2 pfSenses, 2 WAN and 1 Local Server
-
Hello,
I am trying to make this scenario:
Place 1 has:- internet connection1
- pfsense1 (WAN(public IP/28), LAN 192.168.0.0/24)
- local server (connected to the same LAN of pfsense1)
Place 2 has:
- 10 computers
- switch
i have two NANOs (Both are in the same LAN of place1) to make the connection between the Place1 and Place2 so i can use the local server in Place2
i need an advice to put pfsense2 and internet connection2(public IP/25) in the place2, so the PCs in place2 use the internet2 and the same local server.
The connection between the two NANOs is more fast than a VPN site-to-site.
How can i do that? how many interfaces that i need to put in pfsense2?
thanks in advance, -
What is a NANO
-
Nano antenna (connection point to point), because the distance between place1 and place2 is 3km
-
The connection mode of the both nanos is bridge
Nano1 ip is 192.168.0.2
Nano2 ip is 192.168.0.3
Pfsense1 lan 192.168.0.200 -
You have to determine everything at Place 2 that needs to access things at place 1 and vice versa.
You are setting yourself up for asymmetric routing issues all over the place.
If you really need those LANs bridged and the Nano link is reliable, I would consider just getting another (or faster) WAN at Place 1.
What is causing the desire to get the internet traffic for Place 2 off the wireless and internet connection 1? What problem are you trying to solve?
-
What i am trying to solve is to find a way that i can access the LAN in place1 from place2 and vice versa and use internet1 just in place1 and internet2 just in place2.
So the connection between two nanos just to pass the LANs packets to be more fast without need to pass the internets over the nanos. -
If i put OPT1 interface in pfsense2 with ip from lan1 subnet and make routing will work?
-
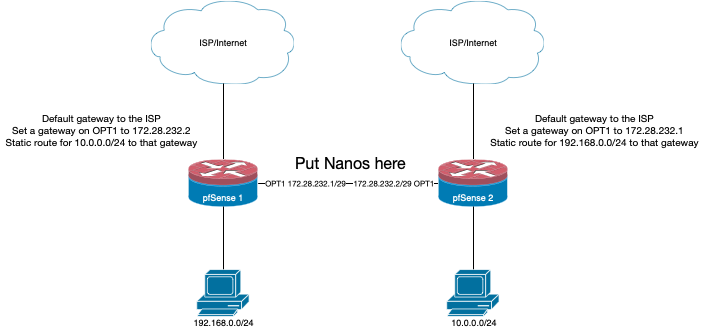
I made the following:
pfsense1 - place1:- WAN (public static ip/28 - ISP default gateway - Internet connection1 10Mbps)
- LAN 192.168.0.200 (192.168.0.0/24 - no default gateway)
- Gateways:
- GW_WAN (default) (ISP default gateway)
- pfsense2_OPT1 192.168.0.201 (not a default gateway)
- Static Routes
- Destination network 10.0.0.0/24 - gateway 192.168.0.201
- Bypass firewall rules for traffic on the same interface checkbox is checked
pfsense2 - place2:
- WAN (public static ip/25 - ISP default gateway - Internet connection2 20Mbps)
- LAN 10.0.0.200 (10.0.0.0/24 - no default gateway)
- OPT1 192.168.0.201 (default gateway 192.168.0.200)
- Gateways:
- GW_WAN (default) (ISP default gateway)
- pfsense1_LAN 192.168.0.200 (not a default gateway)
The connection between pfsesne1- LAN and pfsense2-OPT1 is done by a NANO connection
- NANO1 192.168.0.2/24 connected to the same subnet of pfsense1
- NANO2 192.168.0.3/24 connected directly to pfsense2-OPT1
now all PCs on the both sides can ping each others. But when i connect to internet in place 2, appear for me that i am using the public ip 2 but the speed of internet1 10Mbps. so the internet speed is the same in both sides
-
Don't do it like that. Create a transit network and put the nano bridges on that.
Bypass firewall rules for traffic on the same interface checkbox is checked
If you have to use that checkbox you are almost certainly doing it wrong.
-
i will do, but have to make a load balance?
-
No. If you WANT to you can create a gateway group using the ISP and the wireless gateways so if one side's ISP goes down it could have internet over the wireless, but that is independent of the static route to just the other side's LAN.
-
thanks Derelict
i made exactly the same design that you suggested and worked perfectly for two days and the ping from a pc in LAN1 to a pc in LAN2 was stable. Today, the ping from a pc in LAN1 to the NANO2 (connected directly to OPT2) is stay stable, but the ping from a pc in LAN1 to a pc in LAN2 isn't stable all the time. -
Not sure what you are expecting from us there. Transient internet problems can and do occur. Wireless interference can and does occur.
-
but i am not using the internet to connect the other side, i am using the nano connections, and the nano connection is stable because the ping of other side nano is stable.
-
Well I can safely say that "It's not pfSense."