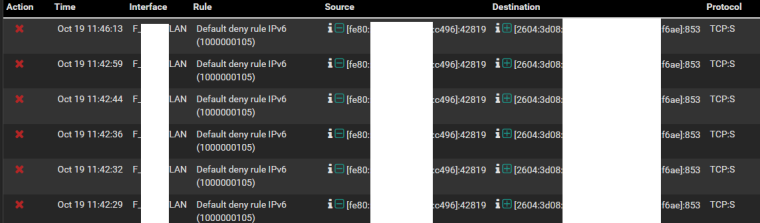
Android 9 "Private DNS"/"DNS over TLS" IPv6 link local to unbound port 853 spam
-
I am seeing port 853 from my android 9 device with default setting of private dns enabled trying to connect to the pfsense unbound dns server ipv6 address getting blocked. The source is link local address.
I am not sure if I should block this or allow it. Any ideas?
-
If your going to run dns on IPv6, then yeah you should not be blocking IPv6 ;)
-
That's up to you. If you have IPv6 enabled on the LAN, and that really is trying to hit the LAN IPv6 address of your firewall, and you have Unbound set to act as a DNS over TLS server, then you probably want to pass them.
If it's going to some other DNS server you probably still want to allow them.
-
@jimp yes I have dns over tls enabled in unbound.
I guess it will help with anyone sniffing packets on my lan.
Thanks for help, I just created a rule to allow it. -
And who is on your lan? And you have old time hubs? Or wifi?
Hmmm - let me think...
I run a service on port X that I want my clients to use.. Should I allow access to this port or not from the clients on my network.. Yah Yah -- I could see why you should check on that ;) -
@johnpoz i am on my lan lol. I have a network tap doing full packet capture and analysis using security onion between my main switch and pfsense.
-
So you want to prevent yourself from sniffing your own traffic?
So your protecting yourself from yourself.. So yeah lets make dns lookups slower and use more overhead.. Sounds like a fantastic plan <rolleyes>
-
@johnpoz 3.8 seconds at the worst. its around 1 sec without dns over tls. I can live with that.
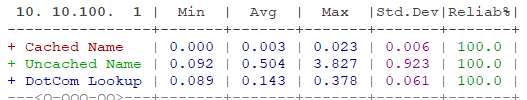
edit: i am going to add cake traffic shaping in front of pfsense soon so that number will improve.
edit2: and I am very self aware of turning on knobs even if it makes no sense. lol -
For what reason are you wanting to wrap overhead around your query when its on your own lan? If the network is not hostile why and the F would you want to add overhead to the query be it 1 ms even. Makes zero sense.. Zero!!!
Have fun... Just utterly pointless.. LIke putting a lock on your thermostat to prevent change - when the only one in the house is you..
-
@johnpoz yes you are right. I am a idiot for doing this and I am well medicated with my illogical paranoid self.
