IP Lan Block Migrated - Remote Access cannot get through Firewall Gateway
-
This post is deleted! -
@virtuousmight said in IP Lan Block Migrated - Remote Access cannot get through Firewall Gateway:
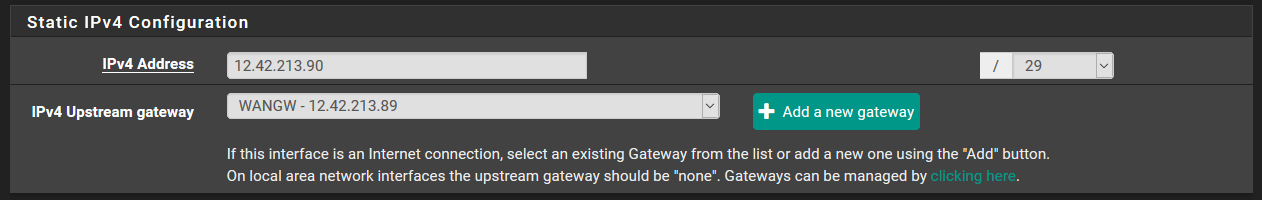
The problem is that AT&T shifted our LAN IP block from 12.42.213.88/29 to 12.42.213.90/29.
Your LAN IP block? Looks like WAN to me. They should have specified the address you should use as a gateway. Probably 12.42.213.91. But that would affect all internet traffic, not just a couple of port forwards. And those are not valid /29 networks. 12.42.213.90 is inside 12.42.213.88/29. The next highest /29 would be 12.42.213.96/29.
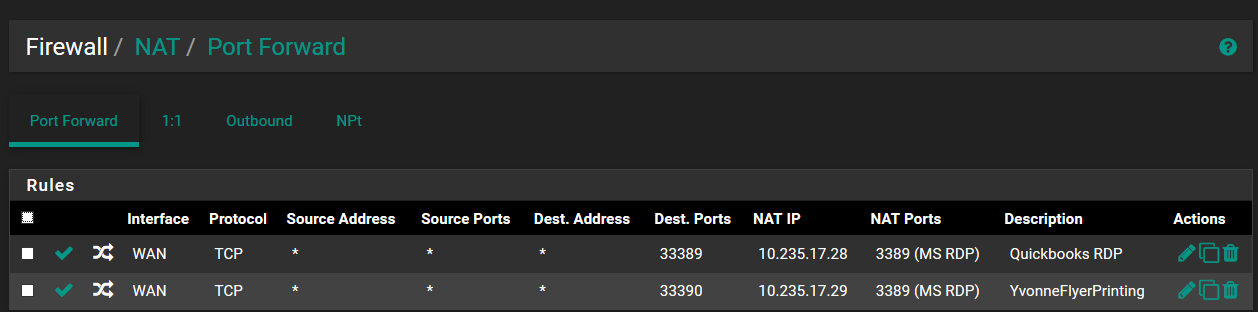
I don't care for destination any in a port forward. The destination address should be the address they are connecting to.
-
This post is deleted! -
I did a tracert to google dns and this is showing that the old IP gateway is still intact
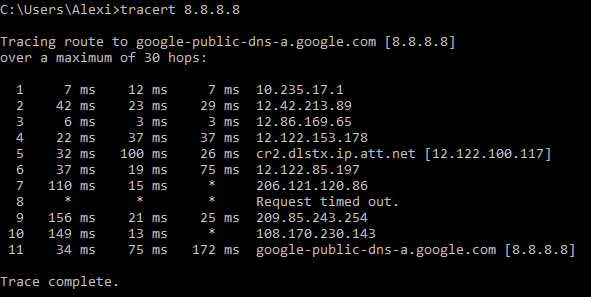
I am very confused.
-
@virtuousmight
For your sake, please obfuscate your public IPs, especially as you appear to have RDP open from the Internet. Consider using a VPN or two-factor. Something like xx.yy.zz.96/29 is sufficient for the topic. -
This post is deleted! -
@dotdash Yep indeed, being hasty with this and publishing said data is not best practice so I can delete my posts correct ?
-
To me that looks like WAN should be configured like this:
IPv4 Configuration Type: Static IPv4
IPv6 Configuration Type: Static IPv6IPv4 Address: X.X.X.66 /30
IPv4 Upstream Gateway: X.X.X.65IPv6 Address: 2001:1890:xxxx:xxxx::1143:6616 /64
IPv6 Upstream Gateway: 2001:1890:xxxx:xxxx::ee43:6616X.X.X.96/29 looks like it is routed to you. A port forward on any of those addresses should work without Virtual IP addresses assigned.
It looks like 2001:1890:xxxx:xxxx::/56 is also routed to you.
The only thing I would change is asking for a /29 instead of a /30 and asking for a /48 instead of a /56. They should have no problems with either request and, IMHO, should not charge for either. If they ask you why you want the /29 on the interface, tell them you need 3 addresses for VRRP.
-
@derelict Will try that implementation. Thanks.
-
Did the WAN interface numberings change?
-
No. The WAN interface numberings in the firewall remained exactly the same as they were before this new circuit and IP migration was done. After I powered on the ATT managed router and the fiber circuit was activated I powered on the pfSense and the juniper switches and nothing was auto-reconfiged or manually reconfiged in the WAN interface at all. Even though ATT made these changes from their endpoint and segments.
-
OK if there's another router then you might have to put the /29 on the pfSense WAN port. That would be:
IPv4 Configuration Type: Static IPv4
IPv6 Configuration Type: NoneIPv4 Address: X.X.X.98 /30
IPv4 Upstream Gateway: X.X.X.97You would have addresses 99-102 available for your port forwards, etc. You would need to add Virtual IP addresses so they ARP to the upstream router.
I left off the IPv6 because there are several ways that can be done.
I am really guessing here because I have no idea what the AT&T router brings to the table or what it does. I would put it in a closet if possible.
-
Okay I can work on that.
I do plan to set up Open VPN with the wizard app in the firewall for these two clients to use as I have not done so before.
-
If AR is AT&T Router and CR is Customer Router, then the first scenario is correct, which is a much better configuration for you.
-
No other router, they just provided another lan IP block which I can use on a different port on the router. I am not entirely sure why. I think because we have had two (they get supplanted with each bandwidth upgrade and relocation) in the recent past and I wanted to conserve those IP schemes.
-
OK. A routed subnet is what you want. It is the proper way to do this.
After I powered on the ATT managed router not sure what this is then.
-
@derelict Okay will have to research that thoroughly to ensure I do not make any errors.
But I still do not understand why when I did the tracert the older lan IP gateway is still a route and that is not listed on the ATT info of the new circuit as you can see above.
-
You never know what is going to respond to traceroute. That router probably has a boatload of addresses on it and that is what it is choosing to source from in reply.
-
@derelict If I go modify the upstream gateway IP will this affect all local network internet traffic in real time or only the remote session clients trying to connect ?
-
Depends on what you're actually talking about and how the traffic is routed to you.