ! LAN Address port <dnsports>)Wouldn't that block request from getting to pfSense? Or does the "!" mean invert match? Not sure quite how to do that in the GUI, but in any case I think I prefer having two rules, somehow seems easier to understand to me.
The "!" inverts the match, there is a "not" checkbox in the firewall rule destination network options to make that happen. If you find it confusing, don't worry about using that syntax. Clarity is better than being concise, so if using two rules is easier for you to understand, that's just fine.
-
@jimp said in Quad9 DNS-over-TLS setup with Unbound & forwarding in 2.4.4-RC:
@occamsrazor said in Quad9 DNS-over-TLS setup with Unbound & forwarding in 2.4.4-RC:
The "!" inverts the match, there is a "not" checkbox in the firewall rule destination network options to make that happen. If you find it confusing, don't worry about using that syntax. Clarity is better than being concise, so if using two rules is easier for you to understand, that's just fine.
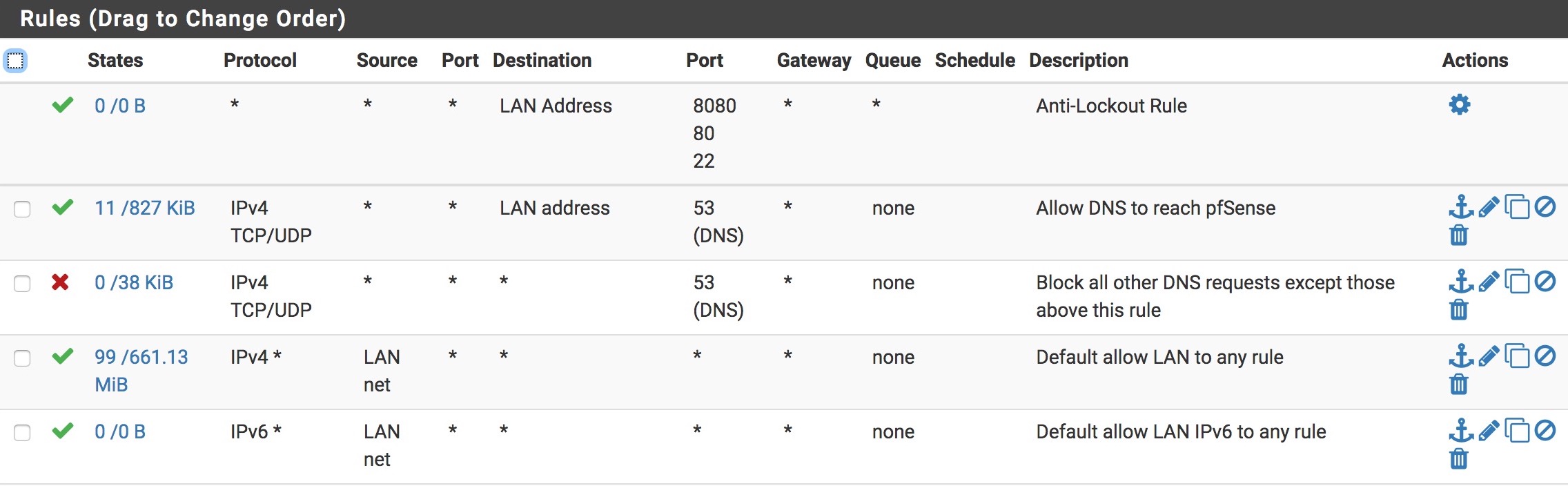
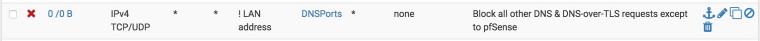
Thanks I understand now, I just didn't know the "!" referred to the invert match checkbox. That's much cleaner. Also, for some reason I thought I needed to explictly allow the DNS to reach LAN Address original rule I had, but now I see that was only necessary because of the way the "block all requests except those above this rule" was written. So basically I can delete the two rules and only use this:
-
@occamsrazor said in Quad9 DNS-over-TLS setup with Unbound & forwarding in 2.4.4-RC:
@jimp said in Quad9 DNS-over-TLS setup with Unbound & forwarding in 2.4.4-RC:
@occamsrazor said in Quad9 DNS-over-TLS setup with Unbound & forwarding in 2.4.4-RC:
The "!" inverts the match, there is a "not" checkbox in the firewall rule destination network options to make that happen. If you find it confusing, don't worry about using that syntax. Clarity is better than being concise, so if using two rules is easier for you to understand, that's just fine.
Thanks I understand now, I just didn't know the "!" referred to the invert match checkbox. That's much cleaner. Also, for some reason I thought I needed to explictly allow the DNS to reach LAN Address original rule I had, but now I see that was only necessary because of the way the "block all requests except those above this rule" was written. So basically I can delete the two rules and only use this:
This rule should be in the Wiki, instead of those other 2 rules there.
https://www.netgate.com/docs/pfsense/dns/blocking-dns-queries-to-external-resolvers.html
Am i am right that the only change to the redirect rule in the Wiki, would be Port 853 added as Destination and Redirect Target Port?
-
@forsaked said in Quad9 DNS-over-TLS setup with Unbound & forwarding in 2.4.4-RC:
Am i am right that the only change to the redirect rule in the Wiki, would be Port 853 added as Destination and Redirect Target Port?
Oh I forgot about that rule that I also had in my NAT > Port Forwards. So if you want to block requests from going outside pfSense, but also to forward those requests to pfSense, then do you need to have both these rules? Don't they sort of cover the same thing? Or it just makes it extra sure?
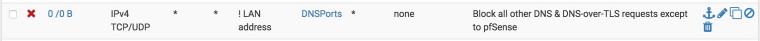
I followed the good advice of @jimp and created a "DNSPorts" alias which does make setting these up easier, so now my port-forward rule looks like this:

When using an alias containing two ports 53 and 853 for Dest. Ports and NAT Ports, is the system smart enough to realise that 53 should go to 53 and 853 to 853?
-
I did the same thing, but since i don't have a client which natively supports DNS over TLS, i can't check if it works with just the Block and Redirect rule.
-
@forsaked Yes I don’t have a way to test either. Just figured I’d set it up in case a device was used on my network that did (eg a visitor).
PS - unrelated, but I have the exact same hardware as you, I like it. -
@occamsrazor The single rule that encompasses the four simple rules is definitely a nice way to compact the Firewall rule set. On the other hand, it gives less detailed information about what is going on, which can help debug issues. For example if the rules on port 853 are never hit, you know that there are not internal DNS over TLS queries. In general, the more compact the rules are, i.e., the more situations they cover, the less visibility into the system they provide.
-
@occamsrazor what is the forwarding address?
-
@d-cgibson87
Hi,
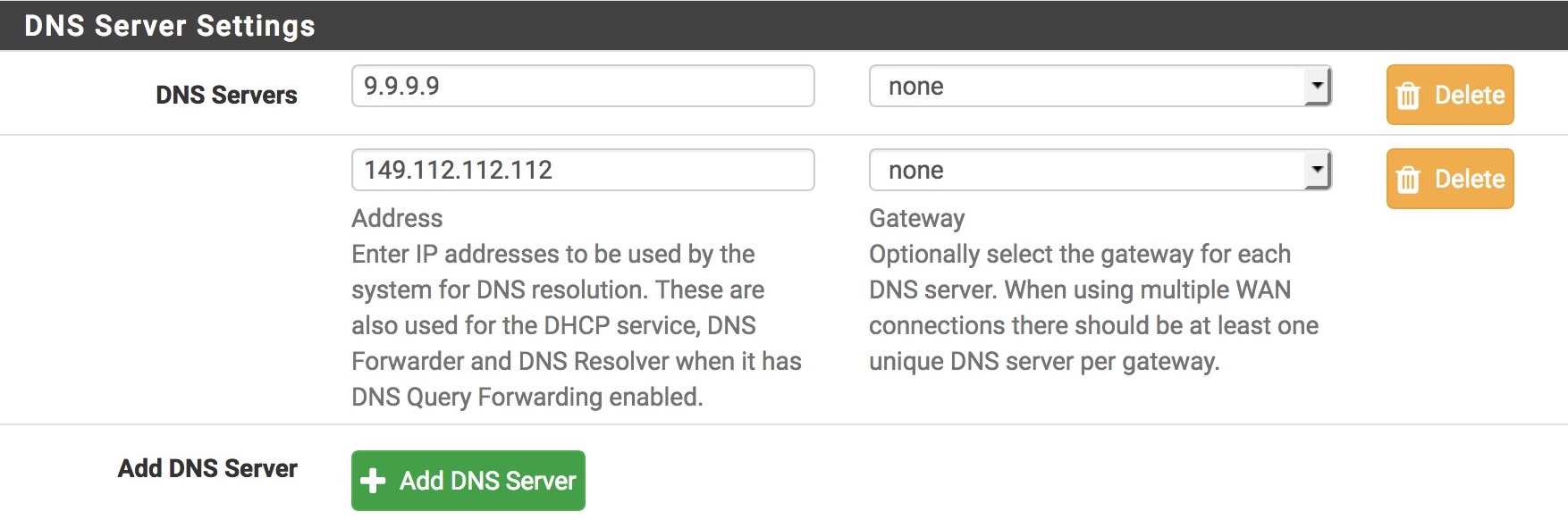
This is what I use: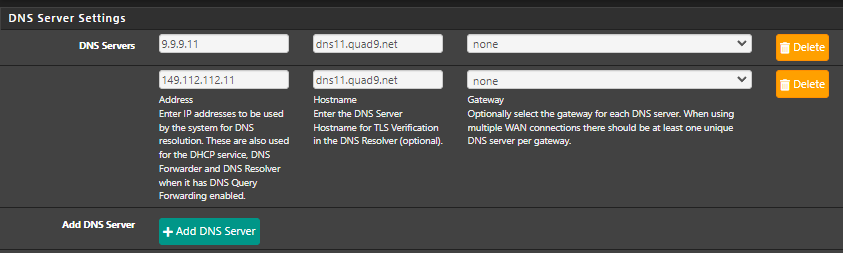
-
Do you know if it is IPSec PSK or RSA or MSCHAPv2
-
@MoonKnight i am running on my galaxy s23. And it shuts my data out all together.
-
 J jimp locked this topic on
J jimp locked this topic on
-
This is a very old topic and you are straying from what it was meant for.
Please start your own topic for help with your setup.
-
 G Gertjan referenced this topic on
G Gertjan referenced this topic on