pfSense Service or DL Package for SIP-ALG?
-
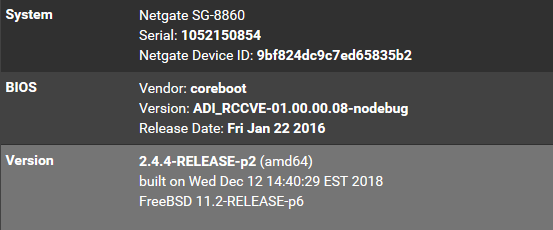
Hello I have this:
And I am working on deploying a new VoIP product and service for our SMB and they require data on SIP-ALG for optimal network set up,
I examined our firewall but I do not see this service.
Am I missing something? Should I search package manager?
Thanks.
-
https://docs.netgate.com/pfsense/en/latest/packages/package-list.html
RTFM: https://docs.netgate.com/pfsense/en/latest/packages/siproxd-package.html and head the warning. -
Requiring an ALG is often a sign your SIP product is configured incorrectly.
What issues are you seeing without it?
Steve
-
Hi Stephen,
Currently the first phase of implementation is just now commencing so nothing has been monitored yet with this.
The reason I want to know about ALG is because this VoIP company states it in their network parameters summary for using their product.
I am just trying to account for all potential points of failure when I fully deploy this.
They list QoS, Bandwidth Limiting, SNMP, Port Blocking capabilities as being required and that SIP-ALG be turned off.
It appears I aggrandized this as SIP-ALG only pertains to enterprise legacy network infrastructure systems I suppose?
Not modern ones?
-
@virtuousmight said in pfSense Service or DL Package for SIP-ALG?:
SIP-ALG be turned off.
Ah well you're good then!

Most recent SIP systems do not require an ALG and in fact it can often do more harm than good. There is no SIP-ALG in pfSense by default and the only thing available is SIProxd. That's usually only required for some ancient SIP phones that insist on using 5060 as the source port and cannot connect if it's randomised like most traffic. In that situation you can only have one phone behind the firewall without a proxy of some sort.
Anyway none of that applies to you and the other requirements can also be met.Steve
-
Stephen, for whitelisting traffic from remote IP addresses to conform to this...
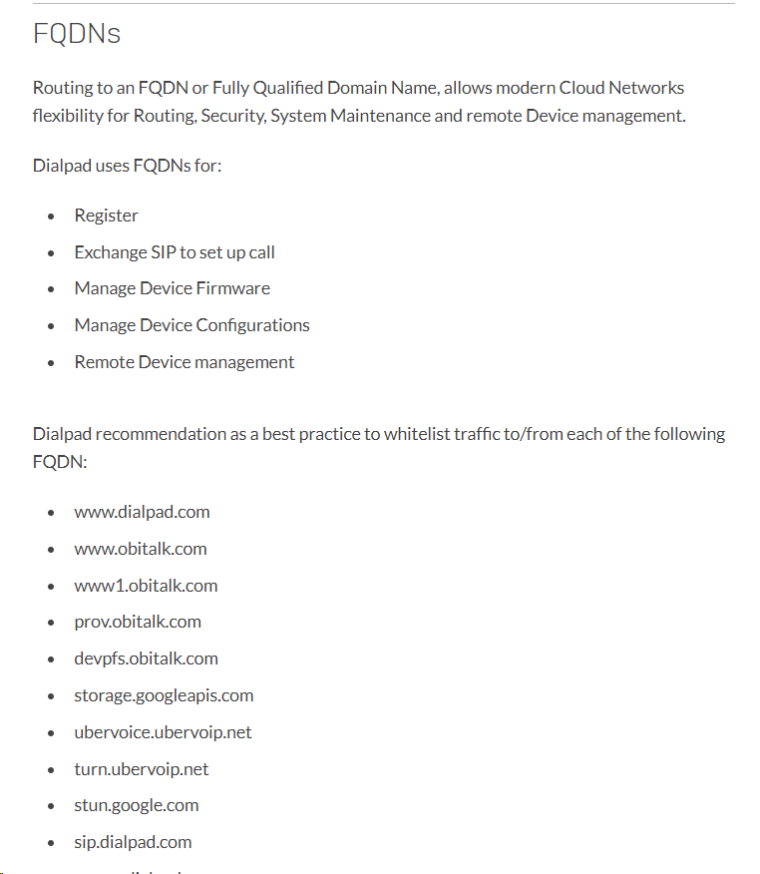
..does this require (out of necessity or optimization ) an external software package or can this be done directly in Interface settings?
-
Those would not be blocked anyway unless you have restrictive outbound rules.
You can add those to an alias and they will update when the filter is reloaded BUT they will be resolved at that time to an IP and that IP will be used. Some of those will probably resolve to multiple IPs and not all of them will be included.
If they have IP lists also you could add both to sure.Looks like they also recommend disabling stateful packet inspection which is possible in pfSense but we definitely do not recommend that and I can see no reason to do so.
https://help.dialpad.com/hc/en-us/articles/209954306-Network-RecommendationsSteve
-
So do you think I should notify them that SPI will remain enabled, because if I disable it then the SG pf sense machine would revert to a routing only platform with no firewall functionality which I think is enacted by disabling all packet filtering (SPI?) in the firewall advanced settings correct?
Which not something I am going to do so they must ensure that their product VoIP data packets are not going to be compromised so we do not get latency, jitter, or packet loss.
-
I don‘t know dialpad but just as a note...we use 3 totally different SIP providers with pfSense without any problems.
Most do not require any fancy configuration. :-)
Maybe they can offer you some-days-trial-account so you can try first with your setup?-Rico
-
Yes Rico, that is analysis phase that I must do and the trial begins next week, then I can monitor how their VoIP product performs against our network system set up to the best of my abilities. We had Ring Central VoIP before I started working here so I do not know whether or not any special configurations had to be set in our firewall for that and perhaps they current scheme will still work without a problem. Only thing I changed was the Firewall optimization option from Normal to Conservative.
Not sure if you meant SPI over SIP, but within the context I think I can infer correctly.
-
Of course I have SPI still enabled in pfSense. :-)
-Rico
-
@VirtuousMight I'm curious how Dialpad ended up working out for you? We recently hired a receptionist and started answering most incoming phone calls to our company main line (previously using Abby Connect.) But we have been seeing a lot of dropped or disconnected incoming calls.
I found this video from Netgate and subsequently switched "Firewall Optimization" to Conservative similar to like you mentioned.
Any other tips/tricks or experiences to share? -
Hello,
So our company decided to revert back to ring central after using dialpad for about a month.
Our experience with their product and services was low-grade - in terms of voip quality and end-user app usability (stability and lack of admin accessibility).
They rely to some extent on google data centers for some of their data operations which can be an advantage but also a dependency that is not fault tolerant. We experienced this when some database servers experienced disruption and our users where unable to access the app to get into their accounts to make calls.
I do not recommend dialpad. It appeared to me their systems are underdeveloped when it comes to non-Ai and non-sync features, meaning the primary usage of voip with them was inconsistent and low-quality as they seemed to have emphasized other feature enhancements over the main functionality, being voice-over-ip call quality and connection stabilization .