Vlans No Switch?
-
@derelict well Basically just segregate each port into different vlans besides the two seperate vlans that are for roku and security systems i have multiple roku tv computers etc i bought two of those switchs i have em0 as wan Re0 and Re1 as lan side stuff so i was hopeing hook one switch to the Re0 and one to the Re1 I need a security system vlan with 4 ports all on same vlan i was hopeing if i put a router on that it would work to access my security systems even that would make my life easy... and setup another wireless router and roku tv vlan with 3 ports for that and that seperates my stuff if all other ports are segregated from each other and maybe once i see how thats done i can figure out whats what thanks
-
I'm under testing some kind of vlans configuration for watching if all work good or not work good.
Setup vlans itself is pretty simple, I need to test a lot of vlans subnet , and pfSense almost will manage without issue.

On pic above you can notice at one shot all my vlans testing environment, so you can see;interface tag number,
subnet and mask in cdir notation,
(Indeed I'm done with all other basic interface setting, DNS and DHCP enabled, one basic rule "interface to all" for each vlans)
This is a side note. If some folks not understand enough all background of pfSense
So, last one CDIR netmask is different for each subnet, I will to try, for testing purposes.
I need to known if will be reliable to generate some more much traffich at once and with different netmask. and switch tagging/untagging and last wireless multi ssid access point
For go foward now with vlans setup after this , before you leave from pfsense webui make sure to do everything is needed you need and rebott it

Next to assign tagged and untagged port on your switch*
well, my layout on crappy tl-sg105e as follow:

At this stage you can look a nice layout on the paper, I made this with my network teacher in mind, when he said something like "is better do a full vlans configuration on your device, for avoiding issues"
LOOL, just start with small "seven" tag configuration, this is enough for checking some vlans behaviors.
** My pfSense is connected at port 1 and my wlan ap is plugged at port 2 , other ports go to other devices and I will test later.**
I'm notice no many problem between devices, but because my crappy switch I guess some kind of "overlaps" and missing to get internet access when I'm under testing this only trought my multi ssid wlan ap.
Because this I back to only two ssid broadcasting instead of four available, with more to two ssid my wlan ap give up
I'm pretty sure of this, so next pic show my current multi ssid configuration:

So my test trials is not really done, but I like to show how to is pretty simple, dealing with vlans and pfSense!
Indeed routing trought all this subnet works well like a charm.
Bye
-
If that TP-Link AP behaves the same as my WA-901N, I can guarantee it won't handle VLANs properly.
-
That sg105e doesnt allow you to remove vlan 1.. So your whole attempt at trying to do vlans is moot.. You can not actually do valns with such switch..
If its v3 hardware you should be able to update so you can remove vlan 1 form your interfaces your wanting to put in other vlans.
Yeah their AP are the same lack of understanding design..
-
@johnpoz said in Vlans No Switch?:
Yeah their AP are the same lack of understanding design..
Same with their support staff. When I contacted them, they couldn't understand that VLANs should act as logically separate LANs, with no traffic passing between them. When I was able to reach 2nd level support, they accepted there was a problem, but no fix was forthcoming.
-
@johnpoz Using the Dgs-1100-08 is there a way to make vlans work with pfsense I spent all day messing with stuff I had it easier using ddwrt
-
Of course there is, but you have to understand what you are doing with VLANs in the first place.
In general:
If you assign a pfSense interface (Interfaces > Assignments) to:
igb0 - it will be on the untagged, native VLAN on the switchport it is connected to.
If you create VLAN 10 on igb0 and assign an interface to:
VLAN 10 on igb0 (igb0.10) it will be excpecting the switchport it is connected to to be tagging VLAN 10.
-
It sounds like I'm really close the way I had it I was trying to tag 4 vlans on one interface had DHCP serverss enabled I bet you it's the 802.1q tagging on the switch I'm doing wrong and it's probably cause I was treating it like ddwrt I thought it would ignore the Interfaces if I dropped them out of vlan 1 I thank you every little discussion seems to help I literally am still working on this since last night so yeah I'm really not as smart as i think
-
Why don't you post up a picture of what what you did.. I could fire up the one I have and show you the setup for exactly what you want it but it is drop dead simple
And you can use vlan one as your native - this isn't a enterprise network with policy and procedure about vlan 1 use, etc..
So your lan interface in pfsense has
192.168.1.0/24 on it
Lets create 2 other vlans
vlan 10, 192.168.10.0/24
vlan 20, 192.168.20.0/24These vlan are running on your lan interface..
So the port connected to lan of pfsense would be
vlan 1 (untagged), vlan 10 and 20 tagged. the pvid of this port would be vlan 1Now on your other ports you set them for either vlan 10 or 20 UNTAGGED... And pvid of vlan they are in 10 or 20..
For a port running to your AP it would be just like the port connected to pfsense lan
vlan 1 (untagged), vlan 10 and 20 tagged. the pvid of this port would be vlan 1edit: Here I pulled it off the shelf and connected it.. While I was at it updated its firmware ;)
ver 1.00.B031, current beta just came out this month..Anyhoo - as stated above for example..
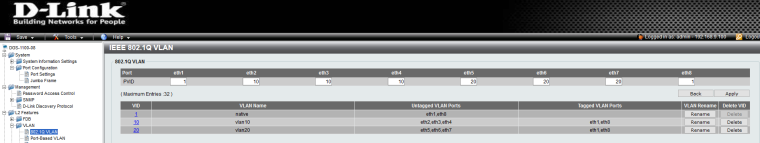
So say pfsense would be connected to port 1, and your AP would be connected to port 8..
While 2,3,4 would be devices in vlan 10, 5,6,7 would be devices in vlan 20 -
i was tagging ports on vlan 1 and tagging the ones you had untagged and i kept getting confused cause everything warned about using vlan1 thank you so much i am going to test it tonight and it took alot for me to follow this simple thing i got severe memory problems and attention
-
You can for sure change if you want the management vlan or default vlan of your switch.. I have mine set to vlan 9 for example... Then again I do this for living for like 30 years ;)
Vlan 1 is just the default - it means nothing in the big picture.. Any enterprise level switch will allow you to change the default vlan.. Your 30$ smart switch maybe not - but its not a bad thing using it.. Its just the default untagged vlan.. Be it 1, be it 10 or whatever id you assign.. its nothing more than the default vlan of the switch that ports are in that are not assigned to a different vlan..
In a soho sort of setup for sure you can just use vlan 1 as your default untagged network on your switches... Only in enterprise and controlled networks do they have policies that say you have to change the default vlan.. It doesn't really mean anything really from a security point of view on the big picture.. Its just BS policy ;)
It makes more sense to make sure that ports that are not used are actually disabled, etc. etc..
-
Okay with your switch configuration on the LAN interface that all worked for some reason it wouldnt on my opt1 interface RE1 but I assume i may have misconfigured it since i was so tired when attempting to do it...Next thing is Do i need to make rules to block cross traffic ? or does pfsense or the switch allready do that? My network has no Hardened rules right now which isnt good so I need to start reading all that and i watched a video where they setup vlans and you had to block all other vlan networks and allow dns and i was thinking that was wrong i just assumed that pfsense or the switch would automatically set the basic vlan to isolate and then you would be allowed to unsecure it if you wanted but im not an expert. THANK YOU You Saved me Months Of confusion. i just have default to any rules but thats very temporary
-
Traffic entering the firewall passes according to the rules on that interface.
No traffic is passed unless you pass it.
If you want to pass traffic you need to pass it.
If you want to block exceptions to that you need to block it.
-
@derelict you are the man, simple and clear description of approach to firewalling world.

Not needed "months" of learning to understand basic 's of how to pfSense handle firewalling rules.
Regards. -
@babiz No that is simple I just didnt understand How to setup my switch properly and while they do have 24 7 tech support for first 30 days they make me more confused than just attempting to do I know its simple now but their are somethings my brain just doesnt comprehend and thank you all for your Help I learned something from everyone
-
@telescopedepth I appreciate people's goodwill.

I understand you, also networking's jobs. you can learn enough, trought forum and community, as I do...
If you really want, nothing is impossible!
Meanwhile I'll reading some nice book like this
Some page for a day, it's easy to follow and full of good pratice, for me.
Regards.(Indeed pfSense book it is) Finally I need to thank so much pfsense team for this pretty nice gift, I dicovered few days ago, pfsense book for everyone is a must to have. Cool!