Can I route internet traffic from site B through site A via Ipsec VTI?
-
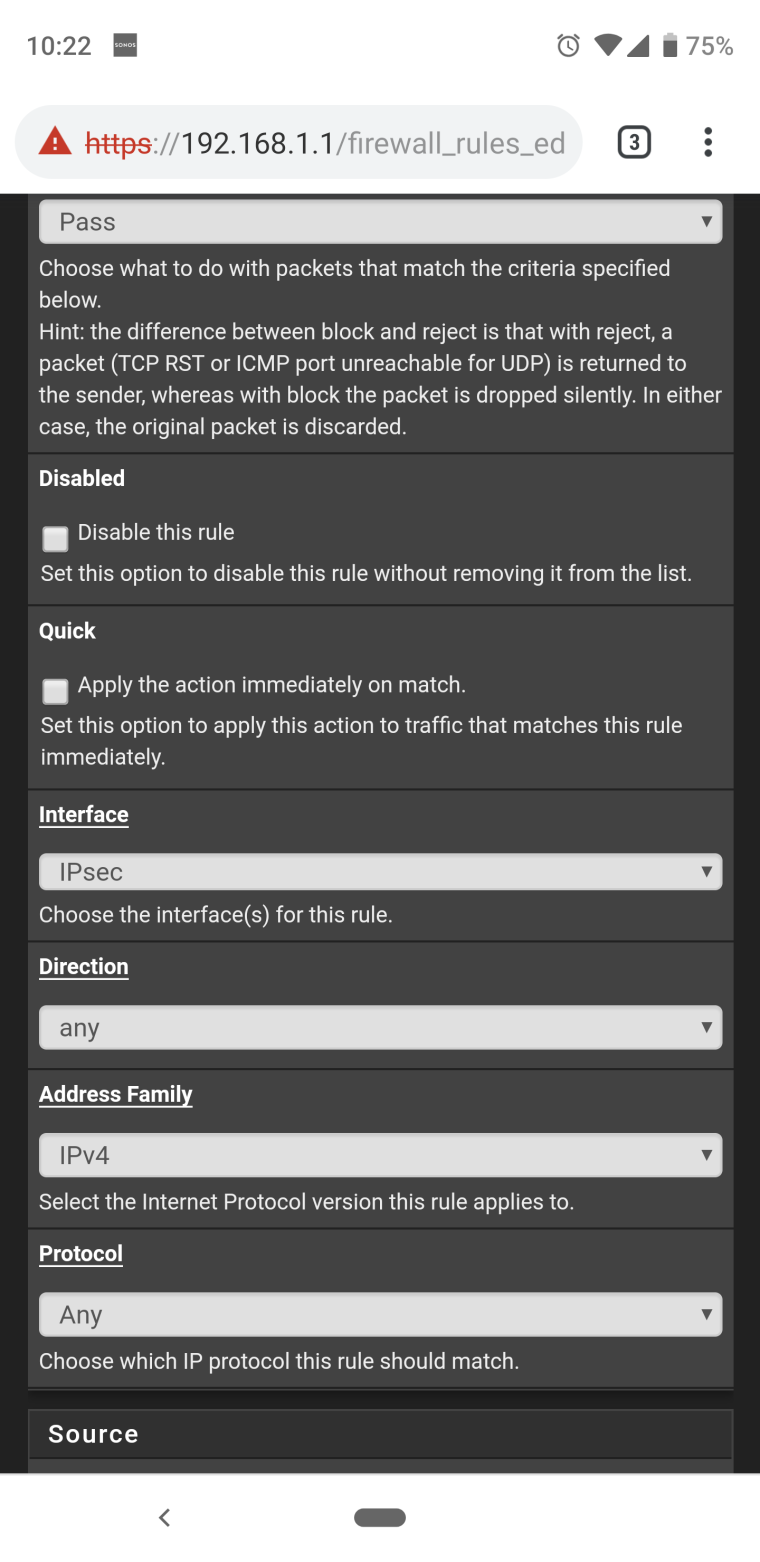
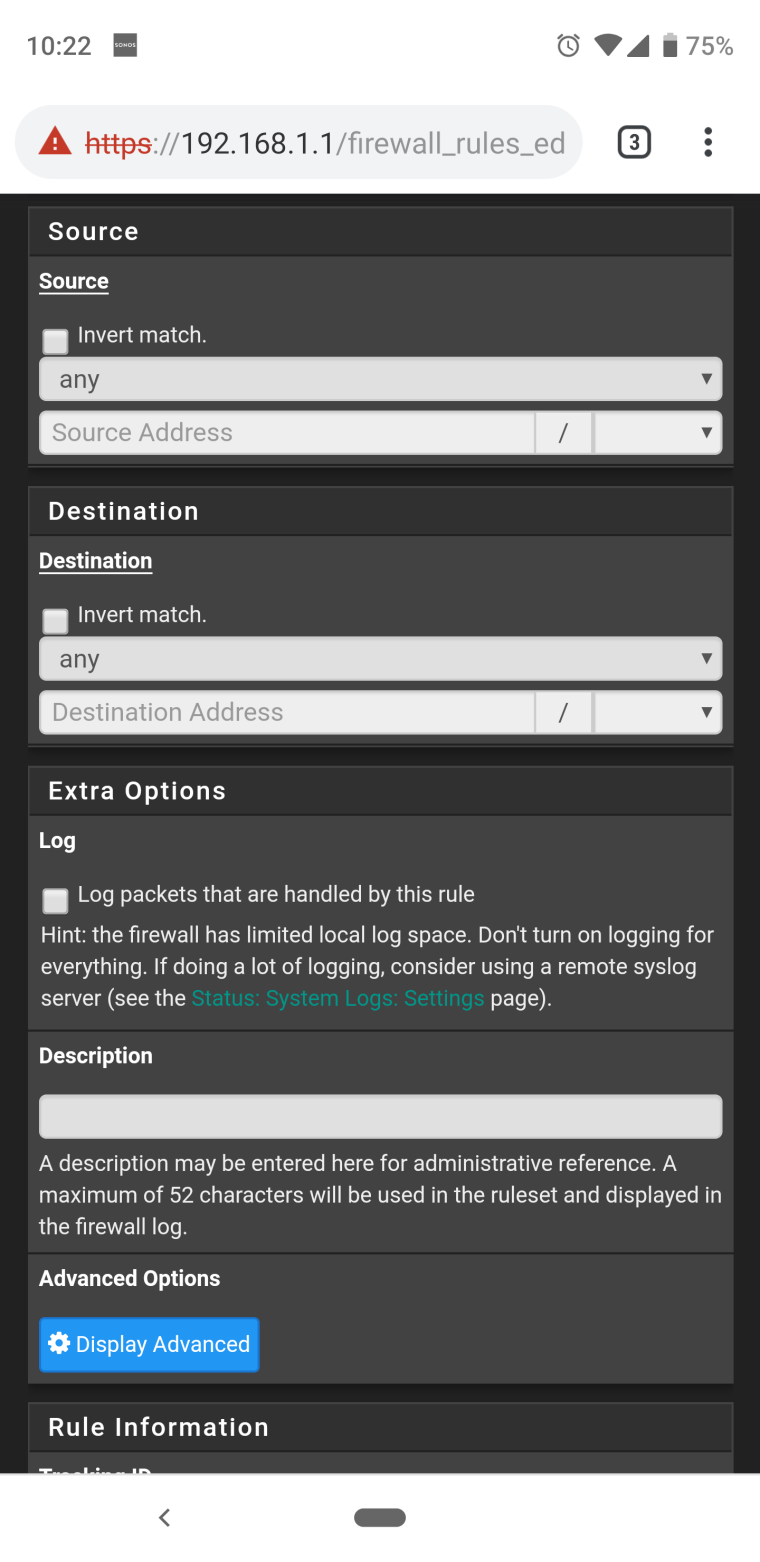
Done. See the below screenshots just to make sure I didn't do something wrong. No advance setting changes were made.
-
Still seeing the same issue flagging on the same rule.
-
@ngoehring123 said in Can I route internet traffic from site B through site A via Ipsec VTI?:
Still seeing the same issue flagging on the same rule.
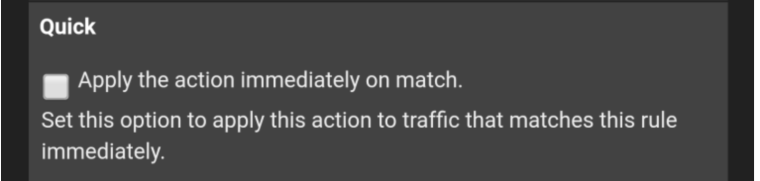
And if you check QUICK ?
-
Same deal - logs are on fire. I really wonder if I'm trying something that isn't fully implemented in pfsense/freebsd. I've done a ton of web searches and haven't been able to find anything that matches. Part of me wonders if site A forgets or cannot remember/track the connection and so when something comes back from the internet the router at site A it says "what's this request for 192.168.2.2?" and then blocks it or parts of it.
-
@ngoehring123
The first time such see
Show me what the command shows
pfctl -sr | grep enc0
(WebGUI /Diagnostics/Command Prompt/) -
pass out on enc0 all flags S/SA keep state label "IPsec internal host to host"
pass quick on enc0 inet all flags S/SA keep state label "USER_RULE"
pass in quick on enc0 inet all flags S/SA keep state label "USER_RULE" -
@ngoehring123
And still try in floating rule put option TCP Flags - ANY Flags and State type None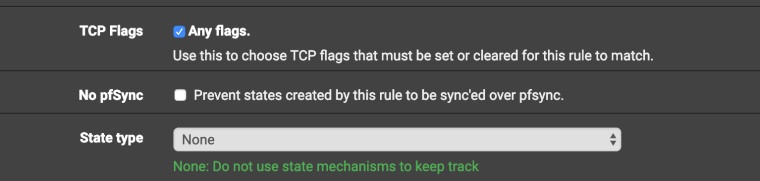
-
So firewall is still having events however now the interface has changed from ipsec to IPSEC_VTI. ???
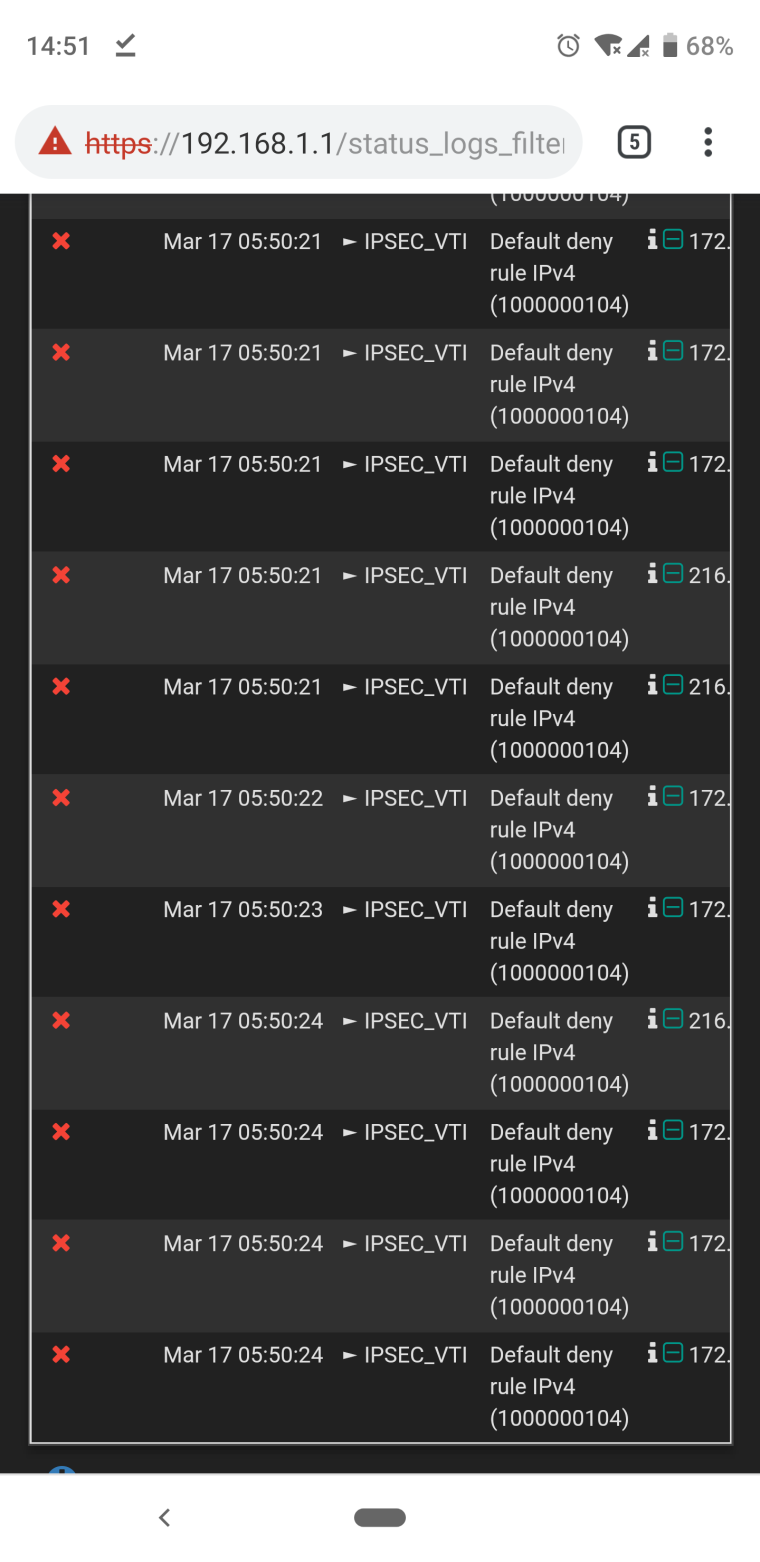
-
@ngoehring123 said in Can I route internet traffic from site B through site A via Ipsec VTI?:
IPSEC_VTI
That's the same floating rule , but for IPSEC_VTI ?
There will be two identical rules , one for IPSEC and the other for VTI -
I just have the one floating rule for ipsec. When I made those last changes you suggested the firewall errors started saying IPSEC_VTI instead of ipsec. I had to disable those last changes as they resulted in me losing access to the remote router. Thank goodness for openvpn.

-
@ngoehring123
Excuse. I didn't think there would be such a result. I have no more ideas )))
-
No worries my friend. Your time and effort is greatly appreciated. Here's to hoping this gets sorted out soon. I'll be sure to share the fix with you. Thanks again!
-
@ngoehring123
I would consider an option of the usual IPSEC tunnel, through it too it is possible to pass a traffic outside.
https://docs.netgate.com/pfsense/en/latest/vpn/ipsec/routing-internet-traffic-through-a-site-to-site-ipsec-vpn.html
-
I had thought of doing that as well but really like the routed option more due to its flexibility and power. Perhaps @jimp has some tips for me.
-
The really weird thing now is that my phone says I have no internet connection yet here I am writing to you and browsing the internet. Something is ascew...
-
@ngoehring123
That's possible. I myself use the GRE over IPSEC option and do not want to switch to VTI yet.
Will wait to hear other forum members -
@ngoehring123
In this forum, I read that some remove the VTI interface, re-create the tunnel , and the problems are solved -
I'll give that a go. After everything else, it won't hurt!
-
Hi,
I have the exactly same problem, did you get find any solution? -
I did not. Last thing I tried was to remove the interface, delete the static routes, and the remove the p1 and p2 and do it all over again. No luck. So I went back to openvpn. I was super excited to use the ipsec route instead due to the better throughput and all.