Users on the LAN network do not surf the internet
-
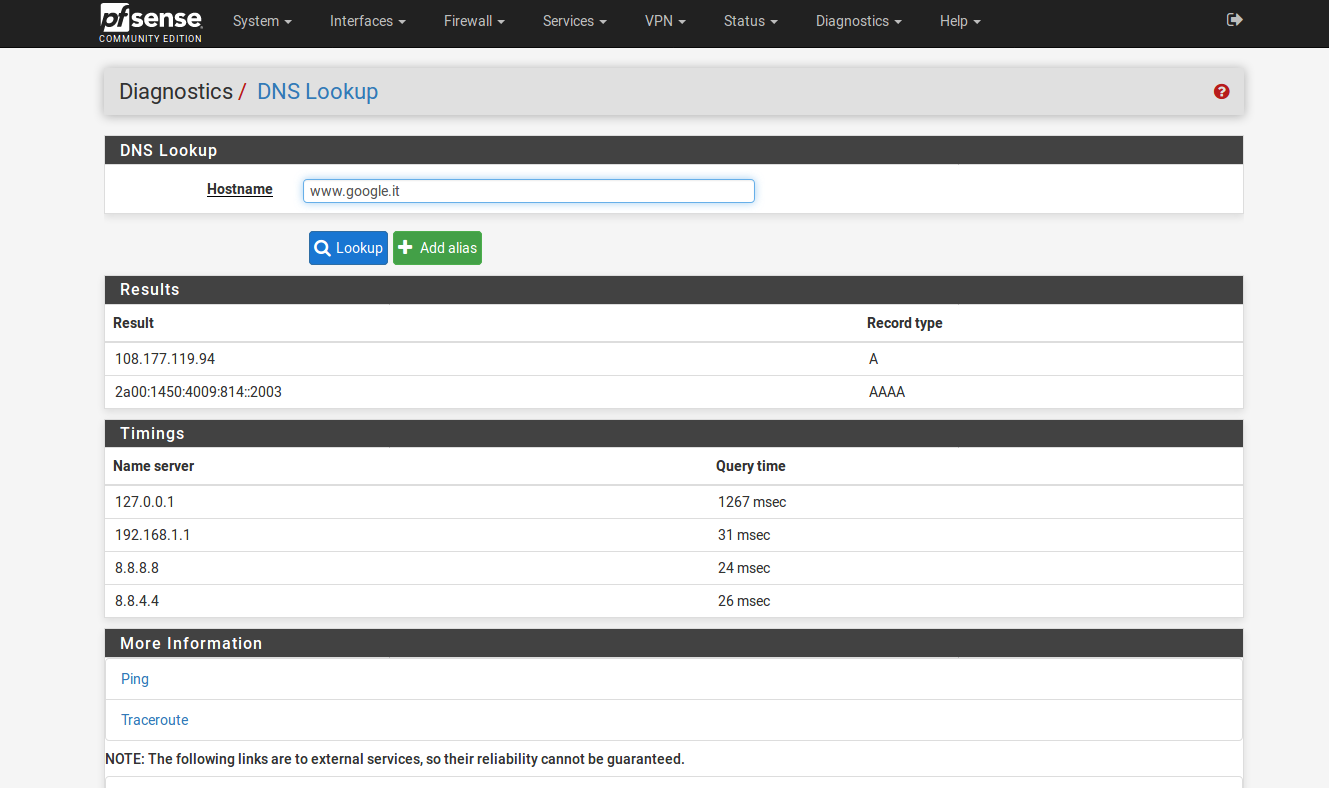
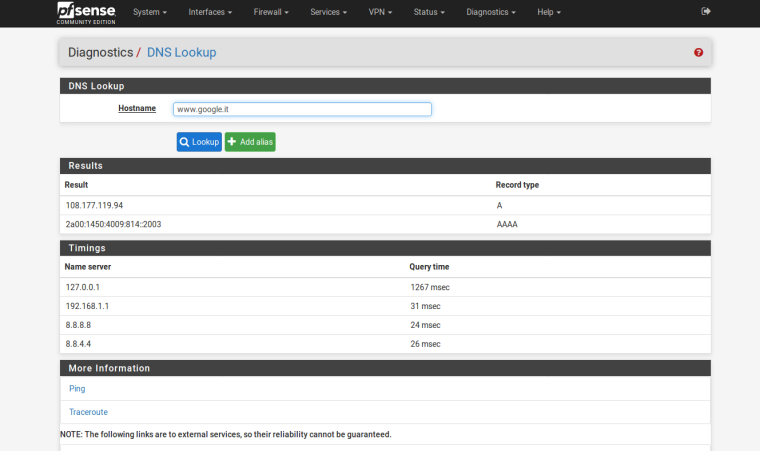
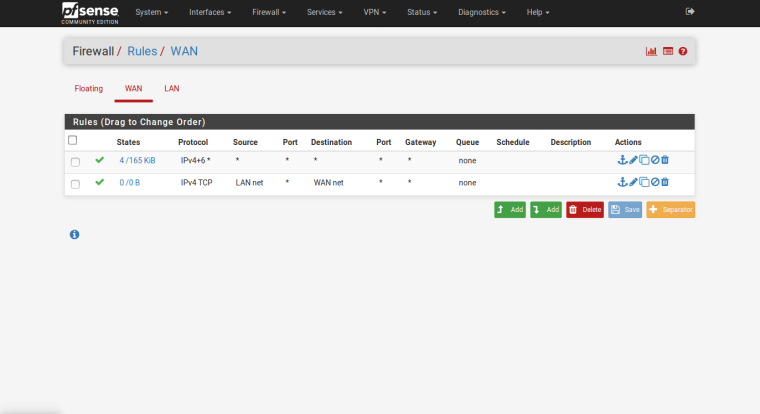
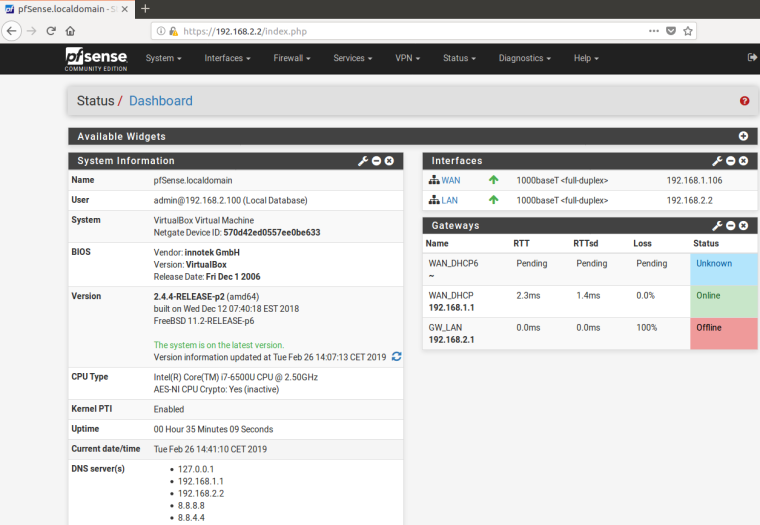
Hi everyone. I have a problem that I can not solve, and that is, I installed pfSense as virtual machine on VirtualBox to run tests in view of a future physical installation, but despite having performed to the letter the typical installation of pfSense, the machine, always virtual with the network card configured as "internal network" in DHCP with pfSense, does not surf the internet. From the web interface of the firewall I run ping tests to google DNS is successful but the virtual machine is completely isolated because it does not type the google DNS and therefore does not open any WEB page. I am attaching some pfSense screens on how the machine is configured. In addition I also tried to create rules to open HTTP ports etc ... both in the LAN and in the WAN, but always with no results.
Thanks a lot!
-
Hi,
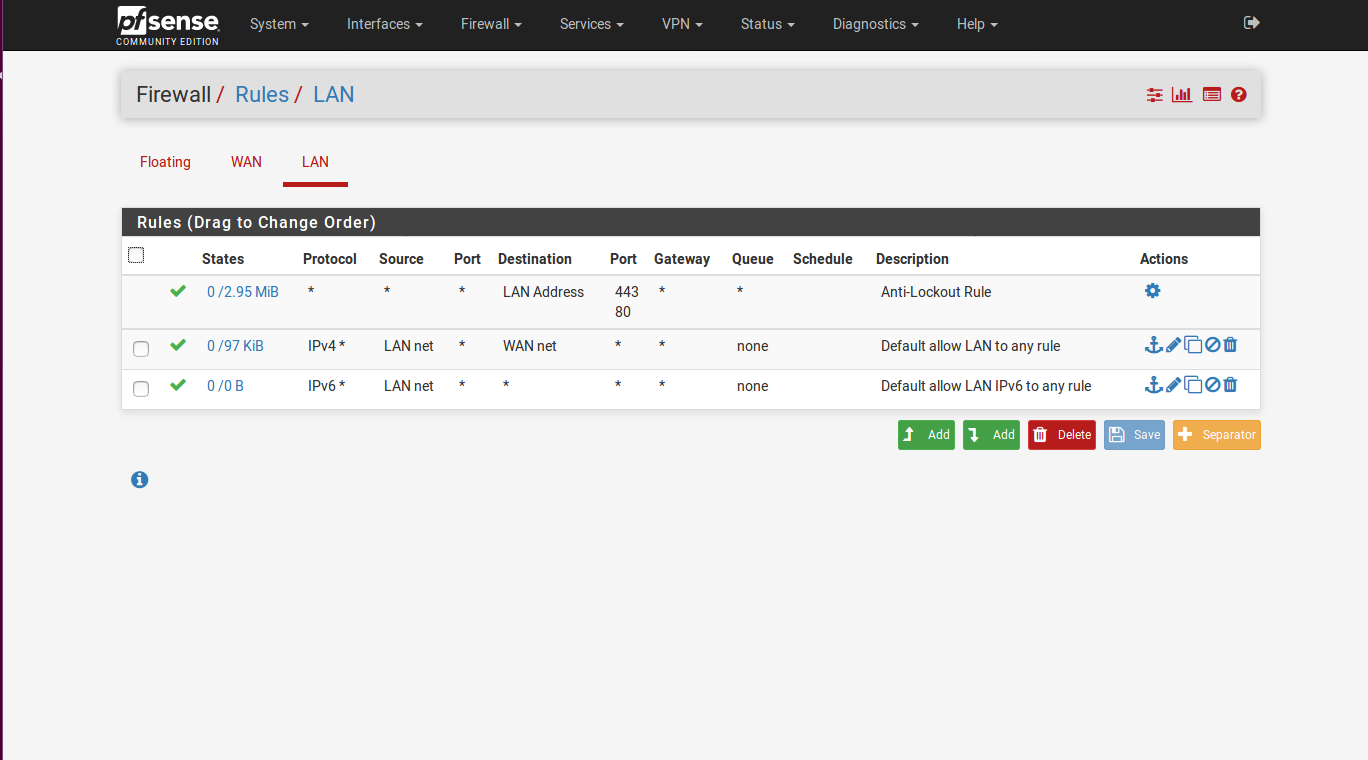
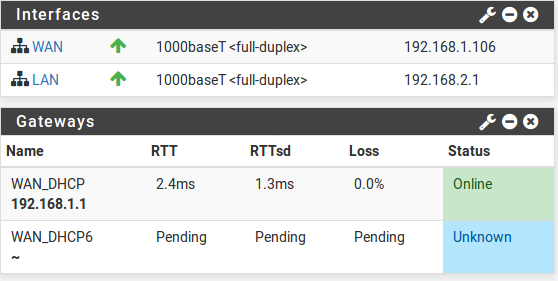
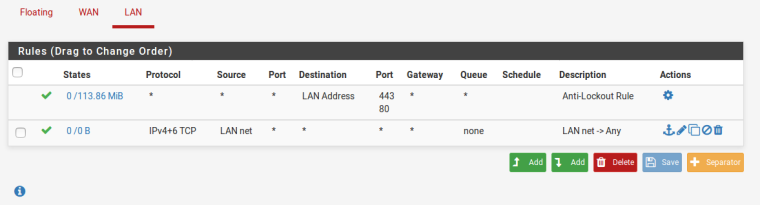
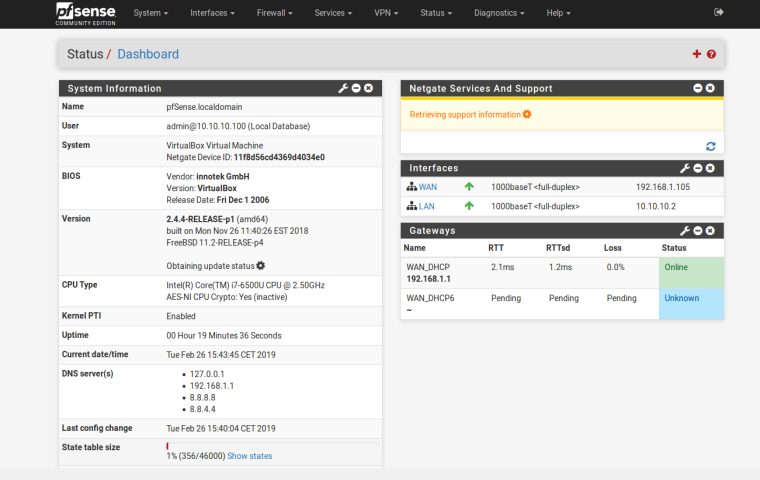
First image : looks good.
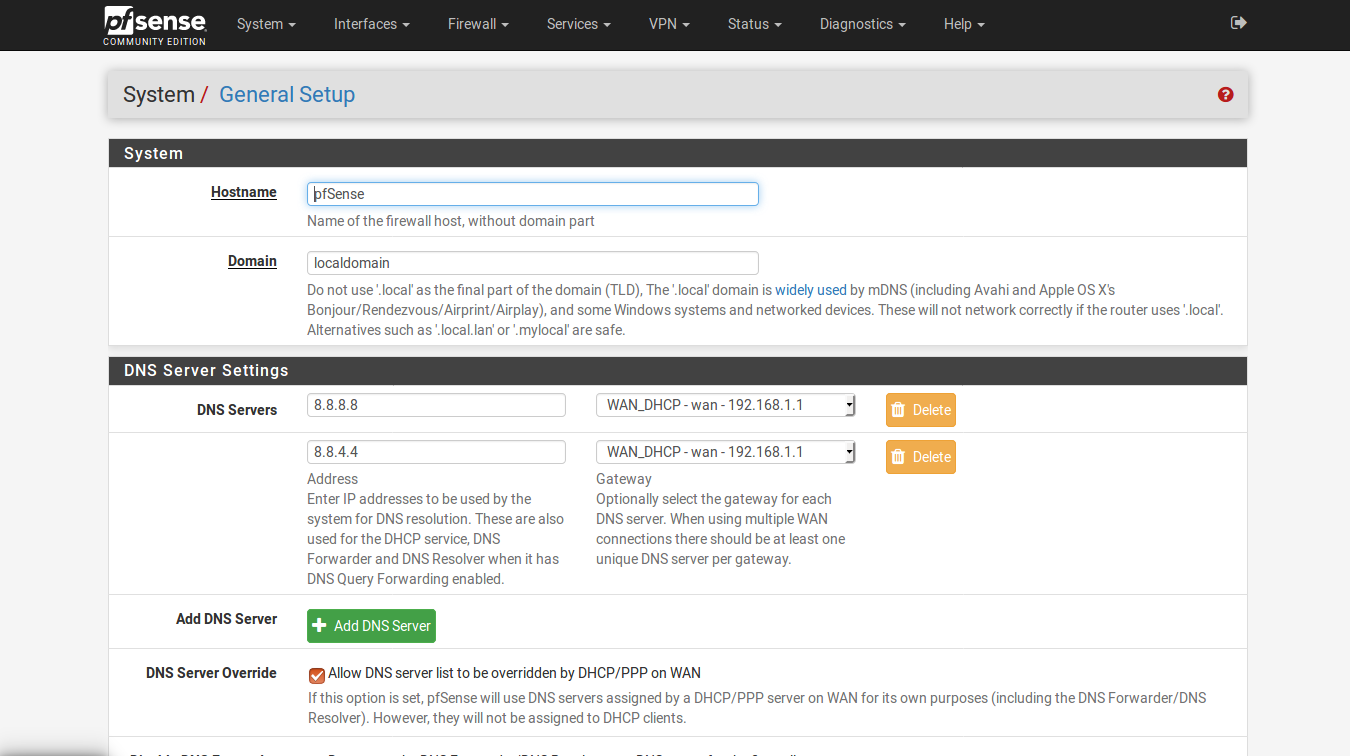
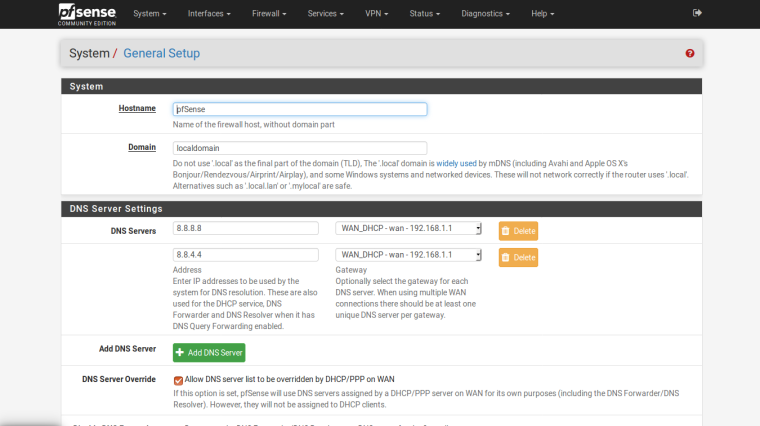
Seconds image : So you signed that contract with Google that they should be informed on everything you do on your LAN. I have just one (non related to your question) question : do they pay for that ? Other advantages ? You are aware of the fact that the default Resolver works just fine (and zero setup needed) ?
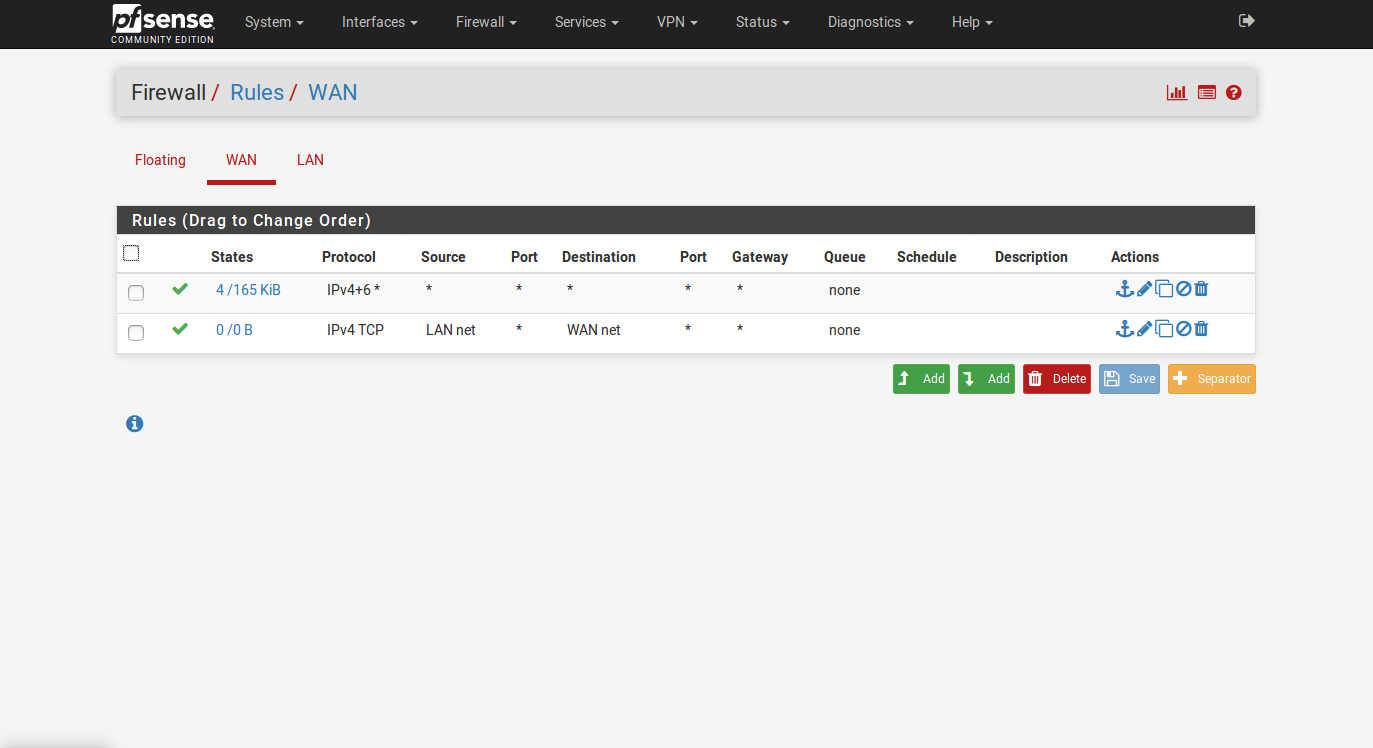
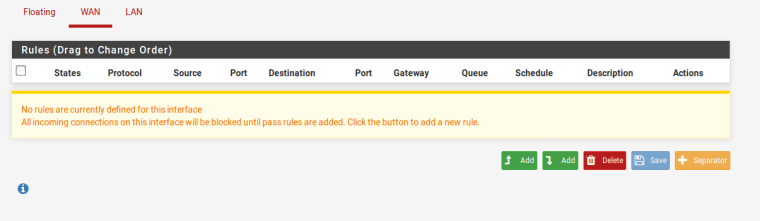
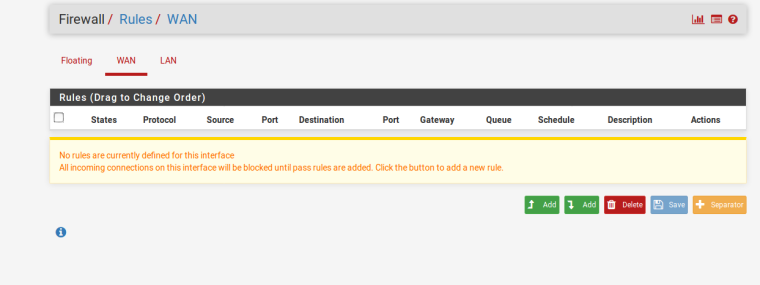
Third image : The WAN interface : this is very scary ! Remove these rules right now. Rules 2 is useless - rule one kills your firewall, creating a huge security risk. Normally, there are no firewall rules on WAN interface.
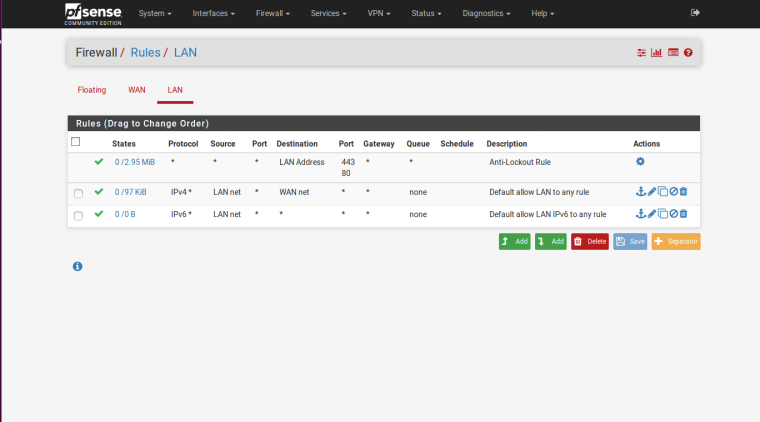
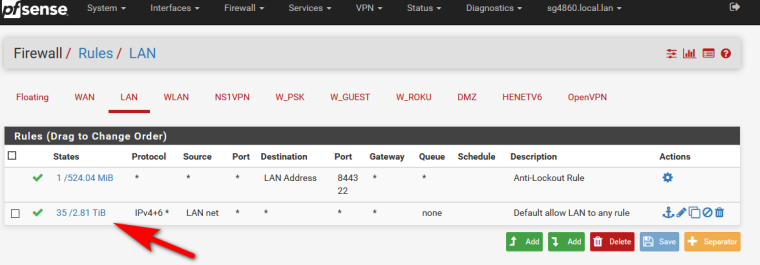
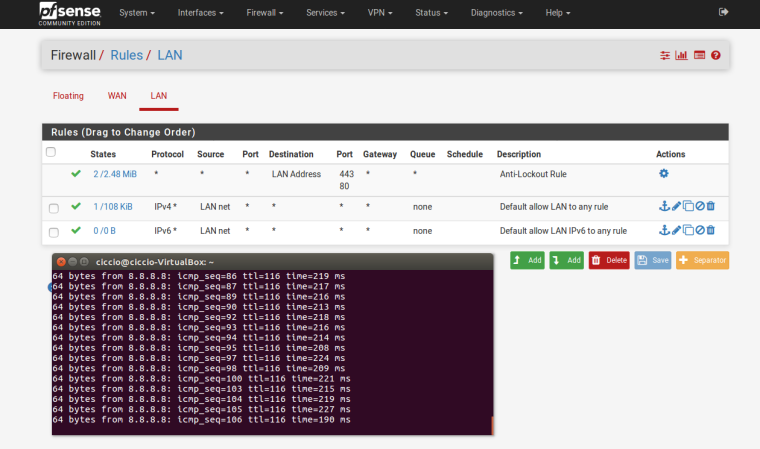
Fourth image : looks good. These rules permit any traffic to go out.Your main problem is : wrong setup of the VM.
Your WAN has IP 192.168.1.1 - ok, fine, but normally LAN is 192.168.1.1
And if LAN == WAN then you broke rule TCP/IP n° 1 and everything stops. -
@gertjan said in Users on the LAN network do not surf the internet:
Hi,
First image : looks good.
Seconds image : So you signed that contract with Google that they should be informed on everything you do on your LAN. I have just one (non related to your question) question : do they pay for that ? Other advantages ? You are aware of the fact that the default Resolver works just fine (and zero setup needed) ?
Third image : The WAN interface : this is very scary ! Remove these rules right now. Rules 2 is useless - rule one kills your firewall, creating a huge security risk. Normally, there are no firewall rules on WAN interface.
Fourth image : looks good. These rules permit any traffic to go out.
Your main problem is : wrong setup of the VM.
Your WAN has IP 192.168.1.1 - ok, fine, but normally LAN is 192.168.1.1
And if LAN == WAN then you broke rule TCP/IP n° 1 and everything stops.Thanks for the reply. In fact, I realized the error in the third image and I solved it. The WAN network is different from the LAN, the LAN is 192.168.2.1 while the WAN is 192.168.1.1, as can be seen from the image I entered below. From the virtual desktop machine I can ping the google dns, but I still can not surf the pc on the internet. I have checked the configurations of the virtual machines and I do not think there are errors.
-
Because your WAN is RFC 1918 :
Interfaces => WAN => Block private networks and loopback addresses == unchecked !?Diagnostics => Command Prompt and enter command
curl checkip.dyndns.orgshows what ?
Also try with IP (check IP first):
curl 131.186.113.70 -
yes, the two items of the WAN configuration are disabled. I can not run the "curl" command because it is not installed, and I can not install it (I mean the virtual machine) because it can not connect to the internet, but pinging to google DNS works.
-
@sparviero79 said in Users on the LAN network do not surf the internet:
yes, the two items of the WAN configuration are disabled. I can not run the "curl" command because it is not installed,
Good news for you : read https://forum.netgate.com/topic/140637/update-pfsense-packages-to-protect-against-nginx-libzmq4-and-curl-vulnerabilities
which implies that the command 'curl' is installed by default.Instead of using de dumb "Diagnostics => Command Prompt", use the console access.
Enter option 8.
Type curl.... VLAN10 (opt4) -> fxp0.10 -> v4: 192.168.9.1/24 0) Logout (SSH only) 9) pfTop 1) Assign Interfaces 10) Filter Logs 2) Set interface(s) IP address 11) Restart webConfigurator 3) Reset webConfigurator password 12) PHP shell + pfSense tools 4) Reset to factory defaults 13) Update from console 5) Reboot system 14) Disable Secure Shell (sshd) 6) Halt system 15) Restore recent configuration 7) Ping host 16) Restart PHP-FPM 8) Shell Enter an option: 8 [2.4.4-RELEASE][admin@pfsense.brit-hotel-fumel.net]/root: curlIf curl isn't there, consider your system broken. Re install.
-
ok sorry, I thought the command had to run from the virtual desktop machine. the result from the pfsense console is this:
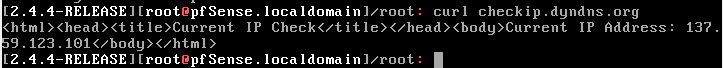
-
Perfect.
It's resolving and http works.Now, throw away 'your' LAN rules (the second and third, the first is auto generated) and make it look like
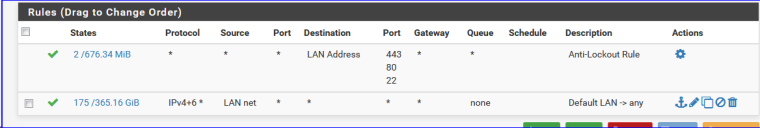
(ditch the Destination : "WAN net" on the IPv4 rule - dono where that came from, somewhat missed that earlier this morning) -
I did, but without result

-
Notice the lan rule doesn't even show any hits its 0/0
You sure your clients are even talking to pfsense to get to the internet?
You should see hits on your lan rule
You have zero?
-
I guess he took a screen shot right after applying without testing LAN access first ;)
-
Actually now I have encountered this problem, the LAN gateway is offline
-
there shouldn't be a LAN gateway.. Is that a gateway to get to downstream networks? If so then it should be connected via transit network.. Using a network with hosts on it as transit is going to be an an issue with asymmetrical routing.
-
I guess I could mention right away : if you 'did' anything with gateways, undo that.
More general : re do the entire setup. Just set up WAN (the access to the up stream router) and do not touch anything else.
It will work.
At that point, start applying your personalization, and test thoroughly every step - as soon as your connection is lost, undo the last step and study more about. -
Guys thank you very much for the help you are giving me. I'm starting now to study the firewall world and then learn more and more because I have a great passion for this world. sorry if I disturb you with my inexperience, but I have to start somehow to learn.
Now I'm doing a clean installation and I'll let you know ;-) -
I made a clean new installation, but the result does not change. I think I did everything you told me ... I'm almost giving up
-
In your General Setup screen, I don't think you need the gateways defined for those 2 Google DNS servers. Of the 5-6 pfsense boxes I've installed and managed, I never have to put in a value there.
Set those values to "None", save your settings, maybe even reboot the pfsense instance, then try the internet from your LAN network again...
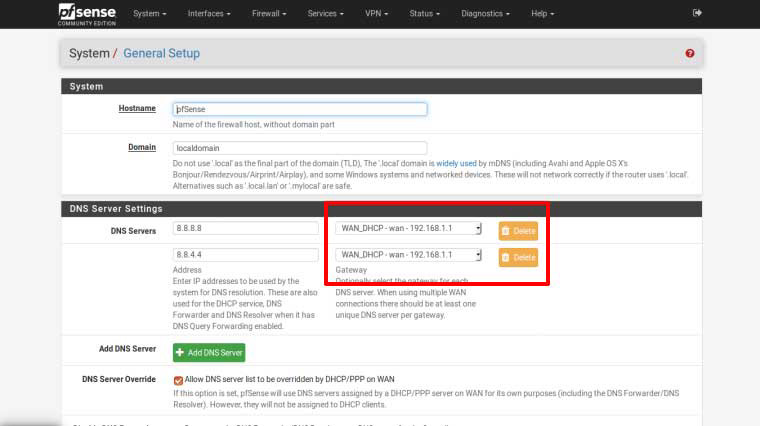
Jeff
-
Agree with that.
One shouldn't even touch anything related to DNS the first 48 hours after initial setup.
No where it has been said in any firewall setup-doc that a DNS should be set ! Not in the official Netgate support doc, and no where else.
These "8.8.8.8" and "4.4.4.4" are like "Christmas" and "Antivirus" : they were invented for pure commercial reasons.
(IMHO) -
VirtualBox does tend to use it's own DHCP server on internal networks, that might conflict with pfSense. So check the network settings on your client VM.
@sparviero79 said in Users on the LAN network do not surf the internet:
sorry if I disturb you with my inexperience, but I have to start somehow to learn.
First learn the details about your virtualization environment, then learn the details about the guest systems.
-
Ok because my questions seem to be causing bad mood, I remove the trouble and look elsewhere.
Thanks anyway