NAT or DNS question
-
Hello All,
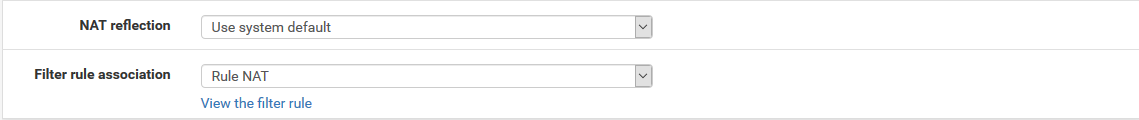
I have a PFSense firewall setup at my house. I have a PC, which I RDP to from both inside and outside of my house with a public DNS record. Internally I would like to be able to get to this PC using the same DNS name. I attempted to allow this by creating a NAT rule from LAN to WAN IP, redirect 9090 (public TCP Port) to TCP 3389. Is this the best path? If so, what am I missing? Also, if this should be solved with DNS, I would only want it to affect this particular DNS record, not the whole domain.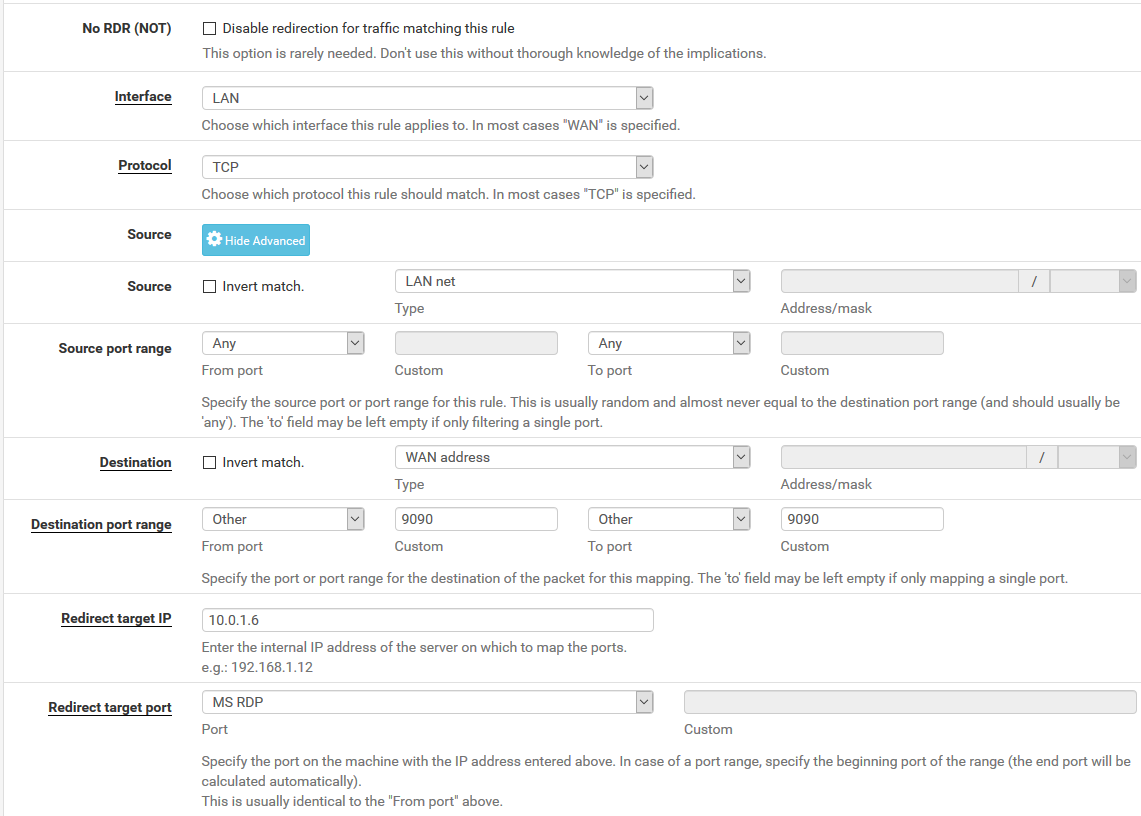
-
If you absolutely have to use <name>:9090 internal as external, then a NAT redirection may be a thing.
BUT: normally I'd never do that. (or even use RDP without a VPN!) If there's no other way as to make RDP accessible via WAN (which is gruesome) then I'd use <name.tld>:9090 from external and <name.tld> from LAN and simply do a Host Override for <name.tld> in your DNS resolver or DNS forwarder configuration (whatever you are using).
Greets
-
If you want to use nat reflection, just set that up on your nat rule on your wan that redirects 9000 to 3389.
If your going to allow rdp from public.. Agree horrible IDEA... and you don't want to remember to use :9000 or not... You could change your rdp to actually listen on 9000 then just port 9000 to 9000
And setup a host override for name.tld that your using to access your public IP outside, to point to the rfc1918 address of the rdp box when your internal.
You should really use VPN to access your rdp resources while your outside your network