Site to Site IPsec tunnel with Cisco and pfsense
-
Hi,
I try to route two lans via my remote cisco router and local pfsense. set up ipsec tunnel according to this link!
connection established but it seems that phase 2 dose not run. because my route does no change. I tracroute remote lan but traffic does not go into ipsec tunnel. I add full access in firewall\rule\ipsec but nothing changes! I have no nat device between cisco and pfsense.
here is the output of ipsec statusallipsec statusall Status of IKE charon daemon (strongSwan 5.5.1, FreeBSD 10.3-RELEASE-p19, amd64): uptime: 47 minutes, since Nov 14 22:29:28 2018 worker threads: 11 of 16 idle, 5/0/0/0 working, job queue: 0/0/0/0, scheduled: 12 loaded plugins: charon unbound aes des blowfish rc2 sha2 sha1 md4 md5 random nonce x509 revocation constraints pubkey pkcs1 pkcs7 pkcs8 pkcs12 pgp dnskey sshkey ipseckey pem openssl fips-prf xcbc cmac hmac curl attr kernel-pfkey kernel-pfroute resolve socket-default stroke vici updown eap-identity eap-sim eap-md5 eap-mschapv2 eap-dynamic eap-radius eap-tls eap-ttls eap-peap xauth-generic xauth-eap whitelist addrblock Listening IP addresses: 172.16.5.5 172.16.111.11 Connections: bypasslan: %any...%any IKEv1/2 bypasslan: local: uses public key authentication bypasslan: remote: uses public key authentication bypasslan: child: 172.16.111.0/24|/0 === 172.16.111.0/24|/0 PASS con1000: 172.16.5.5...172.16.5.20 IKEv1 con1000: local: [172.16.5.5] uses pre-shared key authentication con1000: remote: [172.16.5.20] uses pre-shared key authentication con1000: child: 172.16.111.0/24|/0 === 172.16.152.0/24|/0 TUNNEL Shunted Connections: bypasslan: 172.16.111.0/24|/0 === 172.16.111.0/24|/0 PASS Routed Connections: con1000{89}: ROUTED, TUNNEL, reqid 7 con1000{89}: 172.16.111.0/24|/0 === 172.16.152.0/24|/0 Security Associations (1 up, 0 connecting): con1000[6]: ESTABLISHED 12 minutes ago, 172.16.5.5[172.16.5.5]...172.16.5.20[172.16.5.20] con1000[6]: IKEv1 SPIs: ba88d1056ba2927d_i* f2669096e44c371a_r, pre-shared key reauthentication in 7 hours con1000[6]: IKE proposal: 3DES_CBC/HMAC_SHA1_96/PRF_HMAC_SHA1/MODP_102Any help
-
Need the IPsec logs from the time it is trying to establish the CHILD_SA. It will show you something. If it's not coming up something doesn't match the other side.
-
@derelict said in Site to Site IPsec tunnel with Cisco and pfsense:
CHILD_SA
TNX for replyNov 14 20:00:07 charon 15[NET] <con1000|7> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 20:00:07 charon 15[ENC] <con1000|7> parsed INFORMATIONAL_V1 request 2886137138 [ HASH N(DPD) ] Nov 14 20:00:07 charon 15[ENC] <con1000|7> generating INFORMATIONAL_V1 request 654324424 [ HASH N(DPD_ACK) ] Nov 14 20:00:07 charon 15[NET] <con1000|7> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 20:00:17 charon 15[NET] <con1000|7> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 20:00:17 charon 15[ENC] <con1000|7> parsed INFORMATIONAL_V1 request 63519131 [ HASH N(DPD) ] Nov 14 20:00:17 charon 15[ENC] <con1000|7> generating INFORMATIONAL_V1 request 4107794435 [ HASH N(DPD_ACK) ] Nov 14 20:00:17 charon 15[NET] <con1000|7> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 20:00:18 charon 07[CFG] received stroke: terminate 'con1000' Nov 14 20:00:18 charon 15[IKE] <con1000|7> deleting IKE_SA con1000[7] between 172.16.5.5[172.16.5.5]...172.16.5.20[172.16.5.20] Nov 14 20:00:18 charon 15[IKE] <con1000|7> sending DELETE for IKE_SA con1000[7] Nov 14 20:00:18 charon 15[ENC] <con1000|7> generating INFORMATIONAL_V1 request 856932095 [ HASH D ] Nov 14 20:00:18 charon 15[NET] <con1000|7> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (84 bytes) Nov 14 20:00:19 charon 06[CFG] received stroke: terminate 'con1000' Nov 14 20:00:19 charon 06[CFG] no IKE_SA named 'con1000' found Nov 14 20:00:19 charon 15[CFG] received stroke: initiate 'con1000' Nov 14 20:00:19 charon 06[IKE] <con1000|8> initiating Main Mode IKE_SA con1000[8] to 172.16.5.20 Nov 14 20:00:19 charon 06[ENC] <con1000|8> generating ID_PROT request 0 [ SA V V V V V ] Nov 14 20:00:19 charon 06[NET] <con1000|8> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (176 bytes) Nov 14 20:00:19 charon 06[NET] <con1000|8> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (100 bytes) Nov 14 20:00:19 charon 06[ENC] <con1000|8> parsed ID_PROT response 0 [ SA V ] Nov 14 20:00:19 charon 06[IKE] <con1000|8> received NAT-T (RFC 3947) vendor ID Nov 14 20:00:19 charon 06[ENC] <con1000|8> generating ID_PROT request 0 [ KE No NAT-D NAT-D ] Nov 14 20:00:19 charon 06[NET] <con1000|8> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (244 bytes) Nov 14 20:00:19 charon 06[NET] <con1000|8> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (304 bytes) Nov 14 20:00:19 charon 06[ENC] <con1000|8> parsed ID_PROT response 0 [ KE No V V V V NAT-D NAT-D ] Nov 14 20:00:19 charon 06[IKE] <con1000|8> received Cisco Unity vendor ID Nov 14 20:00:19 charon 06[IKE] <con1000|8> received DPD vendor ID Nov 14 20:00:19 charon 06[ENC] <con1000|8> received unknown vendor ID: 07:a1:37:8b:68:69:0b:00:9a:52:02:88:c5:a7:20:7a Nov 14 20:00:19 charon 06[IKE] <con1000|8> received XAuth vendor ID Nov 14 20:00:19 charon 06[ENC] <con1000|8> generating ID_PROT request 0 [ ID HASH N(INITIAL_CONTACT) ] Nov 14 20:00:19 charon 06[NET] <con1000|8> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (100 bytes) Nov 14 20:00:19 charon 04[NET] <con1000|8> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (68 bytes) Nov 14 20:00:19 charon 04[ENC] <con1000|8> parsed ID_PROT response 0 [ ID HASH ] Nov 14 20:00:19 charon 04[IKE] <con1000|8> IKE_SA con1000[8] established between 172.16.5.5[172.16.5.5]...172.16.5.20[172.16.5.20] Nov 14 20:00:19 charon 04[IKE] <con1000|8> scheduling reauthentication in 27958s Nov 14 20:00:19 charon 04[IKE] <con1000|8> maximum IKE_SA lifetime 28498s Nov 14 20:00:19 charon 04[ENC] <con1000|8> generating QUICK_MODE request 4150498363 [ HASH SA No ID ID ] Nov 14 20:00:19 charon 04[NET] <con1000|8> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (172 bytes) Nov 14 20:00:19 charon 04[NET] <con1000|8> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 20:00:19 charon 04[ENC] <con1000|8> parsed INFORMATIONAL_V1 request 1513016128 [ HASH N((24576)) ] Nov 14 20:00:19 charon 04[IKE] <con1000|8> received (24576) notify Nov 14 20:00:19 charon 04[NET] <con1000|8> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (84 bytes) Nov 14 20:00:19 charon 04[ENC] <con1000|8> parsed INFORMATIONAL_V1 request 92455467 [ HASH N(NO_PROP) ] Nov 14 20:00:19 charon 04[IKE] <con1000|8> received NO_PROPOSAL_CHOSEN error notify Nov 14 20:00:29 charon 15[NET] <con1000|8> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 20:00:29 charon 15[ENC] <con1000|8> parsed INFORMATIONAL_V1 request 775993715 [ HASH N(DPD) ] Nov 14 20:00:29 charon 15[ENC] <con1000|8> generating INFORMATIONAL_V1 request 1047640694 [ HASH N(DPD_ACK) ] Nov 14 20:00:29 charon 15[NET] <con1000|8> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 20:00:39 charon 14[NET] <con1000|8> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 20:00:39 charon 14[ENC] <con1000|8> parsed INFORMATIONAL_V1 request 178573301 [ HASH N(DPD) ] Nov 14 20:00:39 charon 14[ENC] <con1000|8> generating INFORMATIONAL_V1 request 2289513989 [ HASH N(DPD_ACK) ] Nov 14 20:00:39 charon 14[NET] <con1000|8> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 20:00:49 charon 11[NET] <con1000|8> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 20:00:49 charon 11[ENC] <con1000|8> parsed INFORMATIONAL_V1 request 1499108937 [ HASH N(DPD) ] Nov 14 20:00:49 charon 11[ENC] <con1000|8> generating INFORMATIONAL_V1 request 4001475511 [ HASH N(DPD_ACK) ] Nov 14 20:00:49 charon 11[NET] <con1000|8> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 20:00:59 charon 07[NET] <con1000|8> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 20:00:59 charon 07[ENC] <con1000|8> parsed INFORMATIONAL_V1 request 2731137206 [ HASH N(DPD) ] Nov 14 20:00:59 charon 07[ENC] <con1000|8> generating INFORMATIONAL_V1 request 1848772477 [ HASH N(DPD_ACK) ] Nov 14 20:00:59 charon 07[NET] <con1000|8> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 20:01:09 charon 06[NET] <con1000|8> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 20:01:09 charon 06[ENC] <con1000|8> parsed INFORMATIONAL_V1 request 1806648137 [ HASH N(DPD) ] Nov 14 20:01:09 charon 06[ENC] <con1000|8> generating INFORMATIONAL_V1 request 3585273924 [ HASH N(DPD_ACK) ] Nov 14 20:01:09 charon 06[NET] <con1000|8> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 20:01:11 charon 13[CFG] rereading secrets Nov 14 20:01:11 charon 13[CFG] loading secrets from '/var/etc/ipsec/ipsec.secrets' Nov 14 20:01:11 charon 13[CFG] loaded IKE secret for %any 172.16.5.20 Nov 14 20:01:11 charon 13[CFG] rereading ca certificates from '/usr/local/etc/ipsec.d/cacerts' Nov 14 20:01:11 charon 13[CFG] rereading aa certificates from '/usr/local/etc/ipsec.d/aacerts' Nov 14 20:01:11 charon 13[CFG] rereading ocsp signer certificates from '/usr/local/etc/ipsec.d/ocspcerts' Nov 14 20:01:11 charon 13[CFG] rereading attribute certificates from '/usr/local/etc/ipsec.d/acerts' Nov 14 20:01:11 charon 13[CFG] rereading crls from '/usr/local/etc/ipsec.d/crls' Nov 14 20:01:11 charon 04[CFG] received stroke: unroute 'bypasslan' Nov 14 20:01:11 ipsec_starter 23741 shunt policy 'bypasslan' uninstalled Nov 14 20:01:11 charon 10[CFG] received stroke: delete connection 'bypasslan' Nov 14 20:01:11 charon 10[CFG] deleted connection 'bypasslan' Nov 14 20:01:11 charon 13[CFG] received stroke: unroute 'con1000' Nov 14 20:01:11 ipsec_starter 23741 configuration 'con1000' unrouted Nov 14 20:01:11 charon 04[CFG] received stroke: delete connection 'con1000' Nov 14 20:01:11 charon 04[CFG] deleted connection 'con1000' Nov 14 20:01:11 charon 10[CFG] received stroke: add connection 'bypasslan' Nov 14 20:01:11 charon 10[CFG] added configuration 'bypasslan' Nov 14 20:01:11 charon 10[CFG] received stroke: route 'bypasslan' Nov 14 20:01:11 ipsec_starter 23741 'bypasslan' shunt PASS policy installed Nov 14 20:01:11 charon 12[CFG] received stroke: add connection 'con1000' Nov 14 20:01:11 charon 12[CFG] added configuration 'con1000' Nov 14 20:01:11 charon 04[CFG] received stroke: route 'con1000' Nov 14 20:01:11 ipsec_starter 23741 'con1000' routed Nov 14 20:01:18 charon 12[NET] <con1000|8> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 20:01:18 charon 12[ENC] <con1000|8> parsed INFORMATIONAL_V1 request 2098246844 [ HASH N(DPD) ] Nov 14 20:01:18 charon 12[ENC] <con1000|8> generating INFORMATIONAL_V1 request 3652794566 [ HASH N(DPD_ACK) ] Nov 14 20:01:18 charon 12[NET] <con1000|8> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 20:01:29 charon 12[NET] <con1000|8> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 20:01:29 charon 12[ENC] <con1000|8> parsed INFORMATIONAL_V1 request 97097006 [ HASH N(DPD) ] Nov 14 20:01:29 charon 12[ENC] <con1000|8> generating INFORMATIONAL_V1 request 2483709523 [ HASH N(DPD_ACK) ] Nov 14 20:01:29 charon 12[NET] <con1000|8> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes -
@mr-pine said in Site to Site IPsec tunnel with Cisco and pfsense:
Nov 14 20:00:19 charon 04[IKE] <con1000|8> received NO_PROPOSAL_CHOSEN error notify
The other side doesn't like something. The logs over there will tell you what.
https://www.netgate.com/docs/pfsense/vpn/ipsec/ipsec-troubleshooting.html
https://www.netgate.com/docs/pfsense/vpn/ipsec/ipsec-troubleshooting.html#phase-2-encryption-algorithm-mismatch
If you can coerce the other side to initiate, you will get more information. try to ping across it from there and look at the logs again. IPsec intentionally gives the initiator as little information as possible from the responder for obvious reasons.
-
TNX ,
All my cisco config done according to the doc. unfortunately I am not cisco man!*Mar 9 04:54:02.222: ISAKMP:(2027):purging node 145565563 *Mar 9 04:54:11.268: ISAKMP: set new node -1069493972 to QM_IDLE *Mar 9 04:54:11.268: ISAKMP:(2027):Sending NOTIFY DPD/R_U_THERE protocol 1 spi 2231739072, message ID = 3225473324 *Mar 9 04:54:11.268: ISAKMP:(2027): seq. no 0x1AA04C95 *Mar 9 04:54:11.268: ISAKMP:(2027): sending packet to 172.16.5.5 my_port 500 peer_port 500 (R) QM_IDLE *Mar 9 04:54:11.268: ISAKMP:(2027):Sending an IKE IPv4 Packet. *Mar 9 04:54:11.268: ISAKMP:(2027):purging node -1069493972 *Mar 9 04:54:11.268: ISAKMP:(2027):Input = IKE_MESG_FROM_TIMER, IKE_TIMER_IM_ALIVE *Mar 9 04:54:11.268: ISAKMP:(2027):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE *Mar 9 04:54:11.320: ISAKMP (2027): received packet from 172.16.5.5 dport 500 sport 500 Global (R) QM_IDLE *Mar 9 04:54:11.320: ISAKMP: set new node -145323109 to QM_IDLE *Mar 9 04:54:11.324: ISAKMP:(2027): processing HASH payload. message ID = 4149644187 *Mar 9 04:54:11.324: ISAKMP:(2027): processing NOTIFY DPD/R_U_THERE_ACK protocol 1 spi 0, message ID = 4149644187, sa = 0x85CE60CC *Mar 9 04:54:11.324: ISAKMP:(2027): DPD/R_U_THERE_ACK received from peer 172.16.5.5, sequence 0x1AA04C95 *Mar 9 04:54:11.324: ISAKMP:(2027):deleting node -145323109 error FALSE reason "Informational (in) state 1" *Mar 9 04:54:11.324: ISAKMP:(2027):Input = IKE_MESG_FROM_PEER, IKE_INFO_NOTIFY *Mar 9 04:54:11.324: ISAKMP:(2027):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE *Mar 9 04:54:12.236: ISAKMP:(202 -
Don't see anything about the P2 there. If you post both sides' P2 settings we might be able to see the problem.
-
Here is my cisco config:
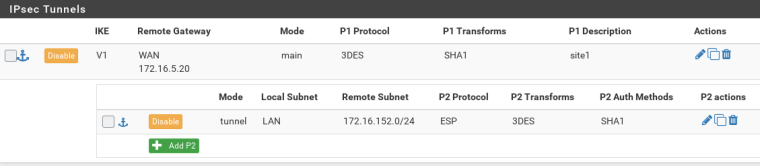
crypto isakmp policy 10 encr 3des authentication pre-share group 2 lifetime 4000 crypto isakmp key mysecret address 172.16.5.5 no-xauth crypto isakmp keepalive 10 periodic ! ! crypto ipsec transform-set 3DES-SHA esp-3des esp-sha-hmac ! ! crypto map PFSVPN 15 ipsec-isakmp ! Incomplete set peer 172.16.5.5 set transform-set 3DES-SHA set pfs group2 match address 100 ! ! ip nat inside source route-map NONAT interface Dialer1 overload ip nat inside source route-map nonat interface Virtual-PPP1 overload ip route 0.0.0.0 0.0.0.0 Dialer1 permanent ip route 172.16.5.5 255.255.255.255 Dialer1 ! access-list 10 permit 172.16.0.0 0.0.255.255 access-list 10 permit any no cdp run ! ! ! route-map nonat permit 10 match ip address 110 !pf P2 settins:
-
Where's access list 100 for the IPsec traffic selector? The Cisco is telling you that IPsec config is
!Incomplete.Where's access list 110 for the NAT bypass?
Is PFS group set to 2 in the Phase 2 on pfSense?
-
@mr-pine said in Site to Site IPsec tunnel with Cisco and pfsense:
crypto map PFSVPN
Oh my god. sorry. PFS group was wrong! as you said I set to 2. I don't know how did you find!?
I also correct my cisco to this:
encr 3des authentication pre-share group 2 lifetime 4000 crypto isakmp key mysecret address 172.16.5.5 no-xauth crypto isakmp keepalive 10 periodic ! ! crypto ipsec transform-set 3DES-SHA esp-3des esp-sha-hmac ! ! crypto map PFSVPN 15 ipsec-isakmp set peer 172.16.5.5 set transform-set 3DES-SHA set pfs group2 match address 100 ! ! ! ! ip forward-protocol nd no ip http server no ip http secure-server ! ip nat inside source route-map NONAT interface Dialer1 overload ip route 0.0.0.0 0.0.0.0 Dialer1 permanent ip route 172.16.5.5 255.255.255.255 Dialer1 ! access-list 10 permit 172.16.0.0 0.0.255.255 access-list 10 permit any access-list 100 permit ip 172.16.152.0 0.0.0.255 172.16.0.0 0.0.0.255 access-list 100 permit ip 172.16.0.0 0.0.255.255 172.16.152.0 0.0.0.255 access-list 110 deny ip 172.16.152.0 0.0.0.255 172.16.0.0 0.0.255.255 access-list 110 permit ip 172.16.152.0 0.0.0.255 any no cdp run ! ! ! route-map NONAT permit 10 match ip address 110 ! !now got new logs on cisco:
*Mar 9 05:31:22.998: map_db_find_best did not find matching map *Mar 9 05:31:22.998: IPSEC(ipsec_process_proposal): proxy identities not supported *Mar 9 05:31:22.998: IPSEC(validate_proposal_request): proposal part #1 *Mar 9 05:31:22.998: IPSEC(validate_proposal_request): proposal part #1, (key eng. msg.) INBOUND local= 172.16.5.20:0, remote= 172.16.5.5:0, local_proxy= 172.16.152.0/255.255.255.0/0/0 (type=4), remote_proxy= 172.16.111.0/255.255.255.0/0/0 (type=4), protocol= ESP, transform= NONE (Tunnel), lifedur= 0s and 0kb, spi= 0x0(0), conn_id= 0, keysize= 128, flags= 0x0 *Mar 9 05:31:22.998: Crypto mapdb : proxy_match src addr : 172.16.152.0 dst addr : 172.16.111.0 protocol : 0 src port : 0 dst port : 0 *Mar 9 05:31:22.998: Crypto mapdb : proxy_match src addr : 172.16.152.0 dst addr : 172.16.111.0 protocol : 0 src port : 0 dst port : 0 *Mar 9 05:31:22.998: Crypto mapdb : proxy_match src addr : 172.16.152.0 dst addr : 172.16.111.0 protocol : 0 src port : 0 dst port : 0 *Mar 9 05:31:22.998: map_db_find_best did not find matching map *Mar 9 05:31:22.998: IPSEC(ipsec_process_proposal): proxy identities not supported -
OK that's great but what is pfSense showing now?
-
Nov 14 21:34:35 charon 07[NET] <con1000|24> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 21:34:45 charon 07[IKE] <con1000|24> sending DPD request Nov 14 21:34:45 charon 07[ENC] <con1000|24> generating INFORMATIONAL_V1 request 3757439349 [ HASH N(DPD) ] Nov 14 21:34:45 charon 07[NET] <con1000|24> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 21:34:45 charon 07[NET] <con1000|24> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 21:34:45 charon 07[ENC] <con1000|24> parsed INFORMATIONAL_V1 request 2314329083 [ HASH N(DPD_ACK) ] Nov 14 21:34:45 charon 07[NET] <con1000|24> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 21:34:45 charon 07[ENC] <con1000|24> parsed INFORMATIONAL_V1 request 453303260 [ HASH N(DPD) ] Nov 14 21:34:45 charon 07[ENC] <con1000|24> generating INFORMATIONAL_V1 request 408573435 [ HASH N(DPD_ACK) ] Nov 14 21:34:45 charon 07[NET] <con1000|24> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 21:34:55 charon 07[IKE] <con1000|24> sending DPD request Nov 14 21:34:55 charon 07[ENC] <con1000|24> generating INFORMATIONAL_V1 request 3451049163 [ HASH N(DPD) ] Nov 14 21:34:55 charon 07[NET] <con1000|24> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 21:34:55 charon 07[NET] <con1000|24> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 21:34:55 charon 07[ENC] <con1000|24> parsed INFORMATIONAL_V1 request 2642134501 [ HASH N(DPD_ACK) ] Nov 14 21:34:55 charon 07[NET] <con1000|24> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 21:34:55 charon 07[ENC] <con1000|24> parsed INFORMATIONAL_V1 request 3569179544 [ HASH N(DPD) ] Nov 14 21:34:55 charon 07[ENC] <con1000|24> generating INFORMATIONAL_V1 request 1472256830 [ HASH N(DPD_ACK) ] Nov 14 21:34:55 charon 07[NET] <con1000|24> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 21:35:05 charon 09[NET] <con1000|24> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 21:35:05 charon 09[ENC] <con1000|24> parsed INFORMATIONAL_V1 request 672897385 [ HASH N(DPD) ] Nov 14 21:35:05 charon 09[ENC] <con1000|24> generating INFORMATIONAL_V1 request 1924986738 [ HASH N(DPD_ACK) ] Nov 14 21:35:05 charon 09[NET] <con1000|24> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 21:35:09 charon 06[CFG] received stroke: terminate 'con1000' Nov 14 21:35:09 charon 15[IKE] <con1000|24> deleting IKE_SA con1000[24] between 172.16.5.5[172.16.5.5]...172.16.5.20[172.16.5.20] Nov 14 21:35:09 charon 15[IKE] <con1000|24> sending DELETE for IKE_SA con1000[24] Nov 14 21:35:09 charon 15[ENC] <con1000|24> generating INFORMATIONAL_V1 request 1137989583 [ HASH D ] Nov 14 21:35:09 charon 15[NET] <con1000|24> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (84 bytes) Nov 14 21:35:10 charon 06[CFG] received stroke: terminate 'con1000' Nov 14 21:35:10 charon 06[CFG] no IKE_SA named 'con1000' found Nov 14 21:35:10 charon 11[CFG] received stroke: initiate 'con1000' Nov 14 21:35:10 charon 06[IKE] <con1000|25> initiating Main Mode IKE_SA con1000[25] to 172.16.5.20 Nov 14 21:35:10 charon 06[ENC] <con1000|25> generating ID_PROT request 0 [ SA V V V V V ] Nov 14 21:35:10 charon 06[NET] <con1000|25> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (176 bytes) Nov 14 21:35:10 charon 06[NET] <con1000|25> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (100 bytes) Nov 14 21:35:10 charon 06[ENC] <con1000|25> parsed ID_PROT response 0 [ SA V ] Nov 14 21:35:10 charon 06[IKE] <con1000|25> received NAT-T (RFC 3947) vendor ID Nov 14 21:35:10 charon 06[ENC] <con1000|25> generating ID_PROT request 0 [ KE No NAT-D NAT-D ] Nov 14 21:35:10 charon 06[NET] <con1000|25> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (244 bytes) Nov 14 21:35:10 charon 06[NET] <con1000|25> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (304 bytes) Nov 14 21:35:10 charon 06[ENC] <con1000|25> parsed ID_PROT response 0 [ KE No V V V V NAT-D NAT-D ] Nov 14 21:35:10 charon 06[IKE] <con1000|25> received Cisco Unity vendor ID Nov 14 21:35:10 charon 06[IKE] <con1000|25> received DPD vendor ID Nov 14 21:35:10 charon 06[ENC] <con1000|25> received unknown vendor ID: 07:a1:37:8b:fb:24:a7:73:33:0b:c6:e6:1b:71:7e:90 Nov 14 21:35:10 charon 06[IKE] <con1000|25> received XAuth vendor ID Nov 14 21:35:10 charon 06[ENC] <con1000|25> generating ID_PROT request 0 [ ID HASH N(INITIAL_CONTACT) ] Nov 14 21:35:10 charon 06[NET] <con1000|25> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (100 bytes) Nov 14 21:35:10 charon 05[NET] <con1000|25> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (68 bytes) Nov 14 21:35:10 charon 05[ENC] <con1000|25> parsed ID_PROT response 0 [ ID HASH ] Nov 14 21:35:10 charon 05[IKE] <con1000|25> IKE_SA con1000[25] established between 172.16.5.5[172.16.5.5]...172.16.5.20[172.16.5.20] Nov 14 21:35:10 charon 05[IKE] <con1000|25> scheduling reauthentication in 28008s Nov 14 21:35:10 charon 05[IKE] <con1000|25> maximum IKE_SA lifetime 28548s Nov 14 21:35:10 charon 05[ENC] <con1000|25> generating QUICK_MODE request 1619982291 [ HASH SA No KE ID ID ] Nov 14 21:35:10 charon 05[NET] <con1000|25> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (380 bytes) Nov 14 21:35:10 charon 05[NET] <con1000|25> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 21:35:10 charon 05[ENC] <con1000|25> parsed INFORMATIONAL_V1 request 4054978725 [ HASH N((24576)) ] Nov 14 21:35:10 charon 05[IKE] <con1000|25> received (24576) notify Nov 14 21:35:10 charon 05[NET] <con1000|25> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (84 bytes) Nov 14 21:35:10 charon 05[ENC] <con1000|25> parsed INFORMATIONAL_V1 request 3129956325 [ HASH N(NO_PROP) ] Nov 14 21:35:10 charon 05[IKE] <con1000|25> received NO_PROPOSAL_CHOSEN error notify Nov 14 21:35:20 charon 13[IKE] <con1000|25> sending DPD request Nov 14 21:35:20 charon 13[ENC] <con1000|25> generating INFORMATIONAL_V1 request 2706628016 [ HASH N(DPD) ] Nov 14 21:35:20 charon 13[NET] <con1000|25> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 21:35:20 charon 13[NET] <con1000|25> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 21:35:20 charon 13[ENC] <con1000|25> parsed INFORMATIONAL_V1 request 2813541667 [ HASH N(DPD) ] Nov 14 21:35:20 charon 13[ENC] <con1000|25> generating INFORMATIONAL_V1 request 1538694707 [ HASH N(DPD_ACK) ] Nov 14 21:35:20 charon 13[NET] <con1000|25> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 21:35:20 charon 13[NET] <con1000|25> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 21:35:20 charon 13[ENC] <con1000|25> parsed INFORMATIONAL_V1 request 444822346 [ HASH N(DPD_ACK) ] Nov 14 21:35:30 charon 13[NET] <con1000|25> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 21:35:30 charon 13[ENC] <con1000|25> parsed INFORMATIONAL_V1 request 3486885508 [ HASH N(DPD) ] Nov 14 21:35:30 charon 13[ENC] <con1000|25> generating INFORMATIONAL_V1 request 2522299192 [ HASH N(DPD_ACK) ] Nov 14 21:35:30 charon 13[NET] <con1000|25> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 21:35:40 charon 13[NET] <con1000|25> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 21:35:40 charon 13[ENC] <con1000|25> parsed INFORMATIONAL_V1 request 593879169 [ HASH N(DPD) ] Nov 14 21:35:40 charon 13[ENC] <con1000|25> generating INFORMATIONAL_V1 request 4184589574 [ HASH N(DPD_ACK) ] Nov 14 21:35:40 charon 13[NET] <con1000|25> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 21:35:49 charon 13[NET] <con1000|25> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 21:35:49 charon 13[ENC] <con1000|25> parsed INFORMATIONAL_V1 request 891356160 [ HASH N(DPD) ] Nov 14 21:35:49 charon 13[ENC] <con1000|25> generating INFORMATIONAL_V1 request 922756253 [ HASH N(DPD_ACK) ] Nov 14 21:35:49 charon 13[NET] <con1000|25> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 21:35:59 charon 10[NET] <con1000|25> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 21:35:59 charon 10[ENC] <con1000|25> parsed INFORMATIONAL_V1 request 1675134373 [ HASH N(DPD) ] Nov 14 21:35:59 charon 10[ENC] <con1000|25> generating INFORMATIONAL_V1 request 280815738 [ HASH N(DPD_ACK) ] Nov 14 21:35:59 charon 10[NET] <con1000|25> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 21:36:05 charon 08[CFG] rereading secrets Nov 14 21:36:05 charon 08[CFG] loading secrets from '/var/etc/ipsec/ipsec.secrets' Nov 14 21:36:05 charon 08[CFG] loaded IKE secret for %any 172.16.5.20 Nov 14 21:36:05 charon 08[CFG] rereading ca certificates from '/usr/local/etc/ipsec.d/cacerts' Nov 14 21:36:05 charon 08[CFG] rereading aa certificates from '/usr/local/etc/ipsec.d/aacerts' Nov 14 21:36:05 charon 08[CFG] rereading ocsp signer certificates from '/usr/local/etc/ipsec.d/ocspcerts' Nov 14 21:36:05 charon 08[CFG] rereading attribute certificates from '/usr/local/etc/ipsec.d/acerts' Nov 14 21:36:05 charon 08[CFG] rereading crls from '/usr/local/etc/ipsec.d/crls' Nov 14 21:36:05 charon 07[CFG] received stroke: unroute 'bypasslan' Nov 14 21:36:05 ipsec_starter 23741 shunt policy 'bypasslan' uninstalled Nov 14 21:36:05 charon 10[CFG] received stroke: delete connection 'bypasslan' Nov 14 21:36:05 charon 10[CFG] deleted connection 'bypasslan' Nov 14 21:36:05 charon 07[CFG] received stroke: unroute 'con1000' Nov 14 21:36:05 ipsec_starter 23741 configuration 'con1000' unrouted Nov 14 21:36:05 charon 10[CFG] received stroke: delete connection 'con1000' Nov 14 21:36:05 charon 10[CFG] deleted connection 'con1000' Nov 14 21:36:05 charon 04[CFG] received stroke: add connection 'bypasslan' Nov 14 21:36:05 charon 04[CFG] added configuration 'bypasslan' Nov 14 21:36:05 charon 10[CFG] received stroke: route 'bypasslan' Nov 14 21:36:05 ipsec_starter 23741 'bypasslan' shunt PASS policy installed Nov 14 21:36:05 charon 04[CFG] received stroke: add connection 'con1000' Nov 14 21:36:05 charon 04[CFG] added configuration 'con1000' Nov 14 21:36:05 charon 10[CFG] received stroke: route 'con1000' Nov 14 21:36:05 ipsec_starter 23741 'con1000' routed Nov 14 21:36:09 charon 10[NET] <con1000|25> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 21:36:09 charon 10[ENC] <con1000|25> parsed INFORMATIONAL_V1 request 3532946353 [ HASH N(DPD) ] Nov 14 21:36:09 charon 10[ENC] <con1000|25> generating INFORMATIONAL_V1 request 453231053 [ HASH N(DPD_ACK) ] Nov 14 21:36:09 charon 10[NET] <con1000|25> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 21:36:18 charon 10[NET] <con1000|25> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 21:36:18 charon 10[ENC] <con1000|25> parsed INFORMATIONAL_V1 request 1660378267 [ HASH N(DPD) ] Nov 14 21:36:18 charon 10[ENC] <con1000|25> generating INFORMATIONAL_V1 request 2731222186 [ HASH N(DPD_ACK) ] Nov 14 21:36:18 charon 10[NET] <con1000|25> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes) Nov 14 21:36:28 charon 15[NET] <con1000|25> received packet: from 172.16.5.20[500] to 172.16.5.5[500] (92 bytes) Nov 14 21:36:28 charon 15[ENC] <con1000|25> parsed INFORMATIONAL_V1 request 3531350043 [ HASH N(DPD) ] Nov 14 21:36:28 charon 15[ENC] <con1000|25> generating INFORMATIONAL_V1 request 1091241482 [ HASH N(DPD_ACK) ] Nov 14 21:36:28 charon 15[NET] <con1000|25> sending packet: from 172.16.5.5[500] to 172.16.5.20[500] (92 bytes)cisco log:
*Mar 9 06:07:19.143: ISAKMP (2038): received packet from 172.16.5.5 dport 500 sport 500 Global (R) QM_IDLE *Mar 9 06:07:19.143: ISAKMP: set new node 1619982291 to QM_IDLE *Mar 9 06:07:19.147: ISAKMP:(2038): processing HASH payload. message ID = 1619982291 *Mar 9 06:07:19.147: ISAKMP:(2038): processing SA payload. message ID = 1619982291 *Mar 9 06:07:19.147: ISAKMP:(2038):Checking IPSec proposal 0 *Mar 9 06:07:19.147: ISAKMP: transform 1, ESP_AES *Mar 9 06:07:19.147: ISAKMP: attributes in transform: *Mar 9 06:07:19.147: ISAKMP: key length is 256 *Mar 9 06:07:19.147: ISAKMP: authenticator is HMAC-SHA *Mar 9 06:07:19.147: ISAKMP: group is 2 *Mar 9 06:07:19.147: ISAKMP: encaps is 1 (Tunnel) *Mar 9 06:07:19.147: ISAKMP: SA life type in seconds *Mar 9 06:07:19.147: ISAKMP: SA life duration (basic) of 3600 *Mar 9 06:07:19.147: ISAKMP:(2038):atts are acceptable. *Mar 9 06:07:19.147: ISAKMP:(2038):Checking IPSec proposal 0 *Mar 9 06:07:19.147: ISAKMP: transform 2, ESP_AES *Mar 9 06:07:19.147: ISAKMP: attributes in transform: *Mar 9 06:07:19.147: ISAKMP: key length is 192 *Mar 9 06:07:19.147: ISAKMP: authenticator is HMAC-SHA *Mar 9 06:07:19.147: ISAKMP: group is 2 *Mar 9 06:07:19.147: ISAKMP: encaps is 1 (Tunnel) *Mar 9 06:07:19.147: ISAKMP: SA life type in seconds *Mar 9 06:07:19.147: ISAKMP: SA life duration (basic) of 3600 *Mar 9 06:07:19.147: ISAKMP:(2038):atts are acceptable. *Mar 9 06:07:19.147: ISAKMP:(2038):Checking IPSec proposal 0 *Mar 9 06:07:19.147: ISAKMP: transform 3, ESP_AES *Mar 9 06:07:19.147: ISAKMP: attributes in transform: *Mar 9 06:07:19.147: ISAKMP: key length is 128 *Mar 9 06:07:19.151: ISAKMP: authenticator is HMAC-SHA *Mar 9 06:07:19.151: ISAKMP: group is 2 *Mar 9 06:07:19.151: ISAKMP: encaps is 1 (Tunnel) *Mar 9 06:07:19.151: ISAKMP: SA life type in seconds *Mar 9 06:07:19.151: ISAKMP: SA life duration (basic) of 3600 *Mar 9 06:07:19.151: ISAKMP:(2038):atts are acceptable. *Mar 9 06:07:19.151: IPSEC(validate_proposal_request): proposal part #1 *Mar 9 06:07:19.151: IPSEC(validate_proposal_request): proposal part #1, (key eng. msg.) INBOUND local= 172.16.5.20:0, remote= 172.16.5.5:0, local_proxy= 172.16.152.0/255.255.255.0/0/0 (type=4), remote_proxy= 172.16.0.0/255.255.0.0/0/0 (type=4), protocol= ESP, transform= NONE (Tunnel), lifedur= 0s and 0kb, spi= 0x0(0), conn_id= 0, keysize= 256, flags= 0x0 *Mar 9 06:07:19.151: Crypto mapdb : proxy_match src addr : 172.16.152.0 dst addr : 172.16.0.0 protocol : 0 src port : 0 dst port : 0 *Mar 9 06:07:19.151: Crypto mapdb : proxy_match src addr : 172.16.152.0 dst addr : 172.16.0.0 protocol : 0 src port : 0 dst port : 0 *Mar 9 06:07:19.151: Crypto mapdb : proxy_match src addr : 172.16.152.0 dst addr : 172.16.0.0 protocol : 0 src port : 0 dst port : 0 *Mar 9 06:07:19.151: map_db_find_best did not find matching map *Mar 9 06:07:19.151: IPSEC(ipsec_process_proposal): proxy identities not supported *Mar 9 06:07:19.151: ISAKMP:(2038): IPSec policy invalidated proposal with error 32 *Mar 9 06:07:19.151: IPSEC(validate_proposal_request): proposal part #1 *Mar 9 06:07:19.151: IPSEC(validate_proposal_request): proposal part #1, (key eng. msg.) INBOUND local= 172.16.5.20:0, remote= 172.16.5.5:0, local_proxy= 172.16.152.0/255.255.255.0/0/0 (type=4), remote_proxy= 172.16.0.0/255.255.0.0/0/0 (type=4), protocol= ESP, transform= NONE (Tunnel), lifedur= 0s and 0kb, spi= 0x0(0), conn_id= 0, keysize= 192, flags= 0x0 *Mar 9 06:07:19.151: Crypto mapdb : proxy_match src addr : 172.16.152.0 dst addr : 172.16.0.0 protocol : 0 src port : 0 dst port : 0 *Mar 9 06:07:19.155: Crypto mapdb : proxy_match src addr : 172.16.152.0 dst addr : 172.16.0.0 protocol : 0 src port : 0 dst port : 0 *Mar 9 06:07:19.155: Crypto mapdb : proxy_match src addr : 172.16.152.0 dst addr : 172.16.0.0 protocol : 0 src port : 0 dst port : 0 *Mar 9 06:07:19.155: map_db_find_best did not find matching map *Mar 9 06:07:19.155: IPSEC(ipsec_process_proposal): proxy identities not supported *Mar 9 06:07:19.155: ISAKMP:(2038): IPSec policy invalidated proposal with error 32 *Mar 9 06:07:19.155: IPSEC(validate_proposal_request): proposal part #1 *Mar 9 06:07:19.155: IPSEC(validate_proposal_request): proposal part #1, (key eng. msg.) INBOUND local= 172.16.5.20:0, remote= 172.16.5.5:0, local_proxy= 172.16.152.0/255.255.255.0/0/0 (type=4), remote_proxy= 172.16.0.0/255.255.0.0/0/0 (type=4), protocol= ESP, transform= NONE (Tunnel), lifedur= 0s and 0kb, spi= 0x0(0), conn_id= 0, keysize= 128, flags= 0x0 *Mar 9 06:07:19.155: Crypto mapdb : proxy_match src addr : 172.16.152.0 dst addr : 172.16.0.0 protocol : 0 src port : 0 dst port : 0 *Mar 9 06:07:19.155: Crypto mapdb : proxy_match src addr : 172.16.152.0 dst addr : 172.16.0.0 protocol : 0 src port : 0 dst port : 0 *Mar 9 06:07:19.155: Crypto mapdb : proxy_match src addr : 172.16.152.0 dst addr : 172.16.0.0 protocol : 0 src port : 0 dst port : 0 *Mar 9 06:07:19.155: map_db_find_best did not find matching map *Mar 9 06:07:19.155: IPSEC(ipsec_process_proposal): proxy identities not supported *Mar 9 06:07:19.155: ISAKMP:(2038): IPSec policy invalidated proposal with error 32 *Mar 9 06:07:19.155: ISAKMP:(2038): phase 2 SA policy not acceptable! (local 172.16.5.20 remote 172.16.5.5) *Mar 9 06:07:19.155: ISAKMP: set new node -1165010971 to QM_IDLE *Mar 9 06:07:19.155: ISAKMP:(2038):Sending NOTIFY PROPOSAL_NOT_CHOSEN protocol 3 spi 2231737992, message ID = 3129956325 *Mar 9 06:07:19.159: ISAKMP:(2038): sending packet to 172.16.5.5 my_port 500 peer_port 500 (R) QM_IDLE *Mar 9 06:07:19.159: ISAKMP:(2038):Sending an IKE IPv4 Packet. *Mar 9 06:07:19.159: ISAKMP:(2038):purging node -1165010971 *Mar 9 06:07:19.159: ISAKMP:(2038):deleting node 1619982291 error TRUE reason "QM rejected" *Mar 9 06:07:19.159: ISAKMP:(2038):Node 1619982291, Input = IKE_MESG_FROM_PEER, IKE_QM_EXCH *Mar 9 06:07:19.159: ISAKMP:(2038):Old State = IKE_QM_READY New State = IKE_QM_READY *Mar 9 06:07:23.904: ISAKMP:(2037):purging node 967766711 *Mar 9 06:07:29.097: ISAKMP: set new node -1481425629 to QM_IDLE *Mar 9 06:07:29.097: ISAKMP:(2038):Sending NOTIFY DPD/R_U_THERE protocol 1 spi 2231739072, message ID = 2813541667 *Mar 9 06:07:29.097: ISAKMP:(2038): seq. no 0x4BDC3AFD *Mar 9 06:07:29.097: ISAKMP:(2038): sending packet to 172.16.5.5 my_port 500 peer_port 500 (R) QM_IDLE *Mar 9 06:07:29.097: ISAKMP:(2038):Sending an IKE IPv4 Packet. *Mar 9 06:07:29.097: ISAKMP:(2038):purging node -1481425629 *Mar 9 06:07:29.097: ISAKMP:(2038):Input = IKE_MESG_FROM_TIMER, IKE_TIMER_IM_ALIVE *Mar 9 06:07:29.097: ISAKMP:(2038):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE *Mar 9 06:07:29.141: ISAKMP (2038): received packet from 172.16.5.5 dport 500 sport 500 Global (R) QM_IDLE *Mar 9 06:07:29.141: ISAKMP: set new node -1588339280 to QM_IDLE *Mar 9 06:07:29.141: ISAKMP:(2038): processing HASH payload. message ID = 2706628016 *Mar 9 06:07:29.141: ISAKMP:(2038): processing NOTIFY DPD/R_U_THERE protocol 1 spi 0, message ID = 2706628016, sa = 0x85D0E0A0 *Mar 9 06:07:29.141: ISAKMP:(2038):deleting node -1588339280 error FALSE reason "Informational (in) state 1" *Mar 9 06:07:29.141: ISAKMP:(2038):Input = IKE_MESG_FROM_PEER, IKE_INFO_NOTIFY *Mar 9 06:07:29.141: ISAKMP:(2038):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE *Mar 9 06:07:29.145: ISAKMP:(2038):DPD/R_U_THERE received from peer 172.16.5.5, sequence 0x18869FBA *Mar 9 06:07:29.145: ISAKMP: set new node 444822346 to QM_IDLE *Mar 9 06:07:29.145: ISAKMP:(2038):Sending NOTIFY DPD/R_U_THERE_ACK protocol 1 spi 2231739112, message ID = 444822346 *Mar 9 06:07:29.145: ISAKMP:(2038): seq. no 0x18869FBA *Mar 9 06:07:29.145: ISAKMP:(2038): sending packet to 172.16.5.5 my_port 500 peer_port 500 (R) QM_IDLE *Mar 9 06:07:29.145: ISAKMP:(2038):Sending an IKE IPv4 Packet. *Mar 9 06:07:29.145: ISAKMP:(2038):purging node 444822346 *Mar 9 06:07:29.149: ISAKMP:(2038):Input = IKE_MESG_FROM_PEER, IKE_MESG_KEEP_ALIVE *Mar 9 06:07:29.149: ISAKMP:(2038):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE *Mar 9 06:07:29.149: ISAKMP (2038): received packet from 172.16.5.5 dport 500 sport 500 Global (R) QM_IDLE *Mar 9 06:07:29.149: ISAKMP: set new node 1538694707 to QM_IDLE *Mar 9 06:07:29.149: ISAKMP:(2038): processing HASH payload. message ID = 1538694707 *Mar 9 06:07:29.149: ISAKMP:(2038): processing NOTIFY DPD/R_U_THERE_ACK protocol 1 spi 0, message ID = 1538694707, sa = 0x85D0E0A0 *Mar 9 06:07:29.149: ISAKMP:(2038): DPD/R_U_THERE_ACK received from peer 172.16.5.5, sequence 0x4BDC3AFD *Mar 9 06:07:29.153: ISAKMP:(2038):deleting node 1538694707 error FALSE reason "Informational (in) state 1" *Mar 9 06:07:29.153: ISAKMP:(2038):Input = IKE_MESG_FROM_PEER, IKE_INFO_NOTIFY *Mar 9 06:07:29.153: ISAKMP:(2038):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE *Mar 9 06:07:33.718: ISAKMP:(2037):purging node 1956731654 *Mar 9 06:07:33.910: ISAKMP:(2037):purging node -745430556 *Mar 9 06:07:38.707: ISAKMP: set new node -808081788 to QM_IDLE *Mar 9 06:07:38.707: ISAKMP:(2038):Sending NOTIFY DPD/R_U_THERE protocol 1 spi 2231739072, message ID = 3486885508 *Mar 9 06:07:38.707: ISAKMP:(2038): seq. no 0x4BDC3AFE *Mar 9 06:07:38.707: ISAKMP:(2038): sending packet to 172.16.5.5 my_port 500 peer_port 500 (R) QM_IDLE *Mar 9 06:07:38.707: ISAKMP:(2038):Sending an IKE IPv4 Packet. *Mar 9 06:07:38.707: ISAKMP:(2038):purging node -808081788 *Mar 9 06:07:38.707: ISAKMP:(2038):Input = IKE_MESG_FROM_TIMER, IKE_TIMER_IM_ALIVE *Mar 9 06:07:38.707: ISAKMP:(2038):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE *Mar 9 06:07:38.759: ISAKMP (2038): received packet from 172.16.5.5 dport 500 sport 500 Global (R) QM_IDLE *Mar 9 06:07:38.759: ISAKMP: set new node -1772668104 to QM_IDLE *Mar 9 06:07:38.759: ISAKMP:(2038): processing HASH payload. message ID = 2522299192 *Mar 9 06:07:38.759: ISAKMP:(2038): processing NOTIFY DPD/R_U_THERE_ACK protocol 1 spi 0, message ID = 2522299192, sa = 0x85D0E0A0 *Mar 9 06:07:38.759: ISAKMP:(2038): DPD/R_U_THERE_ACK received from peer 172.16.5.5, sequence 0x4BDC3AFE *Mar 9 06:07:38.759: ISAKMP:(2038):deleting node -1772668104 error FALSE reason "Informational (in) state 1" *Mar 9 06:07:38.759: ISAKMP:(2038):Input = IKE_MESG_FROM_PEER, IKE_INFO_NOTIFY *Mar 9 06:07:38.759: ISAKMP:(2038):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE *Mar 9 06:07:43.724: ISAKMP:(2037):purging node -537527947 *Mar 9 06:07:43.848: ISAKMP:(2037):purging node 408573435 *Mar 9 06:07:48.429: ISAKMP: set new node 593879169 to QM_IDLE *Mar 9 06:07:48.429: ISAKMP:(2038):Sending NOTIFY DPD/R_U_THERE protocol 1 spi 2231739072, message ID = 593879169 -
Oh, Its works!!!!
I adjust this acl:access-list 100 permit ip 172.16.0.0 0.0.255.255 172.16.152.0 0.0.0.255 access-list 100 permit ip 172.16.152.0 0.0.0.255 172.16.0.0 0.0.255.255now I can 172.16.152.1 from pf box, but can not see pf lan from cisco,
new cisco log :Mar 9 07:06:07.622: ISAKMP (2051): received packet from 172.16.5.5 dport 500 sport 500 Global (R) QM_IDLE *Mar 9 07:06:07.622: ISAKMP: set new node -1294467565 to QM_IDLE *Mar 9 07:06:07.622: ISAKMP:(2051): processing HASH payload. message ID = 3000499731 *Mar 9 07:06:07.622: ISAKMP:(2051): processing DELETE payload. message ID = 3000499731 *Mar 9 07:06:07.626: ISAKMP:(2051):peer does not do paranoid keepalives. *Mar 9 07:06:07.626: ISAKMP:(2051):deleting node -1294467565 error FALSE reason "Informational (in) state 1" *Mar 9 07:06:07.626: IPSEC(key_engine): got a queue event with 1 KMI message(s) *Mar 9 07:06:07.626: IPSEC(key_engine_delete_sas): rec'd delete notify from ISAKMP *Mar 9 07:06:07.626: IPSEC(key_engine_delete_sas): delete SA with spi 0xC50D9769 proto 50 for 172.16.5.5 *Mar 9 07:06:07.626: IPSEC(delete_sa): deleting SA, (sa) sa_dest= 172.16.5.20, sa_proto= 50, sa_spi= 0x1EF2C2A8(519226024), sa_trans= esp-3des esp-sha-hmac , sa_conn_id= 3 sa_lifetime(k/sec)= (4417323/3600), (identity) local= 172.16.5.20:0, remote= 172.16.5.5:0, local_proxy= 172.16.152.0/255.255.255.0/0/0 (type=4), remote_proxy= 172.16.0.0/255.255.0.0/0/0 (type=4) *Mar 9 07:06:07.626: IPSEC(update_current_outbound_sa): updated peer 172.16.5.5 current outbound sa to SPI 0 *Mar 9 07:06:07.626: IPSEC(delete_sa): deleting SA, (sa) sa_dest= 172.16.5.5, sa_proto= 50, sa_spi= 0xC50D9769(3306002281), sa_trans= esp-3des esp-sha-hmac , sa_conn_id= 4 sa_lifetime(k/sec)= (4417323/3600), (identity) local= 172.16.5.20:0, remote= 172.16.5.5:0, local_proxy= 172.16.152.0/255.255.255.0/0/0 (type=4), remote_proxy= 172.16.0.0/255.255.0.0/0/0 (type=4) *Mar 9 07:06:07.630: ISAKMP (2051): received packet from 172.16.5.5 dport 500 sport 500 Global (R) QM_IDLE *Mar 9 07:06:07.630: ISAKMP: set new node 123795513 to QM_IDLE *Mar 9 07:06:07.630: ISAKMP:(2051): processing HASH payload. message ID = 123795513 *Mar 9 07:06:07.630: ISAKMP:(2051): processing DELETE payload. message ID = 123795513 *Mar 9 07:06:07.630: ISAKMP:(2051):peer does not do paranoid keepalives. *Mar 9 07:06:07.630: ISAKMP:(2051):deleting SA reason "No reason" state (R) QM_IDLE (peer 172.16.5.5) *Mar 9 07:06:07.630: ISAKMP:(2051):deleting node 123795513 error FALSE reason "Informational (in) state 1" *Mar 9 07:06:07.634: ISAKMP: set new node -1701654990 to QM_IDLE *Mar 9 07:06:07.634: ISAKMP:(2051): sending packet to 172.16.5.5 my_port 500 peer_port 500 (R) QM_IDLE *Mar 9 07:06:07.634: ISAKMP:(2051):Sending an IKE IPv4 Packet. *Mar 9 07:06:07.634: ISAKMP:(2051):purging node -1701654990 *Mar 9 07:06:07.634: ISAKMP:(2051):Input = IKE_MESG_INTERNAL, IKE_PHASE1_DEL *Mar 9 07:06:07.634: ISAKMP:(2051):Old State = IKE_P1_COMPLETE New State = IKE_DEST_SA *Mar 9 07:06:07.634: ISAKMP:(2051):deleting SA reason "No reason" state (R) QM_IDLE (peer 172.16.5.5) *Mar 9 07:06:07.634: ISAKMP: Unlocking peer struct 0x859C9ED8 for isadb_mark_sa_deleted(), count 0 *Mar 9 07:06:07.638: ISAKMP: Deleting peer node by peer_reap for 172.16.5.5: 859C9ED8 *Mar 9 07:06:07.638: ISAKMP:(2051):Input = IKE_MESG_FROM_PEER, IKE_MM_EXCH *Mar 9 07:06:07.638: ISAKMP:(2051):Old State = IKE_DEST_SA New State = IKE_DEST_SA *Mar 9 07:06:07.638: IPSEC(key_engine): got a queue event with 1 KMI message(s) *Mar 9 07:06:08.827: ISAKMP (0): received packet from 172.16.5.5 dport 500 sport 500 Global (N) NEW SA *Mar 9 07:06:08.827: ISAKMP: Created a peer struct for 172.16.5.5, peer port 500 *Mar 9 07:06:08.827: ISAKMP: New peer created peer = 0x859C9ED8 peer_handle = 0x800000C8 *Mar 9 07:06:08.831: ISAKMP: Locking peer struct 0x859C9ED8, refcount 1 for crypto_isakmp_process_block *Mar 9 07:06:08.831: ISAKMP: local port 500, remote port 500 *Mar 9 07:06:08.831: ISAKMP: Find a dup sa in the avl tree during calling isadb_insert sa = 85D3B234 *Mar 9 07:06:08.831: ISAKMP:(0):Input = IKE_MESG_FROM_PEER, IKE_MM_EXCH *Mar 9 07:06:08.831: ISAKMP:(0):Old State = IKE_READY New State = IKE_R_MM1 *Mar 9 07:06:08.831: ISAKMP:(0): processing SA payload. message ID = 0 *Mar 9 07:06:08.831: ISAKMP:(0): processing vendor id payload *Mar 9 07:06:08.831: ISAKMP:(0): vendor ID seems Unity/DPD but major 215 mismatch *Mar 9 07:06:08.831: ISAKMP:(0): vendor ID is XAUTH *Mar 9 07:06:08.831: ISAKMP:(0): processing vendor id payload *Mar 9 07:06:08.831: ISAKMP:(0): vendor ID is DPD *Mar 9 07:06:08.831: ISAKMP:(0): processing vendor id payload *Mar 9 07:06:08.831: ISAKMP:(0): processing IKE frag vendor id payload *Mar 9 07:06:08.831: ISAKMP:(0):Support for IKE Fragmentation not enabled *Mar 9 07:06:08.835: ISAKMP:(0): processing vendor id payload *Mar 9 07:06:08.835: ISAKMP:(0): vendor ID seems Unity/DPD but major 69 mismatch *Mar 9 07:06:08.835: ISAKMP (0): vendor ID is NAT-T RFC 3947 *Mar 9 07:06:08.835: ISAKMP:(0): processing vendor id payload *Mar 9 07:06:08.835: ISAKMP:(0): vendor ID seems Unity/DPD but major 123 mismatch *Mar 9 07:06:08.835: ISAKMP:(0): vendor ID is NAT-T v2 *Mar 9 07:06:08.835: ISAKMP:(0):found peer pre-shared key matching 172.16.5.5 *Mar 9 07:06:08.835: ISAKMP:(0): local preshared key found *Mar 9 07:06:08.835: ISAKMP : Scanning profiles for xauth ... *Mar 9 07:06:08.835: ISAKMP:(0):Checking ISAKMP transform 1 against priority 10 policy *Mar 9 07:06:08.835: ISAKMP: encryption 3DES-CBC *Mar 9 07:06:08.835: ISAKMP: hash SHA *Mar 9 07:06:08.835: ISAKMP: default group 2 *Mar 9 07:06:08.835: ISAKMP: auth pre-share *Mar 9 07:06:08.835: ISAKMP: life type in seconds *Mar 9 07:06:08.835: ISAKMP: life duration (basic) of 28800 *Mar 9 07:06:08.835: ISAKMP:(0):atts are acceptable. Next payload is 0 *Mar 9 07:06:08.835: ISAKMP:(0):Acceptable atts:actual life: 4000 *Mar 9 07:06:08.835: ISAKMP:(0):Acceptable atts:life: 0 *Mar 9 07:06:08.835: ISAKMP:(0):Basic life_in_seconds:28800 *Mar 9 07:06:08.835: ISAKMP:(0):Returning Actual lifetime: 4000 *Mar 9 07:06:08.835: ISAKMP:(0)::Started lifetime timer: 4000. *Mar 9 07:06:08.835: ISAKMP:(0): processing vendor id payload *Mar 9 07:06:08.835: ISAKMP:(0): vendor ID seems Unity/DPD but major 215 mismatch *Mar 9 07:06:08.839: ISAKMP:(0): vendor ID is XAUTH *Mar 9 07:06:08.839: ISAKMP:(0): processing vendor id payload *Mar 9 07:06:08.839: ISAKMP:(0): vendor ID is DPD *Mar 9 07:06:08.839: ISAKMP:(0): processing vendor id payload *Mar 9 07:06:08.839: ISAKMP:(0): processing IKE frag vendor id payload *Mar 9 07:06:08.839: ISAKMP:(0):Support for IKE Fragmentation not enabled *Mar 9 07:06:08.839: ISAKMP:(0): processing vendor id payload *Mar 9 07:06:08.839: ISAKMP:(0): vendor ID seems Unity/DPD but major 69 mismatch *Mar 9 07:06:08.839: ISAKMP (0): vendor ID is NAT-T RFC 3947 *Mar 9 07:06:08.839: ISAKMP:(0): processing vendor id payload *Mar 9 07:06:08.839: ISAKMP:(0): vendor ID seems Unity/DPD but major 123 mismatch *Mar 9 07:06:08.839: ISAKMP:(0): vendor ID is NAT-T v2 *Mar 9 07:06:08.839: ISAKMP:(0):Input = IKE_MESG_INTERNAL, IKE_PROCESS_MAIN_MODE *Mar 9 07:06:08.839: ISAKMP:(0):Old State = IKE_R_MM1 New State = IKE_R_MM1 *Mar 9 07:06:08.843: ISAKMP:(0): constructed NAT-T vendor-rfc3947 ID *Mar 9 07:06:08.843: ISAKMP:(0): sending packet to 172.16.5.5 my_port 500 peer_port 500 (R) MM_SA_SETUP *Mar 9 07:06:08.843: ISAKMP:(0):Sending an IKE IPv4 Packet. *Mar 9 07:06:08.843: ISAKMP:(0):Input = IKE_MESG_INTERNAL, IKE_PROCESS_COMPLETE *Mar 9 07:06:08.843: ISAKMP:(0):Old State = IKE_R_MM1 New State = IKE_R_MM2 *Mar 9 07:06:08.899: ISAKMP (0): received packet from 172.16.5.5 dport 500 sport 500 Global (R) MM_SA_SETUP *Mar 9 07:06:08.899: ISAKMP:(0):Input = IKE_MESG_FROM_PEER, IKE_MM_EXCH *Mar 9 07:06:08.899: ISAKMP:(0):Old State = IKE_R_MM2 New State = IKE_R_MM3 *Mar 9 07:06:08.899: ISAKMP:(0): processing KE payload. message ID = 0 *Mar 9 07:06:08.943: ISAKMP:(0): processing NONCE payload. message ID = 0 *Mar 9 07:06:08.943: ISAKMP:(0):found peer pre-shared key matching 172.16.5.5 *Mar 9 07:06:08.947: ISAKMP:received payload type 20 *Mar 9 07:06:08.947: ISAKMP (2052): His hash no match - this node outside NAT *Mar 9 07:06:08.947: ISAKMP:received payload type 20 *Mar 9 07:06:08.947: ISAKMP (2052): No NAT Found for self or peer *Mar 9 07:06:08.947: ISAKMP:(2052):Input = IKE_MESG_INTERNAL, IKE_PROCESS_MAIN_MODE *Mar 9 07:06:08.947: ISAKMP:(2052):Old State = IKE_R_MM3 New State = IKE_R_MM3 *Mar 9 07:06:08.947: ISAKMP:(2052): sending packet to 172.16.5.5 my_port 500 peer_port 500 (R) MM_KEY_EXCH *Mar 9 07:06:08.947: ISAKMP:(2052):Sending an IKE IPv4 Packet. *Mar 9 07:06:08.947: ISAKMP:(2052):Input = IKE_MESG_INTERNAL, IKE_PROCESS_COMPLETE *Mar 9 07:06:08.947: ISAKMP:(2052):Old State = IKE_R_MM3 New State = IKE_R_MM4 *Mar 9 07:06:09.011: ISAKMP (2052): received packet from 172.16.5.5 dport 500 sport 500 Global (R) MM_KEY_EXCH *Mar 9 07:06:09.011: ISAKMP:(2052):Input = IKE_MESG_FROM_PEER, IKE_MM_EXCH *Mar 9 07:06:09.011: ISAKMP:(2052):Old State = IKE_R_MM4 New State = IKE_R_MM5 *Mar 9 07:06:09.015: ISAKMP:(2052): processing ID payload. message ID = 0 *Mar 9 07:06:09.015: ISAKMP (2052): ID payload next-payload : 8 type : 1 address : 172.16.5.5 protocol : 0 port : 0 length : 12 *Mar 9 07:06:09.015: ISAKMP:(0):: peer matches *none* of the profiles *Mar 9 07:06:09.015: ISAKMP:(2052): processing HASH payload. message ID = 0 *Mar 9 07:06:09.015: ISAKMP:(2052): processing NOTIFY INITIAL_CONTACT protocol 1 spi 0, message ID = 0, sa = 0x85D3B234 *Mar 9 07:06:09.015: ISAKMP:(2052):SA authentication status: authenticated *Mar 9 07:06:09.015: ISAKMP:(2052):SA has been authenticated with 172.16.5.5 *Mar 9 07:06:09.015: ISAKMP:(2052):SA authentication status: authenticated *Mar 9 07:06:09.015: ISAKMP:(2052): Process initial contact, bring down existing phase 1 and 2 SA's with local 172.16.5.20 remote 172.16.5.5 remote port 500 *Mar 9 07:06:09.015: ISAKMP: Trying to insert a peer 172.16.5.20/172.16.5.5/500/, and inserted successfully 859C9ED8. *Mar 9 07:06:09.015: ISAKMP:(2052):Input = IKE_MESG_INTERNAL, IKE_PROCESS_MAIN_MODE *Mar 9 07:06:09.015: ISAKMP:(2052):Old State = IKE_R_MM5 New State = IKE_R_MM5 *Mar 9 07:06:09.019: IPSEC(key_engine): got a queue event with 1 KMI message(s) *Mar 9 07:06:09.019: ISAKMP:(2052):SA is doing pre-shared key authentication using id type ID_IPV4_ADDR *Mar 9 07:06:09.019: ISAKMP (2052): ID payload next-payload : 8 type : 1 address : 172.16.5.20 protocol : 17 port : 500 length : 12 *Mar 9 07:06:09.019: ISAKMP:(2052):Total payload length: 12 *Mar 9 07:06:09.019: ISAKMP:(2052): sending packet to 172.16.5.5 my_port 500 peer_port 500 (R) MM_KEY_EXCH *Mar 9 07:06:09.019: ISAKMP:(2052):Sending an IKE IPv4 Packet. *Mar 9 07:06:09.019: ISAKMP:(2052):Returning Actual lifetime: 4000 *Mar 9 07:06:09.019: ISAKMP: set new node 37561868 to QM_IDLE *Mar 9 07:06:09.023: ISAKMP:(2052):Sending NOTIFY RESPONDER_LIFETIME protocol 1 spi 2231739112, message ID = 37561868 *Mar 9 07:06:09.023: ISAKMP:(2052): sending packet to 172.16.5.5 my_port 500 peer_port 500 (R) MM_KEY_EXCH *Mar 9 07:06:09.023: ISAKMP:(2052):Sending an IKE IPv4 Packet. *Mar 9 07:06:09.023: ISAKMP:(2052):purging node 37561868 *Mar 9 07:06:09.023: ISAKMP: Sending phase 1 responder lifetime 4000 *Mar 9 07:06:09.023: ISAKMP:(2052):Input = IKE_MESG_INTERNAL, IKE_PROCESS_COMPLETE *Mar 9 07:06:09.023: ISAKMP:(2052):Old State = IKE_R_MM5 New State = IKE_P1_COMPLETE *Mar 9 07:06:09.023: ISAKMP:(2052):IKE_DPD is enabled, initializing timers *Mar 9 07:06:09.023: ISAKMP:(2052):Input = IKE_MESG_INTERNAL, IKE_PHASE1_COMPLETE *Mar 9 07:06:09.023: ISAKMP:(2052):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE *Mar 9 07:06:09.075: ISAKMP (2052): received packet from 172.16.5.5 dport 500 sport 500 Global (R) QM_IDLE *Mar 9 07:06:09.075: ISAKMP: set new node -933143284 to QM_IDLE *Mar 9 07:06:09.079: ISAKMP:(2052): processing HASH payload. message ID = 3361824012 *Mar 9 07:06:09.079: ISAKMP:(2052): processing SA payload. message ID = 3361824012 *Mar 9 07:06:09.079: ISAKMP:(2052):Checking IPSec proposal 0 *Mar 9 07:06:09.079: ISAKMP: transform 1, ESP_3DES *Mar 9 07:06:09.079: ISAKMP: attributes in transform: *Mar 9 07:06:09.079: ISAKMP: authenticator is HMAC-SHA *Mar 9 07:06:09.079: ISAKMP: group is 2 *Mar 9 07:06:09.079: ISAKMP: encaps is 1 (Tunnel) *Mar 9 07:06:09.079: ISAKMP: SA life type in seconds *Mar 9 07:06:09.079: ISAKMP: SA life duration (basic) of 3600 *Mar 9 07:06:09.079: ISAKMP:(2052):atts are acceptable. *Mar 9 07:06:09.079: IPSEC(validate_proposal_request): proposal part #1 *Mar 9 07:06:09.079: IPSEC(validate_proposal_request): proposal part #1, (key eng. msg.) INBOUND local= 172.16.5.20:0, remote= 172.16.5.5:0, local_proxy= 172.16.152.0/255.255.255.0/0/0 (type=4), remote_proxy= 172.16.0.0/255.255.0.0/0/0 (type=4), protocol= ESP, transform= NONE (Tunnel), lifedur= 0s and 0kb, spi= 0x0(0), conn_id= 0, keysize= 0, flags= 0x0 *Mar 9 07:06:09.079: Crypto mapdb : proxy_match src addr : 172.16.152.0 dst addr : 172.16.0.0 protocol : 0 src port : 0 dst port : 0 *Mar 9 07:06:09.083: ISAKMP:(2052): processing NONCE payload. message ID = 3361824012 *Mar 9 07:06:09.083: ISAKMP:(2052): processing KE payload. message ID = 3361824012 *Mar 9 07:06:09.127: ISAKMP:(2052): processing ID payload. message ID = 3361824012 *Mar 9 07:06:09.127: ISAKMP:(2052): processing ID payload. message ID = 3361824012 *Mar 9 07:06:09.127: ISAKMP:(2052):QM Responder gets spi *Mar 9 07:06:09.127: ISAKMP:(2052):Node 3361824012, Input = IKE_MESG_FROM_PEER, IKE_QM_EXCH *Mar 9 07:06:09.127: ISAKMP:(2052):Old State = IKE_QM_READY New State = IKE_QM_SPI_STARVE *Mar 9 07:06:09.131: ISAKMP:(2052): Creating IPSec SAs *Mar 9 07:06:09.131: inbound SA from 172.16.5.5 to 172.16.5.20 (f/i) 0/ 0 (proxy 172.16.0.0 to 172.16.152.0) *Mar 9 07:06:09.131: has spi 0x23247432 and conn_id 0 *Mar 9 07:06:09.131: lifetime of 3600 seconds *Mar 9 07:06:09.131: outbound SA from 172.16.5.20 to 172.16.5.5 (f/i) 0/0 (proxy 172.16.152.0 to 172.16.0.0) *Mar 9 07:06:09.131: has spi 0xC7771621 and conn_id 0 *Mar 9 07:06:09.131: lifetime of 3600 seconds *Mar 9 07:06:09.131: ISAKMP:(2052): sending packet to 172.16.5.5 my_port 500 peer_port 500 (R) QM_IDLE *Mar 9 07:06:09.131: ISAKMP:(2052):Sending an IKE IPv4 Packet. *Mar 9 07:06:09.131: ISAKMP:(2052):Node 3361824012, Input = IKE_MESG_INTERNAL, IKE_GOT_SPI *Mar 9 07:06:09.131: ISAKMP:(2052):Old State = IKE_QM_SPI_STARVE New State = IKE_QM_R_QM2 *Mar 9 07:06:09.135: IPSEC(key_engine): got a queue event with 1 KMI message(s) *Mar 9 07:06:09.135: Crypto mapdb : proxy_match src addr : 172.16.152.0 dst addr : 172.16.0.0 protocol : 0 src port : 0 dst port : 0 *Mar 9 07:06:09.135: IPSEC(crypto_ipsec_sa_find_ident_head): reconnecting with the same proxies and peer 172.16.5.5 *Mar 9 07:06:09.135: IPSEC(policy_db_add_ident): src 172.16.152.0, dest 172.16.0.0, dest_port 0 *Mar 9 07:06:09.135: IPSEC(create_sa): sa created, (sa) sa_dest= 172.16.5.20, sa_proto= 50, sa_spi= 0x23247432(589591602), sa_trans= esp-3des esp-sha-hmac , sa_conn_id= 5 sa_lifetime(k/sec)= (4410759/3600) *Mar 9 07:06:09.135: IPSEC(create_sa): sa created, (sa) sa_dest= 172.16.5.5, sa_proto= 50, sa_spi= 0xC7771621(3346470433), sa_trans= esp-3des esp-sha-hmac , sa_conn_id= 6 sa_lifetime(k/sec)= (4410759/3600) *Mar 9 07:06:09.195: ISAKMP (2052): received packet from 172.16.5.5 dport 500 sport 500 Global (R) QM_IDLE *Mar 9 07:06:09.195: ISAKMP:(2052):deleting node -933143284 error FALSE reason "QM done (await)" *Mar 9 07:06:09.195: ISAKMP:(2052):Node 3361824012, Input = IKE_MESG_FROM_PEER, IKE_QM_EXCH *Mar 9 07:06:09.195: ISAKMP:(2052):Old State = IKE_QM_R_QM2 New State = IKE_QM_PHASE2_COMPLETE *Mar 9 07:06:09.195: IPSEC(key_engine): got a queue event with 1 KMI message(s) *Mar 9 07:06:09.195: IPSEC(key_engine_enable_outbound): rec'd enable notify from ISAKMP *Mar 9 07:06:09.195: IPSEC(key_engine_enable_outbound): enable SA with spi 3346470433/50 *Mar 9 07:06:09.195: IPSEC(update_current_outbound_sa): get enable SA peer 172.16.5.5 current outbound sa to SPI C7771621 *Mar 9 07:06:09.195: IPSEC(update_current_outbound_sa): updated peer 172.16.5.5 current outbound sa to SPI C7771621 *Mar 9 07:06:10.439: ISAKMP:(2050):purging node -181097793 *Mar 9 07:06:19.025: ISAKMP: set new node 757893848 to QM_IDLE *Mar 9 07:06:19.025: ISAKMP:(2052):Sending NOTIFY DPD/R_U_THERE protocol 1 spi 2231739072, message ID = 757893848 *Mar 9 07:06:19.025: ISAKMP:(2052): seq. no 0x407B4CC7 *Mar 9 07:06:19.025: ISAKMP:(2052): sending packet to 172.16.5.5 my_port 500 peer_port 500 (R) QM_IDLE *Mar 9 07:06:19.025: ISAKMP:(2052):Sending an IKE IPv4 Packet. *Mar 9 07:06:19.025: ISAKMP:(2052):purging node 757893848 *Mar 9 07:06:19.025: ISAKMP:(2052):Input = IKE_MESG_FROM_TIMER, IKE_TIMER_IM_ALIVE *Mar 9 07:06:19.025: ISAKMP:(2052):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE *Mar 9 07:06:19.073: ISAKMP (2052): received packet from 172.16.5.5 dport 500 sport 500 Global (R) QM_IDLE *Mar 9 07:06:19.073: ISAKMP: set new node -884230151 to QM_IDLE *Mar 9 07:06:19.077: ISAKMP:(2052): processing HASH payload. message ID = 3410737145 *Mar 9 07:06:19.077: ISAKMP:(2052): processing NOTIFY DPD/R_U_THERE_ACK protocol 1 spi 0, message ID = 3410737145, sa = 0x85D3B234 *Mar 9 07:06:19.077: ISAKMP:(2052): DPD/R_U_THERE_ACK received from peer 172.16.5.5, sequence 0x407B4CC7 *Mar 9 07:06:19.077: ISAKMP:(2052):deleting node -884230151 error FALSE reason "Informational (in) state 1" *Mar 9 07:06:19.077: ISAKMP:(2052):Input = IKE_MESG_FROM_PEER, IKE_INFO_NOTIFY *Mar 9 07:06:19.077: ISAKMP:(2052):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE *Mar 9 07:06:20.085: ISAKMP:(2050):purging node -1138592519 *Mar 9 07:06:28.999: ISAKMP: set new node -672023835 to QM_IDLE *Mar 9 07:06:28.999: ISAKMP:(2052):Sending NOTIFY DPD/R_U_THERE protocol 1 spi 2231739072, message ID = 3622943461 *Mar 9 07:06:28.999: ISAKMP:(2052): seq. no 0x407B4CC8 *Mar 9 07:06:28.999: ISAKMP:(2052): sending packet to 172.16.5.5 my_port 500 peer_port 500 (R) QM_IDLE *Mar 9 07:06:28.999: ISAKMP:(2052):Sending an IKE IPv4 Packet. *Mar 9 07:06:28.999: ISAKMP:(2052):purging node -672023835 *Mar 9 07:06:28.999: ISAKMP:(2052):Input = IKE_MESG_FROM_TIMER, IKE_TIMER_IM_ALIVE *Mar 9 07:06:28.999: ISAKMP:(2052):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE *Mar 9 07:06:29.051: ISAKMP (2052): received packet from 172.16.5.5 dport 500 sport 500 Global (R) QM_IDLE *Mar 9 07:06:29.051: ISAKMP: set new node 1050033724 to QM_IDLE *Mar 9 07:06:29.051: ISAKMP:(2052): processing HASH payload. message ID = 1050033724 *Mar 9 07:06:29.051: ISAKMP:(2052): processing NOTIFY DPD/R_U_THERE_ACK protocol 1 spi 0, message ID = 1050033724, sa = 0x85D3B234 *Mar 9 07:06:29.051: ISAKMP:(2052): DPD/R_U_THERE_ACK received from peer 172.16.5.5, sequence 0x407B4CC8 *Mar 9 07:06:29.051: ISAKMP:(2052):deleting node 1050033724 error FALSE reason "Informational (in) state 1" *Mar 9 07:06:29.051: ISAKMP:(2052):Input = IKE_MESG_FROM_PEER, IKE_INFO_NOTIFY *Mar 9 07:06:29.051: ISAKMP:(2052):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETEIt seems that I have still error in my cisco log.
-
Did you add the proper Firewall > Rules to the IPsec tab?
-
yes,
-
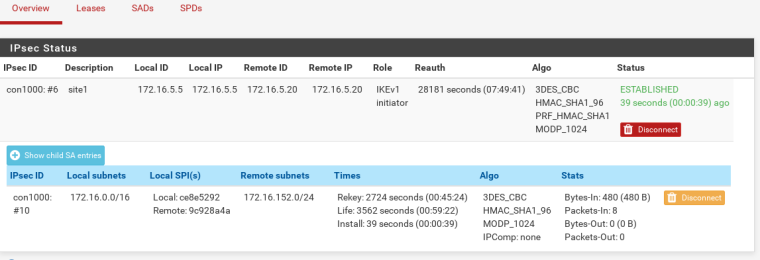
What does Status > IPsec show with the Phase 2 expanded?
-
-
It works like a charm.
 that last problem was related to my routing on main router(pf)
that last problem was related to my routing on main router(pf)
TNX Derelict, That was a great help for me.
That was a great help for me.
Another easy question:
Is it possible to have multi tunnel with more than one cisco at the same time?! like openvpn... -
Sure. Just do the same thing with a Phase 1 to the other endpoint and a phase 2 under that.
We have seen systems with hundreds of tunnels.
-
Ok,
TNX again, -
Hi, Again!,
I have a little question about the above configuration!
I calculate mtu over ipsec tunnel and enable 'Enable MSS clamping on VPN traffic' with 1486 value! over the ipsec tunnel clinets can see 2 lans without any problem.
but gre or l2tp/ipsec connection seems to have mtu problem. my clients on the remove lan uses windows l2tp/ipsec connection to connect to anther vlan on the main site over the Cisco-pf ipsec tunnel.
but can not access some services like https or big object like images on http. it seems that mtu problem!?
BTW, my ipsec tunnel on the cisco side runs over PPPoE connection. I set 'ip mtu' and 'ip tcp adjust-mss' in pppoe interface!
Any help ?!