Another IGMP proxy post
-
For the life of me I cannot seem to get this to work...
Vlan 10 - 192.168.10.0/24
Vlan 55 - 192.168.55.0/24My setup goes like this...
PFSENSE
Connected via a trunk line to port 1 on a switch allowed vlans 10,55Server 1 - 192.168.55.125 - UPSTREAM
connected to port 2 on switch Vlan 55PC 1 - 192.168.10.2 - DOWNSTREAM
connected to port 3 on switch Vlan 10I have IGMP proxy turned on in PFSENSE
Rules are allowed any IPv4 for both interfaces with the extra IP options checked.annnnnnnnnnnnnnnd. Nothing.... I do a packet capture and I see no communication between the two interfaces. However they can ping each other and navigate via webbrowser, etc. Just no multicast traffic.
Any thoughts?
-
What are you running on the server and client?
Do you see igmp or multicast traffic coming from either device in pcaps? Just not crossing between subnets?
Steve
-
In terms of OS? The client is running on windows. It's a closed source video app that looks for a TV tuner on the network via multicast and then sends video via a unicast.
The server is a TV tuner on the network.I did see some random IGMP packets on the server side but nothing on the client side.
-
10:02:36.940821 ARP, Request who-has 192.168.55.1 (ff:ff:ff:ff:ff:ff) tell 192.168.55.125, length 46 10:02:36.940827 ARP, Reply 192.168.55.1 is-at 00:1b:21:a5:10:45, length 28 10:03:36.940486 ARP, Request who-has 192.168.55.1 (ff:ff:ff:ff:ff:ff) tell 192.168.55.125, length 46 10:03:36.940495 ARP, Reply 192.168.55.1 is-at 00:1b:21:a5:10:45, length 28 10:03:38.888473 IP 192.168.55.125 > 224.0.0.22: igmp 10:03:39.134480 IP 192.168.55.125 > 224.0.0.22: igmp -
That is the opposite of what I expect to see there. Usually the client is on the TV and tries to discover the server to get media from it. Do you see anything coming from the TV side?
Also why did 192.168.55.125 not see that first ARP reply?Steve
-
Yeah I'm a little perplexed myself...
I checked did a pcap for the other interface and didnt see any IGMP traffic.
I could put them in the same subnet and see whats going on but I don't know if it'll make it past the switch as the switch will probably just route the traffic no?
-
on another note I did another pcap but had medium details shown. It looks like the "server" is sending out upnp ssdp packets
11:29:31.344213 IP (tos 0x0, ttl 4, id 7976, offset 0, flags [none], proto UDP (17), length 301) 192.168.55.125.1900 > 239.255.255.250.1900: UDP, length 273 11:29:31.365150 IP (tos 0x0, ttl 4, id 7977, offset 0, flags [none], proto UDP (17), length 292) 192.168.55.125.1900 > 239.255.255.250.1900: UDP, length 264 11:29:31.386168 IP (tos 0x0, ttl 4, id 7978, offset 0, flags [none], proto UDP (17), length 362) 192.168.55.125.1900 > 239.255.255.250.1900: UDP, length 334 11:29:31.407139 IP (tos 0x0, ttl 4, id 7979, offset 0, flags [none], proto UDP (17), length 356) 192.168.55.125.1900 > 239.255.255.250.1900: UDP, length 328 11:29:31.428197 IP (tos 0x0, ttl 4, id 7980, offset 0, flags [none], proto UDP (17), length 301) 192.168.55.125.1900 > 239.255.255.250.1900: UDP, length 273 11:29:31.449146 IP (tos 0x0, ttl 4, id 7981, offset 0, flags [none], proto UDP (17), length 344) 192.168.55.125.1900 > 239.255.255.250.1900: UDP, length 316 11:29:31.470155 IP (tos 0x0, ttl 4, id 7982, offset 0, flags [none], proto UDP (17), length 346) 192.168.55.125.1900 > 239.255.255.250.1900: UDP, length 318 -
Just to be clear 55.125 is the TV here right?
And is it in someway interactive or more like an advertising screen? It looks for video source and plays it as sooin as it;s powered up?
Steve
-
55.125 is the video server. https://www.silicondust.com/images/hdhomerun/QS_HDHomeRun_PRIME.pdf
The TV/client is on a separate subnet.
https://www.silicondust.com/support/hdhomerun/testfail/upnp_multicast_recv/
"HDHomeRun Setup triggers the HDHomeRun to send a series of SSDP NOTIFY packets to the 239.255.255.250 multicast group."
-
Ah I see. It is the opposite way around to how I would usually expect. OK.
There have been issues with the IGMP proxy on VLANs in the past but I thought they were mostly resolved.
Do you see any errors in the system log when you start it?You might try stopping the service in the GUI and then starting it in debug mode at the command line:
igmpproxy -d -vv /var/etc/igmpproxy.confThat will give you a lot of output. It will show if the groups are being joined correctly though.
Steve
-
So I did that. I don't know where it is outputting to but this is what happens when I do a pcap on full for the interface that the server is on.
10:17:44.128444 00:18:dd:32:28:1b > 01:00:5e:00:00:16, ethertype IPv4 (0x0800), length 60: (tos 0xc0, ttl 1, id 0, offset 0, flags [DF], proto IGMP (2), length 40, options (RA)) 192.168.10.142 > 224.0.0.22: igmp v3 report, 1 group record(s) [gaddr 239.255.255.250 is_ex { }] 10:17:44.377428 00:18:dd:32:28:1b > 01:00:5e:00:00:16, ethertype IPv4 (0x0800), length 60: (tos 0xc0, ttl 1, id 0, offset 0, flags [DF], proto IGMP (2), length 40, options (RA)) 192.168.10.142 > 224.0.0.22: igmp v3 report, 1 group record(s) [gaddr 239.255.255.250 is_ex { }]Is the TTL being "1" going to cause an issue with forwarding it to the interface/vlan with the client on it?
-
It should be outputting the debug stuff at the command line where you started it. That should tell us if it's doing anything useful at all.
Steve
-
The only output is what is below:
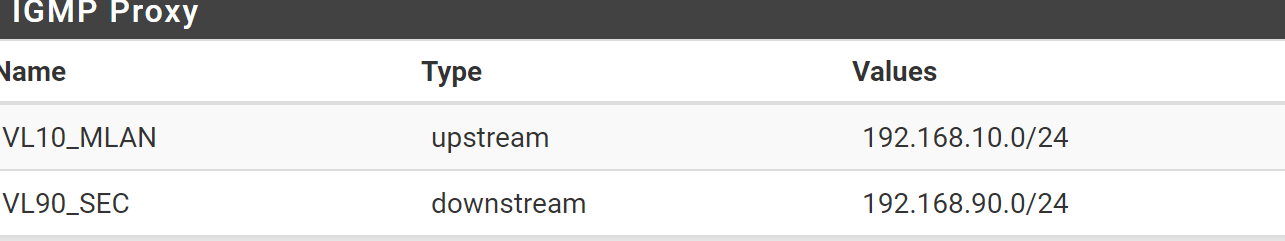
Searching for config file at '/var/etc/igmpproxy.conf' Config: Quick leave mode enabled. Config: Got a phyint token. Config: IF: Config for interface igb1.10. Config: IF: Got upstream token. Config: IF: Got ratelimit token '0'. Config: IF: Got threshold token '1'. Config: IF: Got altnet token 192.168.10.0/24. Config: IF: Altnet: Parsed altnet to 192.168.10/24. Config: IF: Got altnet token xxxxxxxxxx. Config: IF: Altnet: Parsed altnet to xxxxxxxxx. IF name : igb1.10 Next ptr : 0 Ratelimit : 0 Threshold : 1 State : 1 Allowednet ptr : e25000 Config: Got a phyint token. Config: IF: Config for interface igb1.90. Config: IF: Got downstream token. Config: IF: Got ratelimit token '0'. Config: IF: Got threshold token '1'. Config: IF: Got altnet token 192.168.90.0/24. Config: IF: Altnet: Parsed altnet to 192.168.90/24. IF name : igb1.90 Next ptr : 0 Ratelimit : 0 Threshold : 1 State : 2 Allowednet ptr : e25020 Config: Got a phyint token. Config: IF: Config for interface igb0. Config: IF: Got disabled token. IF name : igb0 Next ptr : 0 Ratelimit : 0 Threshold : 1 State : 0 Allowednet ptr : 0 Config: Got a phyint token. Config: IF: Config for interface igb1. Config: IF: Got disabled token. IF name : igb1 Next ptr : 0 Ratelimit : 0 Threshold : 1 State : 0 Allowednet ptr : 0 Config: Got a phyint token. Config: IF: Config for interface igb1.99. Config: IF: Got disabled token. IF name : igb1.99 Next ptr : 0 Ratelimit : 0 Threshold : 1 State : 0 Allowednet ptr : 0 Config: Got a phyint token. Config: IF: Config for interface ovpnc2. Config: IF: Got disabled token. IF name : ovpnc2 Next ptr : 0 Ratelimit : 0 Threshold : 1 State : 0 Allowednet ptr : 0 Config: Got a phyint token. Config: IF: Config for interface ovpns1. Config: IF: Got disabled token. IF name : ovpns1 Next ptr : 0 Ratelimit : 0 Threshold : 1 State : 0 Allowednet ptr : 0 Config: Got a phyint token. Config: IF: Config for interface vmx0. Config: IF: Got disabled token. IF name : vmx0 Next ptr : 0 Ratelimit : 0 Threshold : 1 State : 0 Allowednet ptr : 0 Config: Got a phyint token. Config: IF: Config for interface igb1.60. Config: IF: Got disabled token. IF name : igb1.60 Next ptr : 0 Ratelimit : 0 Threshold : 1 State : 0 Allowednet ptr : 0 Config: Got a phyint token. Config: IF: Config for interface igb1.55. Config: IF: Got disabled token. IF name : igb1.55 Next ptr : 0 Ratelimit : 0 Threshold : 1 State : 0 Allowednet ptr : 0 buildIfVc: Interface igb0 Addr: xxxxx, Flags: 0xffff8843, Network: xxxxxxx buildIfVc: Interface igb1 Addr: 192.168.1.177, Flags: 0xffff8a43, Network: 192.168.1/24 buildIfVc: Interface vmx0 Addr: 192.168.66.1, Flags: 0xffff8843, Network: 192.168.66/24 buildIfVc: Interface lo0 Addr: 127.0.0.1, Flags: 0xffff8049, Network: 127/8 buildIfVc: Interface igb1.99 Addr: 192.168.99.1, Flags: 0xffff8843, Network: 192.168.99/24 buildIfVc: Interface igb1.10 Addr: 192.168.10.1, Flags: 0xffff8a43, Network: 192.168.10/24 buildIfVc: Interface igb1.90 Addr: 192.168.90.1, Flags: 0xffff8a43, Network: 192.168.90/24 buildIfVc: Interface igb1.60 Addr: 192.168.60.1, Flags: 0xffff8843, Network: 192.168.60/24 buildIfVc: Interface igb1.55 Addr: 192.168.55.1, Flags: 0xffff8843, Network: 192.168.55/24 buildIfVc: Interface ovpns1 Addr: 192.168.91.1, Flags: 0xffff8051, Network: 192.168.91/24 buildIfVc: Interface ovpnc2 Addr: xxxxxxx, Flags: 0xffff8051, Network: xxxxxxxx Found config for igb0 Found config for igb1 Found config for vmx0 Found config for igb1.99 Found config for igb1.10 Found config for igb1.90 Found config for igb1.60 Found config for igb1.55 Found config for ovpns1 Found config for ovpnc2 MC-Router API already in use; Errno(48): Address already in use -
@pr3dict said in Another IGMP proxy post:
Errno(48): Address already in use
Doesn't look good.
So you have a whole number of interfaces besides what you mentioned initially. You should try to get this working just on those interfaces initially before adding anything further.
Steve
-
I have a bunch of interfaces but I only have 1 of them listed for downstream and upstream...
-
I restarted the router and was able to start it up.
but i cant give the output because the site thinks its spam...
About to call timeout 4 (#0) SENT Membership query from 192.168.90.1 to 224.0.0.1 Sent membership query from 192.168.90.1 to 224.0.0.1. Delay: 10 Created timeout 5 (#0) - delay 10 secs (Id:5, Time:10) Created timeout 6 (#1) - delay 115 secs (Id:5, Time:10) (Id:6, Time:115) RECV Membership query from 192.168.90.1 to 224.0.0.1 The IGMP message was local multicast. Ignoring. RECV V2 member report from 192.168.90.100 to 224.0.0.252 Should insert group 224.0.0.252 (from: 192.168.90.100) to route table. Vif Ix : 1 Updated route entry for 224.0.0.252 o ```n VIF #1Current routing table (Insert Route): ----------------------------------------------------- #0: Dst: 224.0.0.251, Age:2, St: I, OutVifs: 0x00000002 #1: Dst: 224.0.0.252, Age:2, St: I, OutVifs: 0x00000002 -
Post it on pastebin or similar and link to it.
-
Gooood idea!
https://pastebin.com/2j8MGRRF
-
Ok, so you moved the server from 192.168.55.125? Where is it now exactly?
-
@stephenw10 Yeah sorry about that. The .10 subnet is where a lot of other clients are so while I was testing this I didnt want to have ot keep switching between .55 and .10...
The server is now at 192.168.10.142