How to permit a new HTTPS port
-
Hello,
I have a website that i need it which URL is like:
HTTPS://URL:8173
For the user ip address, is allowed to access Internet. (ports: HTTP/HTTPS/FTP). But now it's not working.
I've already did it by customizing allowed ports of HTTPS in TMG firewall, but in pfSense, i can't seem to find a clue.
Thank you in advance. -
Hi,
Where is this web site ?
Somewhere on the Internet ? On one of your LAN's ? Where is the USER ? On a LAN ? -
Hello,
The website is on the Internet, and user is on LAN. -
Then you have nothing to to.
The default LAN firewall rule is : allow everybody to everywhere, using any protocol.Edit : pfSense behaves, by default, as any router that your ISP gave you : from LAN, you can access the world, as soon a sthe WAN interface uis up.
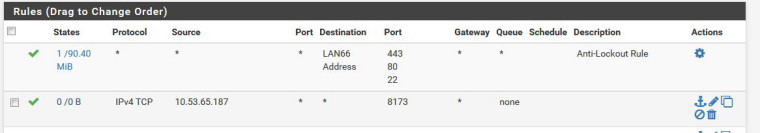
No need to NAT (NAT handles inbound connections, all forbidden, normally) or to ouch anything, it just works.Here a my LAN rules :
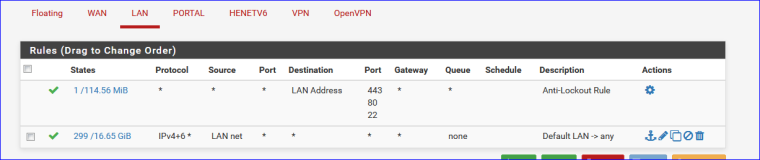
The first rule is the "anti lockout rule.
The second a pass all.
Can visit every IP address, every port, using every protocol. -
The second one is disabled, because i cannot permit anyone to go Internet. I just need to permit the combination of HTTPS + PORT: 8173
What i did in TMG, is configure the HTTPS port number by adding that port. Now i'd like to do the same in pfSense.
Thank you. -
Ah ... this is new :
@lotfidz said in How to permit a new HTTPS port:The second one is disabled, because i cannot permit anyone to go Internet.
I would start with this :
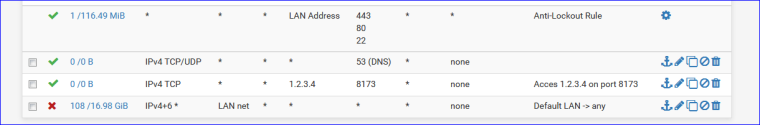
1.2.3.4 is the IP of your URL.
Yous should grant access to DNS, otherwise the 'URL' will never get resolved to 'IP'.
You can't filter for "https" : that's something that IN the packets, pfSense doesn't look at the data - which is scrambled anyway because SSL. Use IP + port number. -
Hello, And thank you for your time.
For DNS, i cannot change it. Because i have already an Active directory Domain.
For the rule:
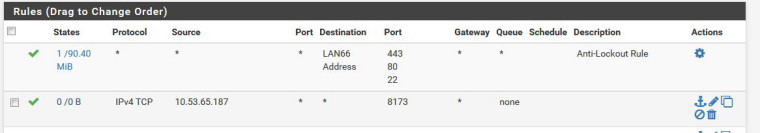
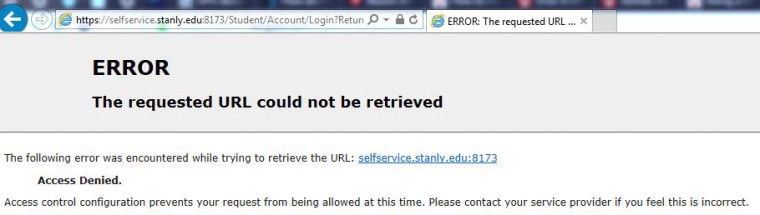
For the error message:
Thank you for your help. -
Your rules do not allow your client to lookup selfservice.stanly.edu so how would they ever talk to that IP on port 8173.. You can just allow clients to that port, but they also need to be able to lookup that FQDN IP..
Which in turn is just a cname anyway for another FQDN
;; ANSWER SECTION:
selfservice.stanly.edu. 3600 IN CNAME ss-prod.stanly.edu.
ss-prod.stanly.edu. 3600 IN A 152.27.54.108Where do these clients point for dns? If they point to pfsense IP then you need to allow the clients to talk to pfsense IP on udp/tcp 53.
-
@lotfidz said in How to permit a new HTTPS port:
Hello, And thank you for your time.
For DNS, i cannot change it. Because i have already an Active directory Domain.
For the rule:
For the error message:
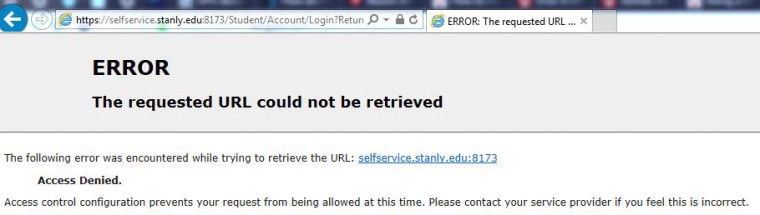
You can not ask your clients to resolve selfservice.s***.edu and the also say that you can't "change DNS".
If clients (device on LAN) can't resolve then the show stops.
Clients have - at a minimum, resolve URL's.
Or, just use IP addresses like https://152.2x.54.108:8173 and your good. -
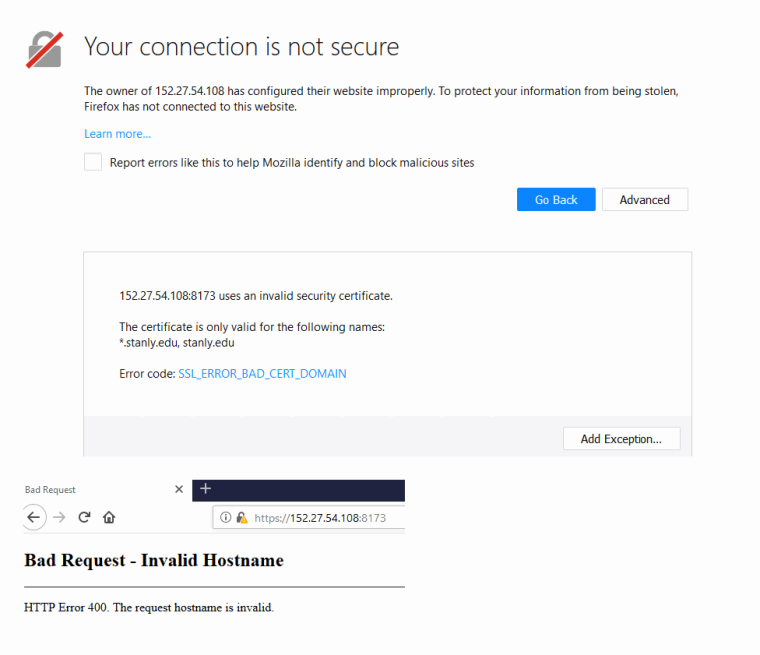
@gertjan said in How to permit a new HTTPS port:
Or, just use IP addresses like https://152.2x.54.108:8173 and your good.
Not always - if the site does not answer to IP, and if https unless the IP is listed in the SAN then they will get an error that will just confuse them shit out of them even more ;)
That is points to cname screams there are going to be multiple sites hosted off that IP - that you would get the actual page you want by hitting the IP directly would be unlikely..
Just like I thought ;)
-
Yep, the IP should be part of the SAN (the certicate on the selfservi****.edu site).
Ok, then make your DNS work !
-
Exactly - if your clients point to your AD for dns, why does it not resolve it? You could just put in a record for that FQDN if you so desired pointing to that IP in the AD dns.. Like a host override in pfsense.
If your client can not resolve this fqdn, then they would never hit the firewall with the dest IP and port..
-
Hello, and thank you for your help.
When i was in TMG, i'd do it like the screenshot bellow.
I want to do the same in pfSense.
For DNS resolution, it's working fine (tested access in the old firewall and it's working).
Still looking for your valuable help.
Thank you

-
it is a squid setting, you are searching for I assume. your screenshot looks like a squid error message, so I assume you are using the squid proxy. Is this a transparent proxy or explicit? you have to allow port 8173 in squid as ssl port.
squid -> acls > ACL SSLPorts
hth
-
@zacha
Thank you! you're a Hero!! Your solution helped me. And i confess, i've already seen it!