Want to Block 1IP from using Internet when VPN goes down
-
nope didnt work
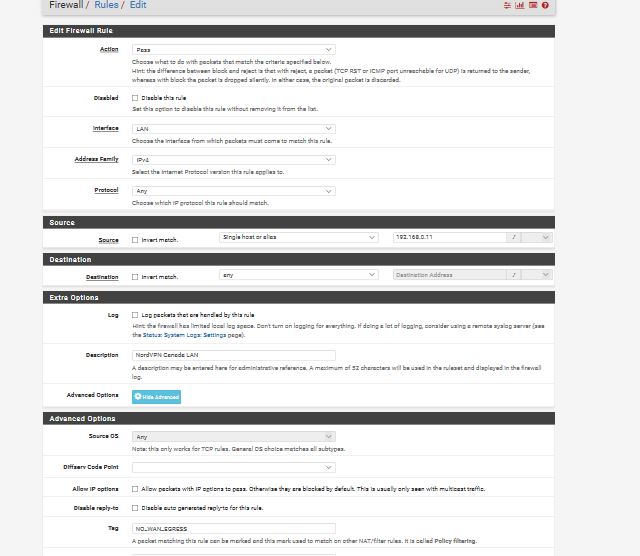
having TAG No Wan EGress for the 192.168.0.11 Under NordVPN one
and having TAGGED No Wan Eggress under Floating
just lets the 192.168.0.11 get WAN internet instead of blocked..
shouldnt the Rule be also set to TAGGED not TAG?
-
No.
TAG sets the mark. You set the mark on traffic from 192.168.0.11 when it arrives on the firewall using the LAN rule.
TAGGED matches the traffic that has that mark set so you are rejecting any traffic trying to go out WAN with that tag already set. It will only be set on traffic sourced from 192.168.0.11 because that's the only source address that matches the rule that sets the tag.
You must have done it wrong again or it would be working.
-
NORDVPN 192.168.011 TAG No WAN EGREE
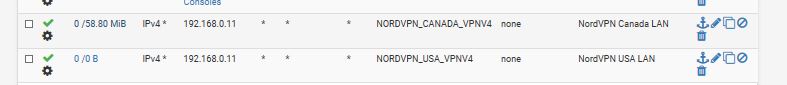
FLOATING TAGGED: NO WAN EGREE
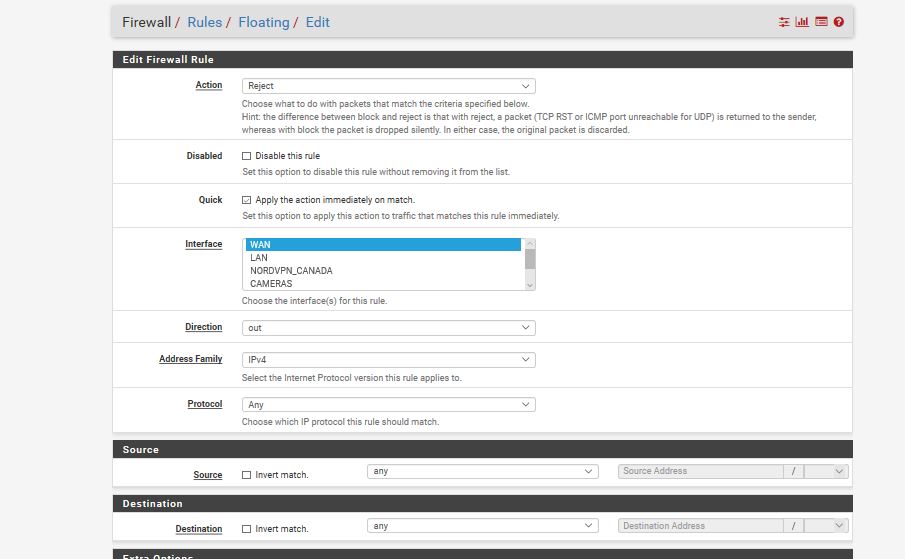
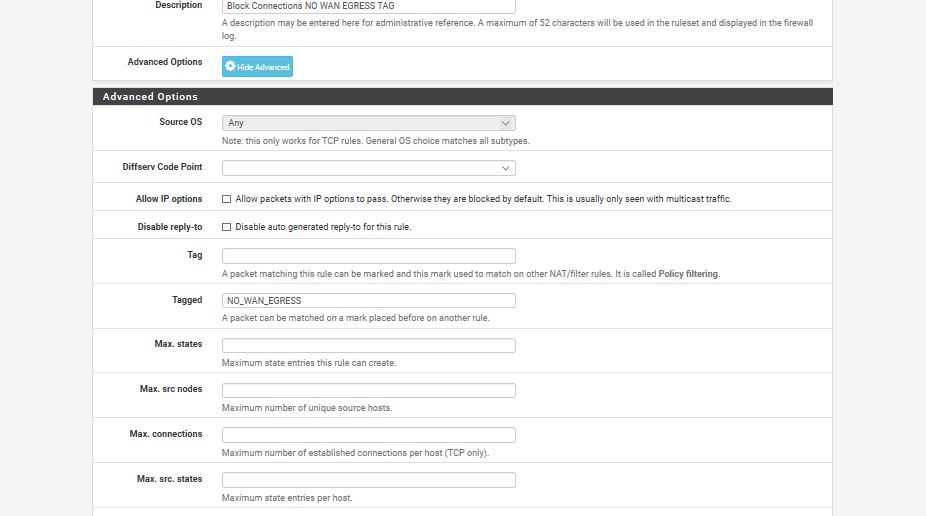
im going to delete the rule and the float and re type it in
i frustrated i getting frustrated yes understand its not easy but stupid dislexia is kicking me too and i like pfsense better then an asus router
i appreciate the help i going to type it up again and see what happens in 30 min i need a break... wish i was in the IT field id know this program better then just only adjust when i find there a problem once a month or so.. set it and forget it kinda thing
thank you for being patient with me i really appreciate it
-
Don't touch anything.
Just post /tmp/rules.debug
That tells everyone everything they need to know about your rule sets.
-
Hi.
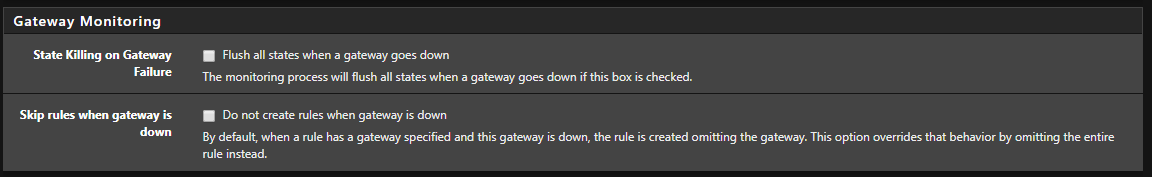
Go to System -> Advanced -> Miscellaneous
Scroll down to: Gateway Monitoring
Make sure it look like this.
-
so for the gate monitoring yes my 2 are also unchecked
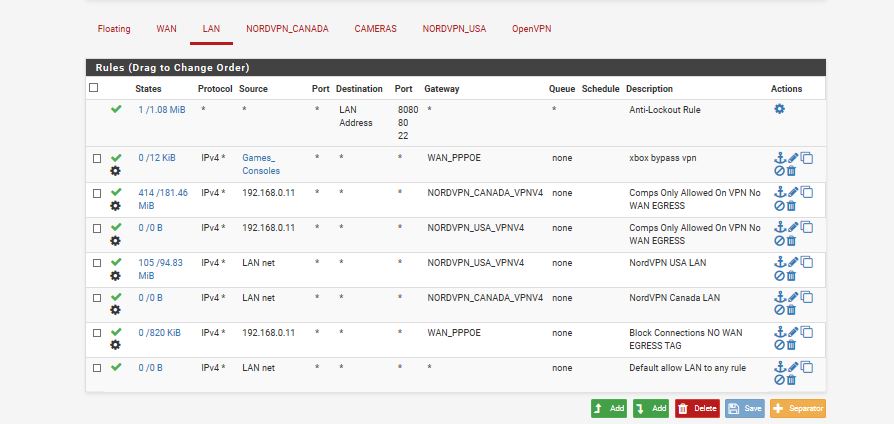
as for the Floating its working now.. i had disabled them then just re typed them up and the float
and it worked... also found i had to add a
another No WAN Egress for the LAN.NET when a VPN isnt enabled when i was testing it by turning it off
so this is working now.. doesnt help my dislexia i read like TAG as TAGGED so thats all working... i dont dare ask about how do i route the USA VPN to the USA one in the Rules and the CANADA VPN to the CAnada one.. instead of both going to the first rule... as i dont wanna frustrate you more with my questions..i played with it i didnt wanna annoy you more with questions i stepped away from it a bit then re looked at it fresh eyes for setting that floating etc
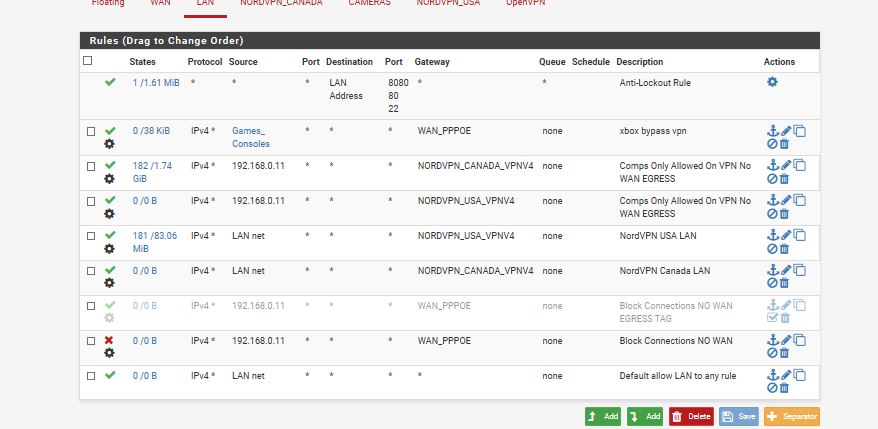
so this is working now in this order... i wont trouble you with my other question i jsut mentioned because i dont want you mad at me... but here is a pic of rules its working so i not going to touch it... it works when i shut off the vpn or if it goes down
i appreciate your patience with me
-
If you don't want traffic from 192.168.0.11 to go out WAN at all, why are you policy routing it out WAN?
-
if your talking about from the picture above the 2nd from the bottom
i dont... but if i dont put that rule in there... and i turn off both VPN's
the rules skip the 2 rules below Game Consoles and goes straight to the last Line..so i put rule just above it... and its TAG No WAN EGRESS so it blocks using WAN
-
figured that was better then saying Block 192.168.0.11 * * * in the rules
unless thats better then the TAG i just figured it was a better block if not ill change it -
is this more proper then
-
@Derelict
I have 1 more question if you might know..
the no_wan_egreess works as long as my vpn I don't check the box "Don't Pass Routes"
if I enable it... The IP Address I have Tag NO WAN EGRESS is automatically blocked yet should be using the VPNbut I notice I need to check Don't Pass Routes to get my XBOX to work bypass VPN
do you know how to get get the rule to work for the VPN and TAG No Wan Egress when you check "Don't Pass Routes"
and should I be using that check box or not... whats the difference I tried googling info but I didn't find info
if you have a link that explains the 2 be good toobut I figured I ask you about that since your very smart at this stuff
-
so having the check mark Dont Pass Routes... still leaks dns yet i dont see it...
i get email from my isp i done suspicious things but i didnt
i run www.dnsleaktest.com on the 192.168.0.11 and it shows 1 server my NordVPN
yet it must be leakingis there another program that runs on windows that securly checks this stuff?
as this No Wan Egress isnt working
least it seems to work only when "DO Not Pull Routes" is not Checked.
when its checked it seems to leak or not work rightis there a way to test this and i read some articles you want Do Not Pull Routes other times you do .. how do you know when
-
I'm not sure that people appreciate how complicated what you are trying to do is.
-
sorry then ill figure out myself
didnt think it was complicated for you guys just for me
cuz i guess it works fine if Do not pull routes... yet XBOX doesnt work for OPen Nat
and when i do check off pull routes No WAN Gress does not kick in instantly like it does when "do not pull routes " is not checked... and Xbox Works Open Natvery sorry for troubling you guys then.. i wont ask again
have a good weekend
-
It's not complicated for me. It would just take me three hours I don't have to explain it to you.
You need to understand:
- Policy routing and what it is and is not
- The routing table and what it is and is not
- What Don't pull routes actually does with your chosen VPN provider
- How DNS actually works
- How connections originating from the firewall itself apply in all of the above
- How tagging and matching tagged in pf works
I suggest watching https://www.youtube.com/watch?v=lp3mtR4j3Lw
-
Think you forget the 0 on your 3 there Derelict... Your 4 days in already.. ;)
This is clearly simple facebook sort of post -- suggest you get your help over there since you don't seem to want to take Derelicts ;) Sure they help you out in couple of mins..