IPsec manual routing
-
Hi,
I'm looking for some help with the following setup.
I have a datacenter with a layer 2 connection and a remote site connected via IPsec VPN, on this remote site is an additional edge router.
I have successfully been able to configure the pFsense on the remote site to route local traffic to the edge router, this works great by using a static route in pFsense.
What I'd like to be able to do now is to route traffic from 10.172.118.253/24 to 172.1.1.128/27 across the Ipsec VPN connection.
I'm unsure how best to do this and which method. I've read that the new IPsec VTI may be able to do this but unsure how to configure, or whether I should be using manual outbound NAT.
Here is the current setup.
Datacenter WAN 31.31.31.65/26 LAN 10.172.117.253/24 OPT1 10.172.118.253/24 (Layer2) Remote site WAN 100.100.100.76/29 LAN 10.172.119.253/24 Edge Router 10.172.119.251 (172.1.1.128/27) -
Define the IPSec tunnel (seems this step is already done)
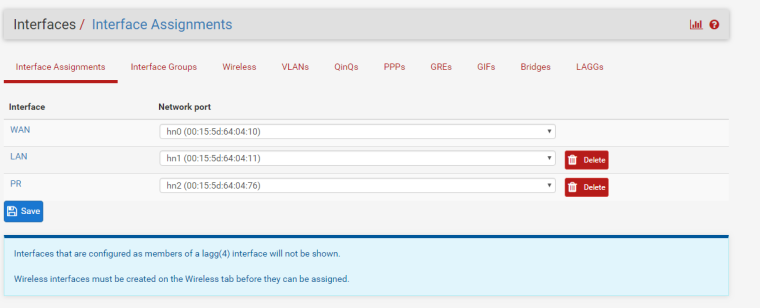
Go to interface assignments, add the IPSec tunnel interface.
Define the other side as a gateway (System->Routing)Assuming 10.172.118.253/24 is behind a 'LAN' interface:
On the LAN firewall rules table, create a rule with that subnet source, the 172.1.1.128/27 subnet as destination, Any protocol, any port, and at the bottom select 'Advanced', find the gateway option and send the traffic to your newly created gateway.What this does: Traffic matching the rule is grabbed and sent out via the IPSec VPN.
What additional setup is needed: Ensure a return route is also provided by the other end.Notes on when to NAT:
A general rule of thumb is: Do you control the distant end of this VPN tunnel? If so, its preferrable to avoid NAT. this allows more accurate troubleshooting in the event of an issue (I.E. packet captures, security log events etc.). Typically site to site vpn to a third party are behind a NAT in order to prevent the distant side from knowing what internal IP's you have configured. There are instances where you may make an exception to this (Maybe you have a remote DEV team you hired, and you want to verify logs from sources for auditing purposes, etc).Improving this configuration:
If it is possible, redundant routing can also be accomplished. You would set up any additional tunnels/gateways and add them to a gateway group. You would then specify this gateway group in the rule to be matched. Ex: MPLS route gateway can deliver to the same location that your IPSec tunnel can, but you prefer IPSec over MPLS. You would specify the IPSec gateway first in the group, then specify the MPLS gateway next. If IPSec goes down, your routing is swapped automatically to the MPLS circuit. -
Correct, the IPsec tunnel has already been added and has been working correctly for quite some time now.
I'm unable to add the IPSec tunnel interface, there's no add button here?
-
my apologies, for some reason i thought IPSec could be done the same as OpenVPN.
You may have to accomplish this with static routes or a GRE tunnel. -
If both sides support VTI I would suggest that over GRE.
https://www.youtube.com/watch?v=AKMZ9rNQx7Y