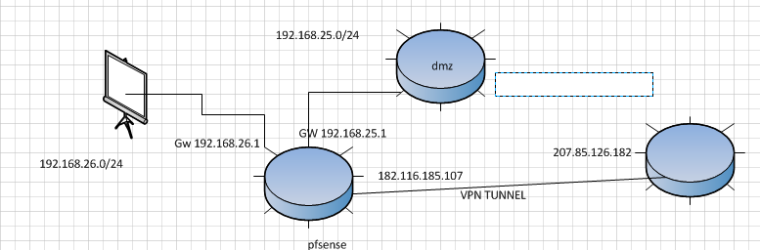
Access to VPN with other network with Masquerade
-
Hello, I have a problem I can not communicate the 192.168.26.0/24 network as seen in the graph since the tunnel that the VPN has only accepts traffic from the IPs of the 192.168.25.0/24 network, find out that I need to mask my IPs from the 26 but I do not understand ... Help me
-
mask? You do not need to mask you just need to setup your what I assume is site to site to allow for the 26/24 network
-
@johnpoz amm need to traffic to network 26 to VPN but I have no idea how to do it since the VPN only accepts traffic from the IPs of network 25 and I do not have access to the other side of the VPN to be able to modify it
-
So I would get with who manages the other side of this site to site and have them add it. Making a device to a different IP for starters would be security issue in such a setup, and 2nd depending on how your actually setup not even possible.
Is this a site to site connection? What is it - ipsec, openvpn?
-
@johnpoz not posible contact with other admin with VPN, the VPN config is with IPSEC
-
@ridley said in Access to VPN with other network with Masquerade:
not posible contact with other admin with VPN
Huh? That makes ZERO sense.. How could you have a site to site vpn connection with NOBODY that can fix the other side... Where you should be concerned is with that... What if it goes down - how is going to fix it?
Is this really a site to site - or is this some vpn service your routing traffic through and your just a client connection?
You just making UP ips that you listed - that end point is a DoD IP address. And your other address is a China address.. You have a vpn connection between an IP In china and a DoD network?? Really?
Masking a IP into a DoD network for sure would be a HUGE concern!!!
-
@johnpoz You would be absolutely AMAZED how many "we can't change, get logs from, or talk to the other side" IPsec tickets we get.
@Ridley If the other side is only expecting connections from 192.168.25.0/24, why are you trying to connect from 192.168.26.0/24?
You can use NAT to translate 192.168.26.0/24 to 192.168.25.0/24 but not both 192.168.25.0/24 and 192.168.26.0/24. Your choices are 1:1 NAT or Many to 1.
-
@Derelict how could that be other then the one side is just too lazy to work out who to contact? How was the tunnel ever brought up in the first place? Both sides have to be involved..
Something is wrong here for sure - either they just pulled those public IPs posted out of thin air and its a crazy coincidence that one is china and the other is dod... Or this is just utter BS completely..
If the one side is DoD, and they discovered you were masking the source IP to allow access - then heads would roll for sure! ;)
If you want a simple solution to the problem presented, then just put your devices in the 26 into the 25 if you need them to talk to the other side.. Or just nat your 26 into the 25.. Simple enough to do with any 20$ soho router.
-
Happens all the time.
I am not putting any weight into the addresses in the diagram.
But yeah. If they want to talk to 25, then put the hosts they need to talk to in 25.
