Configuration for Insertion between Router and Lan Clients
-
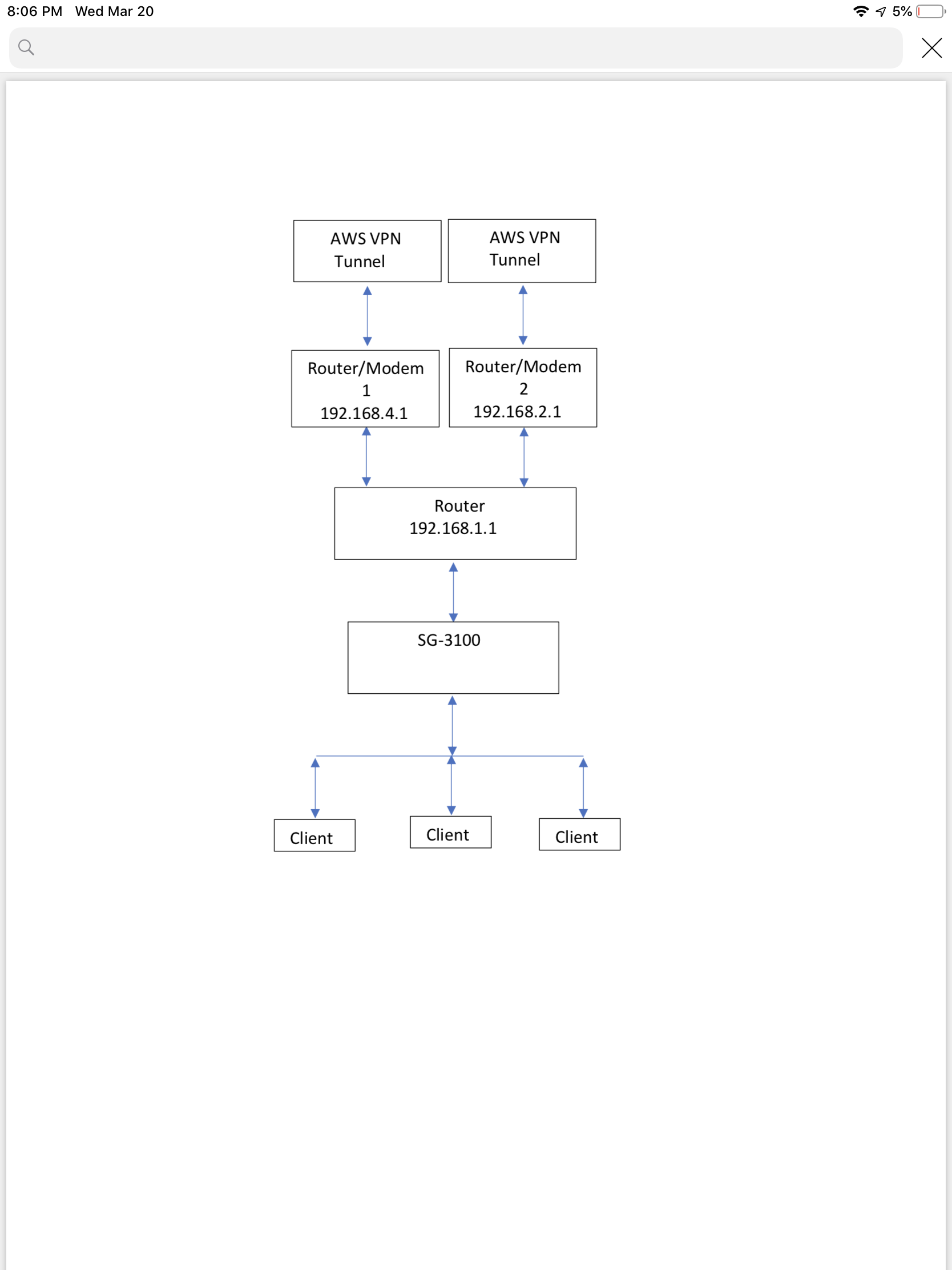
I have been unable to find the details of how to configure PFSense WAN and LAN Settings to allow insertion between the Router (running AWS VPN tunnels) to the LAN Clients.
I have tried turning off the PFSense DHCP and tried static IP’s for the WAN and LAN it without any luck. More than once I have lost connectivity with the appliance.
So if someone would be kind enough to specify in detail the WAN and LAN configuration I would appreciate it.
I include a drawing below (I think) for reference.
Thanks!
-
It's hard to say exactly as you have not labeled subnets but you probably need to setup the 3100 as a transparent firewall.
That means bridging WAN and LAN so that both are in the 192.168.1.X subnet.
But that's usually a terrible idea! It appears you're already double NATing the connection via two routers. Adding a 3rd router probably isn't what you want. What exactly are you doing here?
What are those "Modem/Router" devices?
Where is the AWS VPN terminated?
Ideally you want to replace the thing you have labeled "Router" with the 3100 and switch the other devices to modem mode to pass public IPs to the 3100 directly.
Steve
-
Thanks for providing your thoughts on this. From my research it does appear bridge mode would allow insertion per my diagram (after the existing router). Using the Wan and Opt1 ports in bridge mode on the SG-3100.
I will do my best to explain what I am trying to accomplish and what the various devices are.
The modem/router devices are provided by my IP and I sure wish they were just modems. They are called Bell Home Hub 3000's which appear to be rebranded Sagecomm Fast 5566 units that can do Fiber or Fixed Wireless LTE. In my case I am stuck with fixed wireless and they are locked down to prevent customer access. The current configuration (prior to the SG-3100 insertion) seems to work well but I do realize I could be into a double NAT situation. The existing Balance 210 Router has something called "Drop In Mode" that allows it to be semi transparent when installed into an existing network.
The AWS VPN tunnel is used to do Dual Wan bonding using the "free" service made available by Peplink .... Solo Fusion Hub.
Apparently I could have used PFSense to do something similar and I now note that there is a means to setup session persistence which would have been mandatory. When I was searching for Dual Wan Bonding devices, PFSense never seemed to be a player otherwise you can bet I would have jumped at it as it would have been way less cost!
I realize inserting the PFSense appliance behind the router removes much of the functionality that it can provide however the PFSense firewall would be superior to anything I could setup on my existing router and I can also download packages such as Snort.
I am woking hard to read up on network design and the PFSense appliance is aiding with that steep learning curve.
So once again I really appreciate your thoughts.
Now that I have explained what I am trying to do please provide any additional insights and thanks again!
-
So the Balance 210 Router is providing the line bonding via a Peplink service in AWS? And that is the 192.168.1.1 device in your diagram?
If not where is the 'Solo Fusion Hub' in that?Steve
-
You are correct. Fusionhub is the Peplink wan bonding service. Solo just means it allows an individual to use the AWS VPN tunnel for free.
https://www.peplink.com/products/fusionhub/
-
Ah, I see! Interesting. pfSense can't bond links in that way. It can do failover or load-balanced WAN connections but not lossless like that.
To just add IDS/IPS you could just add it in bridge mode but it will make things more complex.
Steve
-
I gave the bridge mode a try today. I believe I have the PFSense appliance properly configured.
I was able to update firmware and download Snort but I think I had a conflict of some kind so I decided to abort for now. Everything went south on me so I stopped and backed out.
It turns out I accidentally took down my whole network by accidentally plugging my Lan into the third expansion Wan port on the Balance 210 Router that is not activated. Stupid move! It took me an hour to realize the bone head move!
Needless to say ...that port is now tapped over.
Will read some more and go at it again in a few days ....