Port Forwarding
-
Having some issues forwarding Port 21. Not sure if I've missed something obvious or whether it is our ISP. Any suggestions would be appreciated.
-
Do you get this issue when you try to connect to your WAN-address both fron within the LAN and when you try from the outside?
In other words is it a NAT reflection issue, or doesn't the port forward work at all?Also are you sure you get a public IP from your ISP, or do you get a CG-NAT IP?
-
Explain "some issues" in more detail?
For instance if you are trying to say a passive FTP connection doesn't fully connect did you forward all the other ports? This is a Meraki document but explains the setup:
https://documentation.meraki.com/MX/NAT_and_Port_Forwarding/Active_and_Passive_FTP_Overview_and_Configuration#Passive_FTP_OverviewUsually we will restrict the port range on the FTP server software in order to forward less ports.
-
You really shouldn't use port 21 for FTP. I've got a setup here at the office, and I tried FTP first, but with it being so unsecure, and flaky with passive/active, etc., I gave up and switched to SFTP over the SSH port 22. I run 2 setups like this and they work perfectly on both ends - sending and receiving. Any modern FTP client supports SFTP in this way.
So, if you can get that going, all you need to do to make it work are a NAT port forward, and an associated firewall rule.
Here's how to do it:
First setup your internal SFTP server. I think there's some kind of certificate/code it generates that you have to use the first time on your FTP client, but I can't remember now, it's been a while, sorry.
Then, follow these steps:
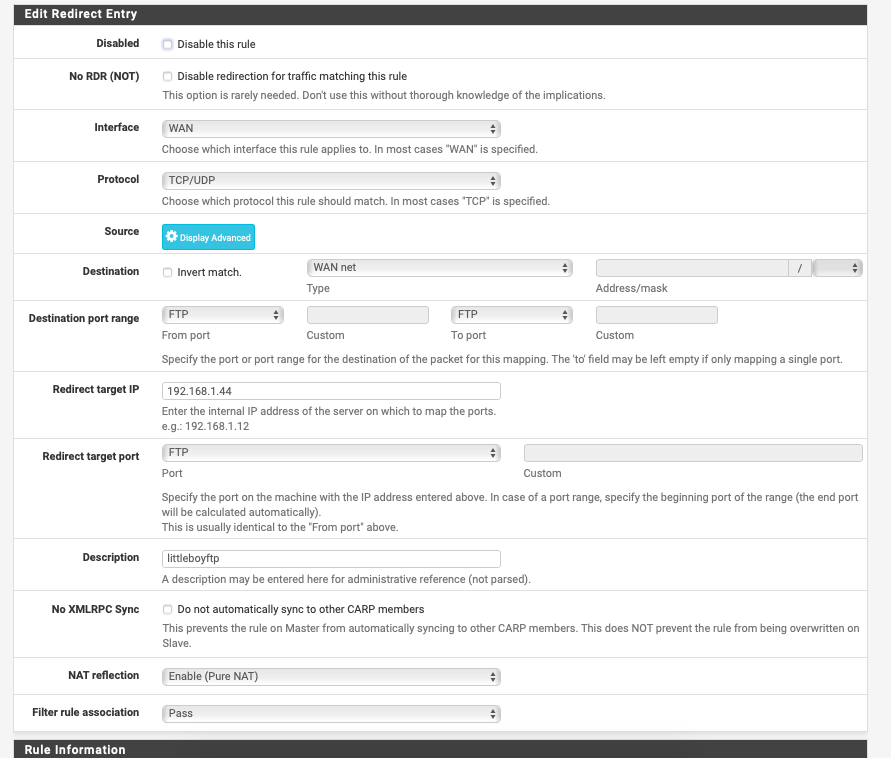
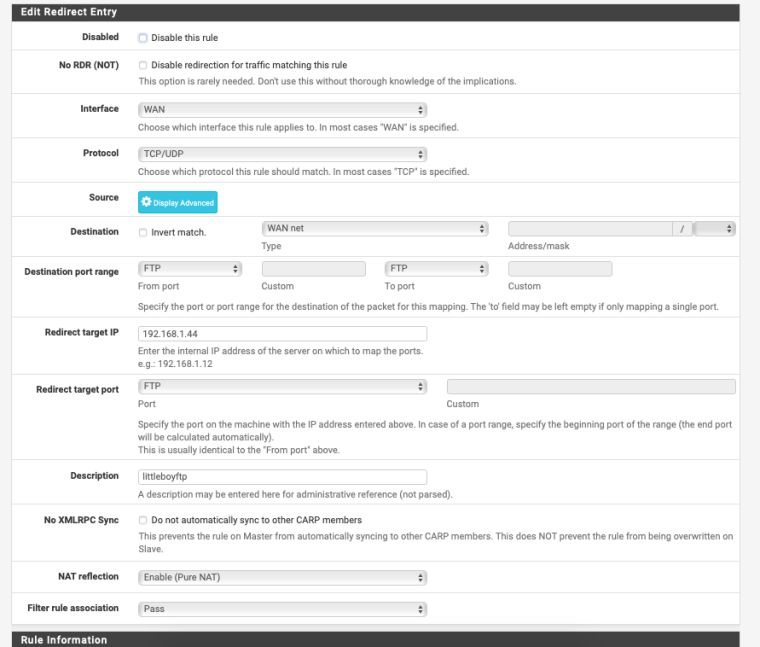
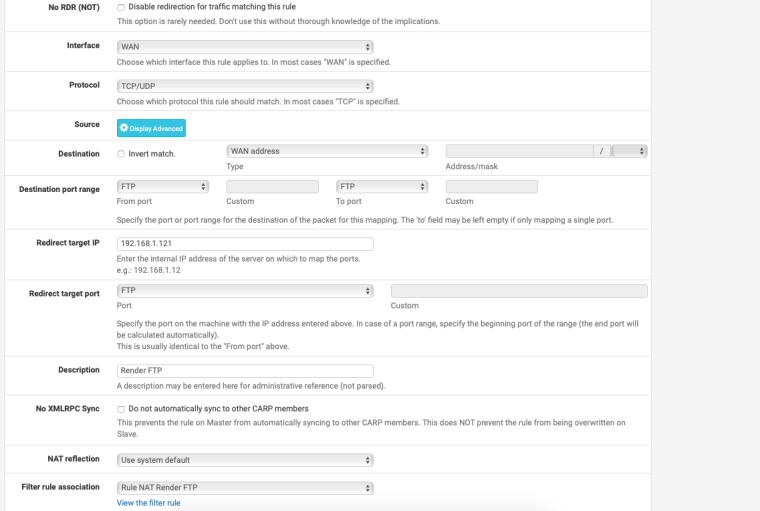
- Make a new port forward and select WAN as the interface
- Source is any, port range is from any to any
- Destination is WAN address, port range is from SSH to SSH
- Redirect target IP is your internal machine where the SFTP server is running, redirect target port is SSH
- give it a good description name
- make sure filter rule association is set to "create new rule"
And click save.
Hope that helps.
Jeff
-
@akuma1x Hi Jeff thanks for the suggestion. Unfortunately, port 22 also won't open. I have been trying 3389 as well but to no avail. Do you think it could be the ISP possibly?
-
@no_jah said in Port Forwarding:
CG-NAT IP
- We have tried multiple ports and can't seem to get any to open.
- It is possible that we are getting a CG NAT IP I will contact my ISP for that.
-
To find out if you got public IP or CG-NAT IP, all you need to d i s to got to whatsmyip.org to see if that IP is the sam as the pfSense WAN IP.
If they are the same IP you got public IP, if not you don't have publlic IP. -
@no_jah Just checked and they are the same
-
Ok, are you on the inside of the router (LAN) when you are testing the port forward, or do you com from the outside?
-
I can connect to the server from the internal IP from the LAN then I connect to a hotspot to test the WAN connection
-
Yes, but what I mean is if you have tested to connect any of the forwarded port when you are not physically on the inside of the pfSense machine (LAN), becaus the you also need to make sure NAT-reflection is set up and working.
For me Nat reflection only works if I select NAT + Proxy mode.
-
@no_jah oh I see sorry, yes I have used a different device. I did change the NAT reflection but this also didn't work.
-
Did you change to NAT + Proxy at System / Advanced, or at the NAT rule?
I recommend you set it at Systen / Anvanced, and then select Use system default at the NAT rule? -
@no_jah Ive gone ahead and set that but still no luck. Its weird ive never had this issue, Ive got a plex server set up at home fine through FTP
-
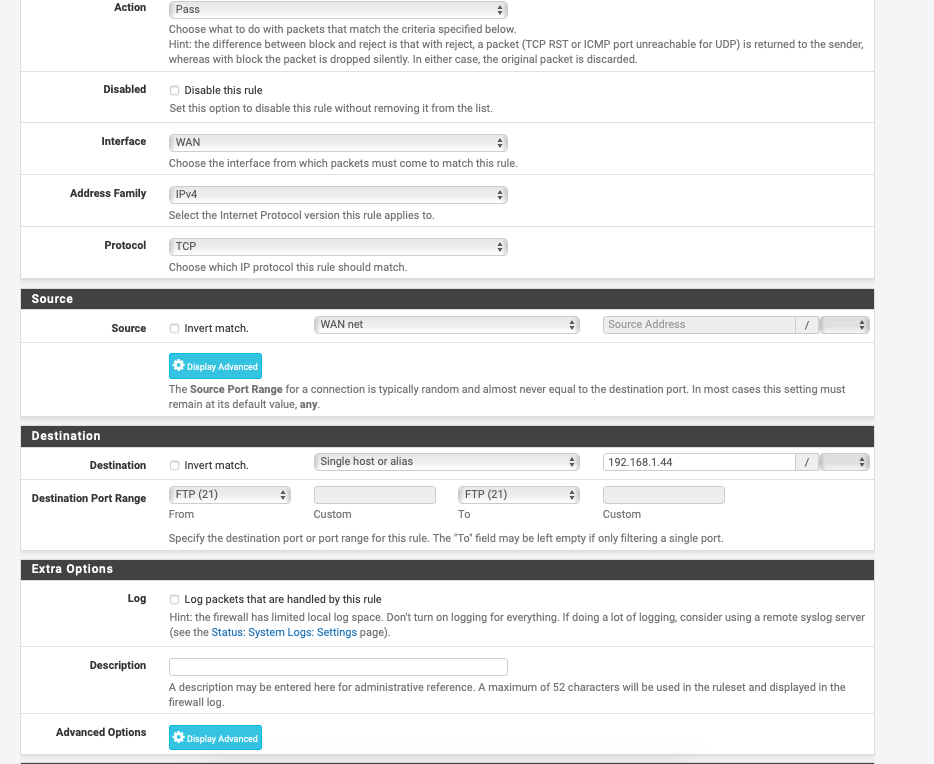
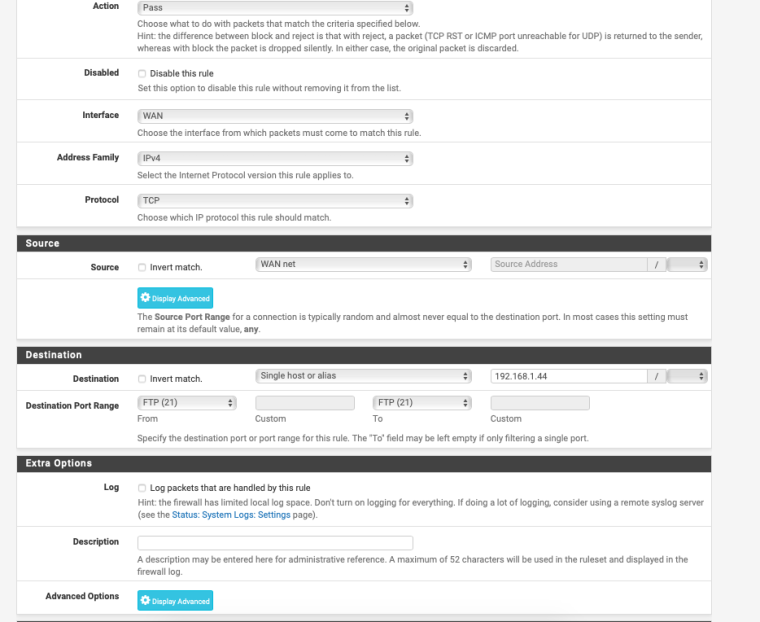
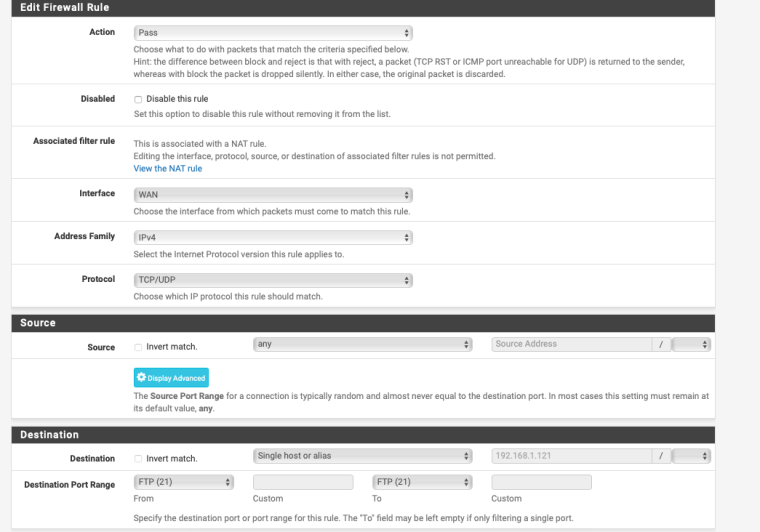
When I compare my port forward with the images you atatched I see a couple differences
- On port forward page I have WAN address instead of WAN net as Destination
- On the FW rule page I have any instead of WAN net as Source
-
Source of wan net would only allow IP from the wan net, ie the transit network that connects you to your ISP.. that is NOT the internet.
Also dest should be your wan address...
-
@no_jah I did in fact make these changes previously and didn't update the reference photos so these are the updated photos
-
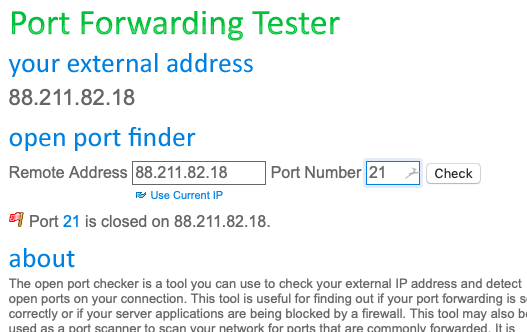
Just to really be sure you connect from the outside, try to use:
https://www.yougetsignal.com/tools/open-ports/There you enter your wan IP if it's not already picked up, and enter the port you want to check
-
@no_jah Just tried that
-
please post your wan rules and screenshot of your port forwards.
This is drop dead simple to do.. Follow the guide and you will find your issue within a couple of minutes.
https://www.netgate.com/docs/pfsense/nat/port-forward-troubleshooting.html
First thing to do if you feel your rules are correct is actually validate the traffic hits your WAN... Its impossible for pfsense to forward something it never gets. If pfsense gets it, then sniff on your lan interface of pfsense - does it send on... If so then problem is in your network or the host your sending it too.. Wrong host? Host firewall.. Host not even listening for that service, etc..